Reveton / IcePol Ransomware Moves to Android

It was just a matter of time until the highly prolific gang behind the Reveton / IcePol network made a move on Android. This shouldn’t be much of a surprise, given that Android is the world’s dominant mobile operating system.
The sample we stumbled on this week is a simple piece of Android ransomware dubbed Android.Trojan.Koler.A delivered automatically while the victim is browsing malicious porn sites.
It is the same sample that has been documented by independent security researcher Kafeine on the MalwareDontNeedCoffee blog.
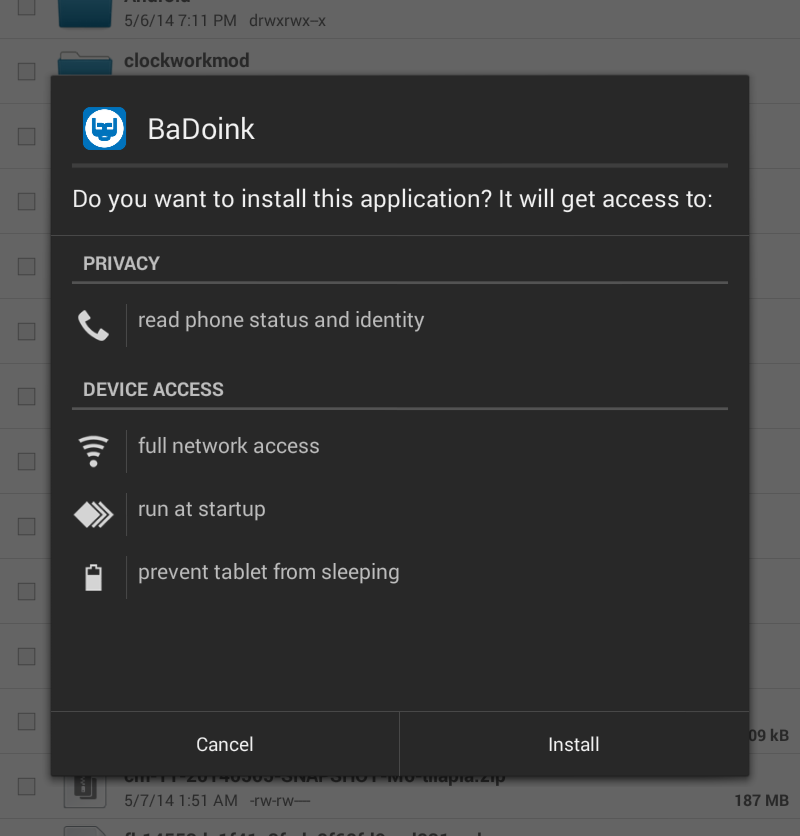
As the user browses, an application that claims to be a video player used for premium access to pornography downloads automatically. Unlike the Windows-based Reveton that is delivered via zero-interaction exploits, Koler.A still requires the user to enable sideloading and manually install the application.
Once in, the Trojan launches a browser on top of the Home screen and briefly displays a logo of the player it impersonates:
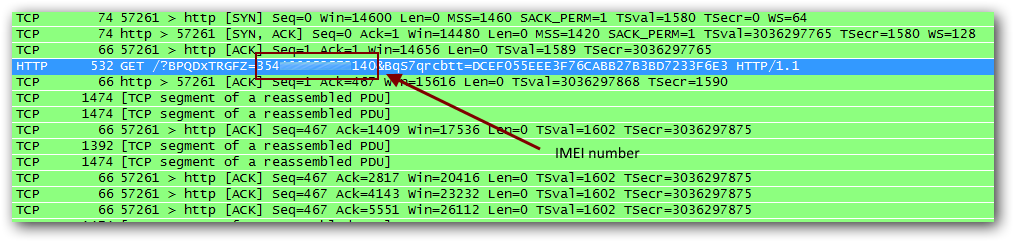
Meanwhile, the APK calls home to one of the over 200 domains known to be involved in the scheme. It also sends the device’s IMEI along with the GET requests, as well as a key that appears to be identical for all infections.
The server identifies the victim’s location via an IP to Geo lookup and responds with the HTML page localized in the victim’s language. Here are some examples of lock screens for various countries:
Ransomware lock-screen for US-based victims.
Ransomware lock-screen for British victims.
Ransomware lock-screen for Swedish victims.
Ransomware lock-screen for Danish victims.
The Trojan disables the back button, but still lets you briefly return to the Home screen. After you press the Home screen, you have five seconds to uninstall the APK before a timer brings the malicious application back to the foreground. This goes on every five seconds until you pay the ransom.
Although the message claims the stored data is encrypted, the application does not have the permissions it needs to touch files; it’s a lie to push users into paying the $300 ransom.
The bad news is that, by the time you see the message, the bad guys already have your IMEI on file. The good news is that Koler.A can be easily removed by either pressing the home screen and navigating to the app, then dragging it on the top of the screen where the uninstall control is located, or by booting the device in safe mode and then uninstalling the app.
Koler.A is the second piece of ransomware we know of to date, after the Fakedefender Trojan discovered in September last year. Its functionality is very limited, but the APK code is highly obfuscated, either to deter analysis, or to prevent a wannabe cyber-criminal from modifying the binary and using it for his own profit.
The Android version of Icepol might be a test-run for cyber-criminals to see how well this type of scam can be monetized on mobile platform. If this is the case, we should expect much more sophisticated strains of ransomware, possibly capable of encrypting files, to emerge shortly.
tags
Author
Right now Top posts
Infected Minecraft Mods Lead to Multi-Stage, Multi-Platform Infostealer Malware
June 08, 2023
Vulnerabilities identified in Amazon Fire TV Stick, Insignia FireOS TV Series
May 02, 2023
EyeSpy - Iranian Spyware Delivered in VPN Installers
January 11, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks