Triout Android Spyware Framework Makes a Comeback, Abusing App with 50 Million Downloads

In August 2018, Bitdefender researchers stumbled across an Android malware framework, dubbed Triout, which packed massive surveillance capabilities.
Bundled with a legitimate application ripped from the official Google Play marketplace, the spyware framework can hide its existence on the device, record phone calls, log incoming text messages, record videos, take pictures, and even collect GPS coordinates. All of this information is sent to a Command & Control server managed by the threat actors, without triggering alarms from its victims.
The previous version of the spyware framework was bundled within an application that displayed adult content, but Bitdefender researchers have found a new tainted app that disseminates the malware.
Using Privacy as Bait
The “com.psiphon3” package name is a popular application in Google’s official Android app store that promises a means to bypass censored or blocked websites by leveraging a series of proxies. The application has over 50 million installs and over 1 million reviews (mostly positive), meaning its popularity might have been abused by threat actors to repackage it with the spyware framework.
Ironically, while the original legitimate application is advertised as a privacy tool that enables access to the open internet, when bundled with the Triout spyware framework it serves the exact opposite purpose.
While it’s not distributed using the official Google Play marketplace, but through third party ones, the tampered application has the same malicious code as the version previously analyzed. It also comes bundled with three adware components – Google Ads, Inmobi Ads, Mopub Ads – to generate some revenue on the side for threat actors.
The investigation
We first spotted the new tampered application on October 11th 2018, while it seems to have been active from May 2nd 2018 all through December 7th 2018. During this time, the malicious application was apparently scanned from 7 different devices, including 5 from the Republic of Korea and 2 from Germany. While the number of victims that we know of based on our telemetry is relatively small, it’s difficult to estimate exactly how many there are on a global scale.
When analyzing the sample (MD5: 7ed754a802f0b6a1740a99683173db73 Package Name: com.psiphon3 Signed with Debug Certificate: SHA:
61ed377e85d386a8dfee6b864bd85b0bfaa5af81) we found the same malicious code as in the previous iteration. The new infected package packs the same functionalities as the previous version but bears the name “psp.jsp.datamd”.
