Configuring GravityZone Cloud single sign-on with Okta
GravityZone Cloud supports single sign-on (SSO) with various Identity Providers (IdP) that use SAML 2.0 as authentication standard.
This topic describes how to configure GravityZone Cloud single sign-on with Okta. For generic information on configuring other Identity Providers, refer to Configuring single sign-on using a 3rd party identity provider.
Prerequisites and requirements
You have an Okta account to create, activate and assign applications to users.
You have a GravityZone Cloud administrator account to manage users, your company and other companies.
GravityZone users have Okta accounts with the same email addresses.
Important
As GravityZone administrator, you can configure single sign-on for users from your company and from companies under your management. You cannot enable SSO for your own GravityZone account due to security reasons.
Users must be under companies that have SSO enabled. While SSO is active, users cannot log in with GravityZone credentials.
Email addresses are case sensitive with GravityZone SSO. Therefore, username[at]company.domain is different from UserName[at]company.domain and USERNAME[at]company.domain. If the email address from GravityZone does not match the email address from the Identity Provider, the user will receive a login error message when trying to connect to Control Center.
Configure Okta
GravityZone single sign-on requires an Okta application that will connect the two platforms.
This is how you configure an Okta application:
Extract the GravityZone SAML metadata using the following steps:
Sign in to Bitdefender GravityZone as an administrator.
Click your user name in the upper right side of the screen and select My Company.
Go to the Authentication tab.
Under the Single sign on section, click the
 button next to the SINGLE SIGN ON USING SAML field to copy the metadata URL.
button next to the SINGLE SIGN ON USING SAML field to copy the metadata URL.Open the metadata URL in a separate tab of your browser and save the page as a metadata.xml file.
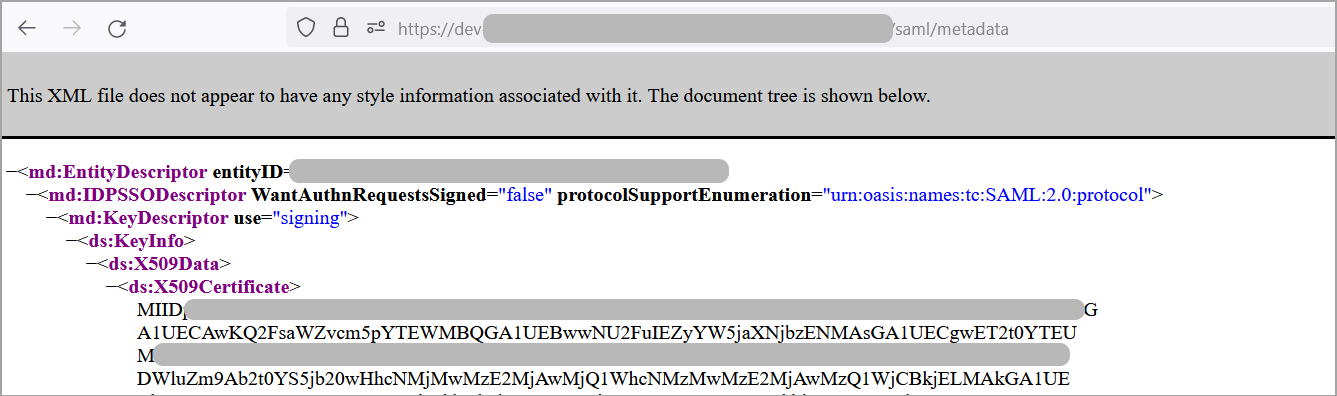
Open the metadata.xml file you saved in the previous step.
Copy the
<ds:X509Certificate>...</ds:X509Certificate>value as shown below and paste it into a text editor.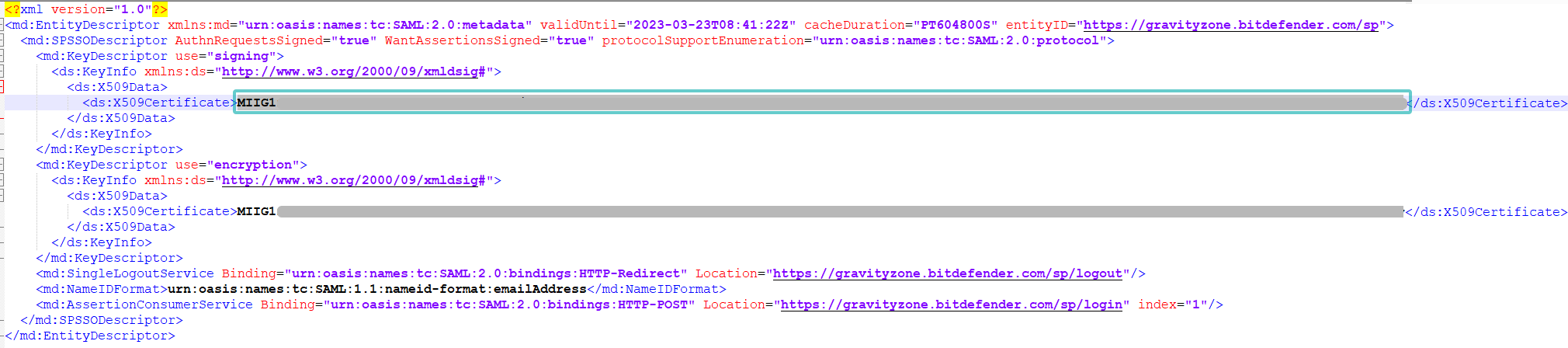
Add the following lines at the beginning and end of the file:
-----BEGIN CERTIFICATE-----
-----END CERTIFICATE-----
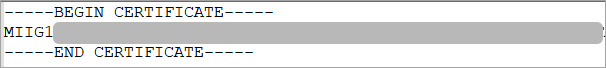
Save the file you created as
certificate.cer.
Log in to Okta.
From your profile dropdown menu, go to My settings and then select the Admin section.
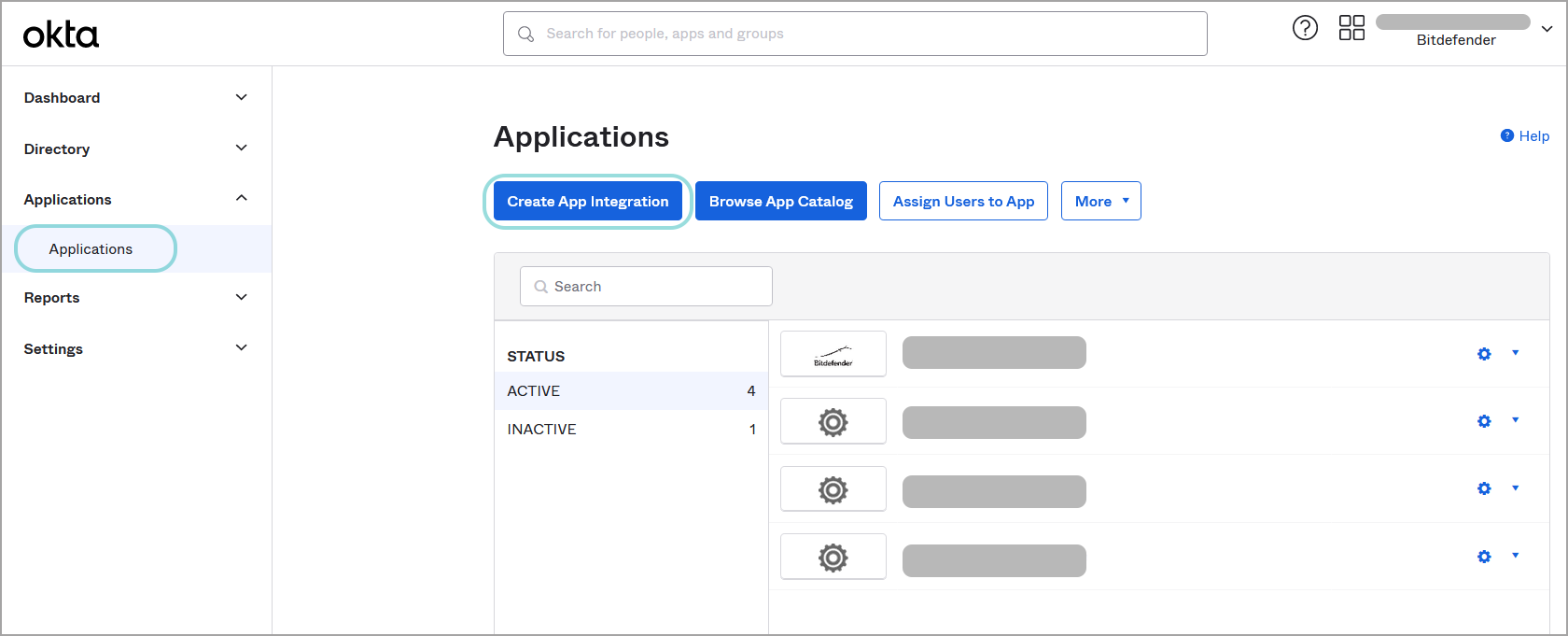
Go to the Applications section and click Create App Integration.
