GravityZone VA
Manage the GravityZone appliance
The GravityZone appliance comes with a basic configuration interface, available from the management tool used for managing the virtualized environment where you have deployed the appliance.
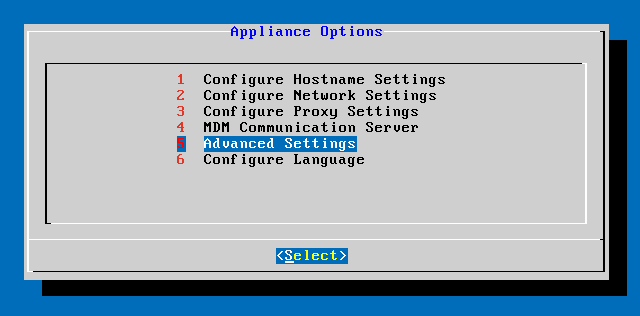
These are the available main options after the first GravityZone appliance deployment:
Use the arrow keys and the Tab key to navigate through menus and options. Press Enter to select a specific option.
Configure hostname settings
Communication with the GravityZone roles is performed using the IP address or DNS name of the appliance they are installed on.
By default, the GravityZone components communicate using IP addresses.
If you want to enable communication via DNS names, you must configure GravityZone appliances with a DNS name and make sure it correctly resolves to the configured IP address of the appliance.
Prerequisites:
Configure the DNS record in the DNS server.
The DNS name must correctly resolve to the configured IP address of the appliance. Therefore, you must make sure the appliance is configured with the correct IP address.
To configure the hostname settings:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Configure Hostname Settings.
Enter the hostname of the appliance and the Active Directory domain name (if needed).
Select OK to save the changes.
Configure network settings
You can configure the appliance to automatically obtain network settings from the DHCP server or you can manually configure network settings.
If you choose to use DHCP, you must configure the DHCP Server to reserve a specific IP address for the appliance.
To configure the network settings:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Configure Network Settings.
Select the network interface (default
eth0).Select the configuration method:
Configure network settings manually
You must specify the IP address, network mask, gateway address and DNS server addresses.
Obtain network settings automatically via DHCP
Use this option only if you have configured the DHCP Server to reserve a specific IP address for the appliance.
You can check current IP configuration details or link status by selecting the corresponding options.
Configure proxy settings
If the appliance connects to the Internet through a proxy server, you must configure the proxy settings.
Note
The proxy settings can also be configured from Control Center, Configuration > Proxy page. Changing the proxy settings in one location automatically updates them in the other location too.
To configure the proxy settings:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Configure Proxy Settings.
Select Configure proxy settings.
Enter the proxy server address.
Use the following syntax:
If the proxy server does not require authentication:
http(s)://<IP/hostname>:<port>If the proxy server requires authentication:
http(s)://<username>:<password>@<IP/hostname>:<port>
Select OK to save the changes.
Select Show proxy information to check the proxy settings.
MDM Communication Server
Note
This configuration is required only for mobile device management if your license key covers the Security for Mobile service. The option appears in the menu after installing the Communication Server role.
In the default GravityZone setup, mobile devices can be managed only when they are directly connected to the corporate network (via Wi-Fi or VPN).
This happens because when enrolling mobile devices they are configured to connect to the local address of the communication server appliance.
To manage mobile devices over the Internet, no matter where they are located, you must configure the communication server appliance with a publicly reachable address.
To be able to manage mobile devices when they are not connected to the company network, the following options are available:
Configure port forwarding on the corporate gateway for the communication server appliance.
Add an additional network adapter to the communication server appliance and assign it a public IP address.
In both cases, you must configure the communication server appliance with the external address to be used for mobile device management:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select MDM Communication Server.
Select Configure MDM Server external address.
Enter the external address.
Use the following syntax:
https://<IP/Domain>:<Port>.If you use port forwarding, you must enter the public IP address or domain name, and the port open on the gateway.
If you use a public address for the communication server appliance, you must enter the public IP address or domain name and the communication server port.
The default port is
8443.
Select OK to save the changes.
Select Show MDM Server external address to check the settings.
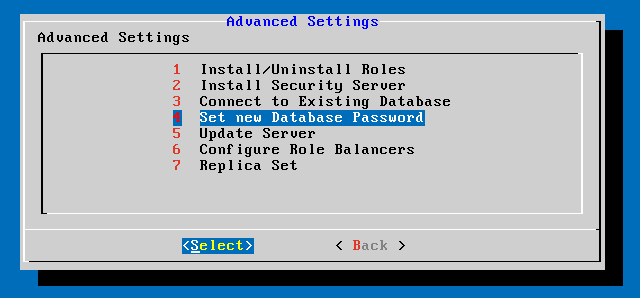
Advanced Settings
The advanced settings cover several options for manual deployment, environment extension and security enhancements:
The options availability vary depending on the installed roles and the enabled services. For example, if the Database Server role is not installed on the appliance, you can only install roles or connect to a GravityZone database deployed in your network. Once the Database Server role has installed on the appliance, the options for connecting to another database become unavailable.
Install/Uninstall roles
Database Server
Update Server
Web Console
Communication Server
A GravityZone deployment requires running one instance of each role.
Consequently, depending on how you prefer to distribute the GravityZone roles, you will deploy one to four GravityZone appliances.
The Database Server role is the first to be installed.
In a scenario with multiple GravityZone appliances, you will install the Database Server role on the first appliance and configure all other appliances to connect to the existing database instance.
Note
You can install additional instances of specific roles using role balancers.
For more information, refer to Configure role balancers.
To install the GravityZone roles:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Advanced Settings.
Select Install/Uninstall Roles.
Select Add or remove roles.
Proceed according to the current situation:
If this is the initial GravityZone appliance deployment, press the
Spacebar and thenEnterto install the Database Server role.You must confirm your choice by pressing
Enteragain. Configure the database password and then wait for the installation to complete.If you have already deployed another appliance with the Database Server role, choose Cancel and return to the Add or remove roles menu.
You must then choose Configure Database Address and enter the address of the database server.
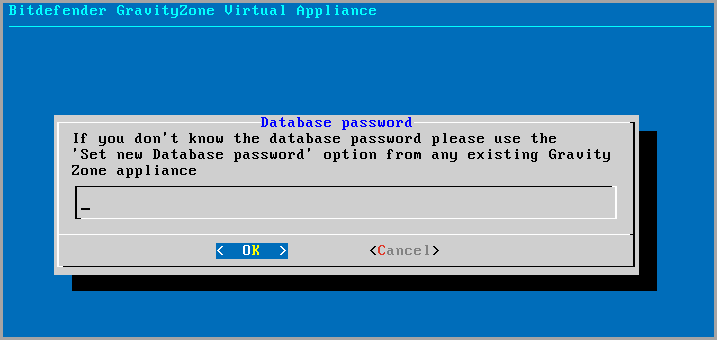
Make sure you set a database password before accessing this option. If you don't know the database password, configure a new one by selecting Advanced Settings > Set a new database password from the main menu.
Use the following syntax:
http://<IP/Hostname>:<Port>.The default database port is
27017. Enter the primary database password.
Install the other roles by choosing Add or remove roles from the Install/Uninstall Roles menu and then the roles to install.
For each role you want to install or uninstall, press the
Spacebar to select or deselect the role and then pressEnterto proceed.You must confirm your choice by pressing
Enteragain and then wait for the installation to complete.
Note
Each role is normally installed within a few minutes.
During installation, required files are downloaded from the Internet. Consequently, the installation takes more time if the Internet connection is slow.
If the installation hangs, redeploy the appliance.
You can view the installed roles and their IPs, by selecting one of the following options from the Install/Uninstall Roles menu:
Show locally installed roles, to view only the roles installed on that appliance.
Show all installed roles, to view all roles installed in your GravityZone environment.
Install Security Server
Note
The Security Server will be available to use only if your license key allows it.
You can install the Security Server from the GravityZone appliance configuration interface, directly on the GravityZone appliance, or from Control Center as a stand alone appliance. The advantages of installing the Security Server from the appliance are:
Suitable for GravityZone deployments with a single appliance having all roles.
You can view and use the Security Server without having to integrate GravityZone with a virtualization platform.
Less deployment operations to perform.
Prerequisites:
The GravityZone appliance must have the Database Server role installed, or it must be configured to connect to an existing database.
To install the Security Server from the appliance interface:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Advanced Settings.
Select Install Security Server. A confirmation message will appear.
Press
Enterto continue and wait until the installation finishes.
Note
You can uninstall this Security Server only from the Advanced Settings menu of the appliance interface.
Set new database password
When installing the Database Server role, you are required to set up a password to protect the database. In case you want to change it, set a new one by accessing Advanced Settings > Set a new database password from the main menu.
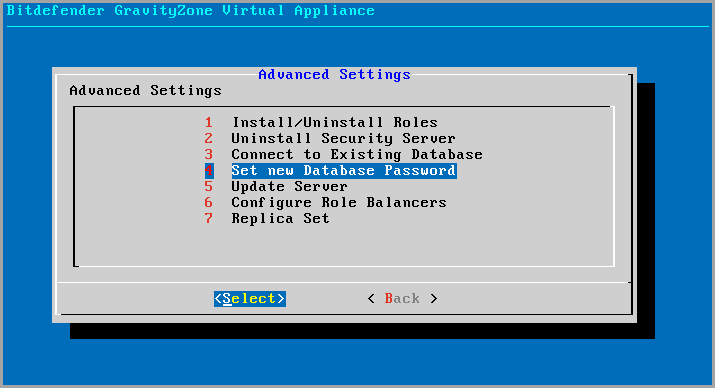
Follow the guidelines to set up a strong password.
Configure Update Server
The GravityZone appliance is by default configured to update from the Internet.
If you prefer, you can set your installed appliances to update from the local Bitdefender update server (the GravityZone appliance with the Update Server role installed).
To set the Update Server address:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Advanced Settings.
Select Update Server.
Select Configure update address.
Enter the IP address or hostname of the appliance running the Update Server role.
The default Update Server port is
7074.
Configure role balancers
To ensure reliability and scalability, you can install multiple instances of specific roles (Communication Server, Web Console).
Each role instance is installed on a different appliance.
All instances of a specific role must be connected to the other roles via a role balancer.
The GravityZone appliance includes built-in balancers that you can install and use.
If you already have balancing software or hardware within your network, you can choose to use them instead of the built-in balancers.
Built-in role balancers cannot be installed together with roles on a GravityZone appliance.
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Advanced Settings.
Select Configure Role Balancers.
Select the desired option:
Use external balancers
Select this option if your network infrastructure already includes balancing software or hardware that you can use.
You must enter the balancer address for each role that you want to balance.
Use the following syntax:
http(s)://<IP/Hostname>:<Port>.Use the built-in balancers
Select this option to install and use the built-in balancer software.
Select OK to save the changes.
Replica Set
With this option you can enable the use of a database replica set instead of a single-server database instance. This mechanism allows creating multiple database instances across a distributed GravityZone environment, ensuring the database high-availability in the case of a failure.
Important
Database replication is available only for fresh installations of GravityZone appliance starting with version 5.1.17-441.
Configuring Replica Set
At first, you have to enable Replica Set on the first installed GravityZone appliance. Then, you will be able to add replica set members by installing the database role to the other GravityZone instances in the same environment.
Important
Replica Set requires at least three members to work.
You can add up to seven database role instances as replica set members (MongoDB limitation).
It is recommended to use an odd number of database instances. An even number of members will only consume more resources for the same results.
To enable the database replication in your GravityZone environment:
Install the Database Server role on the first GravityZone appliance. For more information, refer to Install/Uninstall roles.
Configure the other appliances to connect to the first database instance. For more information, refer to Connect to existing database.
Go to the main menu of the first appliance, select Advanced Settings and then select Replica Set to enable it. A confirmation message will appear.
Select Yes to confirm.
Close the installation wizard window by pressing the Escape key repeatedly, until the login screen pops up. Afterwards, log back in.
Important
This step must be completed on all appliances.
Install the Database Server role on each of the other GravityZone appliances.
As soon as the above steps have been completed, all database instances will start working as a replica set:
A primary instance is elected, being the only one to accept write operations.
The primary instance writes all changes made to its data set to a log.
The secondary instances replicate this log and apply the same changes to their data sets.
When the primary instance becomes unavailable, the replica set will elect one of the secondary instances as primary.
When a primary instance does not communicate with the other members of the set for more than 10 seconds, the replica set will attempt to select another member to become the new primary.
Removing Replica Set Members
To remove replica set members, just choose from their appliance console interface (menu-based interface) Install/Uninstall Roles > Add or Remove Roles and deselect Database Server.
Note
You can remove a replica set member only if at least four database instances have been installed in the network.
Enable Secure VPN Cluster
The GravityZone roles have several internal services that communicate only between them. For a more secure environment, you can isolate these services by creating a VPN cluster for them. Either these services are on the same appliance or on more, they will then communicate via a secure channel.
Important
This feature requires a standard GravityZone deployment, without any custom tools installed.
Once the cluster is enabled, you cannot disable it.
To secure the internal services on the appliances:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Advanced Settings.
Select Enable Secure VPN Cluster.
A message informs you of the changes that will be made.
Select Yes to confirm and proceed with the VPN installation.
When complete, a confirmation message is displayed.
From now on, all roles on the appliance are installed in secured mode and the services will communicate through the VPN interface. Any new appliance you add to the environment must join the VPN cluster. For more information, refer to Connect to existing database (Secure VPN Cluster).
Connect to existing database
In a GravityZone distributed architecture, you need to install the Database Server role on the first appliance and then configure all other appliances to connect to the existing database instance. This way, all appliances will share the same database.
Important
It is recommended to enable Secure VPN Cluster and to connect to a database within such cluster. For more information, refer to:
To connect the appliance to a GravityZone database outside a Secure VPN Cluster:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Advanced Settings.
Select Connect to Existing Database.
Note
Make sure you set a database password before accessing this option. If you don't know the database password, set a new one by accesing Advanced Settings > Set a new database password from the main menu.
Select Configure Database Server address.
Enter the database address, using the following syntax:
<IP/Hostname>:<Port>Specifying the port is optional.
The default port is
27017.Enter the primary database password.
Select OK to save the changes.
Select Show Database Server address to make sure the address has been correctly configured.
Connect to existing database (Secure VPN Cluster)
Use this option when you need to extend your GravityZone deployment with more appliances, and Secure VPN Cluster is enabled. This way, the new appliance will share the same database with the existing deployment in a secure mode.
For more information on Secure VPN Cluster, refer to Enable Secure VPN Cluster.
Prerequisites
Before proceeding, make sure to have the following at hand:
Database Server IP address
Password for the bdadmin user on the appliance with the Database Server role
Connect to database
To connect the appliance to a GravityZone database within a Secure VPN Cluster:
Access the appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Advanced Settings.
Select Connect to Existing Database (Secure VPN Cluster).
You will be informed of the requirements and alternatives, if they are not met.
Select OK to acknowledge and continue.
Enter the IP address of the Database Server within the Secure VPN Cluster.
Enter the password for the bdadmin user on the appliance with the Database Server.
Select OK to save the changes and continune.
When the process is complete, you receive a confirmation message. The new appliance becomes a member of the cluster and it will communicate with the other appliances in a secure way. All appliances will share the same database.
Check the Secure VPN Cluster status
This option is available only after you have previously enabled the secure VPN cluster. Select this option to check which appliances in your GravityZone deployment have not yet secured their services. You may need to investigate further and see if the appliances are online and accessible.
Configure language
To change the appliance configuration interface language:
Select Configure Language from the main menu.
Select the language from the available options. A confirmation message will appear.
Note
You may need to scroll down to view your language.
Select OK to save the changes.
Change the MongoDB password
When first installing the database role in the initial setup of the GravityZone appliance, you will be prompted to setup a MongoDB password.
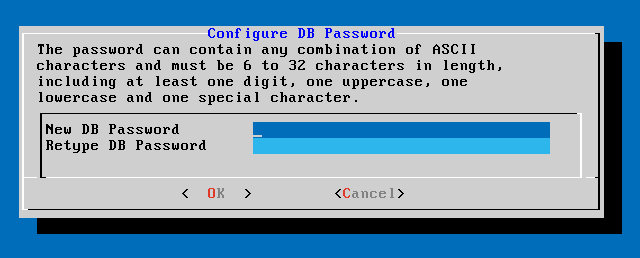
If the MongoDB is already installed, we recommend changing the password as restricting access to critical servers like Bitdefender GravityZone Database is a best practice for preventing attacks.
To change the database password, follow these steps:
Log in to the appliance CLI, using the bdadmin credentials set;
Go to Advanced Settings;
Go to Set new Database Password;
Follow the password requirements in order to setup the new password (must be between 6 and 32 characters in length, including at least one uppercase, one lowercase, one digit and one special character);
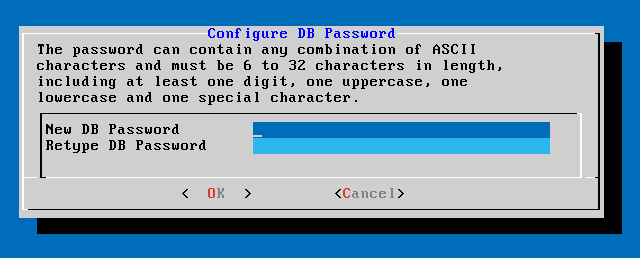
Press OK.
Restore a database backup
When for various reasons your GravityZone instance is working improperly (failed updates, dysfunctional interface, corrupted files, errors, etc.), you can restore the GravityZone database from a backup copy.
Restoring the database to the same GravityZone VA
Prerequisites
A SSH connection to the GravityZone appliance, using root privileges.
You can use putty and bdadmin's credentials to connect to the appliance via SSH, then run the command
sudo suto switch to the root account.Note
As a security measure, the system restricts access and bans IP addresses that fail authentication multiple times when connecting to any GravityZone instance over SSH.
The GravityZone infrastructure has not changed since the backup.
The backup is more recent than April 30th, 2017 and the GravityZone version is higher than 6.2.1-30. If otherwise, contact the Technical Support team.
In distributed architectures, GravityZone has not been configured to use database replication (Replica Set).
To verify the configuration, follow these steps:
Open the
/etc/mongodb.conf file.Check that
replSetis not configured, as in the example below:# replSet = setname
No CLI processes are running.
To make sure all CLI processes are stopped, run the following command:
# killall -9 perlThe
mongoconsolepackage is installed on the appliance.To verify the condition is met, run this command:
# /opt/bitdefender/bin/mongoshellrestore --versionThe command should not return any errors, otherwise run:
# apt-get update# apt-get install --upgrade mongoconsole
Restoring the database
Go to the location containing the database archive:
# cd /directory-with-backupWhere directory-with-backup is the path to the location with the backup files.
For example:
# cd /tmp/backupRestore the database.
/opt/bitdefender/bin/mongoshellrestore -u bd -p 'GZ_db_password' --authenticationDatabase admin --gzip --drop --archive < 'gz-backup-$YYYY-$MM-$DD(timestamp).tar.gz'Important
Make sure to replace
GZ_db_passwordwith the actual password of the GravityZone Database Server and the timestamp variables in the archive's name with the actual date.For example, the actual date should look like this:
gz-backup-2019-05-17(1495004926).tar.gzOptionally, to be able to download again previously published kits in the GravityZone console run the following command:
/opt/bitdefender/bin/mongoshell -u bd -p 'GZ_db_password' --eval 'db.endpointKits.update({state:{$ne:1}},{$set:{internalState:1,isProcessing:true,"applianceIds.downloaded":[],"applianceIds.published":[]}},{multi:true})' --quiet devdbNote
Enabling this option may generate a large amount of data and take a long time depending on your previous update staging settings.
Restart the appliance.
Database restoration is now complete.
Restoring the database from a decommissioned GravityZone VA
Prerequisites
A fresh GravityZone VA installation, with the same IP as the old appliance and having only the Database Server role installed. You can download the GravityZone VA image from here.
A SSH connection to the GravityZone virtual appliance, using the root privileges.
Note
As a security measure, the system restricts access and bans IP addresses that fail authentication multiple times when connecting to any GravityZone instance over SSH.
The GravityZone infrastructure has not changed since the backup was made.
The backup is more recent than April 30th, 2017.
In distributed architectures, GravityZone has not been configured to use database replication (Replica Set). If you use Replica Set in your GravityZone environment, you also have the Database Server role installed on other appliance instances.
Restoring the database
Important
When following this procedure, use the same database password you had when the backup was created. If you have forgotten your password, contact Bitdefender Enterprise Support.
Download the Virtual Appliance.
Install the Database Server role.
For more information about installing the Database Server role, refer to Deploy and set up GravityZone VA.
Stop VASync:
# service vasync stopStop CLI:
# killall -9 perlGo to the location containing the database archive:
# cd /directory-with-backupWhere directory-with-backup is the path to the location with the backup files.
For example:
# cd /tmp/backupRestore the database:
/opt/bitdefender/bin/mongoshellrestore -u bd -p 'GZ_db_password' --authenticationDatabase admin --gzip --drop --archive < 'gz-backup-$YYYY-$MM-$DD(timestamp).tar.gz'Important
Make sure to replace
GZ_db_passwordwith the actual password of the GravityZone Database Server and the timestamp variables in the archive's name with the actual date.For example, the actual date should look like this:
gz-backup-2019-05-17(1495004926).tar.gzTest to make sure you have entered the correct password by running the following command:
mongo admin -u bd -p 'GZ_db_password'Note
If you receive error messages, contact Bitdefender Enterprise Support.
Restore the appliance ID:
/opt/bitdefender/bin/mongoshell -u bd -p 'GZ_db_password' --eval 'print(db.applianceInstalls.findOne({name:"db"}).applianceId);' --quiet devdb > /opt/bitdefender/etc/applianceidImportant
Make sure to replace
GZ_db_passwordwith the actual password of the GravityZone Database Server.Remove the reference to the old roles:
/opt/bitdefender/bin/mongoshell -u bd -p 'GZ_db_password' --eval 'db.applianceInstalls.remove({name:{"$ne": "db"}});' --quiet devdbImportant
Make sure to replace
GZ_db_passwordwith the actual password of the GravityZone Database Server.Start VASync:
# service vasync startOptionally, to be able to download again previously published kits in the GravityZone console run the following command:
/opt/bitdefender/bin/mongoshell -u bd -p 'GZ_db_password' --eval 'db.endpointKits.update({state:{$ne:1}},{$set:{internalState:1,isProcessing:true,"applianceIds.downloaded":[],"applianceIds.published":[]}},{multi:true})' --quiet devdbNote
Enabling this option may generate a large amount of data and take a long time depending on your previous update staging settings.
Start CLI:
/opt/bitdefender/eltiw/installerInstall the remaining GravityZone roles.
Restart the appliance.
Database restoration is now complete.
Restoring the database with staging settings
Prerequisites
The Database and the Update Server roles should be installed on separate appliances
A fresh GravityZone VA installation, with the same IP as the old appliance and having only the Database Server role installed. You can download the GravityZone VA image from here.
A SSH connection to the GravityZone virtual appliance, using the root privileges.
Note
As a security measure, the system restricts access and bans IP addresses that fail authentication multiple times when connecting to any GravityZone instance over SSH.
The GravityZone infrastructure has not changed since the backup was made.
The backup is more recent than April 30th, 2017.
In distributed architectures, GravityZone has not been configured to use database replication (Replica Set). If you use Replica Set in your GravityZone environment, you also have the Database Server role installed on other appliance instances.
Restoring the database and staging settings
To restore the database follow the steps below:
Download the Virtual Appliance.
Install the Database Server role.
For more information about installing the Database Server role, refer to Deploy and set up GravityZone VA.
Stop VASync:
# service vasync stopStop CLI:
# killall -9 perlGo to the location containing the database archive:
# cd /directory-with-backupWhere directory-with-backup is the path to the location with the backup files.
For example:
# cd /tmp/backupRestore the database:
/opt/bitdefender/bin/mongoshellrestore -u bd -p 'GZ_db_password' --authenticationDatabase admin --gzip --drop --archive < 'gz-backup-$YYYY-$MM-$DD(timestamp).tar.gz'Important
Make sure to replace
GZ_db_passwordwith the actual password of the GravityZone Database Server and the timestamp variables in the archive's name with the actual date.For example, the actual date should look like this:
gz-backup-2019-05-17(1495004926).tar.gzTest to make sure you have entered the correct password by running the following command:
mongo admin -u bd -p 'GZ_db_password'Note
If you receive error messages, contact Bitdefender Enterprise Support.
Restore the appliance ID:
/opt/bitdefender/bin/mongoshell -u bd -p 'GZ_db_password' --eval 'print(db.applianceInstalls.findOne({name:"db"}).applianceId);' --quiet devdb > /opt/bitdefender/etc/applianceidImportant
Make sure to replace
GZ_db_passwordwith the actual password of the GravityZone Database Server.Remove the reference to the old roles:
/opt/bitdefender/bin/mongoshell -u bd -p 'GZ_db_password' --eval 'db.applianceInstalls.remove({name:{"$ne": "db"}});' --quiet devdbImportant
Make sure to replace
GZ_db_passwordwith the actual password of the GravityZone Database Server.Start VASync:
# service vasync startOptionally, to be able to download again previously published kits in the GravityZone console run the following command:
/opt/bitdefender/bin/mongoshell -u bd -p 'GZ_db_password' --eval 'db.endpointKits.update({state:{$ne:1}},{$set:{internalState:1,isProcessing:true,"applianceIds.downloaded":[],"applianceIds.published":[]}},{multi:true})' --quiet devdbNote
Enabling this option may generate a large amount of data and take a long time depending on your previous update staging settings.
Start CLI:
/opt/bitdefender/eltiw/installerRestart the appliance.
Database restoration is now complete.
To restore the staging settings follow the steps below:
Go to the location containing the backup archives.
Copy or move the
gz-backup-stagingarchive to a directory of your choice on the appliance where the Update Server role will be installed.For example:
/home/bdadmin/backup-stagingStart CLI:
/opt/bitdefender/eltiw/installerConnect to the existing database previously created.
Install the Update Server role.
Stop the update server service:
# service arrakis stopRemove the product updates directories:
# rm -rf /opt/bitdefender/var/data/products/v2# rm -rf /opt/bitdefender/var/data/products/bst_nix# rm -rf /opt/bitdefender/var/data/products/bst_nix7_updateUnpack the
gz-backup-stagingarchive from the location it was saved:# tar -xvzf archiveCopy all directories:
# rsync -a -v -r --chown=bitdefender:bitdefender /home/bdadmin/extracted_archive_folder/opt/bitdefender/var/data/products/ /opt/bitdefender/var/data/products/ > /home/bdadmin/rsync_output.txtReplace the
extracted_archive_folderwith the exact location where the archive was extracted.To check the status of the process open
/home/bdadmin/rsync_output.txt.Make sure the copying process ended successfully then start the update server service:
# service arrakis start
You can continue to install the remaining roles on the database appliance or on separate appliances. Make sure no other roles are installed on the update server appliance.
Restoring the database in a Replica Set environment
If you have deployed the database in a Replica Set environment, you can find the official restore procedure on the mongoDB online manual (English only).
Note
The procedure requires advanced technical skills and should be done only by a trained engineer. If you encounter difficulties, please contact our Technical Support to assist you in restoring the database.
Enable privilege escalation for users belonging to an Active Directory group
Follow these steps to configure the GravityZone appliance to allow Active Directory users to log in to the configuration interface with root privileges.
Configure the appliance hostname and domain name
The Active Directory (AD) technology depends on proper DNS names. Therefore, make sure the GravityZone virtual appliance has the hostname and the domain name configured correctly.
To configure the hostname settings:
Access the GravityZone virtual appliance console from your virtualization management tool (for example, vSphere Client).
From the main menu, select Configure Hostname Settings.
Enter the hostname of the appliance and the Active Directory domain name.
Select OK to save the changes.
Reboot the appliance once configured.
Install the required packages
This procedure uses Samba to enable the Active Directory integration. Thus, you need to install these packages:
# apt-get install krb5-user winbind samba ntp
Configure Kerberos
Modify the file /etc/krb5.conf as in the following example:
[logging]
default = FILE:/var/log/krb5.log
[libdefaults]
default_realm = EXAMPLE.LOCAL
kdc_timesync = 1
ccache_type = 4
forwardable = true
proxiable = true
[realms]
EXAMPLE.LOCAL = {
kdc = adserver.example.local
admin_server = adserver.example.local
default_domain = EXAMPLE.LOCAL
}
[domain_realm]
.adserver.example.local = EXAMPLE.LOCAL
adserver.example.local = EXAMPLE.LOCAL
.kerberos.server = EXAMPLE.LOCAL
[login]
krb4_convert = true
krb4_get_tickets = falseConfigure Samba
Modify the file /etc/samba/smb.conf as in the following example:
[global]
log file = /var/log/samba/log.%m
max log size = 1000
security = ADS
realm = EXAMPLE.LOCAL
password server = 192.168.1.2
workgroup = EXAMPLE
idmap uid = 10000-20000
idmap gid = 10000-20000
winbind enum users = yes
winbind enum groups = yes
template homedir = /home/%D/%U
template shell = /bin/bash
client use spnego = yes
client ntlmv2 auth = yes
encrypt passwords = true
winbind use default domain = yes
restrict anonymous = 2Configure the Name Service Switch
Modify the file /etc/nsswitch.conf as in the following example:
passwd: compat winbind group: compat winbind shadow: compat hosts: files dns networks: files protocols: db files services: db files ethers: db files rpc: db files netgroup: nis
Configure the NTP daemon
Change the time synchronization server to the AD server. Modify /etc/ntp.conf as in the following example:
... server dc.example.local ...
Stop the NTP daemon:
# service ntp stop
Force a time synchronization:
# ntpdate dc.example.local
Restart the NTP daemon:
# service ntp start
Configure PAM
In Ubuntu 12.04 LTS and newer, the winbind package does most of the configuration work. However, there are some non-default options that should be present to facilitate the login.
To configure these options, add the following line in both /etc/pam.d/common-session and /etc/pam.d/sshd:
session required pam_mkhomedir.so skel=/etc/skel/ umask=0022
Restart winbind
service winbind restart
Join the appliance in the domain
# net ads join -U [email protected]
Reconfigure the SSH daemon
Make sure the SSH daemon allows all users to log in, except the root:
... # Authentication: LoginGraceTime 120 PermitRootLogin no StrictModes yes ...
This will also disable the restriction for bdadmin.
Configure sudo
Using the command visudo, enable priviledge elevation for a specific group. For example:
%vcservicesadmin ALL=(ALL) ALL
You can now connect through SSH to the GravityZone appliance using a domain user:
$ ssh EXAMPLE\\[email protected]
The home directory will be automatically created and the user will be able to gain root privileges, provided it belongs to the right group.
Run filesystem check in GravityZone Virtual Appliance
The filesystem check operation, or fsck, can be used to check and repair Linux filesystems. You can use this operation if, for example, your GravityZone Virtual Appliance (VA) instance fails to boot, or it is stuck in an endless boot.
Select the method you want to use from the menu in the upper left side of the screen.
Run offline filesystem check on the GravityZone Virtual Appliance
Prerequisites
Virtual Machine console level access to the GravityZone virtual appliance (provided through your hypervisor management software).
An Ubuntu 24.04 (live ISO image for desktop). You can download it from here.
Mounted Ubuntu 24.04 Live image on the GravityZone Virtual Appliance located in your hypervisor management software.
Run offline filesystem check from a mounted Ubuntu 24.04 image
Open your hypervisor management software.
Shut down the GravityZone Virtual Appliance.
Create a snapshot of the GravityZone VA.
Mount the Ubuntu 24.04 Live image into the GravityZone VA.
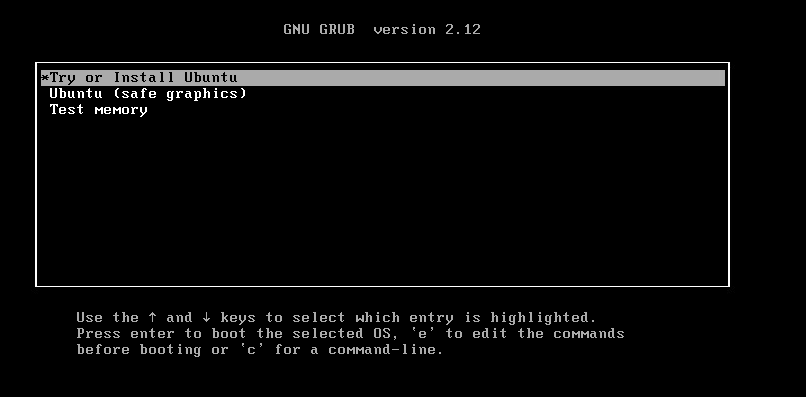
Boot the GravityZone VA from the Ubuntu image and select Try or Install Ubuntu when prompted. Ubuntu boots up.
In Ubuntu desktop, click the search bar at the top of the screen and start typing terminal.
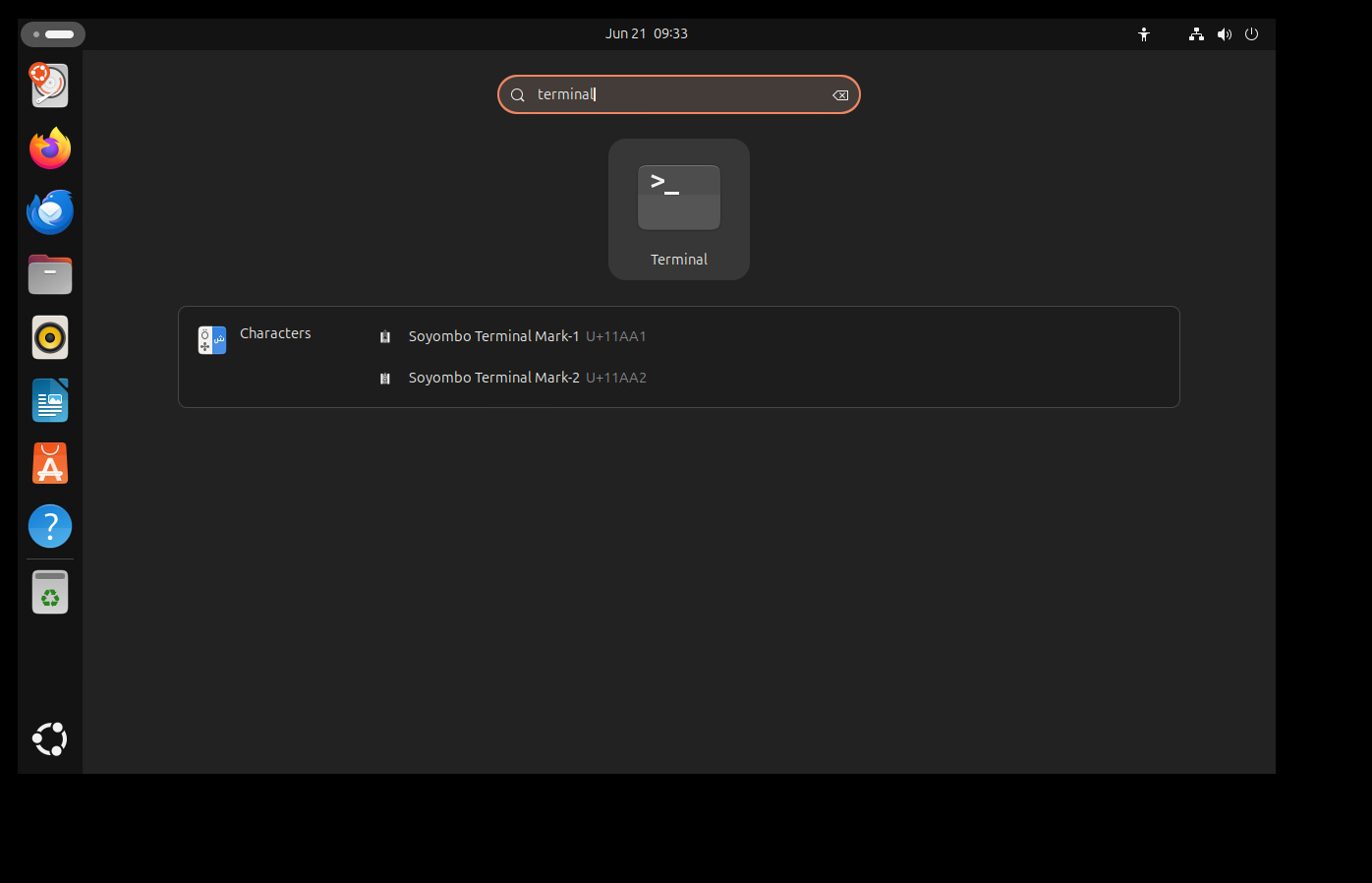
Open Terminal and run the following commands:
sudo suls /dev/mapperIdentify the system disk of the GravityZone VA. You can look for the following names: gzva-root, gzva-data, gz-data or gz-root.
