Official British Army Twitter and YouTube accounts hijacked by NFT scammers

Hundreds of thousands of people who follow the official social media accounts of the British Army may have been surprised to see that it had been hijacked by hackers yesterday.
Although many might have imagined those responsible for the hack might have been a foreign state's cyberwarfare unit, the perpetrators appear to have been scammers exploiting interest in non-fungible tokens (NFTs).
The British Army's verified Twitter account was flooded with promotions related to giveaways and competitions related to NFTs, aimed at enticing its 362,000 followers to visit a scam minting website.
Unwary followers were told that they could win hyped-up NFT digital artworks of cartoon robots and robots in a raffle. At the same time the profile pictures and account details were changed to promote the NFT promotion.

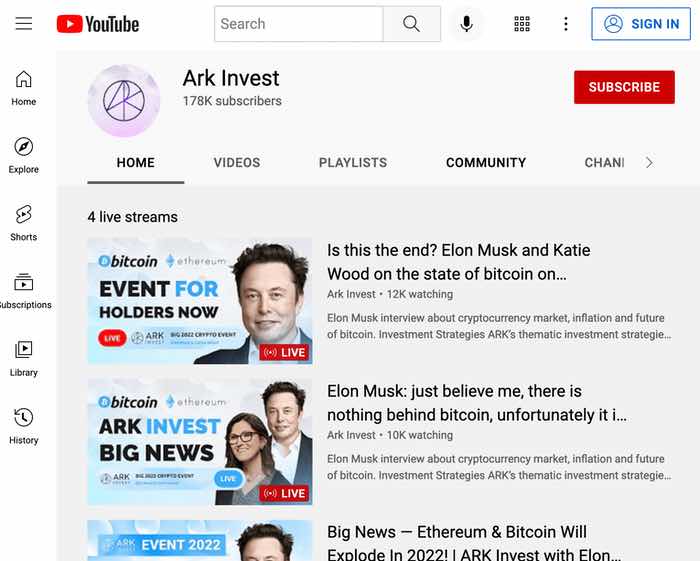
Meanwhile, the army's YouTube channel, with some 178,000 subscribers, was rebranded to resemble that of investment management firm ARK Invest, and published faked videos of Elon Musk promoting "double your money" cryptocurrency scams.
A spokesperson for the British Army confirmed on Twitter that they were back in control of their social media accounts, and that the security breach was being investigated:
"The breach of the Army’s Twitter and YouTube accounts that occurred earlier today has been resolved and an investigation is underway. The Army takes information security extremely seriously and until their investigation is complete it would be inappropriate to comment further."

Although an explanation for the social media security breach has not been shared publicly, likely possibilities include that someone in the British Army's social media team has been careless with their password and/or that multi-factor authentication was not in place to make it harder for unauthorised users to gain access.
In the past there have been many incidents of, say, Twitter accounts being hijacked by mischief-makers and scammers after passwords were either guessed or phished. In many cases, organisations and individuals have made the mistake of reusing passwords they use elsewhere on the internet, choosing weak or easy-to-guess passwords, or carelessly sharing them online.
It's also sadly still common for social media users to have not enabled two-factor authentication on their accounts, which can make it much more difficult for hackers to gain access even if they do manage to determine an account's password. Instructions for how to enable 2FA on Twitter and YouTube accounts are, one hopes, now being shared within the British Army to anyone who hasn't yet enabled these and similar security features.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsRight now Top posts
Fake Download of Mission: Impossible – The Final Reckoning Movie Deploys Lumma Stealer
May 23, 2025
Scammers Sell Access to Steam Accounts with All the Latest Games – It's a Trap!
May 16, 2025
How to Protect Your WhatsApp from Hackers and Scammers – 8 Key Settings and Best Practices
April 03, 2025
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks