“Didn’t you say you had it under control?” Discover why smart security teams choose GravityZone — before the chaos hits. Learn More >>
A zero-day vulnerability is a security flaw in software, hardware, or firmware that the responsible parties — software or hardware vendors — are not yet aware of until it is disclosed to them directly, or the public at-large. In some cases, the vendor is unaware of the flaw before public disclosure or has not had enough time to create a fix, and so there is no official workaround or patch to protect the vulnerability from exploit. These vulnerabilities are especially risky because they can go undetected for an extended period, potentially days, months, or even years.
The term “zero-day” itself refers to the absence of time between a vulnerability being discovered, and potentially exploited, and publicly acknowledged and/or mitigated by the vendor. These vulnerabilities are prime targets for cybercriminals who try to exploit them before they are recognized, or as soon as possible after being publicly revealed. Technically, after the flaw is publicly disclosed, it is no longer considered a zero-day vulnerability but rather an n-day or one-day vulnerability.
A zero-day exploit is the specific method or technique that attackers use to take advantage of a zero-day vulnerability. This is a piece of code or a sequence of commands that exploits a vulnerability to achieve an outcome which advances an attack. If cybercriminals discover these exploits before the vendors, it effectively gives them a head-start in crafting and implementing attacks. Zero-Day exploit kits can be sold on the dark web for substantial amounts, adding another layer of financial incentive for attackers.
In cybersecurity terms, a zero-day attack occurs when an attacker uses a zero-day exploit to compromise a system that has an existing but unknown vulnerability. These attacks can take various forms, ranging from data theft to installing malicious software. Zero-day attacks are particularly menacing because often the only individuals aware of them are the attackers themselves. In many cases, attackers deliver the zero-day exploit through sophisticated methods like socially engineered emails or phishing scams, thereby initiating the attack sequence.
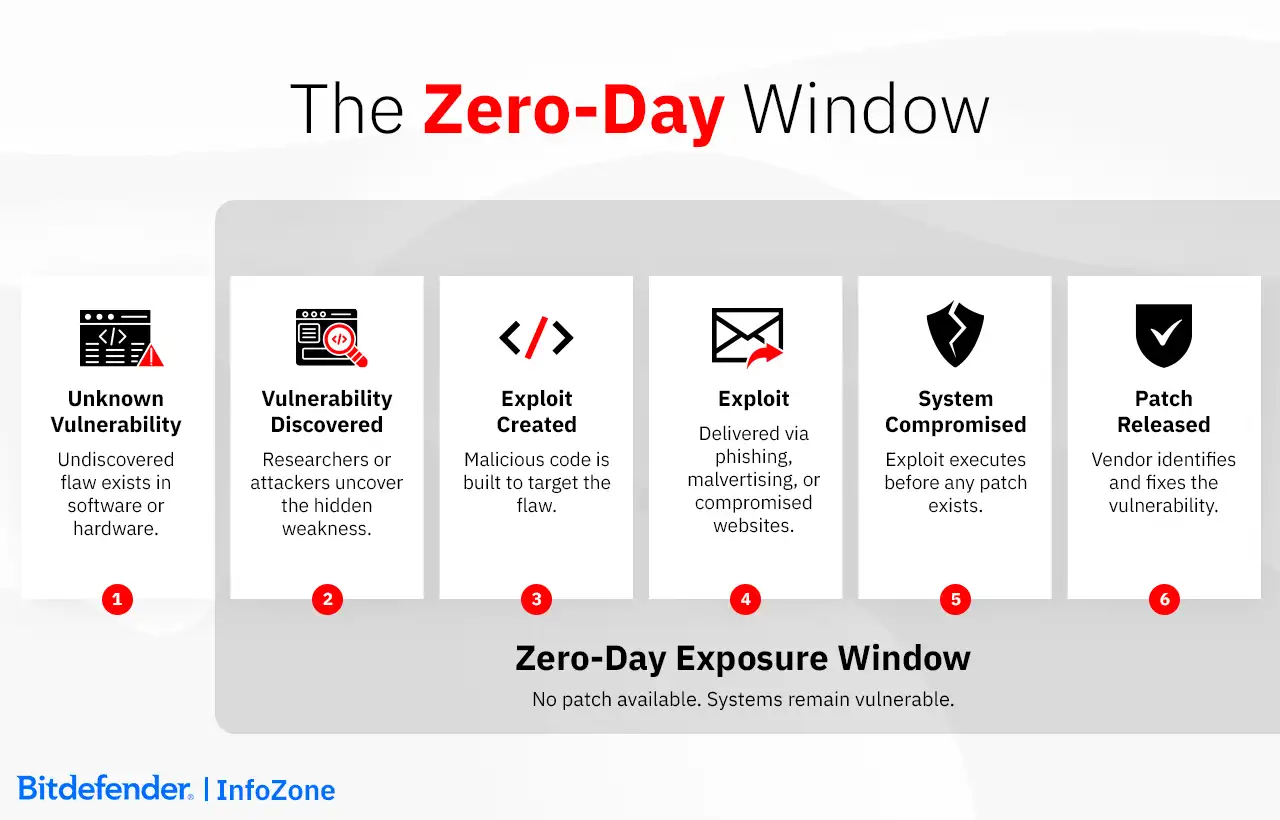
Zero-day vulnerabilities are a major concern because they allow hackers to exploit flaws before targets even become aware of their existence. This means that attackers can breach systems surreptitiously, giving them ample time to wreak havoc. Once such a vulnerability is disclosed, it can take vendors a considerable amount of time to issue a patch. In the interim, organizations remain at high risk.
Complicating matters further, the very architecture of modern networks is becoming more intricate. Organizations now integrate a blend of cloud-based and on-premises applications, various types of devices, and even Internet of Things (IoT) technology, broadening their attack surface significantly.