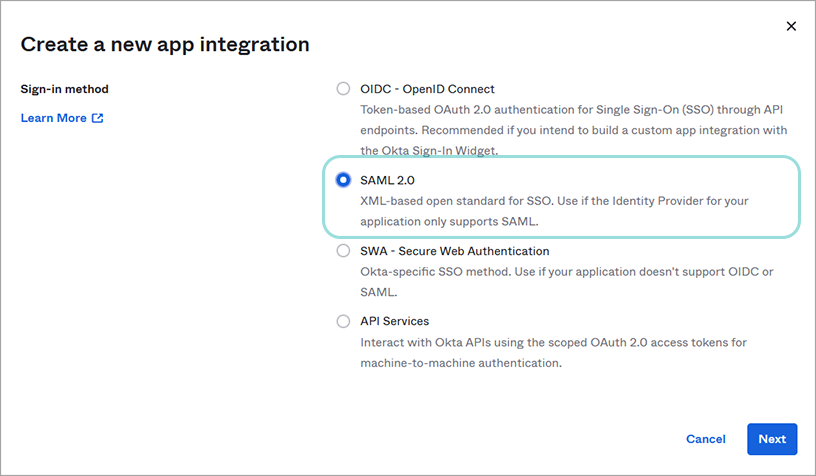
In the Create a new app integration window, select SAML 2.0 as sign-in method, and click Next.
On the Create SAML Integration page, apply the following configuration:
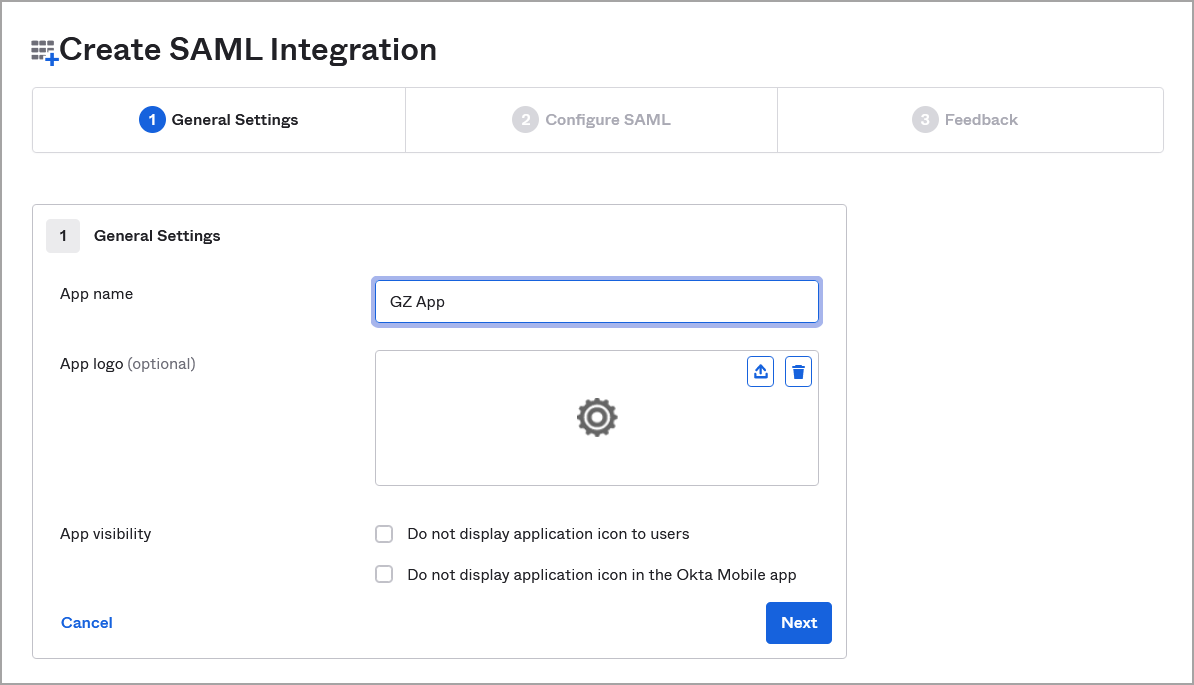
Under the General Settings tab, apply the following configuration:
Enter an app name (for example, GZ App).
(optional) Upload a logo image and set your app’s visibility.
Click Next.
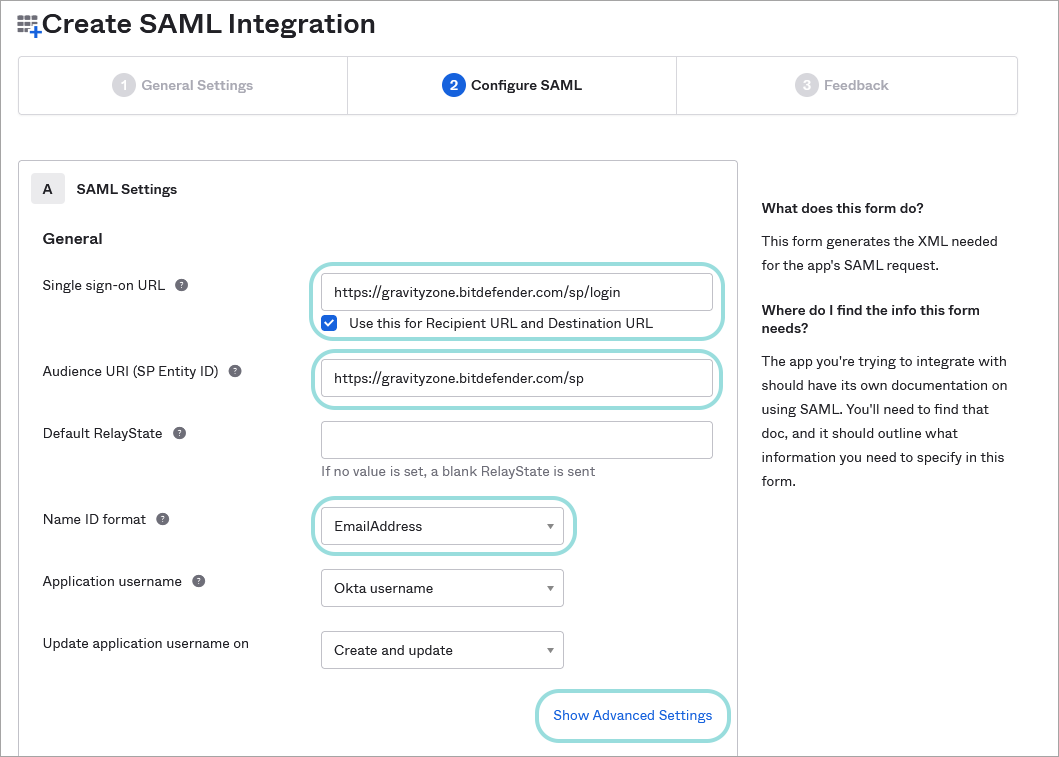
Under Configure SAML, follow the steps below:
Under Single sign on URL, enter
https://gravityzone.bitdefender.com/sp/loginand select the check box for Use this for Recipient URL and Destination URL.Under Audience URL (SP Entity ID), enter
https://gravityzone.bitdefender.com/spFor Name ID format, select EmailAddress.
Click the Show Advanced Settings link.
