A unified, highly effective cybersecurity solution for MSPs, combining system hardening, risk analytics, threat prevention, extended detection and response to provide advanced protection against attacks and strengthen resilience against ransomware and cyber threats.

The GravityZone platform empowers you to manage all your tenants from a centralized management console that features integrations with your RMM, PSA and other platforms to improve efficiency in supporting your customers.
Consistently highly ranked by independent analyst firms and testing organizations including Gartner, Forrester, MITRE, AV-TEST and AV-Comparatives, now becomes accessible to SMBs supported by MSPs.
Our flexible solutions let you choose the proper security for your customers, with recommended options for highly regulated industries, combined with monthly usage-based billing that aligns with the MSP business model.
Technology
Bitdefender GravityZone MSP Security Solutions
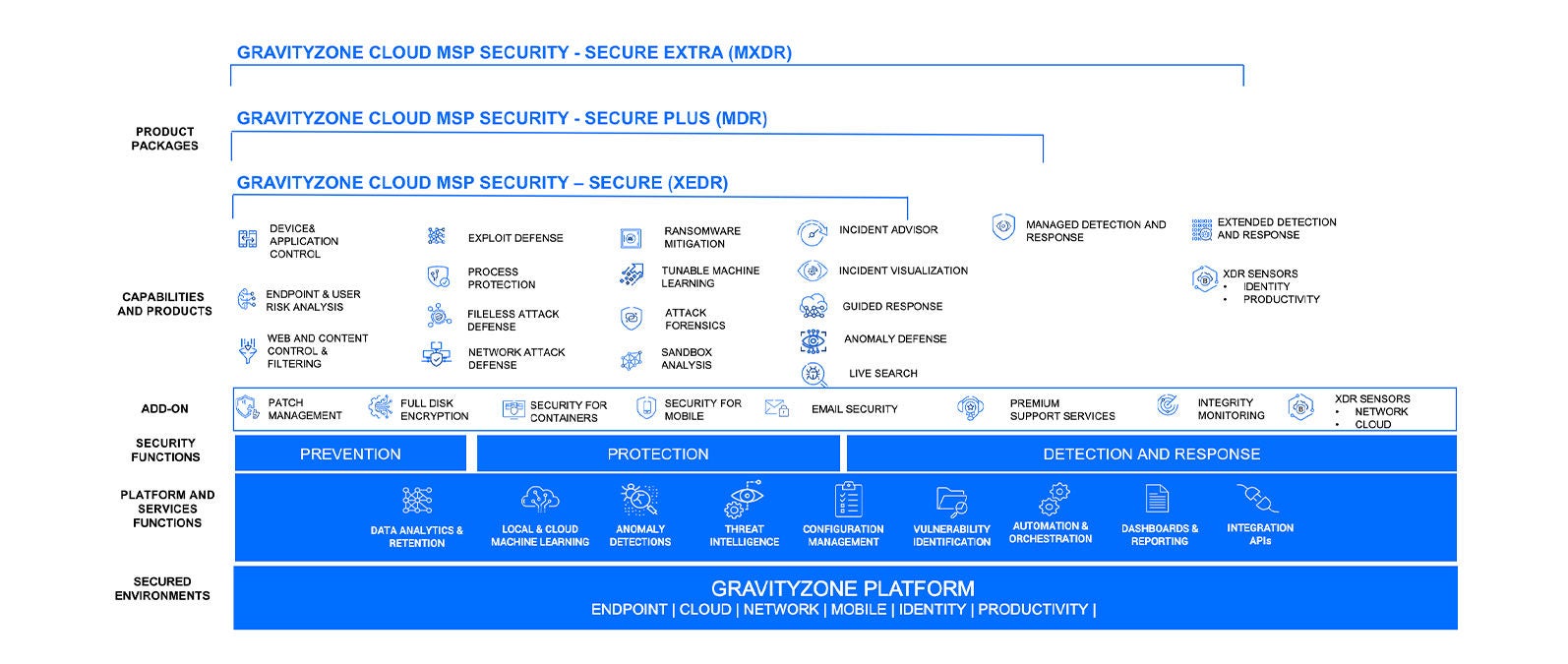
Diversify and strengthen your MSP offering with our custom security solutions. Each solution has been designed to offer a high level of control, flexibility, and scalability, bespoke for Managed Service Providers. Choose the solution that fits your customers' needs.
Bitdefender offers an integrated portfolio of complementary products that provide MSSPs with robust tools to proactively defend against evolving threats, ensure compliance, and maintain operational efficiency—enhancing managed security services and delivering superior protection for their customers.
With more integrated solutions than any other security vendor, Bitdefender does more than understand the MSP community.
We are part of it. We work with tools that you use every day.
Yes, Bitdefender GravityZone for MSP is a cloud-based platform designed for MSP partners to create parent-child infrastructures, making it easier to manage multiple client environments. Additionally, the platform allows for streamlined management through policy inheritance, if desired.
Bitdefender has partnerships with many popular platforms used by MSPs globally. Integrations are available for RMM and PSA platforms like ConnectWise, Kaseya, NinjaOne, Atera, RG System etc. Check our Integration and technology partners section above.
Bitdefender offers endpoint protection for Windows workstations and servers, Linux OS, and macOS. We also provide XDR (Extended Detection and Response) sensors and integrations for popular cloud services like Microsoft 365, Google Cloud, and AWS. Additionally, network sensors are available to further protect on-premises networks.
Our pricing model supports monthly consumption and billing through a global network of distributors and RMM partners. MSP partners can allocate the necessary features or packages on a per-customer basis, offering maximum flexibility to meet clients’ specific needs. There are no minimum commitments, and MSP partners can aggregate usage across all customers to benefit from volume pricing.
Join the Partner Advantage Network and identify a Bitdefender Channel Partner in your area. Our solutions are accessible through an extensive global network of distribution and RMM partners.
A distribution or RMM partner typically creates Partner accounts in the GravityZone console for Service Providers. MSPs can then simply log in and install the Bitdefender security solutions without a traditional license key, then will have visibility over all deployed solutions (including add-ons) in the security console and the Bitdefender Partner Advantage Network Portal.
It usually depends on each customer’s risk profile and tolerance, as well as regulatory environments and budgets. As cyber-attacks are constantly evolving, we recommend that Advanced Threat Security (ATS) and Endpoint Detection and Response (EDR) become the standard or default offering (both included with the GravityZone MSP Secure solution). Also, adding Extended Detection and Response (XDR) on top of ATS and EDR can improve cyber-security for your customers, allowing you to combine expertise with reduced alert overload and analyst fatigue, by automatically analyzing and correlating activities across different telemetry sources. Alerts can be resolved more effectively with integrated views of evidence for the investigation, while automation can increase operational efficiency by reducing repetitive tasks.
For MSPs who struggle with staffing challenges or expertise shortages, Managed Detection and Response (MDR) services can be the right solution.
We’re here to help you choose the solution or service that’s right for your business.