Five Easy Steps to Strengthen the Security of Your Google Account

Internet users today are more wary than ever about their digital security. Major cybersecurity incidents occur almost weekly, catching their attention. The pandemic has also helped raise our understanding of the cyber risks of working remotely. At Bitdefender, we strive to empower our readers to set their own ground rules for security and privacy. Google is one of the world’s most popular internet services, and it’s commendably one of the most transparent when it comes to security and privacy. While privacy deserves its own future guide, today we’ll look at the five key security settings that help you keep your account secure.
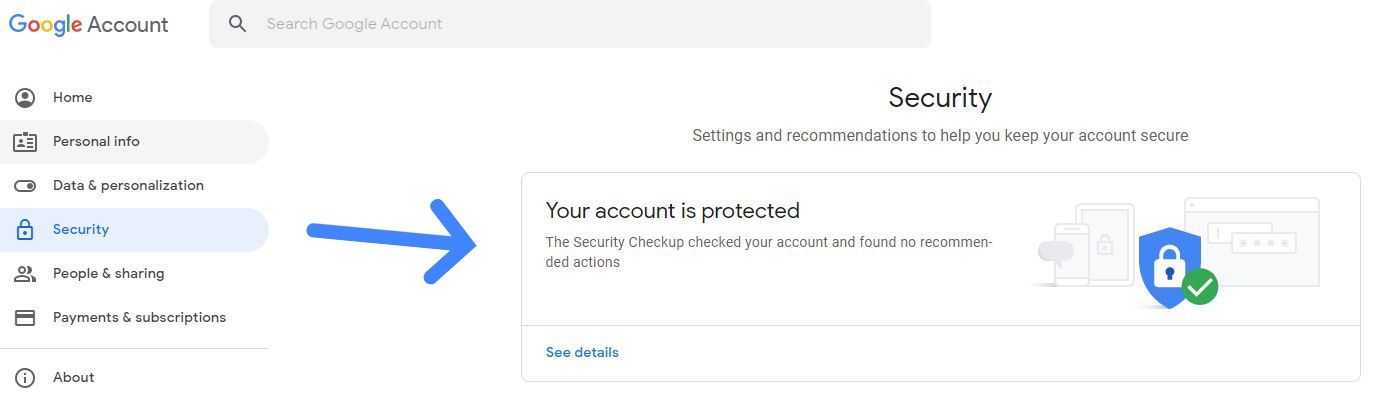
The Security pane in your Google Account settings offers a plethora of ways to strengthen and tweak your account’s security. Chief among them is the Security Checkup module, which offers the most important settings related to the security of your Google Account. Log in to your account and click on your profile pic, then select:
Manage Your Account -> Security -> Security Checkup
1. Unlink old or unfamiliar devices
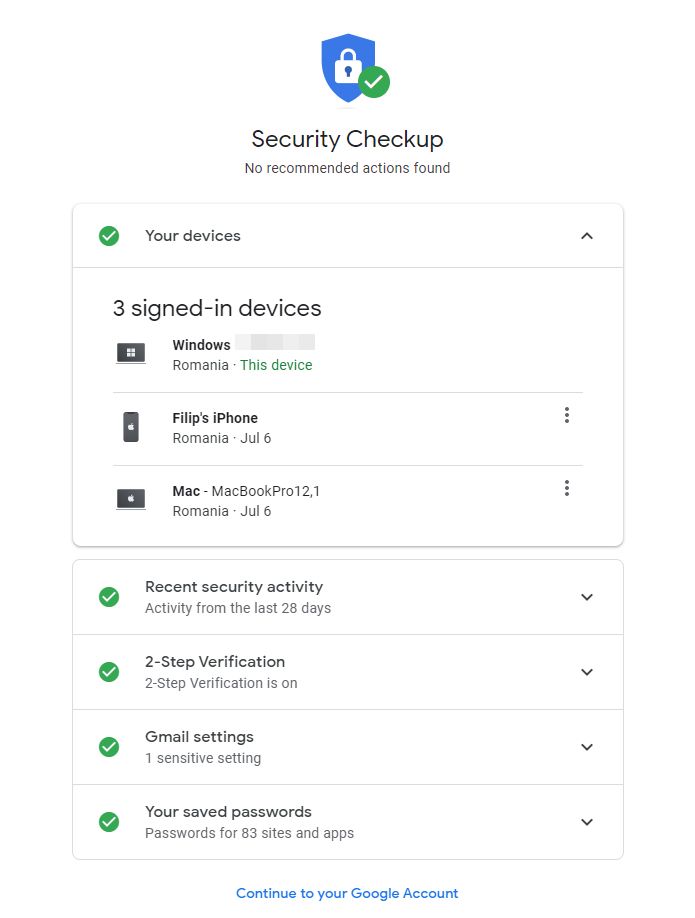
Here, you can:
· Check what devices are associated with your Google account
· Sign out of devices you’re not currently using Google with
· Unlink devices you no longer want associated with your Google account.