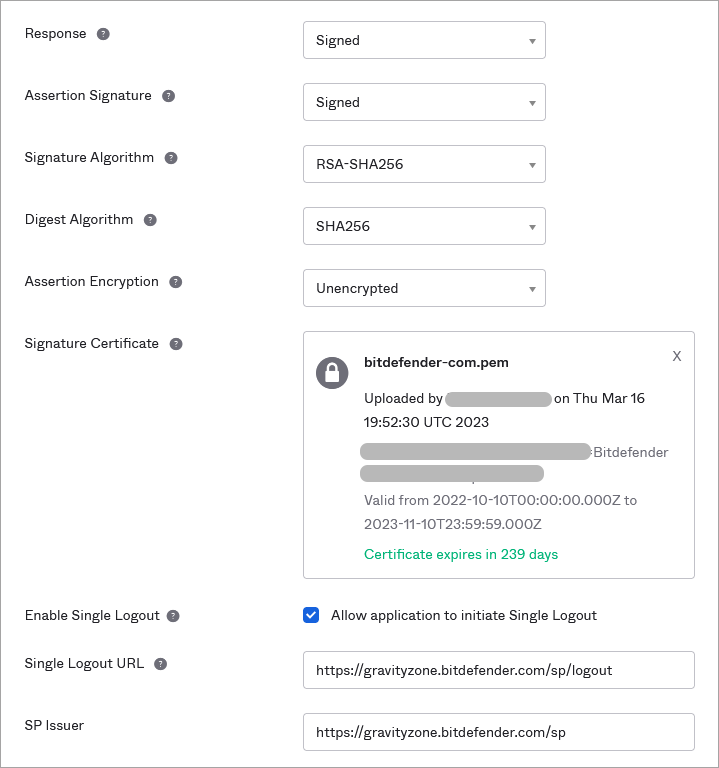
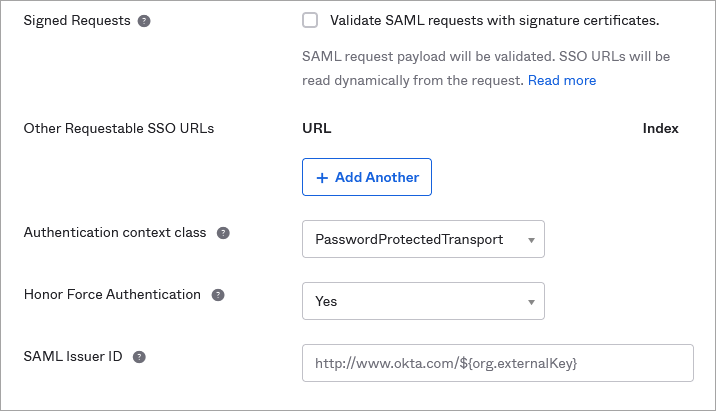
Apply the following configuration:
For Response, select Signed.
For Assertion Signature, select Signed.
For Signature Algorithm, select RSA-SHA256.
For Digest Algorithm, select SHA256.
For Assertion Encryption, select Unencrypted.
Under Signature Certificate, upload the GravityZone certificate obtained at step 1.
For Enable Single Logout, select the check box for Allow application to initiate Single Logout to display new options.
Under Single Logout URL, enter
https://gravityzone.bitdefender.com/sp/logoutUnder SP Issuer, enter
https://gravityzone.bitdefender.com/spFor Authentication context class, select PasswordProtectedTransport.
For Honor Force Authentication, select Yes.
For SAML Issuer ID, leave the default value:
http://www.okta.com/${org.externalKey}.Leave the rest of the fields blank, including Attribute Statements (optional) and Group Attribute Statements (optional).
Important
Make sure you have entered all the above data and uploaded the GravityZone certificate before proceeding further.
Click Next.
