Use cases
Calculate the endpoint usage with the Monthly License Usage report
This section explains how to calculate the endpoint usage with the Monthly License Usage report, in GravityZone Cloud.
As a Bitdefender managed service provider (MSP), you can offer Bitdefender cloud security add-ons and services in a flexible manner, best suited to your clients with monthly license. Consequently, you can charge them depending on how they use these products.
GravityZone helps you keep track of the used resources with the Monthly License Usage report, which you have to generate at the beginning of each month for the previous month.
For details about generating a Monthly License Usage report in Control Center or via API, refer to Create a Monthly License Usage report in GravityZone.
About the Monthly License Usage report
The Monthly License Usage report aims to provide all the details you need to measure and charge the usage of GravityZone services accordingly. It also includes information to simplify the process of billing.
Calculation of the monthly usage relies on the product type, protection model, add-ons and services that companies have used during the previous month.
Companies can use the following product types:
Endpoint Security - the fully-featured security solution, with all modules available for deployment on endpoints.
BitdefenderEDR - a lightweight Endpoint Detection and Response (EDR) solution for Windows-based systems that can run alongside any third-party protection platform.
Bitdefender PHASR - a lightweight PHASR solution for Windows-based systems that can run alongside any third-party protection platform.
When creating the report, you are provided with the following options that help you focus on the data you are interested in:
Product type - generate the report for either companies with Endpoint Security or with Bitdefender EDR.
Only endpoint details - the report focuses on information related to the endpoints and ignores the companies' hierarchy.
Only direct companies - the report does not include the entire hierarchy, but only child companies at the first level under the target company.
Only new customer companies - the report only includes companies created between two specific dates. When selected, these options appear below:
Company registration start date - only companies created after this start date will be included in the report.
Company registration end date - only companies created before this date will be included in the report.
Important
You must fill in both fields, otherwise no information will be included in the request.
As displayed in Control Center, the Monthly License Usage report consists mainly of two areas:
The chart, which depicts the usage of some GravityZone add-ons and services during the month.
The table, which lists details about companies, license and usage. The table is customizable by clicking the Show/Hide Columns button in the top-right corner.
Clicking the numbers of each element of the column provides you with more details regarding endpoints and the usage of GravityZone add-ons and services.
Note
If a GravityZone add-on or service has not been enabled for a company, it is specified as such.
Below we have covered all the information covered in the report.
Note
Some columns can only be found in the .CSV version of the report.
Column name | Description |
|---|---|
Path | The location of the target company in the network tree. |
Company | The company's name. |
Company type | The type of the company. Possible values:
|
License key | The key of the license used by the company. |
License Type | The type of the license. Possible values:
|
Month | The month for which the report was created. |
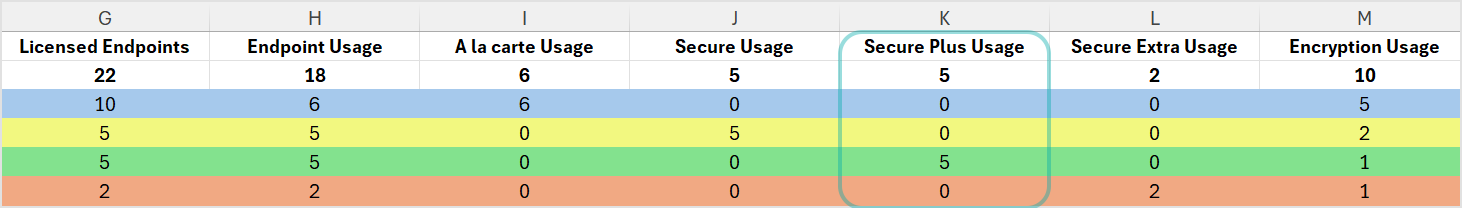
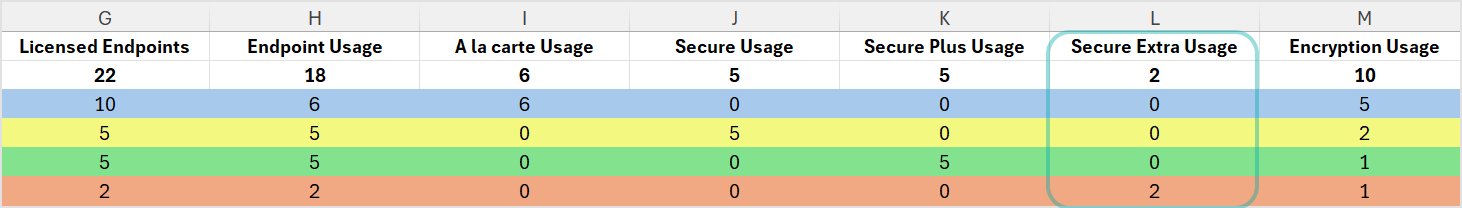
Licensed endpoints | The number of endpoints licensed during the month (physical servers or workstations, virtual servers or workstations and container hosts). |
Endpoint Usage | The number of endpoints with core protection. |
A la carte Usage | The number of endpoints that register under Endpoint Usage under companies that use the A la carte protection model. |