Those launching zero-day attacks aren't a monolithic group; they have various motivations and belong to different categories. It's not just opportunistic hackers who are the problem; there's also a bustling black market where zero-day vulnerabilities and exploits are traded for large sums of money. Nation-state actors, too, are in the hunt for these flaws. Instead of disclosing them, they often stockpile these vulnerabilities to craft specialized zero-day exploits for use against adversaries, a practice that has drawn significant criticism for putting innocent organizations in jeopardy.
Cybercriminals typically seek financial gain, focusing on acquiring sensitive information or holding it for ransom by encrypting (ransomware) or threatening to release sensitive data, or both. State-sponsored actors and hacktivists use zero-day vulnerabilities to advance social or political causes, often aiming to gather sensitive data or publicize their mission. Corporate espionage is another driver, where companies may use exploits to gain a competitive edge by accessing confidential information from rivals. Lastly, these attacks can be tools for cyberwarfare, orchestrated by nation-states targeting another country's digital infrastructure via disruptive long- and short-term attacks to gain advantage against utilities, economic institutions, strategic investment, and intellectual property – including state secrets.
Zero-day exploits have a wide reach, targeting everything from operating systems and web browsers to hardware and IoT devices. This vast spectrum of target devices is used by victims, including:
Targets can be specific or broad. Targeted zero-day attacks aim at high-value targets like government agencies or large corporations, while non-targeted attacks focus on exploiting any vulnerable system they can find. In the latter case, the objective is often to compromise as many users as possible, making no one truly safe from potential harm.
The backbone of a zero-day attack is built on several factors, including:
These factors are enablers for various harmful activities, but the delivery of exploit code is still needed to advance an attack. Delivery of an exploit can happen through various channels:
These exploits can also be bundled into an “exploit pack,” which probes the system for multiple vulnerabilities and delivers the exploit where it will be most effective. Once the code is executed, it can cause a range of damage—from data theft to rendering the system inoperable. Given the stealthy and sophisticated nature of these attacks, they are often hard to detect and prevent, necessitating advanced zero-day attack prevention strategies.
The world has witnessed several significant exploits over the years. Some of them even made it into the general news headlines, causing widespread panic among users. Below we list some major instances that shaped our understanding of this cybersecurity threat.
What makes defeating a zero-day threat so challenging is the definition; they remain unknown until they are exposed. Therefore, the most effective strategies involve multi-layered defenses that incorporate elements such as data analytics and machine learning algorithms.