What’s interesting about the new Triout sample is that the C&C (Command & Control) server the threat actors use to smuggle the data and control infected devices is now different. The new C&C IP address (“188.165.49.205”) is still operational at the time of writing and seems to point to a French website (“magicdeal.fr”) that displays deals and discounts for various products.
It is currently unknown whether the website is a decoy or a legitimate website that the threat actors compromised to use as a C&C server.
Both the legitimate app and the tampered version look and act the same in terms of user interface and functionalities, meaning that attackers only focused on adding the Triout spyware component without raising any suspicion from victims.
However, the tampered version seems to have used the v91 version of the original application when distributing the Triout spyware. The current version of the legitimate app – at the time of writing – is v241.
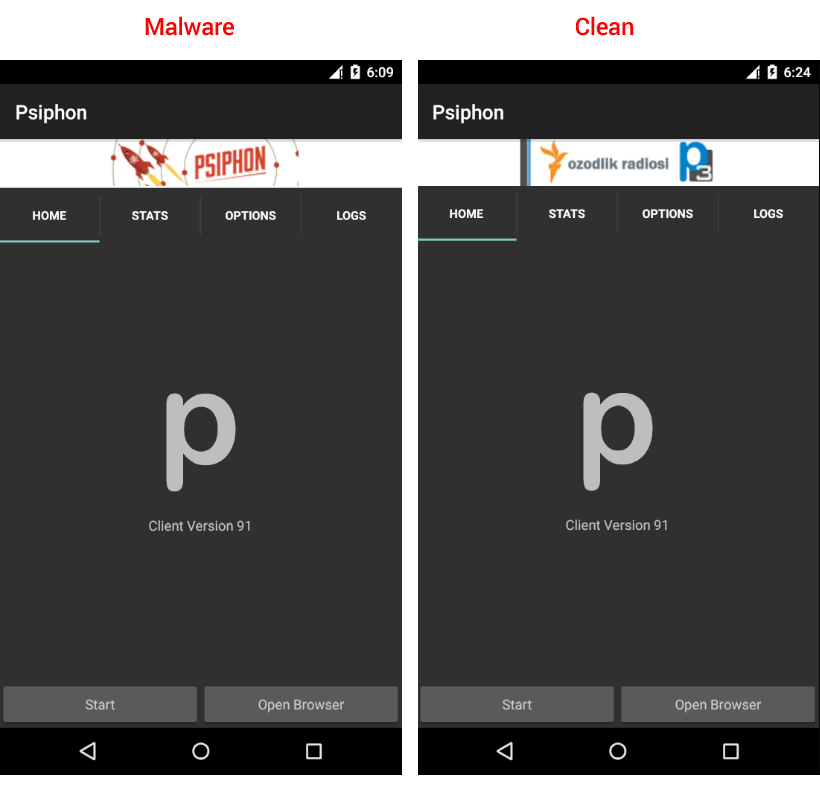
Fig. 1 – Malware vs. Clean App
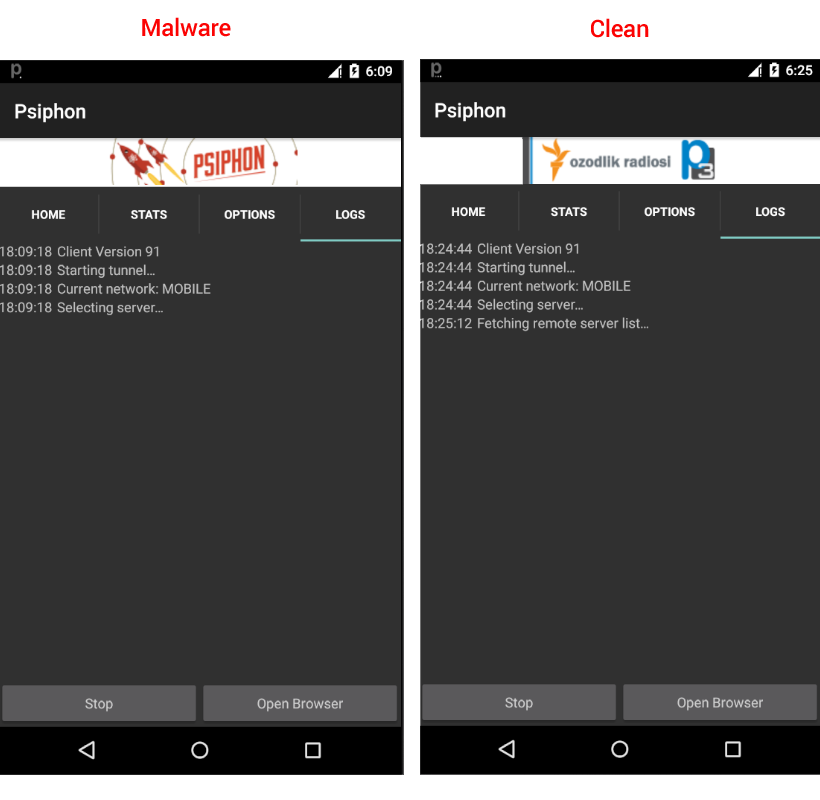
Fig. 2 – Malware vs. Clean App
Takeaways
The proliferation of Android devices has renewed interest from threat actors in developing malware and spyware frameworks. The ubiquity of these devices in our daily lives, the level of information they can access, and the amount of sensors they’re equipped with (e.g. camera, microphone, GPS, etc.) turn them into the perfect spies if weaponized by malware.
While the Triout Android spyware framework itself does not seem to have undergone changes in terms of code or capabilities, the fact that new samples are emerging and that threat actors are using extremely popular apps to bundled the malware, may herald more incidents such as this in the near future.
It’s also worth considering that that the low number of victims and infected devices, coupled with the fact that it packs powerful spyware capabilities, could indicate that Triout is mostly used in highly targeted espionage campaigns aimed at a few individuals.
To steer clear of these threats, it’s best to install apps only from official marketplaces, always use a mobile security solution that can spot Android malware, and constantly keep your Android operating system up to date with the latest security updates.
Note: This article is based on technical information provided courtesy of Cristofor Ochinca – Security Researcher, Bitdefender.
tags
Author
Liviu Arsene is the proud owner of the secret to the fountain of never-ending energy. That's what's been helping him work his everything off as a passionate tech news editor for the past few years.
View all postsRight now Top posts
Infected Minecraft Mods Lead to Multi-Stage, Multi-Platform Infostealer Malware
June 08, 2023
Vulnerabilities identified in Amazon Fire TV Stick, Insignia FireOS TV Series
May 02, 2023
EyeSpy - Iranian Spyware Delivered in VPN Installers
January 11, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks















