Locky ransomware disguises itself as account suspensions and suspicious movements
One of the golden rules of computer security for the last twenty-or-so years has been to be extremely cautious of unsolicited emails.
It’s one of the favourite methods used by cybercriminals to trick unsuspecting computer users into opening dangerous attachments or clicking on a link to a malicious webpage.
The method has been proven to be successful time and time again, especially when combined with cunning social engineering tricks to dupe victims into clicking before they have applied some good old-fashioned common sense.
In the last few days there have been a spate of spammed-out attacks using similar techniques to dupe unwary internet users into clicking on an attachment that will lead to their Windows PC being infected with the notorious Locky ransomware.
For instance, you might have seen messages like the following appearing in your inbox, claiming that there have been “suspicious movements” of funds out of your bank account.
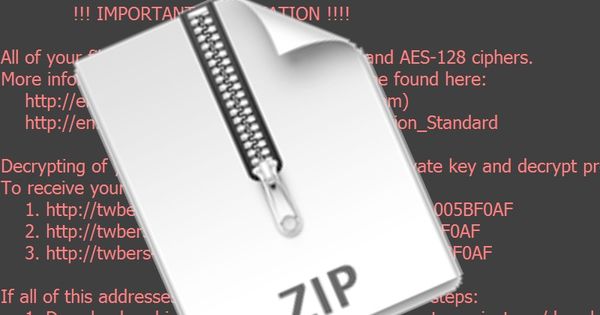
Attached to the email is a ZIP file containing a malicious .JS (Javascript) file, that if opened downloads a version of the Locky ransomware from a remote server from one of five different URLs, saved in a temporary folder under the name “GyFsMGsLUNA.dll”.
The malware is executed without any requirement for further user interaction. Bitdefender anti-virus products detect the malicious Javascript as Trojan.JS.Downloader.GXW.
Similar attacks have been spammed out claiming that your credit card has temporarily been suspended.
Alternatively, you might have received emails posing as notifications that you have a parcel waiting for you at your local mail office.
In this final example, which also leads to the Locky ransomware, the malicious code sets the year to 2015. However, regardless of the year, the malware still executes. Bitdefender detects the Javascript file as Trojan.Js.Downloader.Na and the executable it downloads as Trojan.Ransom.Locky.BF.
In all cases, the criminals can (and frequently do) change the names and contact details used in the emails meaning that you cannot always rely on them looking the same.
The secret is to run a layered defence, combining up-to-date security software on your desktops and email gateways with regular backups and user awareness training to teach employees to be wary of dangerous filetypes and trusting unsolicited emails.
We know that criminals are making a vast amount of money out of online extortion – and ransomware is one of their favourite methods. When combined with spam and tricky social engineering disguises, it’s hard to imagine that it won’t continue to be a profitable source of income for cybercriminals for some time to come.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsYou might also like
Bookmarks



