“Didn’t you say you had it under control?” Discover why smart security teams choose GravityZone — before the chaos hits. Learn More >>
500M+
protected systems delivering telemetry
50B+
security queries processed daily
14K+
sandbox detonations contributing daily to threat intelligence
5min
from detection until indicators are typically available
How Bitdefender Threat Intelligence Works
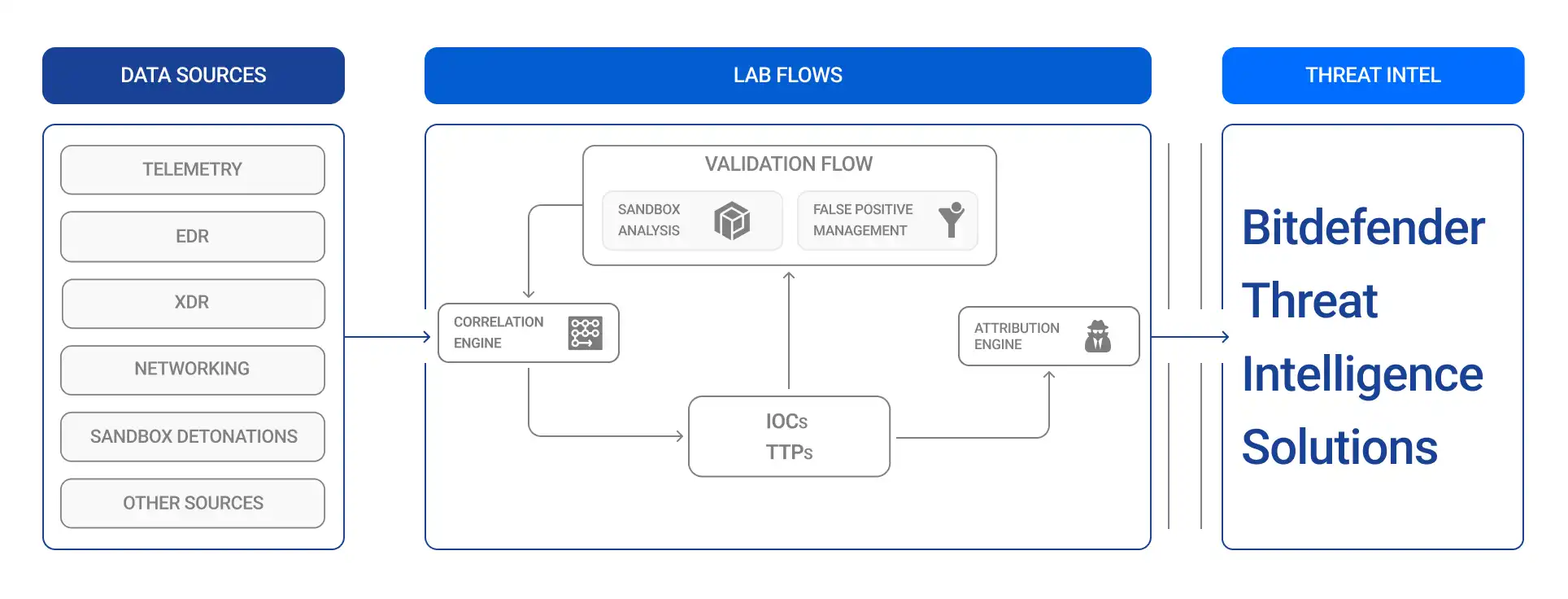
Bitdefender Threat Intelligence Solutions support both security operations teams and organizations building security products. The portfolio includes real-time threat feeds, blocklists, and APIs that help automate detection, enrich alerts, and support security decisions at scale.
Security teams can ingest the intelligence into their own environments to support investigation and response, while security vendors can integrate it directly into their products to power threat detection and prevention.

Built for action. Backed by reality.
Threat intelligence you can trust, whether you are defending an environment or building a security product.
Bitdefender Threat Intelligence is correlated from multiple sources, including endpoint telemetry, root cause analysis, phishing intelligence, mobile threats, honeypots, and open-source intelligence. These sources are analyzed and curated through Bitdefender research and lab workflows to improve accuracy and relevance.
Threat intelligence feeds are delivered in JSONL format. To simplify integration, Bitdefender also provides translation scripts that allow feeds to be converted into formats such as MISP and STIX.
Yes. Bitdefender Threat Intelligence products are designed to support OEM use cases and can be integrated directly into security products and platforms. The only exception is the IntelliZone Portal, which is a user-facing offering.
We’re here to help you choose the solution or service that’s right for your business.