Run the following command to perform a filesystem check:
fsck –f -y /dev/mapper/gzva-rootIn this example we used gzva-root, as seen in the screenshot below.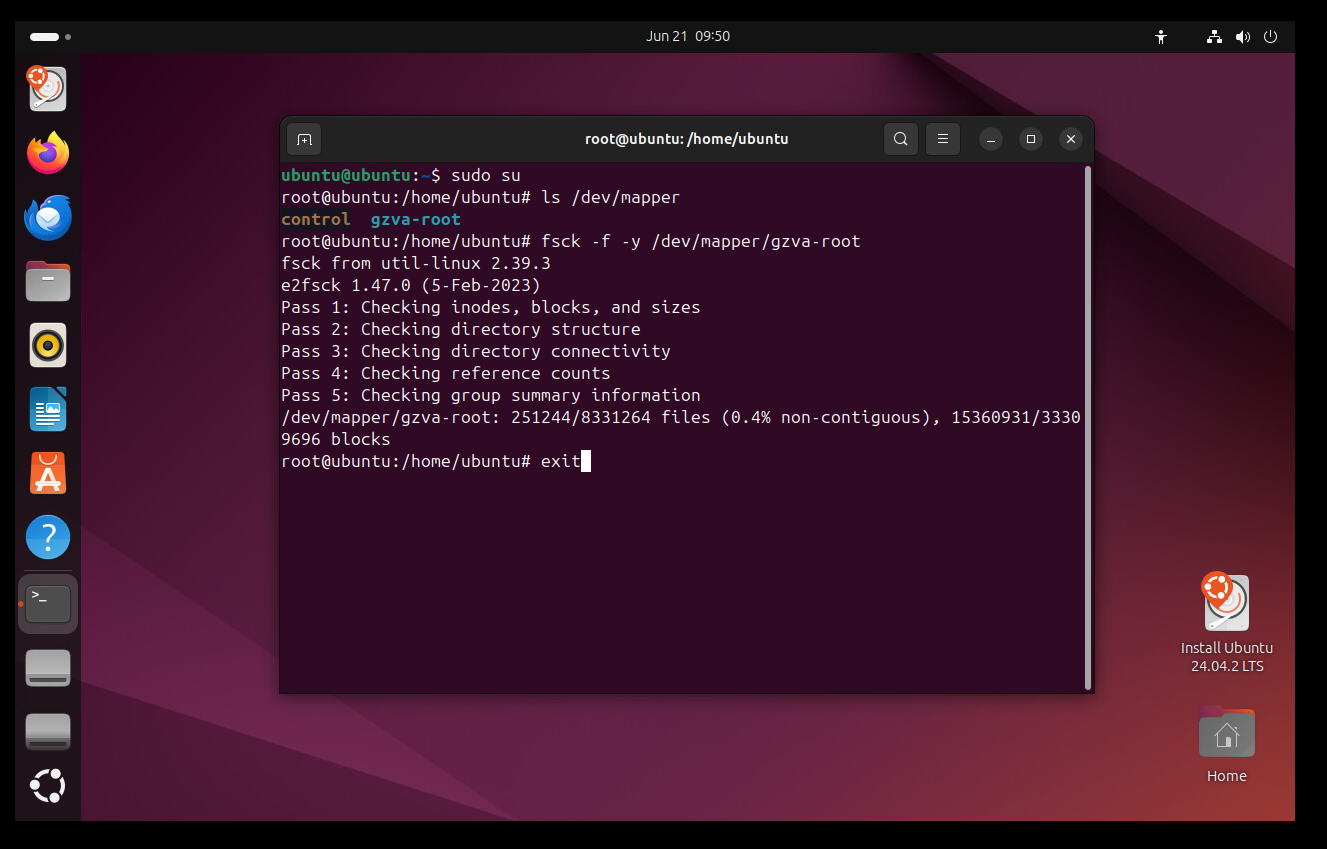
If there are any errors during this operation, you will be prompted by confirmation dialogs. Select yes to all fsck questions.
After the filesystem check is done, reboot the GravityZone VA without the Ubuntu image and check if the appliance boots up successfully.
If the filesystem check is unable to fix the errors, we recommend you to restore your GravityZone Virtual Appliance from a database backup. For more information, refer to Restore a database backup.