Ransomware Mitigation
Ransomware Mitigation is a feature designed to mitigate the impact of an active ransomware attack.
When a file is encrypted the randomness (or entropy) of the file goes up significantly. Ransomware Mitigation monitors for this increase in entropy of files on the disk, and during write attempts. When a request is made to encrypt a file (an increase of randomness over a certain limit), a temporary backup is created in memory and the original file is restored after the file changes are done. Importantly this method does not rely on the Volume Shadow Copy service or other static backup solutions, as this backup data is almost always deleted by threat actors. Requests to delete shadow copies are one of the triggers for an EDR incident. Using this approach, we provide ransomware mitigation even against previously unseen ransomware variants.
Ransomware Mitigation uses detection and remediation technologies to keep your data safe from ransomware attacks. Whether the ransomware is known or new, GravityZone detects abnormal encryption attempts and blocks the process. Afterwards, it recovers the files from backup copies and restores them to their original location.
Install and configure Ransomware Mitigation
Configure and enable the feature
To configure Ransomware Mitigation:
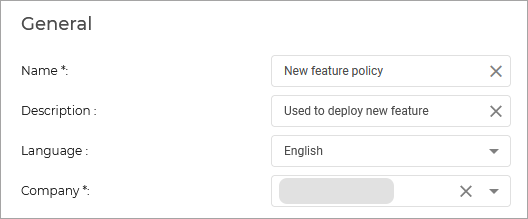
Log in to GravityZone Control Center.
Go to the Policies page from the left side menu.
You can either:
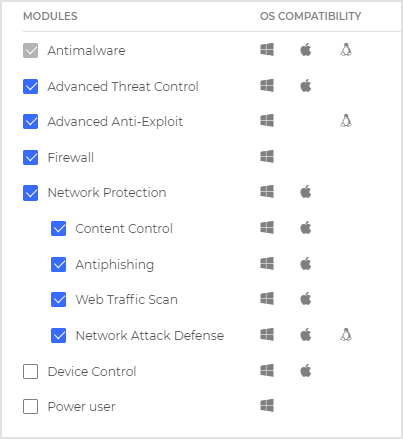
Under Antimalware > On-Access, make sure On access-Scanning is enabled.
Under Antimalware > On-Execute, make sure Advanced Threat Control is enabled.
While still on the On-Execute page, follow these steps to enable and configure the feature:
Enable the feature by selecting the Ransomware Mitigation checkbox.
Select the monitoring modes you want to use:
Locally - GravityZone monitors the processes and detects ransomware attacks initiated locally on the endpoint. It is recommended for workstations. Use with caution on servers due to performance impact.
For Local Ransomware Mitigation, administrators can configure Bitdefender security policy to monitor endpoint processes and recover the encrypted files as soon as the adaptive technology detects and blocks the attack. Even if ransomware manages to encrypt the local files, mitigation technology immediately jumps in to recover those files, either automatically or on-demand where the admin controls the timing of the recovery of the encrypted files.
Remote - GravityZone monitors access to network share paths and detects ransomware attacks that are initiated from another machine. Use this option if the endpoint is a file server or has network shares enabled.
For Remote Ransomware Mitigation, the security administrator can enable the technology to monitor network share paths that can be accessed remotely and prevent the files from being encrypted. On the remote endpoint, the user agent confirms that Ransomware Mitigation intercepted the remote malicious process behavior and protected the files. Bitdefender administrators can quickly run audit reports and find out more information about the IP address from where the remote ransomware attack was launched and the security module which protected the endpoint, and they can also receive an email notification when an attack is blocked containing information about the attacker’s IP address.
Select the recovery method:
On-demand - You manually choose the attacks from which to recover the files. You can do this from the Reports > Ransomware Activity page at any time of your convenience, but no later than 30 days from the attack. After this time, recovery will no longer be possible.
Automatic - GravityZone automatically recovers the files right after a ransomware detection.
Important
For the recovery to be successful, endpoints need to be available.
View Ransomware Mitigation Activity
Informs you with regards to the ransomware attacks that GravityZone detected on the endpoints you manage, and provides you with the necessary tools to recover the files affected during the attacks.
The report is available as a page in Control Center, distinct from the other reports, accessible right from the Control Center main menu.
The Ransomware Activity page consists of a table that, for each ransomware attack, lists the following:
The name, IP address and FQDN of the endpoint on which the attack took place
The company to which the endpoint belongs
The name of the user who was logged in during the attack
The type of attack, respectively a local or a remote one
The process under which the ransomware ran for local attacks, or the IP address from which the attack was initiated for remote ones
Date and time of the detection
Number of files backed up until the attack was blocked
The restore action status for all files on the target endpoint
The action taken on the detection, either Reported or Blocked.
Some details are hidden by default. Click the Show/Hide Columns button in the upper right side of the page to configure the details you want to view in the table. If you have many entries in the table, you can choose to hide filters using the Show/Hide filters button in the upper right side of the page.
Additional information is available by clicking the number for files. You can view a list with the full path to the original and restored files, and the restore status for all files involved in the selected ransomware attack.
Important
The backup copies are available for maximum 30 days. Please mind the date and time until files may still be recovered.
To recover files from ransomware, follow these steps:
Select the attacks you want in the table.
Click the Restore files button. A confirmation window shows up.
A recovery task is being created. You can check its status in the Tasks page, just like for any other task in GravityZone.
If detections are the result of legitimate processes, follow these steps:
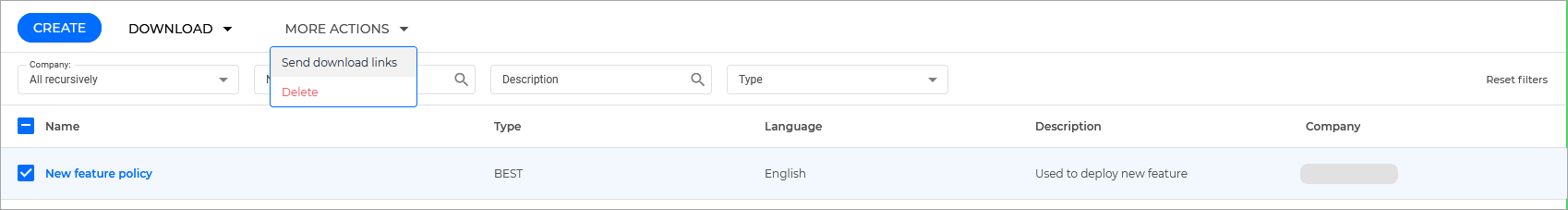
Go to the Policies > Configuration Profiles page from the left side menu in GravityZone Control Center.
Make sure you are on the Exclusions tab.
Click the Add exclusion button.
Fill in the requested details.
Click Add.
GravityZone will apply all possible exclusions: on folder, on process, and on IP address.
Note
Ransomware Activity keeps record of events for two years.