Secure Usage | The number of endpoints that register under Endpoint Usage under companies that use the Secure protection model. |
Secure Plus Usage | The number of endpoints that register under Endpoint Usage under companies that use the Secure Plus protection model. |
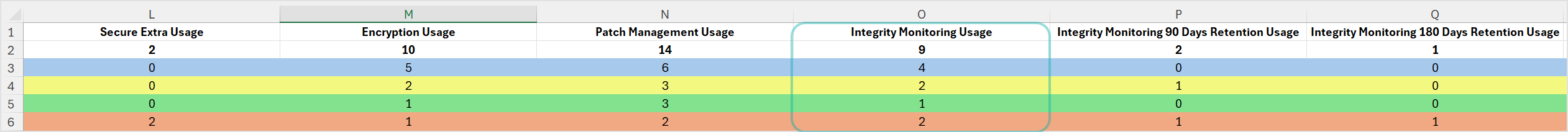
Secure Extra Usage | The number of endpoints that register under Endpoint Usage under companies that use the Secure Extra protection model. |
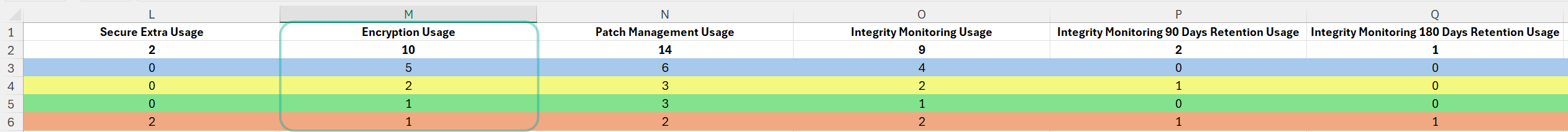
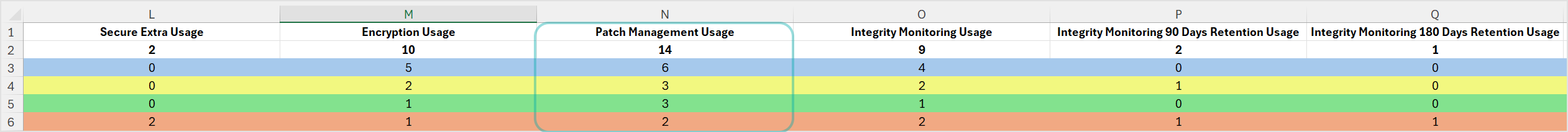
Encryption Usage | The number of endpoints where the Full Disk Encryption add-on was deployed during the month. |
Patch Management Usage | The number of endpoints where the Patch Management add-on was deployed during the month. |
Integrity Monitoring Usage | The number of endpoints where the Integrity Monitoring add-on was deployed during the month. |
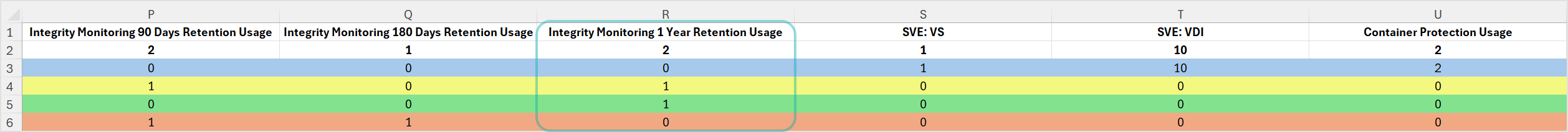
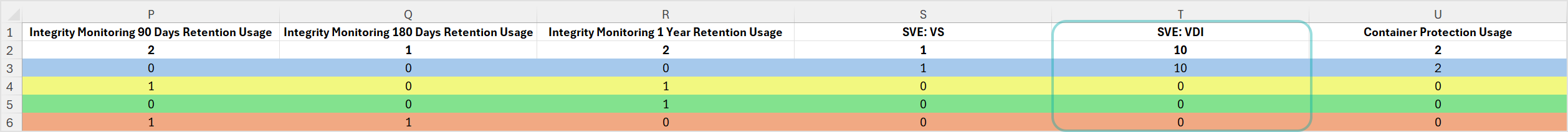
Integrity Monitoring 90 Days Retention Usage | The number of endpoints where the Integrity Monitoring add-on and the 90 days data retention add-on was deployed during the month. |
Integrity Monitoring 180 Days Retention Usage | The number of endpoints where the Integrity Monitoring add-on and the 180 days data retention add-on was deployed during the month. |
Integrity Monitoring 1 Year Retention Usage | The number of endpoints where the Integrity Monitoring add-on and the 1 year data retention add-on was deployed during the month. |
SVE: VS | The number endpoints that meet all the below requirements:
|
SVE: VDI (in hours) | The number of uptime hours for virtual desktops with Central Scan that meet the following requirements:
|
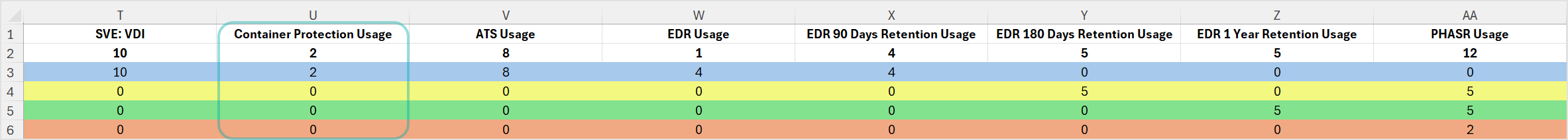
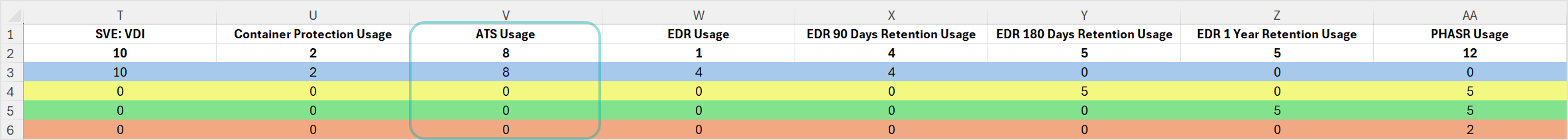
Container Protection Usage | The number of endpoints where the Container Protection add-on was deployed during the month. |
ATS Usage | The number of endpoints where the Advanced Threat Security add-on (this includes both HyperDetect or Sandbox Analyzer) was enabled during the month. |
EDR Usage | The number of endpoints where the Bitdefender EDR add-on was deployed during the month. |
XDR Identity Providers Usage | The number of endpoints where the XDR sensor for Identity Providers was deployed. |
XDR Productivity Usage | The number of endpoints where the XDR sensor for Productivity was deployed. |
XDR Network Usage | The number of endpoints where the XDR sensor for Network was deployed. |
XDR Cloud Workloads Usage | The number of endpoints where the XDR sensor for Cloud Workloads was deployed. |
MDR Foundations Usage | The number of endpoints that belong to companies that use the Bitdefender MDR service, and are monitored. |
Reserved Seats | The number of seats that have been reserved for the company. NoteThe table will show |
Subscription End Date | The end date for the company's license subscription. NoteThe table will show |
Subscription Auto-Renewal | Indicates if the Auto-Renewal option is enabled for the company. |
Minimum Usage | Indicates if the Minimum Usage option is enabled for the company and displays the value assigned to it. |
Product Type | The type of the product the company uses. Possible values:
|
Available output formats
From the GravityZone Control Center, you can export the report in PDF and CSV formats, or you can send it through email.
Usage for companies with Endpoint Security
To calculate the monthly usage for GravityZone modules, add-ons, and services you need the CSV file.
The monthly usage is counted based on the enabled modules, add-ons, and services during the month. The modules are part of the GravityZone core protection, while add-ons and services are optional and billed separately.
Note
Depending on the protection model assigned to the company's own use, some add-ons and services may be included alongside the core protection. In these cases, the usage will show as 0 in monthly usage reports, regardless of the number of endpoints the associated models are deployed on.
If a company has used multiple protection models for its own use during a month, a single one counts toward its monthly usage. From the list of used protection models, the one matching the highest on this list is taken into account:
Secure Extra
Secure Plus
Secure
A la carte
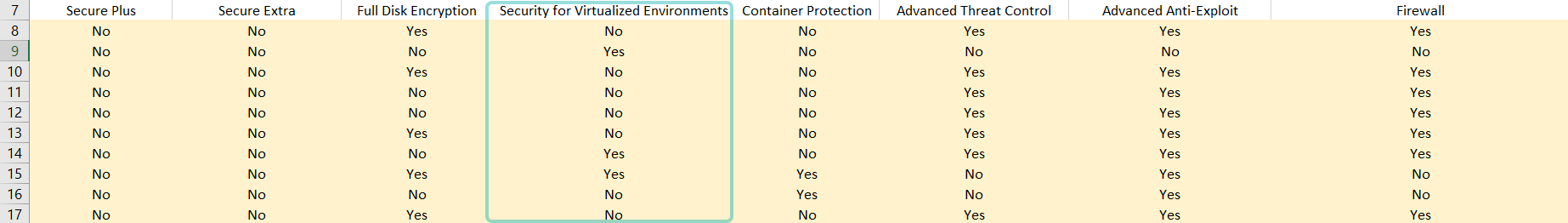
The CSV file lists all the standard and optional security layers, along with other relevant data on companies and endpoints.
Usage for endpoints with core protection
The GravityZone core protection includes the following modules and roles:
Antimalware (not listed in the report as it is installed by default on endpoints)
Advanced Threat Control
Advanced Anti-Exploit
Firewall
Content Control
Device Control
Network Attack Defense
Power User
Relay
The usage for endpoints with standard protection is based on the Antimalware module.
The other modules do not generate additional usage in terms of billing, but they are listed in the CSV file for you to have a complete view over what is installed on the endpoints.
The usage is calculated based on the number of endpoints with core protection installed during the month and is available in the Endpoint Usage column.
A licensed endpoint does not qualify to be added under Endpoint Usage if any of the following conditions apply:
A Security Container package has been deployed on the endpoint during the month.
Note
In this case the endpoint usage will be recorded under Licensed Endpoints and Container Protection Usage.
All of the below conditions apply:
The company the endpoints belong to has the Security for Virtualized Environments feature enabled for own use.
The endpoint type is
virtual.The endpoint is connected to at least one Security Server (SVA).
The endpoint has the Central Scan scan mode enabled.
The endpoint has an operating system that is compatible with Central Scanning. Learn more
Note
In this case the endpoint usage will be recorded under Licensed Endpoints and SVE:VS or SVE:VDI.
API
Use the getMonthlyUsage method to obtain the value for endpointMonthlyUsage. For details, refer to getMonthlyUsage.
Usage for endpoints with add-ons
The GravityZone add-ons include:
The usage for Full Disk Encryption is calculated by the number of endpoints that have installed this add-on during the month.
In the CSV file of the Monthly License Usage report, filter the corresponding column by "Full Disk Encryption = Yes" to get the usage of this add-on.
The usage of Patch Management is calculated by the number of endpoints that have used this add-on during the month.
In the CSV file of the Monthly License Usage report, filter the corresponding column by “Patch Management = Yes” to get the usage of this add-on.
The usage for Advanced Threat Security is calculated by the number of endpoints that have installed at least one of HyperDetect or Sandbox Analyzer add-ons during the month.
In the CSV file, filter the Advanced Threat Security by “ATS=Yes”.
If you want granular information, filter the HyperDetect and Sandbox Analyzer columns by "HyperDetect = Yes", then "Sandbox Analyzer = Yes". You have to combine the results to get the usage of these modules.
The usage for Endpoint Detection and Response (EDR) is calculated by the number of endpoints that have installed the EDR sensor during the month.
In the CSV file of the Monthly License Usage report, filter the corresponding column by “Endpoint Detection and Response = Yes” to get the usage of this module.
Upgrading Data Retention
Endpoint that are active during the change will report usage based on the upgraded retention add-on starting in the current month.
Endpoints that are added during the month when the change occurs will report usage based on the upgraded retention add-on for the current month.
Endpoints that are offline during the change will report usage based on the highest retention level that was active while it was online.
Downgrading data retention
Endpoint that are active during the change will report usage based on the original data retention add-on for the current month. Usage for the new retention option will be recorded starting the next month.
Endpoints that are added during the month when the change occurs will report usage based on the add-on that is active when they go online.
Endpoints that are offline during the change will report usage based on the highest retention level that was active while it was online.
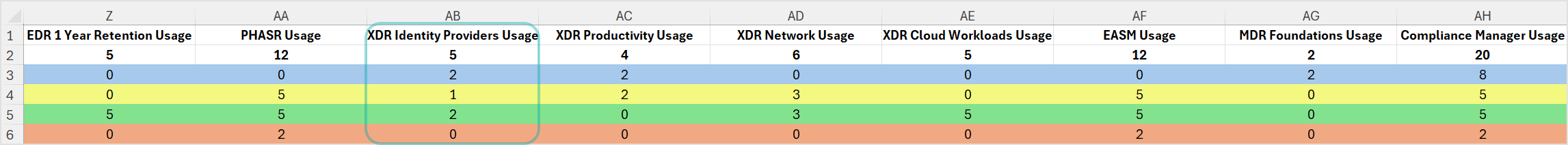
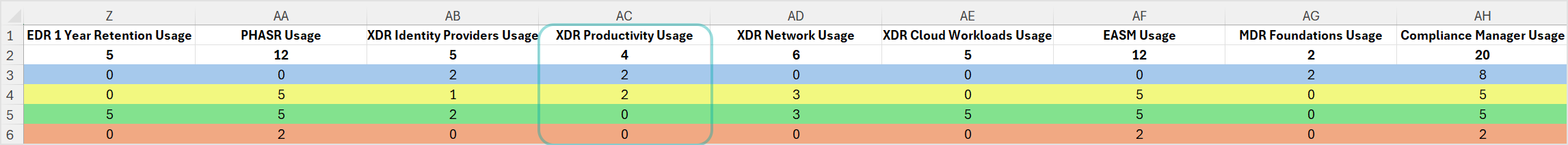
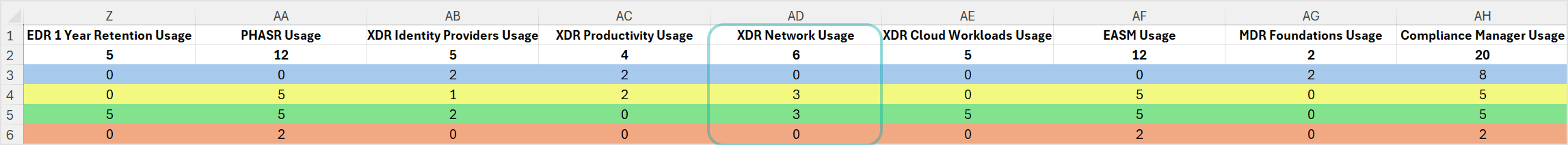
Usage is calculated separately for each XDR category type (Identity Providers, Productivity, Network, and Cloud Workloads), based on three factors:
Having the XDR sensor category enabled.
The total number of endpoints licensed during the month.
Having at least one sensor deployed. If no sensors belonging to the category have been deployed at any point during the month, the usage is set to 0.
Note
Disabling all sensor types or reducing the total number of licensed endpoints will reflect in the following month's usage.
In the .CSV file of the Monthly License Usage report, the XDR Identity Providers, XDR Productivity, XDR Network, and XDR Cloud Workloads indicate which sensor types are enabled. You can get the usage for each sensor type by checking the values under the XDR Identity Providers Usage, XDR Productivity Usage, XDR Network Usage, and XDR Cloud Workloads Usage columns.
The usage for PHASR is calculated by the number of manged endpoints for the company during this month.
In the CSV file of the Monthly License Usage report, filter the corresponding column by PHASR = Yes to get the usage of this add-on.
The usage of Integrity Monitoring is calculated by the number of endpoints that have installed this add-on during the month.
Note
The monthly usage starts when the add-on is installed and licensed, not when it's enabled in the policy.
Upgrading Data Retention
Endpoint that are active during the change will report usage based on the upgraded retention add-on starting in the current month.
Endpoints that are added during the month when the change occurs will report usage based on the upgraded retention add-on for the current month.
Endpoints that are offline during the change will report usage based on the highest retention level that was active while it was online.
Downgrading data retention
Endpoint that are active during the change will report usage based on the original data retention add-on for the current month. Usage for the new retention option will be recorded starting the next month.
Endpoints that are added during the month when the change occurs will report usage based on the add-on that is active when they go online.
Endpoints that are offline during the change will report usage based on the highest retention level that was active while it was online.
The usage for this add-on is calculated by:
Number of virtual servers with Security for Virtualized Environments
Note
Linux virtual machines are considered virtual servers.
Number of hours of using virtual workstations (VDI) with Security for Virtualized Environments
To obtain these data, you are provided with the following columns in the CSV file of the Monthly License Usage report:
Endpoint OS type: server or workstation.
Endpoint type: physical or virtual.
Uptime: how much time the endpoint has been protected by GravityZone. The uptime is counted in seconds and it is rounded up when converted in hours. For example, if the uptime for an endpoint with Central Scan is 3,600 seconds it means the endpoint will be charged for one hour. If the uptime is 3,650 seconds, the endpoint will be charged for two hours.
Important
The sleep and hibernation modes are not counted for uptime.
Security for Virtualized Environments: Yes means the endpoint used Central Scan engine at least once during the month. No means the company has been using Local Scan or Hybrid Scan engines.
In the CSV file, filter the columns as follows:
For virtual servers (VS) with Security for Virtualized Environments by selecting "Security for Virtualized Environments = Yes" and "Endpoint type= Virtual" and "OS type = Server"
For virtual workstations (VDI) with Security for Virtualized Environments by selecting "Security for Virtualized Environments = Yes" and "Endpoint type= Virtual" and "OS type = Workstation", then sum up the uptime and divide it by 3600 to get the hourly usage. The result is rounded up.
Note
In case of using virtual servers (VS) or virtual workstations (VDI), you need to subtract them from the total number of machines to avoid double billing.
The usage of Security for Exchange is calculated with the dedicated [Exchange] Monthly License Usage report. This report provides you with details such as: company name, license keys, month, and the number of protected mailboxes belonging to each managed company.
In the Monthly License Usage report, you can view the number of endpoints with Security for Exchange, but only for your information.
Extended Email Security usage is based on the number of active primary mailboxes during the selected reporting period. Aliases and functional mailboxes are excluded from usage calculations.
Tip
An active mailbox mailbox that sends or receives at least one email during the selected reporting period.
A received email is any email processed by the service, including delivered, quarantined, or attempted deliveries.
A mailbox is subject to billing only if one of the following configurations is in place:
The domain’s MX records are configured for Mesh Gateway or Mesh Unified
Azure synchronization is configured for Mesh 365 or Mesh Unified.
Counting rules:
Only primary mailboxes are counted
Aliases are not counted
Functional mailboxes are not counted
The [Extended Email Security] Monthly License Usage report provides the following details:
Company name
License keys
Reporting month
Number of protected mailboxes per company
The usage for GravityZone Security for Mobile is calculated based on the number of active devices where the security agent is installed.
Mobile devices are subject to billing if:
The security agent is installed on the device.
The device is visible in the Mobile Security console.
The device is visible in the Mobile Security console and has been online at least once during the calendar month
The Mobile Security Monthly License Usage report provides you with details such as: company name, license keys, device ID, device model, device OS, device user, first seen and last seen.
The usage for Container Protection is calculated based on the following criteria:
The number endpoints with Container Protection deployed.
If deployed on a virtual server, the instance will be deducted from the VS usage number.
If not deployed on a virtual server, the instance will be deducted from the endpoint usage number.
To obtain these data, you are provided with the following columns in the CSV file of the Monthly License Usage report:
Container Protection: if the add-on is activated
Container Protection Usage: number of endpoints with the module installed
Endpoint OS type: server or workstation.
Endpoint type: physical or virtual.
The usage for the Compliance Manager add-on is calculated by the number of manged endpoints for the company during this month.
In the CSV file of the Monthly License Usage report, filter the corresponding column by Compliance Manager = Yes to get the usage of this add-on.
API
Choose one of these variants:
Use the method
getMonthlyUsageto obtain the value forcomplianceMonthlyUsage.Use the
getMonthlyUsagePerProductTypemethod to obtain the object usages with"productType": 0and the value forcomplianceMonthlyUsage.
Note
For details, refer to getMonthlyUsage and getMonthlyUsagePerProductType.
The usage for EASM is calculated by the number of manged endpoints for the company during this month.
In the CSV file of the Monthly License Usage report, filter the corresponding column by EASM = Yes to get the usage of this add-on.
API
Choose one of these variants:
Use the method
getMonthlyUsageto obtain the value foreasmMonthlyUsage.Use the
getMonthlyUsagePerProductTypemethod to obtain the object usages with "productType": 0 and the value foreasmMonthlyUsage.
Note
For details, refer to getMonthlyUsage and getMonthlyUsagePerProductType.
Usage for endpoints with services
The GravityZone services include:
The Managed Detection and Response (Bitdefender MDR) for MSPs service is called Foundations.
