Authentication
Fill in the information in the required fields.
Note
Fields marked with * are mandatory.
Two-factor authentication
Enforce two-factor authentication (Recommended)
Two-factor authentication (2FA) adds an extra layer of security to GravityZone accounts, by requiring an authentication code in addition to Control Center credentials.
2FA requires downloading and installing the Google Authenticator, Microsoft Authenticator, or any two-factor TOTP (Time-Based One-Time Password Algorithm) authenticator app - compatible with the standard RFC6238 - on the user's device. The device can be a smartphone or a computer.
The authentication app generates a six-digit code each 30 seconds. To complete the Control Center login, after entering the password, the user will have to provide also the six-digit authentication code.
Two-factor authentication is enabled by default when creating a company and this setting cannot be changed. At login, a configuration window prompts users to enable this feature. Users have the option to skip enabling 2FA for five times only. At the sixth login attempt, skipping the 2FA configuration is no longer possible and users are not allowed to log in.
Users trust their browsers. This option allows you to specify the period during which GravityZone remembers the browsers used for logging in to Control Center:
Select Never for users to enter the six-digit code from their authenticator every time they log in.
Select 1 to 90 days to allow users to skip entering the six-digit code for that specific period and log in directly to Control Center. To enable this option, users must also to select the Trust this browser check box on the GravityZone login screen.
By default, one browsers corresponds to one device such as a computer. If users log in from another browser than the one remembered, they have to enter the six-digit code from authenticator. For details on scenarios where the Trust this browser option does not work, refer to this topic.
Note
You can view the 2FA status for a user account in the Accounts page.
If users cannot log in to GravityZone because of they a new device (phone or computer) or lost secret key, you can reset its two-factor authentication activation from the user account page, under Two-factor authentication section. For more details, refer to User Accounts.
Changing the period for remembering device reflects in user activity section of Control Center.
Regarding the public API,
skip2FAis the parameter corresponding to Trust this browser option, used withcreateCompanyandupdateCompanyDetailsmethods. For details on how to use it, refer to createCompany and updateCompanyDetails.
Password expiry options
Set maximum password age to 90 days
This option enables the password expiration policy. Users need to change their passwords sooner than the specified age. Otherwise, they will not be able to log in to GravityZone anymore.
Lock out account after 5 login attempts with invalid passwords
This option limits the number of consecutive invalid passwords to prevent attacks. When the counter reaches the threshold, the account is locked out and the user needs to reset their password.
The policy applies to the accounts created in GravityZone.
A notification will be sent out to all company’s users when the account lockout option is being enabled on a certain company.
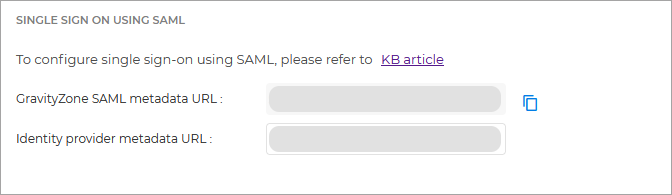
Configure single sign-on using SAML
GravityZone supports service provider(SP) initiated single sign-on (SSO) as a simple and secure alternative to the classic login with username and password.
This method requires integration with third party identity providers (IdP) that uses SAML 2.0 to authenticate GravityZone users and to provide them access to Control Center. Such IdP are AD FS, Okta, and Azure AD.
This is how GravityZone SSO works:
The users enters their email address in the GravityZone login page.
GravityZone creates a SAML request and forwards it to the IdP. It also redirects the user to the identity provider authentication page.
Users are required to authenticate with the identity provider.
The identity provider sends a response to GravityZone in the form of an XML document signed with an X.509 certificate. Also, the identity provider redirects users to GravityZone.
GravityZone retrieves the response, validates it with the certificate fingerprint, and allows users to log in to Control Center with no other interaction from them.
Users continue to automatically log in to Control Center as long as they have an active session with the identity provider.
To enable SSO for a company, you need to follow these steps:
Configure the identity provider to use GravityZone as service provider. For supported identity providers and configuration details, refer to this article.
In the company details page, under Configure single sign-on using SAML, enter the identity provider metadata URL in the corresponding field.
Note
The GravityZone IdP Proxy metadata URL field is currently not used by Bitdefender services. Support for third-party identity providers will be introduced in future releases.
Configure users under the company to authenticate with their Identity Provider. For details, refer to Configuring single sign-on using a 3rd party identity provider.
To disable single sign-on for a company you manage, delete the identity provider metadata URL.
After disabling single sign-on for a company, users will automatically switch to log in with GravityZone credentials. Users can obtain new passwords by clicking the Forgot password? link on the Control Center login page.
After re-enabling SSO for a company, users will continue to log in to Control Center with GravityZone credentials. You need to configure manually each account to use SSO again.
Note
Click the Next button in the lower right side of the screen to proceed to the next screen.
Important
You cannot use at the same time single sign-on (SSO) and two-factor authentication (2FA) in GravityZone.