Security management
In GravityZone, you can use security policies and perform tasks to protect your network inventory. On this page, you learn what are policies and tasks, and why they are important to you as GravityZone user.
Further, this documentation section covers the following topics:
Policy flow management in GravityZone (create, configure, assign policies etc,).
Major GravityZone features that you enable through policies, but you operate them mostly outside policies. Such features refer to EDR/XDR, Risk Management, Integrity Monitoring, and the quarantine.
Best practices and troubleshooting articles on GravityZone features enabled through policies.
See the list with specific topics at the end of this page.
Understanding security policies
The Bitdefender protection can be configured and managed from Control Center using security policies. A policy specifies the security settings to be applied on computers.
Immediately after installation, network inventory objects are assigned with the default policy, which is preconfigured with the recommended protection settings. You cannot modify or delete the default policy. You can only use it as a template for creating new policies.
You can create as many policies as you need based on security requirements, for each type of managed network object.
This is what you need to know about policies:
Policies are created in the Policies page and assigned to network objects from the Network page.
Policies can inherit several modules settings from other policies.
You can configure policy assignment to endpoints so that a policy can apply at all times or only in certain conditions, based on the location of the endpoint. Therefore, an endpoint can have more policies assigned.
Endpoints can have one active policy at a time.
You can assign a policy to individual endpoints or to groups of endpoints. When assigning a policy, you will also define the policy inheritance options. By default, each endpoint inherits the policy of the parent group.
Policies are pushed to target network objects immediately after creating or modifying them. Settings should be applied to network objects in less than a minute (provided they are online). If a network object is not online, settings will be applied as soon as it gets back online.
The policy applies only to the installed protection modules.
Enabling certain modules in the policy triggers a reconfiguration of the security agent BEST) on the endpoints. This reconfiguration, in turn, initiates an agent update, bringing it to the latest available version or as configured in the policy under General > Agent > Update > Update ring. The modules that trigger these actions are:
Live Search
PHASR (under Risk Management)
Remote Shell (under General > Agent > Communication).
The Policies page displays only the following types of policies:
Policies created by you.
Other policies (such as default policy or templates created by other users) which are assigned to endpoints under your account.
You cannot edit policies created by other users (unless the policy owners allow it from the policy settings), but you can override them by assigning the target objects a different policy.
Warning
Only the supported policy modules will apply to target endpoints.
On Amazon EC2 instances, only Antimalware, Advanced Threat Control and Device Control modules are supported.
Policies page
You can view and manage policies in the Policies page.
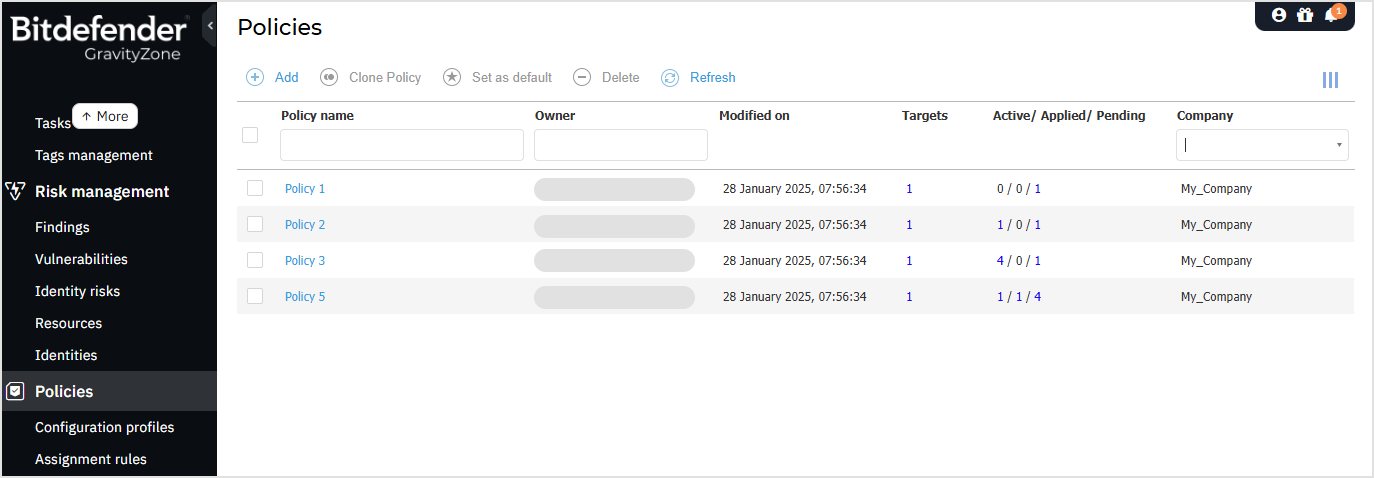
The table presents current policies, showcasing details such as:
Policy name.
Policy owner.
Date and time when the policy was last modified.
In the Targets column, the total number of endpoints and folders where the policy was directly applied.*
In the Active/Applied/Pending column, the number of endpoints where the policy is active, applied or pending. The policy can be directly applied or inherited.*
The company to which the user who created the policy belongs.
Note
* Clicking the number will redirect you to the Network page, where you can view the corresponding endpoints. This action will create a filter using policy criteria.
To customize the policy details displayed in the table:
Click the Columns button at the right side of the Action Toolbar.
Select the columns you want to view.
Click the Reset button to return to the default columns view.
You can sort the available policies and search for certain policies using the available criteria.
Understanding tasks
Besides security policies, you can use actions on the Network page to execute remote operations, or tasks, on endpoints. These tasks include:
For details on how you configure and perform tasks, refer to this section. Once tasks are created, you can monitor their progress in the Network > Tasks page.