The usage for Bitdefender MDR Foundations is calculated by the number of endpoints with an installed EDR module, which have enabled this service during the month.
In the CSV file of the Monthly License Usage report, filter the corresponding columns by "Bitdefender MDR Foundations= Yes" to get the usage of this service.
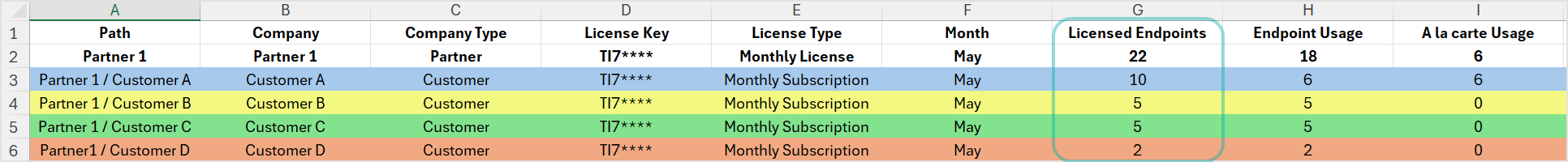
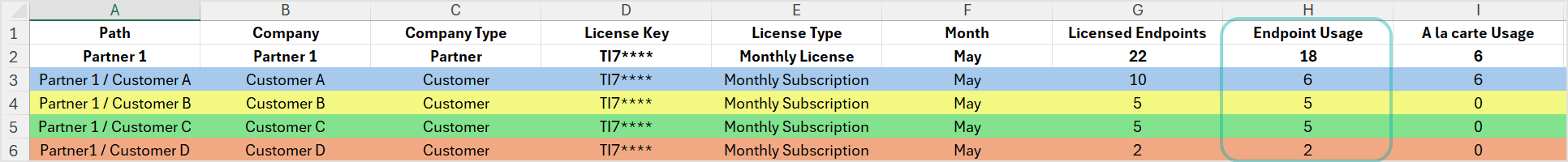
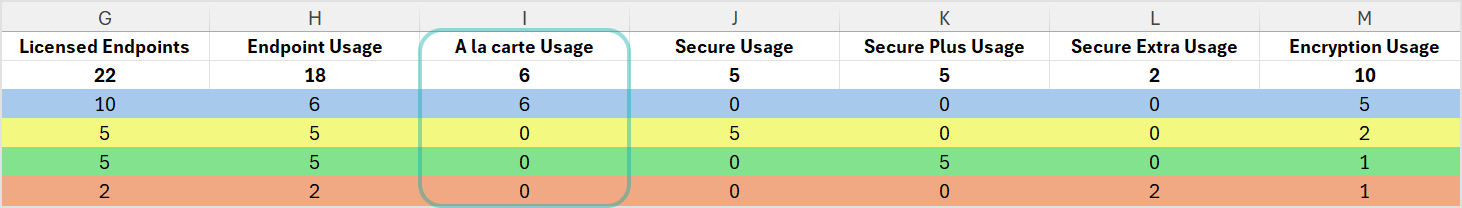
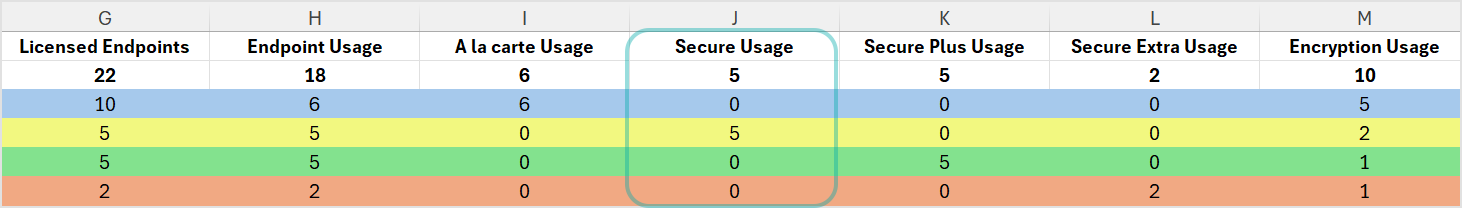
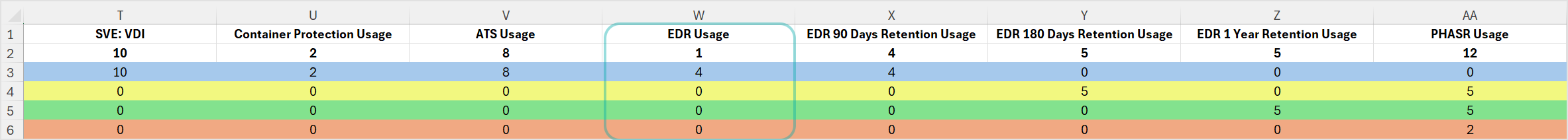
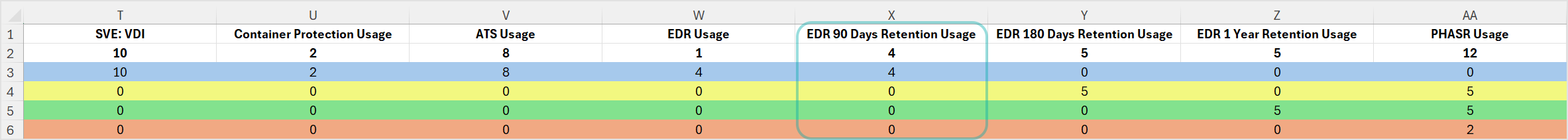
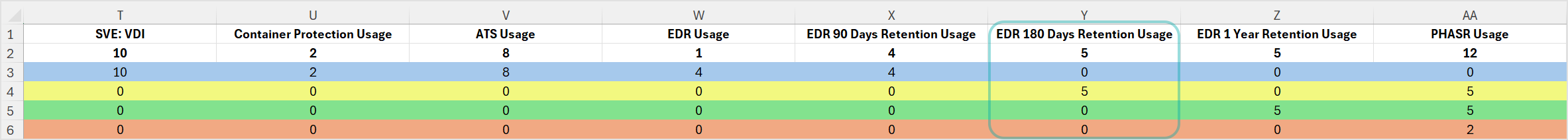
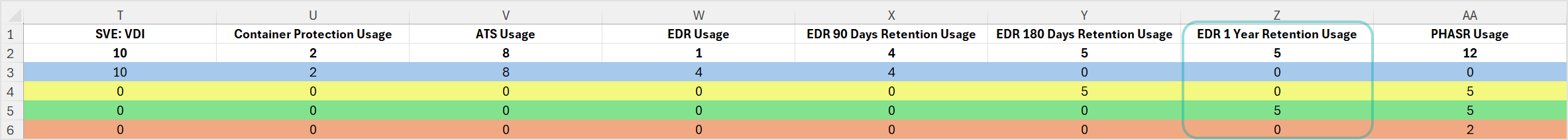
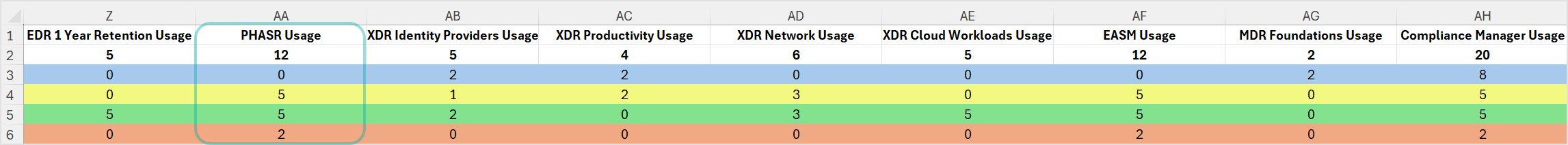
