FDA to demand medical smart device makers undertake strict cybersecurity checks before selling to HCPs

The U.S. Department of Health & Human Services Office of Inspector General (OIG) has proposed the Food & Drug Administration (FDA) change its internal processes to better address cybersecurity of medical devices before approving their sale to healthcare providers (HCPs).
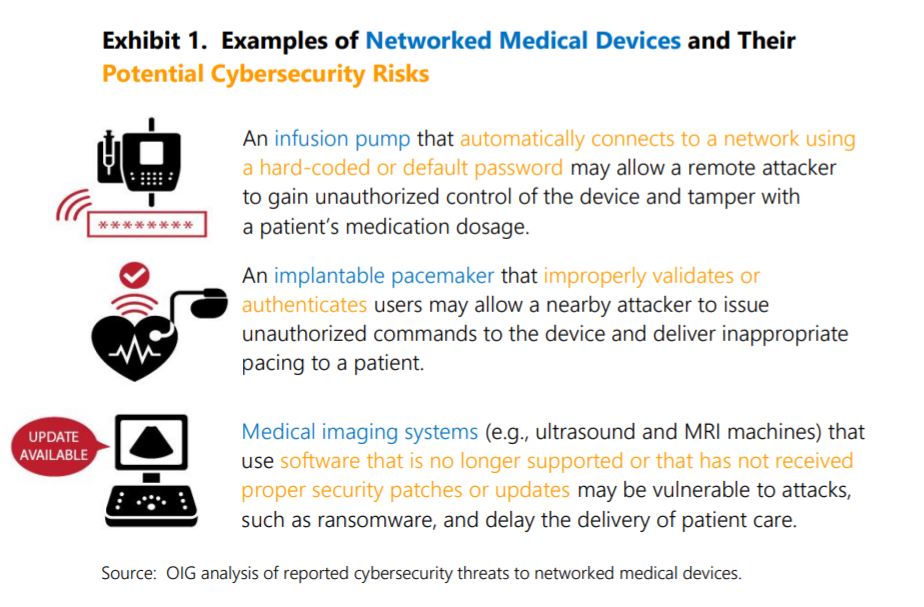
Healthcare is among the verticals most targeted by cybercriminals. In the case of medical smart devices, bad actors could take advantage of certain vulnerabilities to administer the wrong dosages or cause the device to malfunction, seriously jeopardizing patients’ lives.
To examine the FDA’s review of cybersecurity in premarket submissions for networked medical devices, the OIG interviewed FDA staff who carry out and manage the reviews and interviewed members of the FDA’s Cybersecurity Workgroup. The OIG examined a nonrepresentative sample of 22 submissions and FDA reviewer notes for networked medical devices that the FDA cleared or approved in 2016. It then reviewed FDA policies, procedures, and guidance documents related to cybersecurity and its medical device review process.
In its guidelines, it acknowledges that the FDA is already doing a lot to compel medical smart device vendors to conduct proper security checks before rolling out products. FDA reviewers consider known cybersecurity risks and threats when reviewing submissions and apply that knowledge to devices with similar risk profiles. For example, if the FDA identifies a vulnerability in a certain cardiac device from a specific manufacturer, it then considers that same threat in evaluating submissions for similar products from other vendors.
Furthermore, FDA reviewers often request additional information from manufacturers when submissions lack sufficient cybersecurity documentation or when clarification is needed for approval. Still, the OIG feels more can be done.
The FDA now faces a task similar to that of the government officials in the UK who are in charge of prompting IoT vendors to implement “security by design” in their products.
The FDA’s “Refuse-To-Accept” checklist, which it uses to screen submissions for completeness, currently has no checks for cybersecurity information. Also, the agency’s “Smart” template (used to guide its reviews of submissions) does not give FDA reviewers specific cybersecurity questions to consider. It also lacks a dedicated section for recording the results of the cybersecurity review.
“We recommend that FDA promote the use of presubmission meetings to address cybersecurity-related questions, include cybersecurity documentation as a criterion in FDA’s Refuse-To-Accept checklists, and include cybersecurity as an element in the Smart template,” the OIG says.
The OIG says FDA reviewers should consider withholding an approval until the manufacturer provides the cybersecurity information needed to assess the networked medical device’s risks and the controls to mitigate those risks.
According to the report, the FDA concurred with all recommendations. However, no deadline appears to be set for the new policy to take effect.
tags
Author
Filip has 15 years of experience in technology journalism. In recent years, he has turned his focus to cybersecurity in his role as Information Security Analyst at Bitdefender.
View all postsRight now Top posts
Start Cyber Resilience and Don’t Be an April Fool This Spring and Beyond
April 01, 2024
Spam trends of the week: Cybercrooks phish for QuickBooks, American Express and banking accounts
November 28, 2023
3 in 5 travel-themed spam emails are scams, Bitdefender Antispam Lab warns
August 10, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks







