Introducing Cloud Security Posture Management: The Key to Configuration Control

On January 15th Bitdefender started the Early Access Program (EAP) for a new functionality within Bitdefender GravityZone, Bitdefender CSPM+ (Cloud Security Posture Management +). This new module is part of an ongoing project that enhances the multi-layered security strategy and extends the prevention layer for all organizations with public cloud infrastructure footprints by defeating attacks before they cause damage.
Misconfigured cloud resources remain a key factor contributing to data breaches associated with cloud services. The root of this challenge is Cloud service providers use the Shared Responsibility model. It means cloud providers are responsible for ensuring the security of the cloud infrastructure and services, including the underlying hardware, network, and software components. What customers are responsible for includes securing their data, applications, identity access management, and configurations within the cloud environment.
Simply put, a common myth around cloud computing security is based on the misconception that someone else manages it. The reality is customers are responsible for ensuring the security of their cloud workloads which operate on the cloud platform. With Bitdefender CSPM+ organizations can manage their security and compliance risks without requiring deep cloud security expertise and broad teams.
Bitdefender CSPM+
Bitdefender CSPM+ includes not only Cloud Security Posture Management (CSPM) functionality, ensuring the secure and compliant configuration of cloud resources and services to identify and mitigate potential security risks and misconfigurations, but also Cloud Identity and Access Management Security (IAM). The IAM – sometimes referred to as CIEM (Cloud Infrastructure Entitlement Management) – functionality manages user identities and access permissions within the cloud environment. These integrated functionalities provide security and precise control over cloud resources, creating a comprehensive and secure cloud computing environment.
Complete Visibility Into Hybrid Cloud Environments
The CSPM+ management platform is a consolidated component of Bitdefender GravityZone. Integration enables full visibility into public cloud assets and identities on Amazon Web Services (AWS), Google Cloud Platform (GCP), and Microsoft Azure. Administrators can specify the scanning frequency for the cloud environment at the integration level, choosing between daily, weekly, or on-demand scans based on the dynamic nature of the cloud setup. This agentless integration collects and analyzes cloud configuration metadata from customer cloud footprints. Since CSPM+ integrates directly with the cloud provider on the management plane rather than using traditional, in-workload agents, it has zero impact on workload performance.
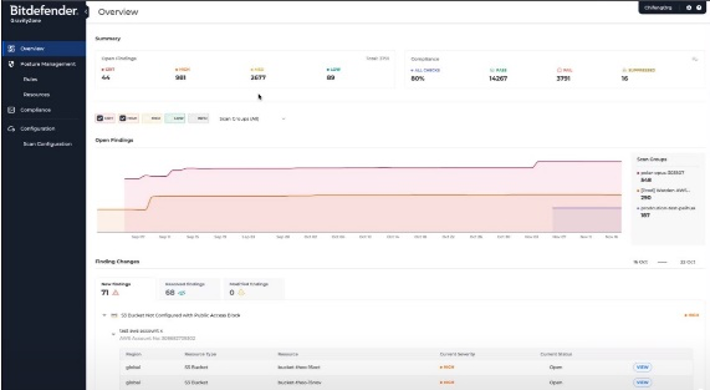
Bitdefender GravityZone CSPM+ management console.
Compliance Standards
Cloud Compliance is ensured through continuous security checks of the configuration of customer public cloud resources based on security standards and regulatory compliance frameworks, such as CIS and GDPR. Currently, Bitdefender GravityZone CSPM+ supports more than 20 frameworks and regulations. It includes frameworks like CIS, PCI DSS, NIST CSF, CCM, ISO 27001, SOC2, and GDPR. Also, it includes a collection of best practices for cloud resources, ensuring secure configurations for elements such as identities, databases, and compute instances.
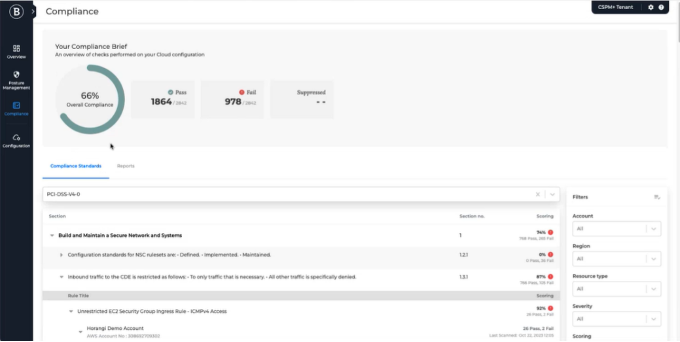
Bitdefender GravityZone CSPM+ Compliance
Security Rules for a Solid Cloud Foundation
Bitdefender GravityZone CSPM+ includes nearly 400 rules across all cloud providers. The rules are checks conducted in a cloud environment against international/local compliance standards. Rules monitor across all integrated multi-, hybrid-cloud environments and consolidate results into a single dashboard available for security teams.