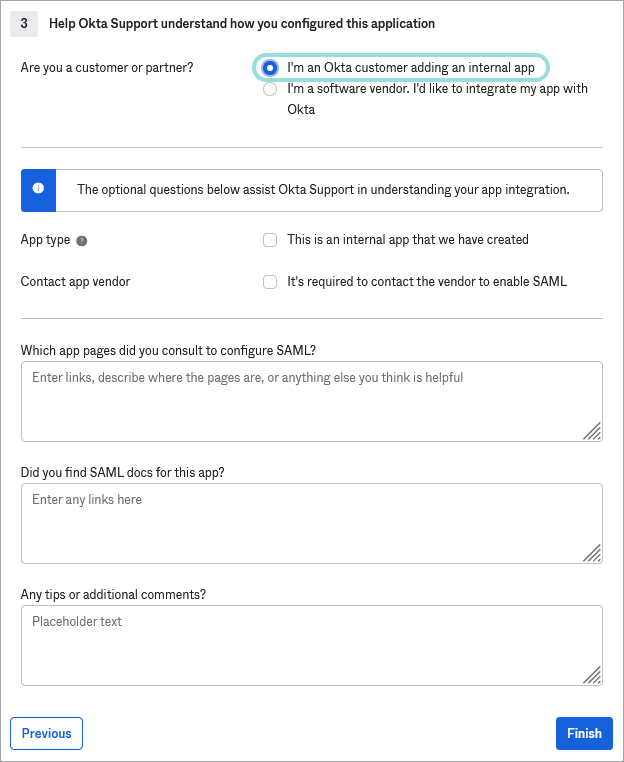
Under Feedback, select I'm an Okta customer adding an internal app and click Finish.
After finishing the configuration, Okta will redirect you to a page containing details about the application you have created.
In the Sign On tab, click the Copy button under the Metadata details section.
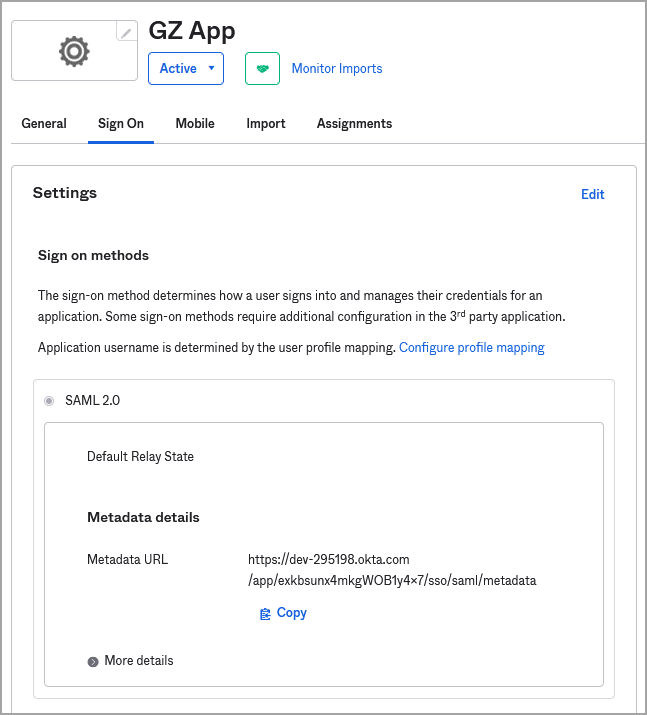
This will copy a URL of the XML file which contains the Metadata details that you have to paste in GravityZoneControl Center to enable SSO. Keep it at hand for future use.
Note
You can paste the URL into a browser window to display the file:
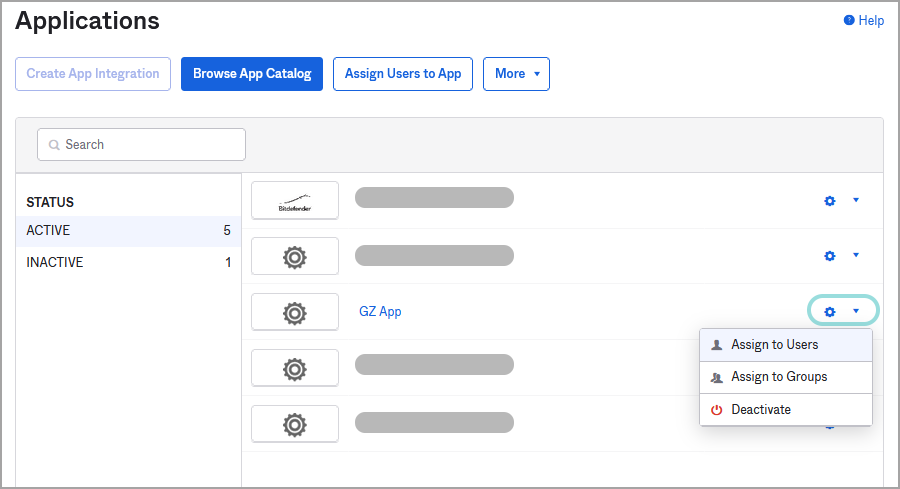
Go to the Applications page in Okta to view the status of your application. The application must be active.
Click the configuration button to assign users, user groups, or to deactivate the application.
Enable SSO in GravityZone
After configuring single sign-on in Okta, go to GravityZone Control Center to enable SSO for companies and users. Only users under a company with SSO enabled have the option to log in with an Identity Provider.
Enable SSO for your company
This is how you enable SSO for your company:
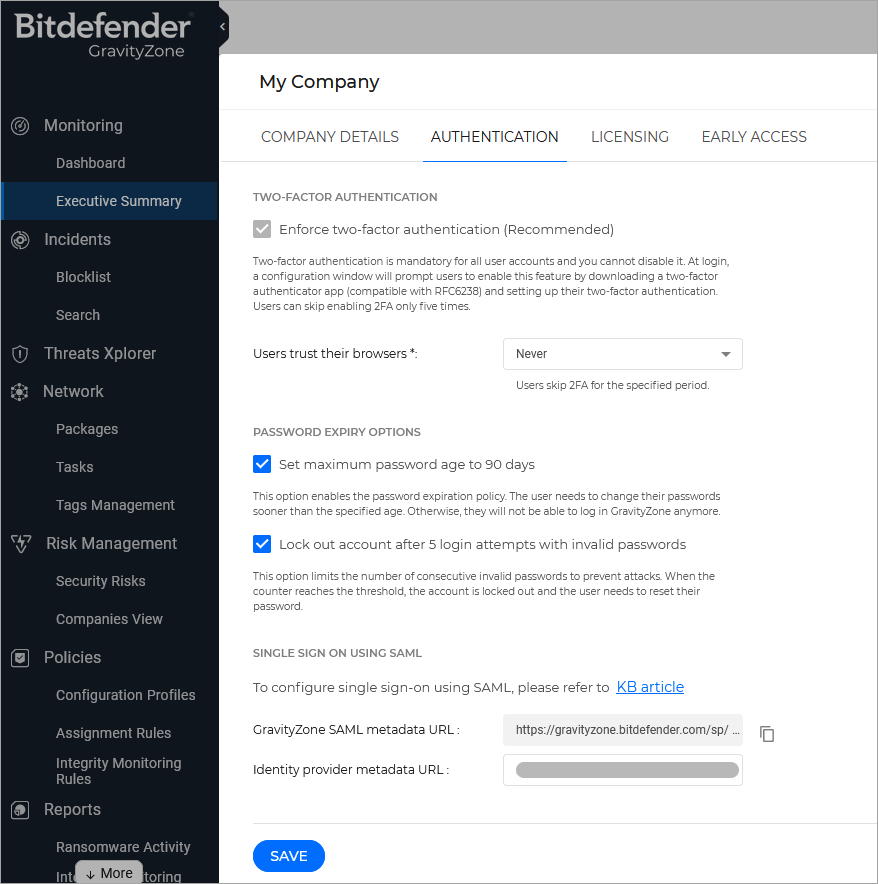
In the upper-right corner of Control Center, click the
 user icon and then select My Company.
user icon and then select My Company.In the Authentication tab, under Single Sign on using SAML, enter the identity provider metadata URL in the corresponding field. The other field, reserved for the GravityZone metadata URL, is non-editable.
Click Save.
Enable SSO for managed companies
This is how you enable single sign-on for a company under your management:
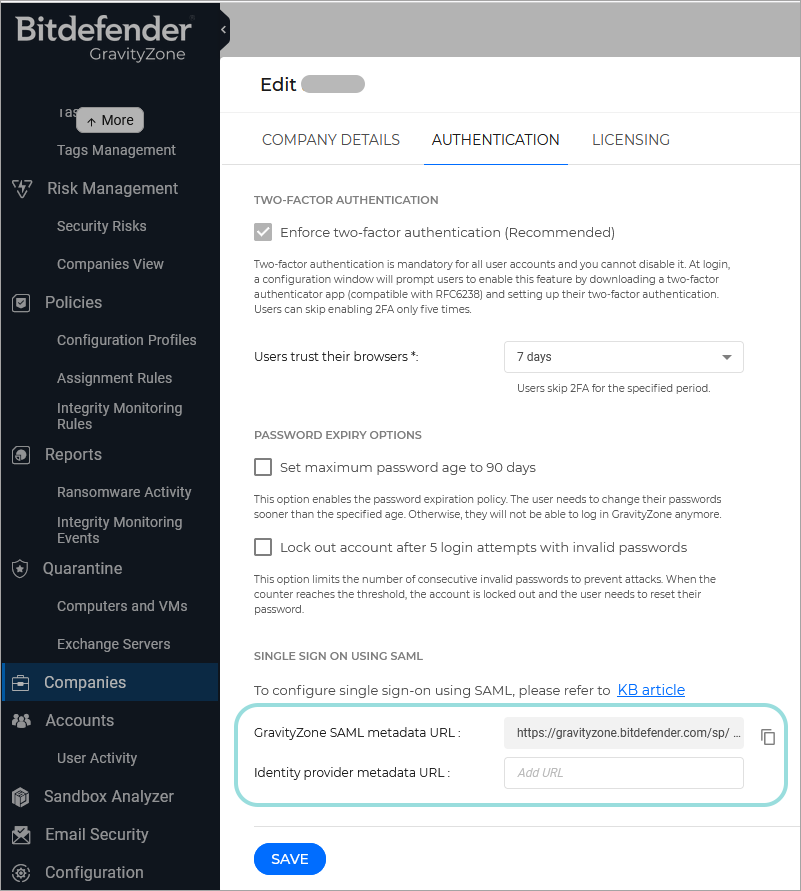
Log in to GravityZone Control Center.
Go to the Companies page from the left side menu.
In the table, click the company’s name.
Under Configure Single Sign-on using SAML, enter the identity provider metadata URL in the corresponding field. The other field, reserved for the GravityZone metadata URL, is non-editable.
Click Save.
Change the authentication method for users
After enabling SSO for a company, GravityZone user accounts under that company become available for changing their authentication method.
You can change the authentication method for users one by one, as follows:
Log in to GravityZone Control Center.
Go to the Accounts page from the left side menu.
In the table, click the user’s name.
Under Login Security, go to Authentication method and select Login using your Identity Provider.
Click Save.
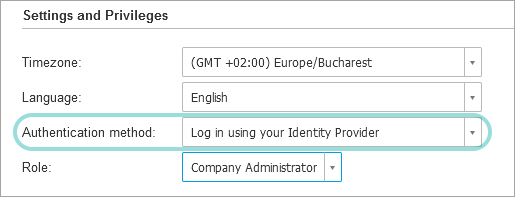
You can enable SSO for as many GravityZone users as you want, but not for your own administrator account.
Note
If the configuration page of a GravityZone user account does not display the Settings and Privileges section, then probably the company has not SSO enabled.
Test GravityZone SSO
After configuring both the identity provider and GravityZone, you can test single sign-on as follows:
Log out from GravityZone.
Log out from Okta.
Go to https://gravityzone.bitdefender.com/.
Note
GravityZone SSO does not support IdP initiated login, but only service provider initiated login. Therefore, you can test the single sign-on by going to the GravityZone console (Control Center), not by clicking the application's logo in Okta.
Enter a valid email address created for testing (other than the one of your GravityZone administrator account).
Click Next.
You should be redirected to the Identity Provider's authentication page.
Authenticate with your identity provider.
You will be redirected back to GravityZone and, in a few moments, you should automatically log in to Control Center.
Disable GravityZone SSO
To disable single sign-on for your company or for a company under your management:
Delete the Identity Provider metadata URL from the configuration page of that company.
Click Save and confirm the action.
Users can obtain new passwords by clicking the Reset my password option on the Control Center login page and following the instructions.
To re-enable GravityZone SSO for a company, enter again the identity provider in the configuration page and click Save.
After re-enabling SSO, users under that company will continue to log in to Control Center with GravityZone credentials. You have to manually configure each account, one by one, to log in with the identity provider again.