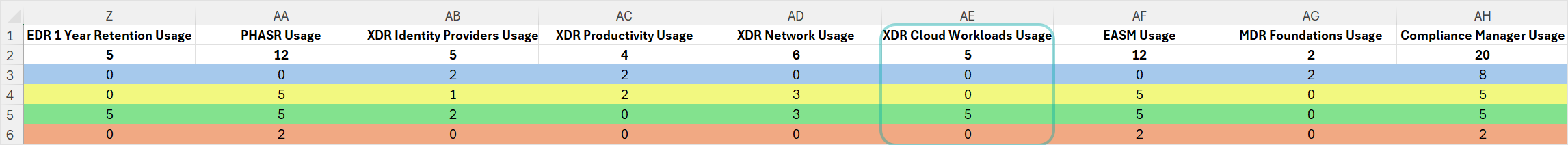
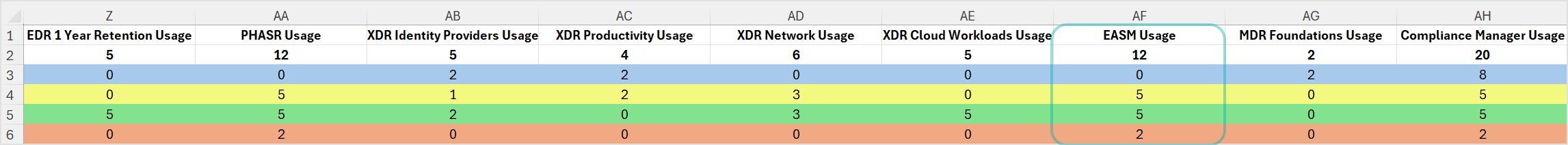
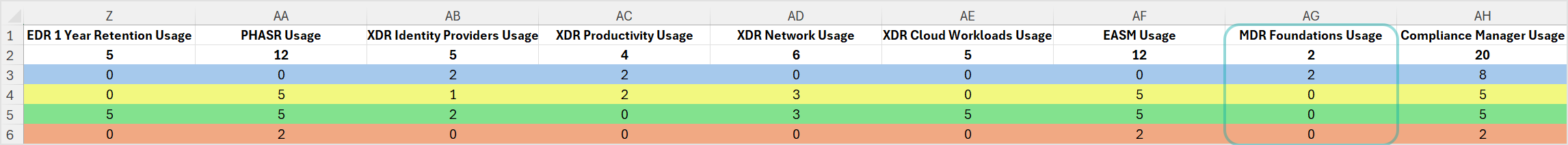
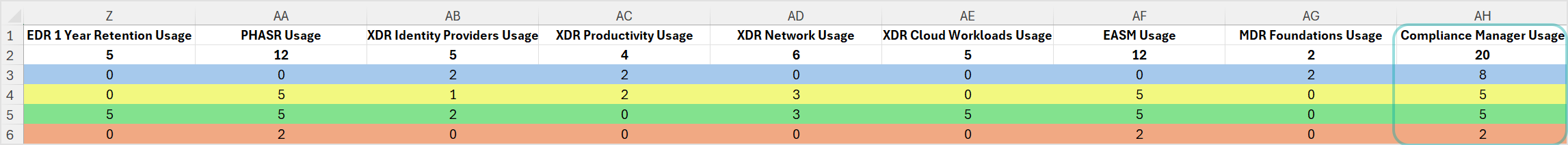
Example of a monthly usage report
In a Monthly License Usage report, you have the following data presented in the CSV file. For enhanced clarity and readability, we have provided a visually improved CSV version. The columns are expanded, displaying clear header titles, and each company's information is presented in a distinct color, making it easier to comprehend and navigate the data:
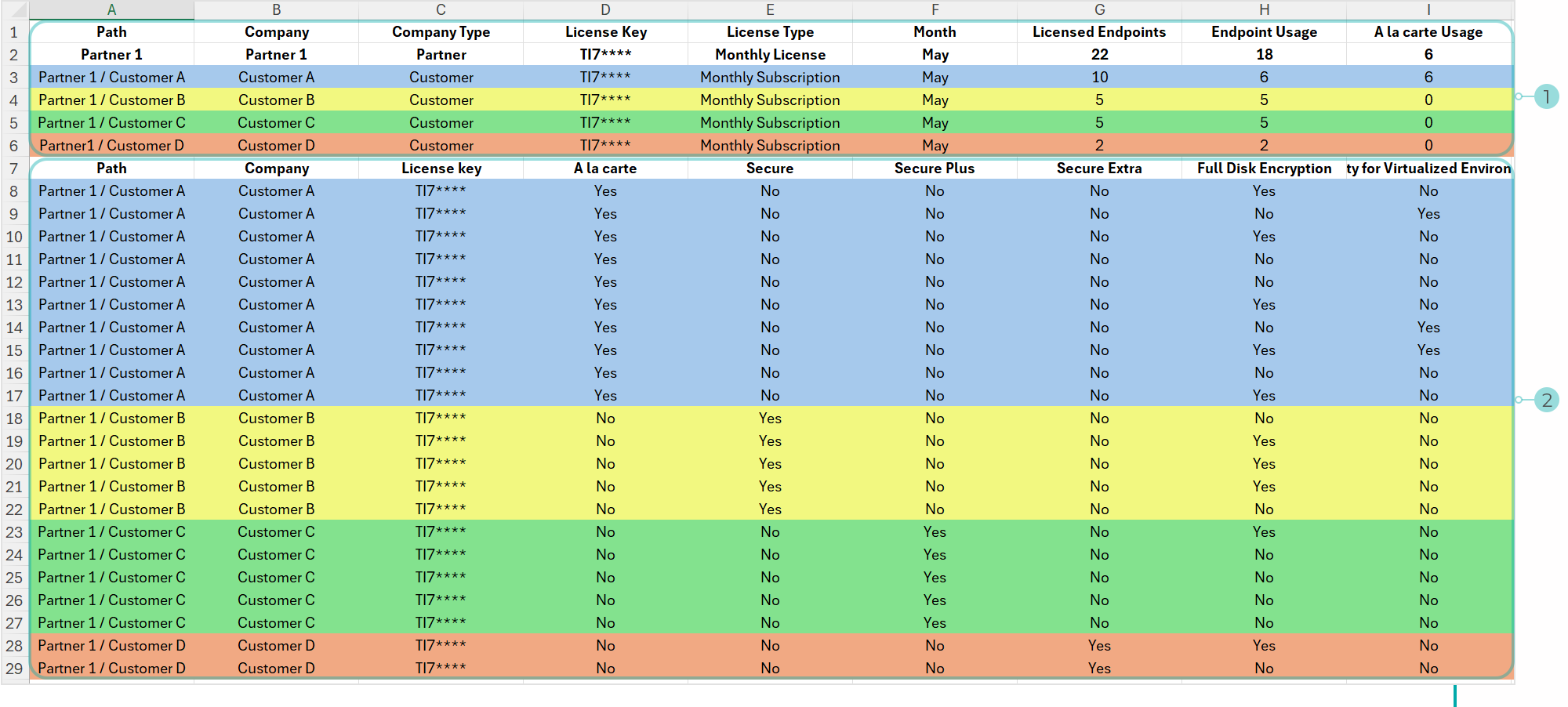
Click here to download the visually improved version of the file.