Machine learning is trained using historical data on past vulnerabilities. This arms the system with the ability to detect malicious behaviors displayed by a new exploit of a novel vulnerability.
In the realm of cybersecurity, signature-based variant detection serves as one method for identifying threats. This technique employs digital signatures to immediately identify known exploits and variations of previously identified attacks. With behavior-based monitoring, defense mechanisms are looking for common malware tactics. It is a pretty hands-on approach.
User behavior analytics also play a crucial role. In a network, authorized users show predictable usage patterns. Inconsistent user behavior patterns, especially when broadly deviating from the norm, might indicate a zero-day attack. For instance, if a web server starts creating outbound connections where unexpectedly, it could suggest an exploit.
A hybrid detection approach combines all these methods to enhance zero-day threat identification. Such an approach uses databases of malware behavior continually enhanced by machine learning algorithms and behavior analytics to establish what is 'normal' to flag deviations. While traditional signature-based anti-malware may fall short in isolation, a multi-faceted strategy provides a robust defense against zero-day threats.
It's important to understand that zero-day attacks are virtually impossible to prevent; however, their impact can be significantly mitigated through robust and proactive cybersecurity measures.
As technology advances, providing richer capabilities, the complexity of applications and platforms increases. This expands the potential attack surface for cybercriminals, especially in configurations and identity and access management, making zero-day attacks more likely and challenging to address. Traditional fixes are not immediately available, therefore, a multi-faceted security strategy is mandatory, particularly in environments using multi-cloud or hybrid-cloud systems. While it's impossible to prevent zero-day attacks entirely, the goal should be to significantly reduce their impact and enhance the ability to respond effectively if they occur.
Security solutions should address vulnerabilities from multiple angles, rather than relying on singular approaches, while ensuring that security policies are consistently applied across all environments, including multi-cloud and hybrid-cloud systems.
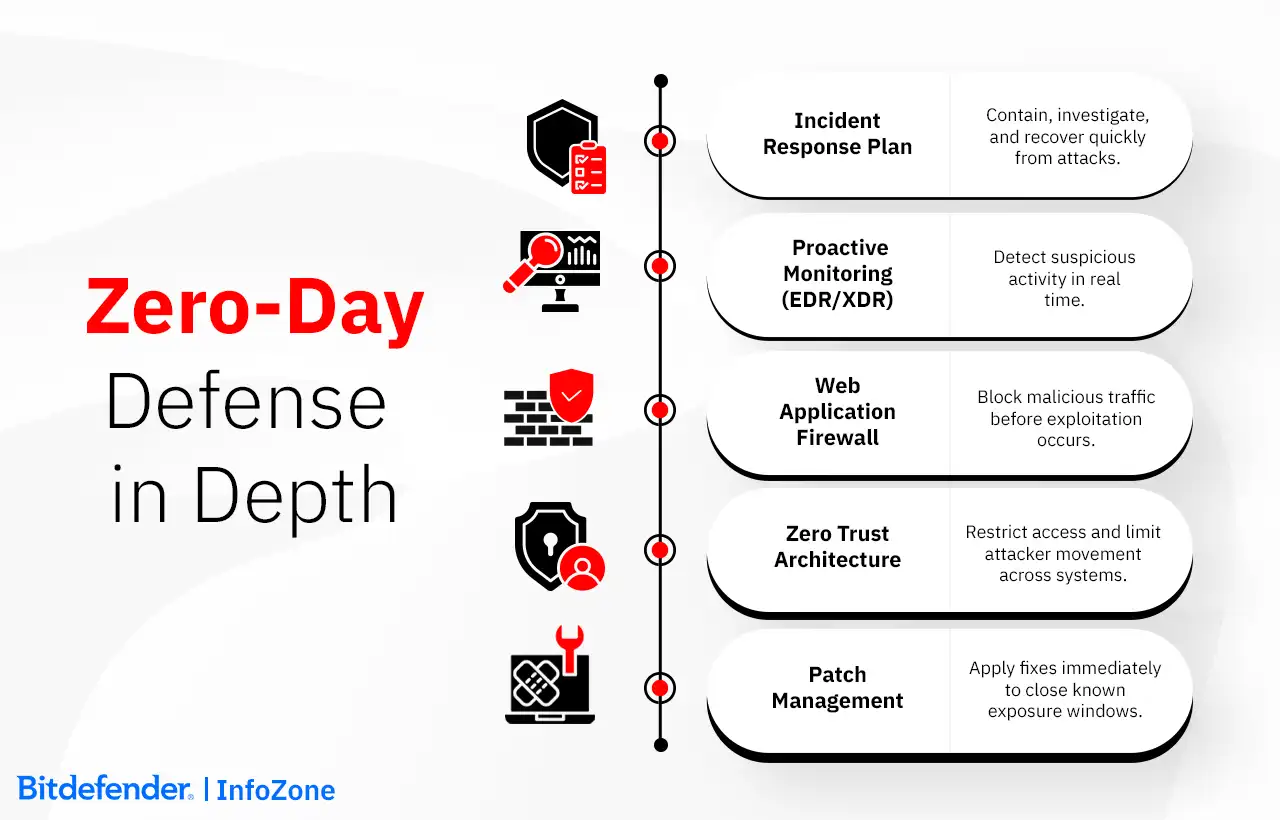
Keep Software and Systems Updated: Zero-Day exploits rely on the fact that software and systems are still not patched. This can be due to the fact that there is no patch yet or because the patch hasn't been applied yet. In order to benefit from the fact that software developers have discovered and fixed a vulnerability, timely updates on all your software and operating systems on a regular basis are essential. Software vendors frequently release security patches that address newly discovered vulnerabilities, but it's often your responsibility to apply them.
Assess and Analyze Software Usage: By reducing the number of installed applications, organizations can minimize potential vulnerabilities. One of the tools used in the decision process is Software Composition Analysis (SCA), which helps in identifying and evaluating the components of software, including both proprietary and open-source elements. This analysis can uncover hidden vulnerabilities within the software, aiding in the process of balancing security with software preferences.
Educate End-Users: Human error is a frequent avenue for zero-day exploits, and regular training on cybersecurity hygiene can significantly reduce this risk. Include training on secure password practices, identifying phishing attempts, and safe internet browsing habits, among others.
Apply Principle of Least Privilege (Zero Trust):
Have a Plan:
How cybersecurity solutions address zero-day vulnerabilities is a valuable differentiator when it comes to comparing their effectiveness. Bitdefender is recognized globally as one of the top-tier cybersecurity solutions also because it has consistently showcased exemplary performance in this arena, as numerous independent tests have proven.
In conclusion, Bitdefender's expertise against zero-day vulnerabilities is the result of a meticulously designed and implemented strategy that consistently delivers superior results.
How governments address zero-day exploits is a complex topic that varies by country, but there are some common regulatory specifics.
For instance, regarding disclosure policies, we can notice that governments often encourage researchers to notify software vendors of vulnerabilities before public disclosure so that they can issue patches.
A special focus is put on critical infrastructure regulations aimed at protecting vital services like power grids from zero-day attacks. Governments’ involvement with zero-day vulnerabilities is dual in nature. Most technologically advanced countries issue penalties for misusing zero-day vulnerabilities through fines or even imprisonment. At the same time, some governments retain zero-day vulnerabilities for intelligence purposes, stockpiling them for their own intelligence benefits.
Economically speaking, there are cases of export restrictions to curb cyberweapon proliferation. Also, in many countries, we can notice governments often partner with private firms for threat intelligence.
Although they are often used interchangeably, linguistically speaking, there is a difference in meaning. A "Zero-Day Exploit" refers to the actual technique used to take advantage of a vulnerability in software or hardware that is unknown to its developer.
On the other hand, a "Zero-day Attack" is the actual implementation of that exploit in the real world. In the simplest of terms, if the exploit is the "recipe," then the attack is the "cooking" of that recipe.
Zero-day vulnerabilities can be present in both new and old software. Delaying updates might avoid new vulnerabilities but leave you exposed to known issues fixed in the update. Instead, consider these steps:
· Research feedback on the update.
· Wait a bit after a new release for any rapid fixes.
· Maintain good cybersecurity practices, such as using reliable security software and backing up data.
· Stay informed about major vulnerabilities and their patches. Always prioritize safety, but remember that updates often bring security improvements as well.