Darkside Ransomware Decryption Tool

We’re happy to announce the availability of a decryptor for Darkside. This family of ransomware has emerged in August 2020 and operates operate under a ransomware-as-a-service business model.
How to use this tool
Step 1: Download the decryption tool below and save it on your computer.
Download the Darkside decryptor
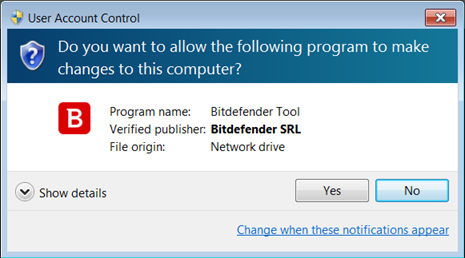
Step 2: Double-click the file (previously saved as BDDarkSideDecryptor.exe) and allow it to run.
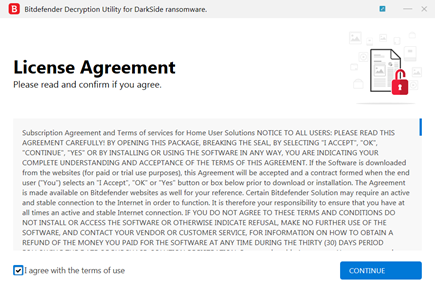
Step 3: Select “I Agree” in the License Agreement screen
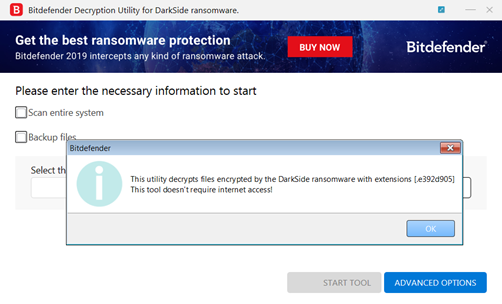
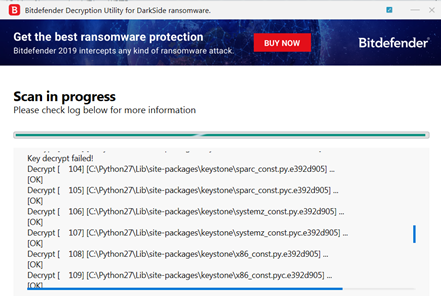
Note: The tool attempts to identify the file extension of the encrypted files automatically. In this example, the encrypted files have the *.e392d905 extension. Please make sure that you have encrypted files on the system you are running the tool.
Step 4: Select “Scan Entire System” if you prefer the tool to search for all encrypted files. Alternatively, add the path to the location you previously moved the encrypted files.
We strongly recommend that you also select “Backup files” before starting the decryption process to avoid potential loss or corruption during decryption. Then press “Start Tool”.
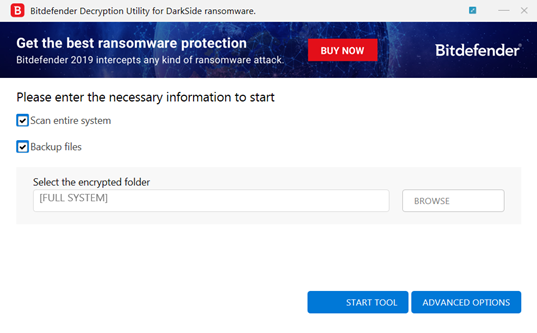
At the end of this step, your files should be decrypted.
If you encounter any issues, please contact us at [email protected].
If you have checked the backup option, you will see both the encrypted and decrypted files. You can also find a log of the decryption process in the %temp%\BDRemovalTool folder.
To remove the encrypted files left behind, you should search for files matching the extension and mass-remove them. We do not encourage you to do this until you made sure that your files can be opened safely and there is no damage to the decrypted files.
Acknowledgement:
This product may include software developed by the OpenSSL Project, for use in the OpenSSL Toolkit (http://www.openssl.org/)
tags
Author

The meaning of Bitdefender’s mascot, the Dacian Draco, a symbol that depicts a mythical animal with a wolf’s head and a dragon’s body, is “to watch” and to “guard with a sharp eye.”
View all postsRight now Top posts
Infected Minecraft Mods Lead to Multi-Stage, Multi-Platform Infostealer Malware
June 08, 2023
Vulnerabilities identified in Amazon Fire TV Stick, Insignia FireOS TV Series
May 02, 2023
EyeSpy - Iranian Spyware Delivered in VPN Installers
January 11, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks