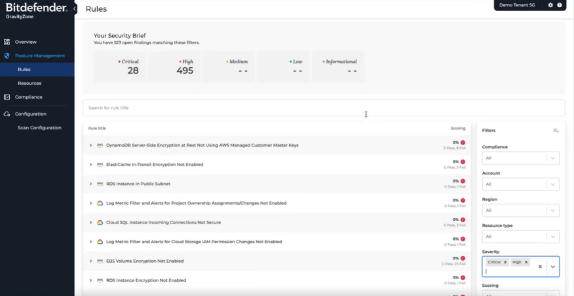
Bitdefender GravityZone CSPM+ Rules security findings.
After selecting a rule, the Check Details section provides the administrator with information about the rule checked (Pass or Fail), affected resources, and recommendations. It includes severity which indicates the importance level (critical, high, medium, or low), and a detailed description explaining the finding's significance regardless of cloud or security expertise. This allows the administrator to decide whether remediation or fixing is necessary. Administrators can accept the risk and suppress findings for a given period of time if remediation isn’t necessary or urgent, and include a justification to support future compliance audits.
Security Findings
To address issues, security teams collaborate with developers, the DevOps team, and the infrastructure team. The integrations we support in the Early Access phase allows administrators to export findings into ticketing tools like JIRA. The export includes the details such as rule title, account, severity, and resource type together with Manual Remediation (described in the next section of this article) and can be additionally commented on by the administrator, meaning security engineers do not have to log in to the Bitdefender GravityZone CSPM+ platform to view these findings and initiate actions. Relevant context on security issues is brought into existing user workflows rather than forcing all involved parties to come to the platform.
Practical Recommendations for Remediation
GravityZone CSPM+ not only alerts security teams with the security findings but also provides instructions on how to resolve them. This is crucial because we aim to ensure that the administrator can take immediate action based on the information from the console.
For every finding, the administrator is provided a Manual remediation which provides the administrator with step-by-step instructions on how to resolve issues with their cloud assets manually.

Bitdefender GravityZone CSPM+ Remediation description.
Additionally, depending on the cloud provider and the type of problem, administrators can leverage Terraform and Playbook Code configuration change examples.
Terraform Code Example uses a configuration language for managing infrastructure. By tailoring the configuration in the provided example and deploying the template again, the administrator can fix the identified findings.
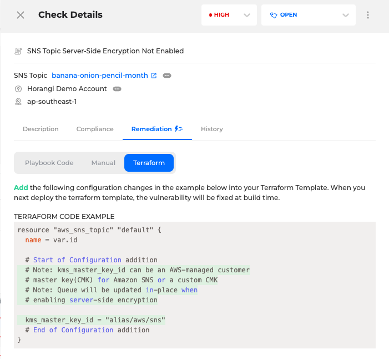
Bitdefender GravityZone CSPM+ Terraform Code example.
In Playbook Code, the administrator is provided nodejs javascript code written by us and automatically generated by the platform. The code can be reviewed by the administrator, and after logging in to the cloud security provider with sufficient permissions, the administrator can simply copy the code from Bitdefender GravityZone CSPM+ and paste it into the cloud CLI to fix the findings.
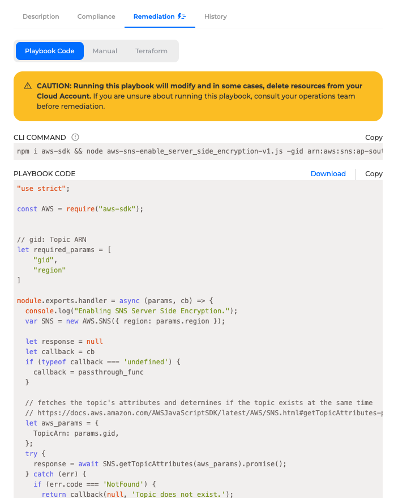
Bitdefender GravityZone CSPM+ Playbook Code example.
Getting Started With Bitdefender CSPM+
All existing customers running cloud workloads on AWS, GCP, and Azure can join the early access phase of the Bitdefender CSPM+ solution. To obtain a dedicated CSPM+ license key, please contact your Bitdefender representative. The license will remain active until the end of February 2024. Once the license key is activated and the account is enrolled in the GravityZone Cloud Security early access program, the feature will be made available via the GravityZone Control Center console. Instructions on how to join the Early Access program and initiate the configuration can be found in the GravityZone Knowledgebase. New customers, before joining EAP, will need to request the trial license for Bitdefender GravityZone here.
Summary
Bitdefender GravityZone CSPM+ is a comprehensive CSPM and Cloud Identity and Access Management (IAM) solution designed to help organizations manage security and compliance risks in various cloud environments. The turnkey integrations with AWS, GCP, and Azure allow administrators to have full visibility into cloud assets and identities. Continuous security checks, compliance monitoring, and remediation options are provided to ensure secure configurations for cloud resources to overcome complexity and focus on enhancing security team productivity.
tags
Author
Grzegorz Nocon is a graduate of the Faculty of Physics at the University of Silesia. With over 16 years of experience in the IT industry, he currently works as a Technical Marketing Engineer at Bitdefender. A strong supporter of a holistic approach to security and passionate about solving security problems in a comprehensive and integrated way. Outside of work, an avid CrossFit enthusiast and a lover of fantasy literature.
View all postsYou might also like
Bookmarks


