Bitdefender discovers emerging IoT botnet that uses custom-built peer-to-peer communication

Bitdefender researchers have uncovered an emerging botnet comprised of infected IoT devices such as DVR cameras, routers, NAS devices and other types of networking equipment.
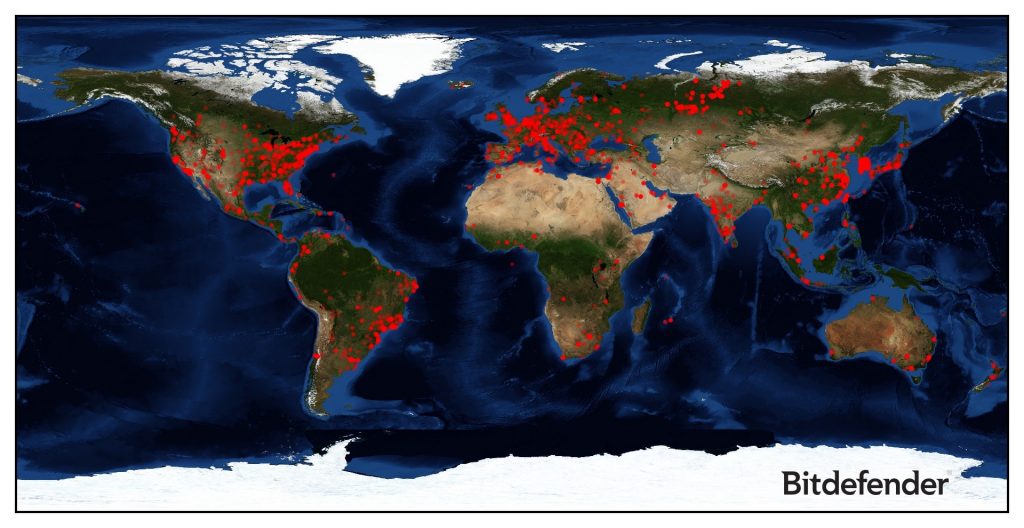
The botnet included hundreds of devices on January 10 when Bitdefender researchers discovered it. Since then, it has enrolled more than 18,000 devices, including 12,000 that were compromised in less than one day. At the time of writing, the botnet has recruited devices from all over the world.
Dubbed HNS, this botnet targets specific devices that are susceptible to several known vulnerabilities by running exploit code against them, but it also attempts to force its way into devices by trying to log into the Telnet service using passwords in a built-in dictionary file.
If you have deployed a Bitdefender BOX in your network, you are already protected against this type of attack, as its AI-powered anomaly-detection technology picks up telltale signs and blocks it before it reaches the vulnerable device.
Here are some things you should do if you have smart devices connected to your network:
– Make sure all your devices are running the latest firmware versions available from the vendor. Check regularly for newer versions of firmware, as your vendor issues code updates to fix vulnerabilities and plug attack avenues.
– Set strong passwords for all devices that require one, and don’t forget the home router. Never leave devices protected with the default factory-set credentials .
– Get a security solution for Internet of Things devices, such as the Bitdefender BOX. This stops the attacks cold, and the Vulnerability Detection feature keeps you informed about your network’s weak spots at all times as well.
If you want to learn more about this new threat, what it targets and how it operates, check out the bot’s technical description on the Bitdefender Labs blog.
tags
Author

Bogdan is living his second childhood at Bitdefender as director of threat research.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks









