New Nebulae Backdoor Linked with the NAIKON Group
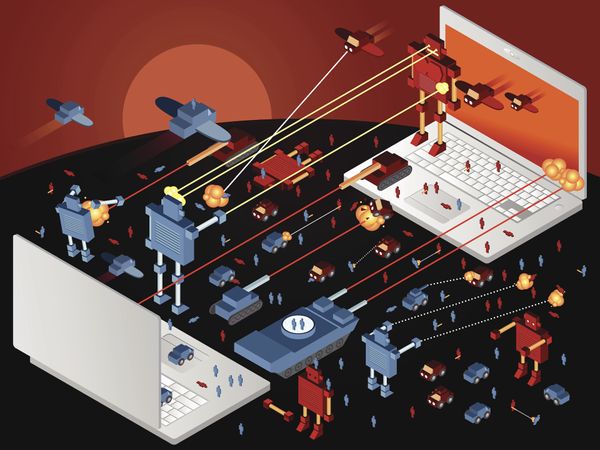
DLL hijacking is a malware execution technique that hardly needs any introduction. But while spotting DLL hijacking vulnerabilities would get mots security researchers bounty or a mention in a hall of fame, our investigation of sideloading techniques in several vulnerable applications led to the discovery of a long-running operation of a notorious APT group known as NAIKON.
Unlike previous NAIKON operations, the one documented in the whitepaper below features a secondary backdoor that has an important role in persistence. We called it Nebulae.
Who is NAIKON?
NAIKON is a threat actor that has been active for more than a decade. Likely tied with China, the group focuses on high-profile targets such as government agencies and military organizations in the South Asia region.
Targets
During our investigation, we identified that the victims of this operation are military organizations located in Southeast Asia. The malicious activity was conducted between June 2019 and March 2021. At the beginning of the operation, the threat actors used Aria-Body loader and Nebulae as the first stage of the attack. From our observations, starting with September 2020, the threat actors included the RainyDay backdoor in their toolkit. The purpose of this operation was cyber-espionage and data theft.
Mitigation
Bitdefender enables organizations to contend with APT style attacks with GravityZone endpoint detection and response (EDR) and managed detection and response (MDR) services that apply the MITRE ATT&CK framework for identifying and remediating security incidents throughout the entire attack kill chain.
For more detailed information about the investigation, please check out the full paper below:
tags
Author

Victor VRABIE is a security researcher at Bitdefender Iasi, Romania. Focusing on malware research, advanced persistent threats and cybercrime investigations, he's also a graduate of Computer Sciences.
View all postsRight now Top posts
Infected Minecraft Mods Lead to Multi-Stage, Multi-Platform Infostealer Malware
June 08, 2023
Vulnerabilities identified in Amazon Fire TV Stick, Insignia FireOS TV Series
May 02, 2023
EyeSpy - Iranian Spyware Delivered in VPN Installers
January 11, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks
