The CSV version of the report is split into two sections:
The Usage section - this area provides a list of managed companies, and related information such as company settings, licensing information, the number of licensed endpoints and usage totals for add-ons and services.
Note
The license usage for some companies for specific add-ons will not be recorded and will be shown as
0if the product is included in the protection model assigned to the company's own use.The Endpoint details section - this area provides a list of endpoints managed by each company, and related information such as endpoint type, operating system, hardware ID, IP, and usage information.
Usage for companies with Bitdefender EDR
The usage is counted based on the number of endpoints that have used Bitdefender EDR during the month.
To get the usage, generate the Monthly License Usage report again with Bitdefender EDR as product type.
In the CSV file, the number of the endpoints is available in the Endpoint Usage column.
Example of a monthly usage report
In a Monthly License Usage report generated for Bitdefender EDR, you have the following data presented in the CSV file:
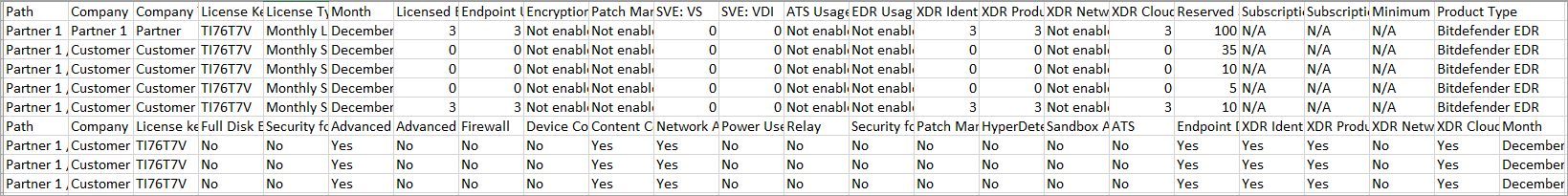
Click the image to view it larger. Click here to download the above CSV file.
The data indicates the following companies:
Partner 1 – Partner company with monthly license and Endpoint Security as product type. Additionally, Partner 1 assigned Bitdefender EDR to its child companies.
Customer A – Customer company under Partner 1, with monthly subscription and Endpoint Security as product type.
Customer B – Customer company under Partner 1, with monthly subscription and Endpoint Security as product type.
Customer C – Customer company under Partner 1, with monthly subscription and Endpoint Security as product type.
Customer D - Customer company under Partner 1, with monthly subscription and Bitdefender EDR as product type.
The usage for Customer A, Customer B, and Customer C is zero, because all these companies use Endpoint Security.
The usage for Customer D, which uses Bitdefender EDR, is 3, as indicated in the Endpoint Usage column.
Because only Customer D has Bitdefender EDR usage in this report, the parent company Partner 1 indicates the same usage.
The CSV file also includes the endpoints list with the following usage per module: Advanced Threat Control, Content Control, Network Attack Defense, and Endpoint Detection and Response. All these modules are part of Bitdefender EDR as product type, so they do no generate additional usage.
Usage for companies with Bitdefender PHASR
The usage is counted based on the number of endpoints that have used Bitdefender PHASR during the month.
To get the usage, generate the Monthly License Usage report again with Bitdefender PHASR as product type.
In the CSV file, the number of the endpoints is available in the Endpoint Usage column.
Example of a monthly usage report
In the Monthly License Usage report generated for the Bitdefender PHASR product type, you have data presented in the CSV file as described below.
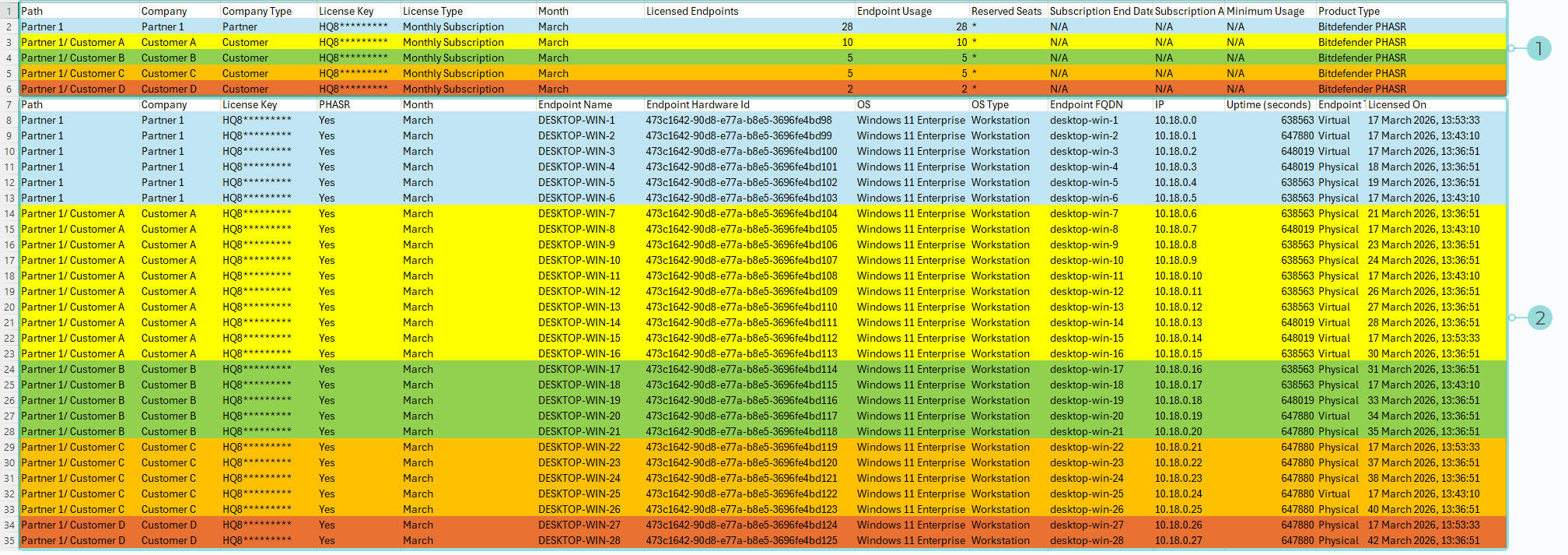
Click the image to view it larger. Click here to download the above CSV file.
Note
In this example, companies are highlighted in different colors for illustration purposes.
The CSV version of the report is split into two sections:
Usage - this section provides a list of managed companies, and related information such as company settings, licensing information, the number of licensed endpoints and usage totals.
Endpoint details - this section provides a list of endpoints managed by each company, and related information such as endpoint type, operating system, hardware ID, IP, and usage information.
Usage explained
The data indicates the following companies:
Partner 1 – Partner company with monthly license and Bitdefender PHASR as product type. Additionally, Partner 1 assigned Bitdefender PHASR to its child companies.
Partner 1 has 6 licensed endpoints, all of which generated usage during March. However, the report shows 28 endpoints because it includes both Partner 1’s 6 endpoints and 22 endpoints from Customer companies managed by Partner 1.
Customer A – Customer company under Partner 1, with monthly subscription and Bitdefender PHASR as product type.
Customer A has 10 licensed endpoints, all of which generated usage during March.
Customer B – Customer company under Partner 1, with monthly subscription and Bitdefender PHASR as product type.
Customer B has 5 licensed endpoints, all of which generated usage during March.
Customer C – Customer company under Partner 1, with monthly subscription and Bitdefender PHASR as product type.
Customer C has 5 licensed endpoints, all of which generated usage during March.
Customer D - Customer company under Partner 1, with monthly subscription and Bitdefender PHASR as product type.
Customer D has 2 licensed endpoints, all of which generated usage during March.
Minimum usage
In GravityZone Control Center, the Monthly License Usage report displays minimum usage in the column with the corresponding name.
In the CSV file, the minimum usage is available in the Minimum usage column.
For details about Bitdefender offering for MSP, refer to Frequently Asked Questions (FAQ) about Bitdefender Cloud Security for MSP.
Create a Monthly License Usage report in GravityZone
This section explains how to create a Monthly License Usage report in GravityZone Control Center or by using APIs.
In GravityZone Control Center
To create a Monthly License Usage report, follow these steps:
Log in to GravityZone Control Center.
Go to the Reports page from the left side menu.
Click Add in the action toolbar.
Under Details, select Monthly License Usage and enter a specific report name, if needed.
Under Settings, configure when the report to be generated, the interval, product type, and delivery by mail, according to your needs.
Select either Now, to instantly generate the report, or Scheduled, to set up a report to run periodically, at a specified time and date.
Under Reporting interval select the interval of time you would like to gather data from. This setting is based on the date the report is generated.
Under Product type, select the type of product you want to generate reports for.
(Optional) Select the Only Endpoint Details checkbox to show only endpoint related information in the report. This will ignore the companies' hierarchy.
(Optional) Select the Only Direct Companies checkbox for the report to include only information from child companies at the first level under the target company.
(Optional) Select the Only New Customer Companies checkbox to include only companies created between two specific dates in the report. When selected, these options appear below:
Company registration start date - only companies created after this start date will be included in the report.
Company registration end date - only companies created before this date will be included in the report.
Important
You must fill in both fields, otherwise no information will be included in the request.
Under Delivery, select the format of the report and if you want to send it via e-mail.
Under Select Target, select the companies you are interested in.
Click Generate.
To obtain the CSV file, follow these steps:
Generate a Monthly License Usage report.
In the report page, click Export CSV.
Choose Export details in csv.
Select to open or to save the file when prompted by the web browser and confirm.
By using GravityZone APIs
You can obtain the Monthly License Usage report and its CSV file by calling certain API methods:
Make a request for
createReport.Parameters:
"type": 13(Monthly License Usage report)"targetIds": [string](your own company ID or other companies)
Options:
"reportingInterval": 4(for the last month)"skipSummary": true. The report will contain only the details. To include the summary, choosefalse.
The response will return a result containing a string.
Make a request for
getDownloadLinksusing the string asreportIdparameter.The response will contain the downloading link for the report.
Examples
Request createReport:
{
"params": {
"name": "reportName",
"type": 13,
"targetIds": [
"5a8d349fb1a43d4d19f7ccc9"
],
"options": {
"reportingInterval": 4,
"skipSummary": true
}
},
"jsonrpc": "2.0",
"method": "createReport",
"id": "e249c22c-0ada-4772-a9f1-ee1cbb322588"
}
Response createReport:
{
"id": "e249c22c-0ada-4772-a9f1-ee1cbb322588",
"jsonrpc": "2.0",
"result": "5aa246f4b1a43db6152b95af"
}
Request getDownloadLinks:
{
"params": {
"reportId": "5aa246f4b1a43db6152b95af"
},
"jsonrpc": "2.0",
"method": "getDownloadLinks",
"id": "e249c22c-0ada-4772-a9f1-ee1cbb322588"
}
Response getDownloadLinks:
{
"id": "e249c22c-0ada-4772-a9f1-ee1cbb322588",
"jsonrpc": "2.0",
"result": {
"readyForDownload": true,
"lastInstanceUrl": "http://192.168.33.20:8221/api/v1.0/http/downloadReportZip?reportId=5aa246f4b1a43db6152b95af&allInstances=0"
}
For details regarding the API methods regarding the license usage in GravityZone Cloud, refer to the GravityZone API Guide for Partners, specifically to these methods:
Companies –
createCompanyLicensing –
getLicenseInfoLicensing –
setMonthlySubscriptionLicensing -
getMonthlyUsageReports –
createReport
To learn how to calculate the monthly license usage, refer to Calculate the endpoint usage with the Monthly License Usage report.