Citrix integration guide
Integration with Citrix requires a connection between the Mobile Security console and the Citrix server. This is accomplished through the Internet using SSL. If you use a Citrix SaaS management server, there are no changes that need to occur to allow this communication. For an on-premise Citrix management server, there must be an allowed path for the Security Console to connect to the API Server on the chosen port.
Prerequisite requirements
Item | Specifics |
|---|---|
Citrix MDM enrolled device | V10.3 and above. |
API Administrator Account in Citrix management console. | Create this account. |
MDM Password | Do not use a colon (:) in the MDM password field or use `password` as a password value. |
Ways of protection
Bitdefender Mobile Security integrates with the Citrix MDM and provides the ability to modify device configurations securely over the internet. Two basic methods are used that provide granular protection capabilities
Lock the Device: This prevents unauthorized access to the device during a threat and can help prevent data leakage during network-based attacks.
Remove Managed Apps from the Device: Remove all organizational applications including any company intellectual property.
GravityZone MTD deployment
To access the Bitdefender GravityZone MTD search for the MTD in your app store, or download it to the device by accessing the following links:
To deploy as an enterprise app:
Log in to the Citrix website.
Navigate to Configure and Apps.
Add a new Enterprise Application and upload either of these application files to Citrix:
IPS for IOS
APK for Android
After selecting the GravityZone MTD, assign the Delivery Group to the application and publish it.
The application was successfully published and installed on the devices allocated to the Delivery Group.
Synchronization
Perform these steps on the Citrix website to set up synchronization:
Log in to the Citrix website.
Create a Citrix administrator user.
Navigate to Manage and Users.
Click Add Local user.
Provide a name and description, and choose the ADMIN role. Membership Groups do not need to be selected.
Create one or more Delivery Groups to contain the protected devices if you do not have existing groups. Mobile Security console uses the Delivery Group(s) to synchronize users and devices.
Perform these steps on Bitdefender Mobile Security console Mobile Security console to set up synchronization:
Set up user and device synchronization in Mobile Security console
To set up the MDM integration in Mobile Security console:
Log in to Mobile Security console.
Go to the Manage page.
Select Integrations.
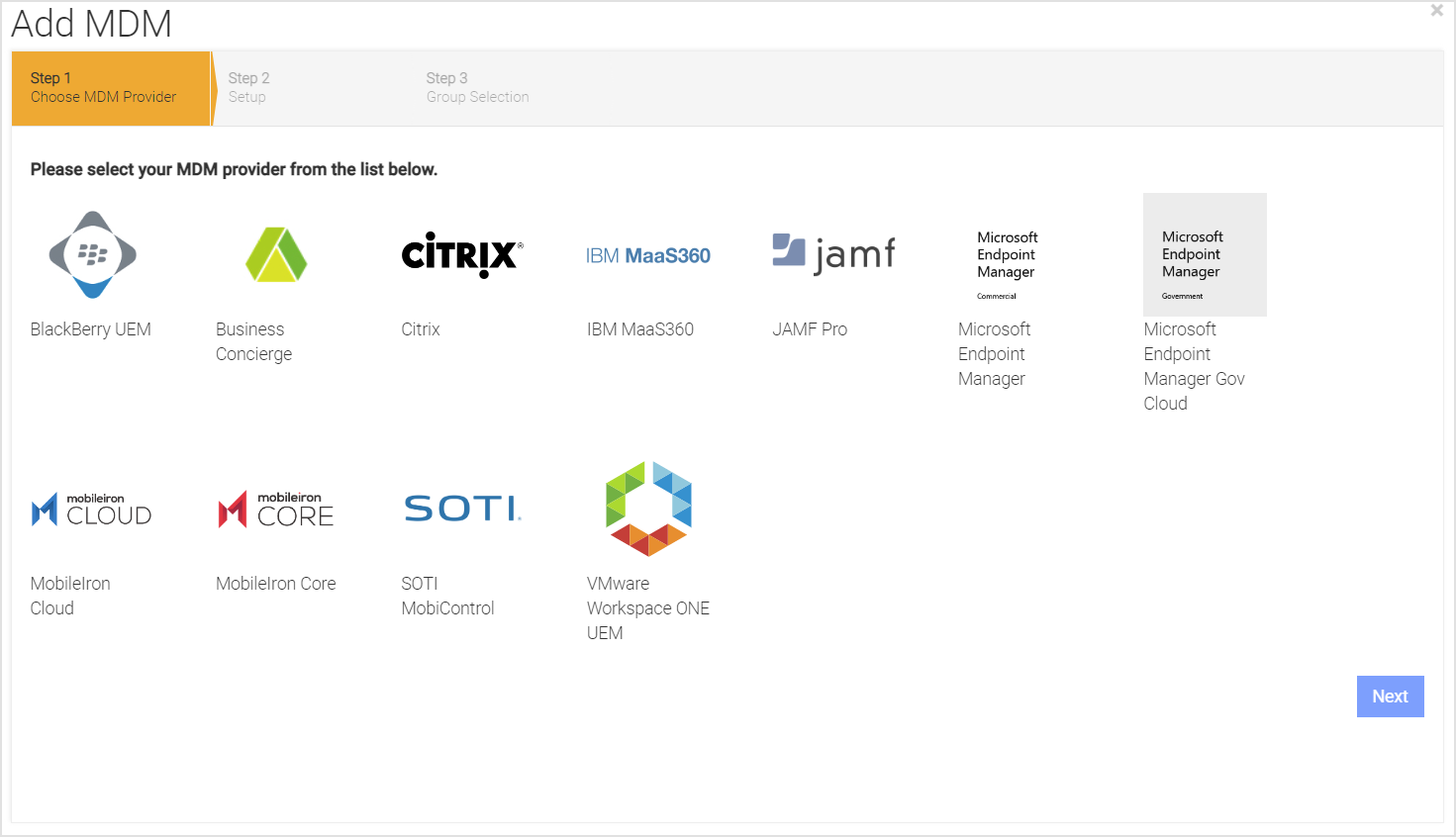
Click on Add MDM and select the MDM integration you want to use.
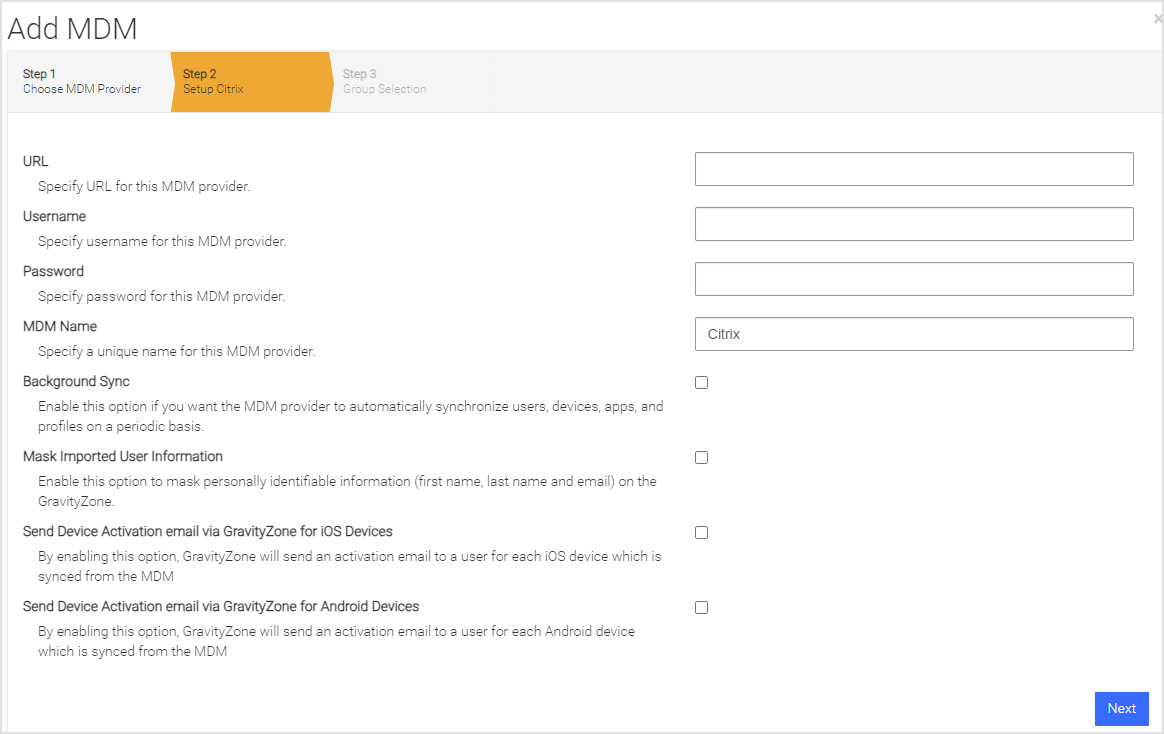
Enter information pertinent to the UEM integration list in the table, and click Next.
Item
Specifics
URL
This is the URL of the Citrix API Server.
Username
This field is the Citrix Administrator created with the API REST Role Access.
Password
The password that the Citrix Administrator created.
MDM Name
The name used in Mobile Security console to reference this MDM integration. This value is prepended to the group name to form the Mobile Security Console group name. This value defaults for you.
Background Sync
Check this box to ensure users and devices are synchronized with the Citrix Delivery Groups chosen on the next page.
Mask Imported Users
Information
Check this box to mask personally identifiable information about the user when displayed, such as name and email address.
Send Device Activation email via Mobile Security console for iOS Devices
Check this box to send an email to the user for every iOS device synced with the MDM.
Send Device Activation email via Mobile Security console for Android Devices
Check this box to send an email to the user for every Android device synced with the MDM.
Click Next and choose the User Group(s) to synchronize. The available groups show up in the Available Device Groups list and can be moved to the Selected Mobile Security console Groups list by clicking on the plus sign (‘+’). This can be reversed by clicking on the minus sign (‘-’).
Click Next.
Specify the MDM alerts if you want to be notified when there are MDM sync errors. If you want more than one email address, separate them by a comma.
Click Finish to save the configuration and start the first synchronization by clicking Sync Now.
Auto activation/advanced application deployment
The GravityZone MTD, in both iOS and Android Enterprise, can auto-activate. The process is different on each platform, as described below.
iOS
When the GravityZone MTD is delivered to the device, the iOS GravityZone MTD makes use of the configuration variables supplied to it from a PLIST file. This gives the optimum user experience by allowing the user to launch iOS GravityZone MTD without entering any passwords. The application configuration populates iOS GravityZone MTD with the necessary information. Make a file that contains these variables.
Configuration Key | Value Type | Configuration Value | Additional Notes |
|---|---|---|---|
MDMDeviceID* | String | $device.uniqueId | |
tenantid | String | Retrieve from Mobile Security console | Copy the value from the Tenant ID field on the Mobile Security console Manage page under the General tab. |
defaultchannel | String | Retrieve from Mobile Security console | Copy the value from the Default Channel field on the Mobile Security console Manage page under the General tab. |
tracking_id_1 | String | Use the desired identifier | (Optional) This field is a tracking identifier. |
tracking_id_2 | String | Use the desired identifier | (Optional) This field is a tracking identifier. |
display_eula | String | No | (Optional) If this key is not used, the default displays the End User License Agreement (EULA). |
Use the value in the table when configuring Citrix Endpoint Management Cloud. If you are using an on-premise configuration for the Citrix XenMobile console, then use the $device.id value for the MDMDeviceID value. See “About Citrix Consoles” for more information.
Note
The configuration keys are case-sensitive.
Set up this configuration within Citrix through iOS Configuration Policies by performing these steps:
Navigate to Configure > Device Policies > Add.
Click on More and select App Configuration under Apps.
Provide a name for this policy and write a description (optional). Then, click Next as seen in the figure.
In the dropdown next to the ‘Identifier’ field, select Add New and fill in the information.
Add the PLIST info for your environment in the ‘Dictionary content’ field. The PLIST info is not in full XML format and has no XML headers
Click on Check Dictionary to verify that you have formatted it correctly.
Click Next to continue.
Select all that apply under Choose delivery groups drop-down list to which this policy should apply.
Click Save.
Android activation
Android Enterprise users can use the managed app configuration for activations. You need to make sure you pass the right device identifier value for the configuration parameter. The variables are the same set as the PLIST variables in the “iOS Activation” section.
For native Android devices, activations require the use of activation URLs. These can be sent to end-users through the Mobile Security console or the MDM. Clicking on the GravityZone MTD without the link does not activate the GravityZone MTD for Android devices. When a user runs the GravityZone MTD with the activation URL link, it activates and downloads the proper Threat Policy.