Mandrake - owning Android devices since 2016
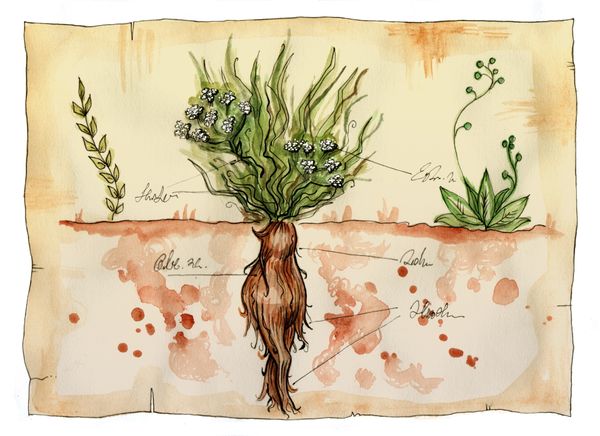
In early 2020 we identified a new, highly sophisticated Android espionage platform that had been active in the wild for at least 4 years. We named the threat Mandrake as the actor(s) behind it used names of toxic plants, or other botanical references, for major development branches: e.g. Briar, Ricinus or Nerium.
An investigation by Bitdefender researchers Marius TIVADAR, Rickey GEVERS, Rareș BLEOTU, Alin Mihai BARBATEI, Bíró BALÁZS and Claudiu COBLIȘ
An incredibly sophisticated piece of Android malware
Unlike run of the mill malware, Mandrake puts in significant effort NOT to infect victims. It cherry-picks a handful of devices it gets installed on for further exploitation. This is likely because its operators know that they increase their chances of being called out with every device they infect, so they have instructed the malware to avoid countries where compromised devices won’t bring them any return of interest.
The malware also uses advanced manipulation tactics to bait users. For instance, it re-draws what the user sees on the screen to hijack taps. What the users perceive as accepting an End-User License Agreement is actually a complex series of requesting and receiving extremely powerful permissions. With those permissions, the malware gets complete control of the device and data on it.
If you want to learn more about Mandrake, the whitepaper below provides insight into how the malware operates, what its end goal seems to be and how it successfully managed to stay undetected in an official app store for more than 4 years.
tags
Author
I am continuously focusing on remediation of Android threats with everything that this involves; I can’t get too picky. I like to read and go hiking in my spare time, and I also do a bit of kirigami.
View all postsI'm a security researcher at Bitdefender with a focus on threats like rootkits and bootkits. I'm also passionate about Automotive Communication Protocols and Real Time Embedded Systems.
View all postsI'm a security researcher at Bitdefender working on cybercrime investigations and developing tools to help with malware and forensics analysis. In my free time, I learn new things and play video games
View all postsYou might also like
Bookmarks