It’s strongly advised to use this feature periodically to make sure you haven’t forgotten about an old device still linked to your account. You never know who ends up accessing your account without your permission. In short, make sure your account is only linked to the trusty devices you regularly use.
2. Check recent security activity
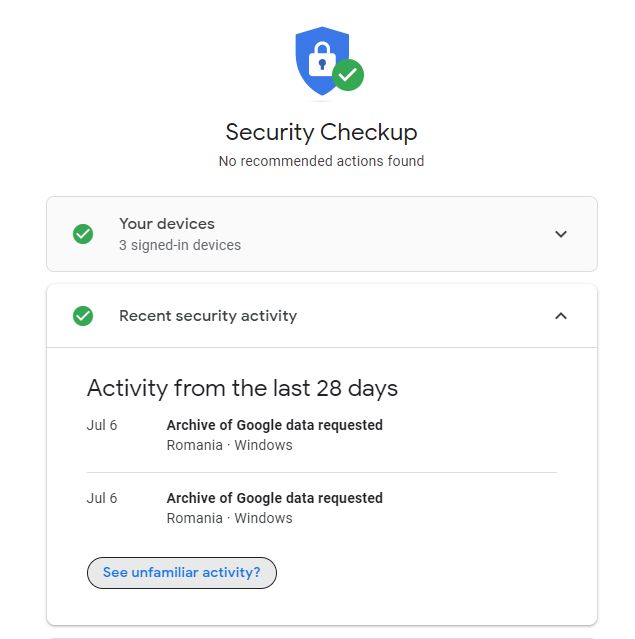
This module is more or less your news feed regarding activity that may pose security risks to your account. For example, Google keeps tabs when you log in from different devices or geographical zones to help you notice suspicious activity. In the example above, Google informs that the user requested two archive downloads on June 6. If you ever see such activity and haven’t requested a copy of your data, log out of all your devices and change your password immediately.
3. Keep two-step verification enabled at all times
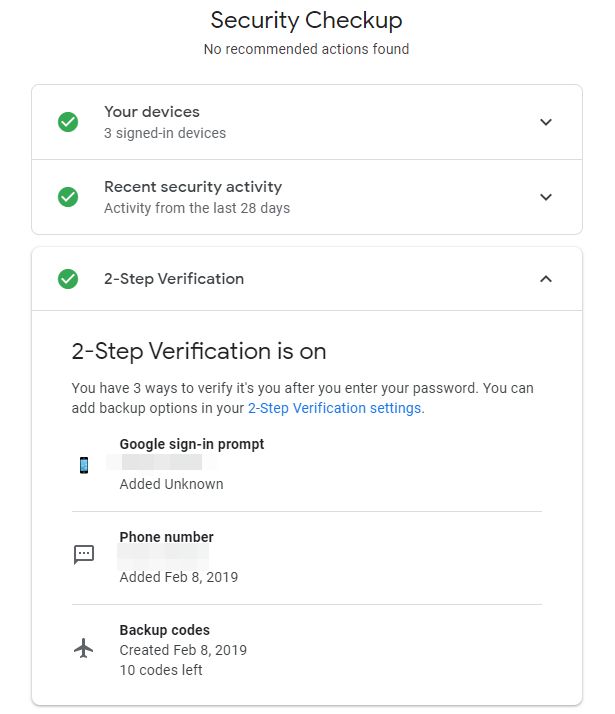
Also known as two-factor authentication (abbreviated 2FA), the two-step verification feature ensures that you are prompted to authorize access to your account from a secondary platform or device. Think of it as a bank vault door that can only be opened with two keys, turned simultaneously. You have multiple ways to do this, including your phone number (SMS code), Google Authenticator, the YouTube app on your phone, or even backup codes that you can download and store for later use.
These days almost every major company enforces two-step verification. It is probably the single most important setting you should never switch off, if you want your account protected.
4. Review your email settings
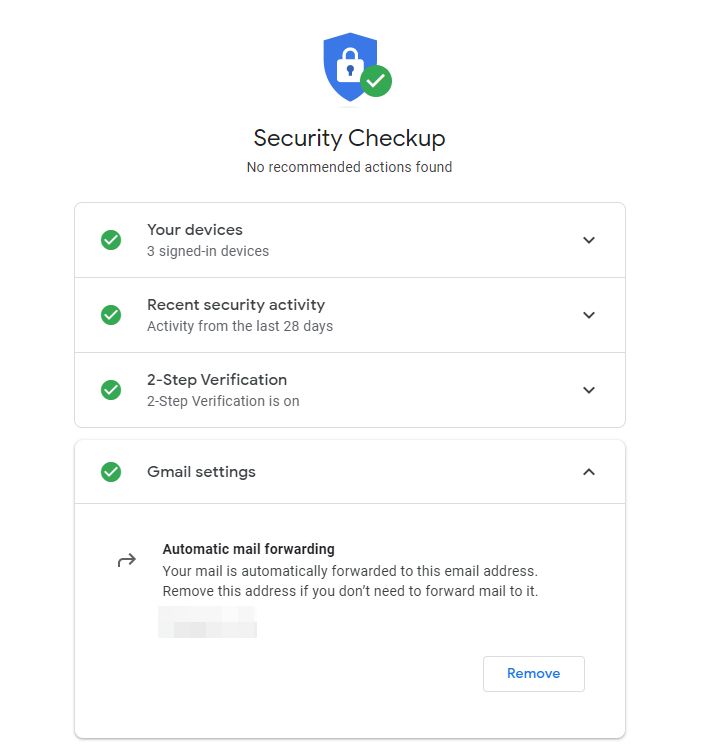
Most people rarely tinker with the settings in Gmail, but sometimes it’s important to remember the way your account is configured so you can expect that behavior or don’t run into conflicting settings that may affect your security or privacy. In this example, email forwarding is on, with the recipient’s address mentioned and an option to remove it if necessary.
5. Manage saved passwords
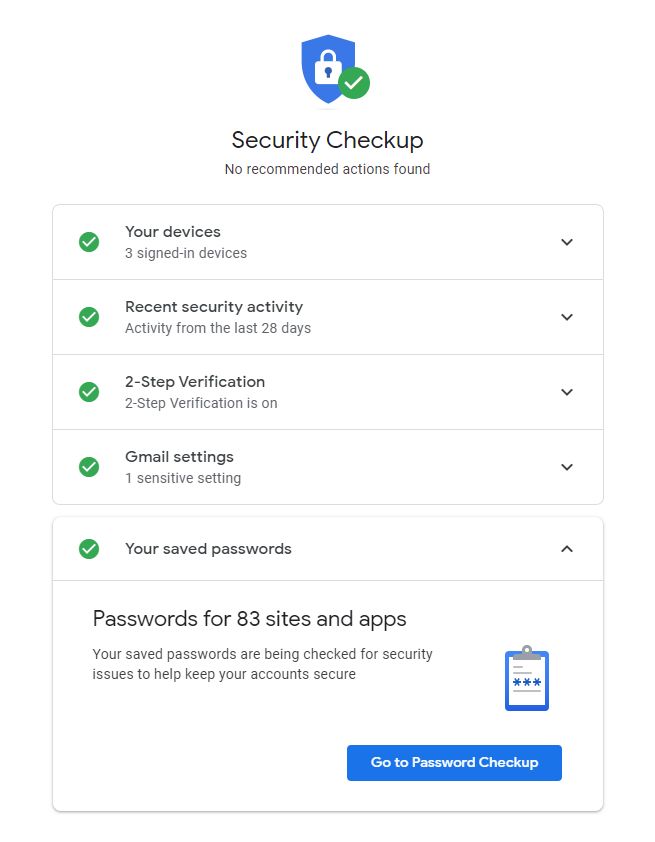
Google Chrome does a great job of keeping our passwords tucked away nice and safe. But it can only do so much. If you recycle passwords (i.e reuse the same password across multiple Internet accounts) you run the risk of having all those accounts compromised if only just one of them is compromised. That’s why it’s important to use unique passwords for each of your online personas. Google also flags weak passwords. This module helps you get on the right track with clear and simple instructions.
Stay safe out there!
In a future post we will take a look at the Privacy & Personalization features inside Google, so you can stay on top of that as well. In the meantime, be sure to apply all the tips mentioned above and use a trusted security solution on your computer and mobile phone for maximum security and peace of mind.
Bitdefender Total Security offers unbeatable threat detection to stop sophisticated malware on both Windows and Mac. Multi-layer ransomware protection keeps your files safe and VPN secures your online privacy. Parents can even use a range of advanced parental controls to keep their kids safe online, while the impact on your system performance is minimal.
Bitdefender Mobile Security for iPhone or Android offers full protection against mobile-specific threats, plus a secure VPN for a fast, anonymous and safe experience while surfing the web. It helps you secure your passwords, private data and financial information, and instantly alerts you whenever an incident is detected and prevented.
Bitdefender Digital Identity Protection enables you to check your online accounts against data breaches, find your private information online in legal and illegal collections of data, detect your social media impersonators and more.
tags
Author
Filip has 17 years of experience in technology journalism. In recent years, he has focused on cybersecurity in his role as a Security Analyst at Bitdefender.
View all postsYou might also like
Bookmarks
