FAN Courier SMS Scam Targets 1 Million Romanians in Massive WhatsApp Takeover Campaign

A new SMS phishing campaign in Romania is impersonating FAN Courier, one of the largest courier and express delivery companies, to trick users into entering their WhatsApp verification codes on fake websites.
Once the victim enters the code, attackers take over their WhatsApp account and then send urgent money requests to their contacts. The scam relies on social engineering rather than installing malware.
Key takeaways
- A new phishing campaign in Romania impersonates Fan Courier through SMS messages.
- The malicious link leads to a fake website designed to steal WhatsApp verification codes.
- Attackers hijack victims’ WhatsApp accounts and request money from their contacts.
- Over a million people have received malicious SMS messages.
- No online service will ever require your WhatsApp login code.
What is the Fan Courier SMS scam?
Cybercriminals have launched a phishing campaign targeting Romanian users by impersonating Fan Courier. Victims receive SMS messages claiming that a parcel is linked to their phone number and that they must choose a locker for pickup, or some variation on the same theme.
The message appears to be routine, mimicking legitimate SMS messages people might receive. The attack uses neutral language and references package delivery, which many people interact with. The page appears to be related to FAN Courier but redirects to a malicious domain controlled by attackers. The immediate objective is WhatsApp account takeover.
Who is targeted by this campaign?
The campaign targets Romanian users indiscriminately. Over a million people have received these messages, according to our insights.
Attackers send bulk SMS messages to thousands of phone numbers simultaneously. Anyone expecting a delivery, using locker services, and relying on WhatsApp as a primary communication app can become a victim.
The campaign follows a precise social engineering sequence. First, the victim receives an SMS about a supposed parcel. Some people may actually be waiting for an official message.
The link directs them to a fake website that looks like a delivery confirmation page.
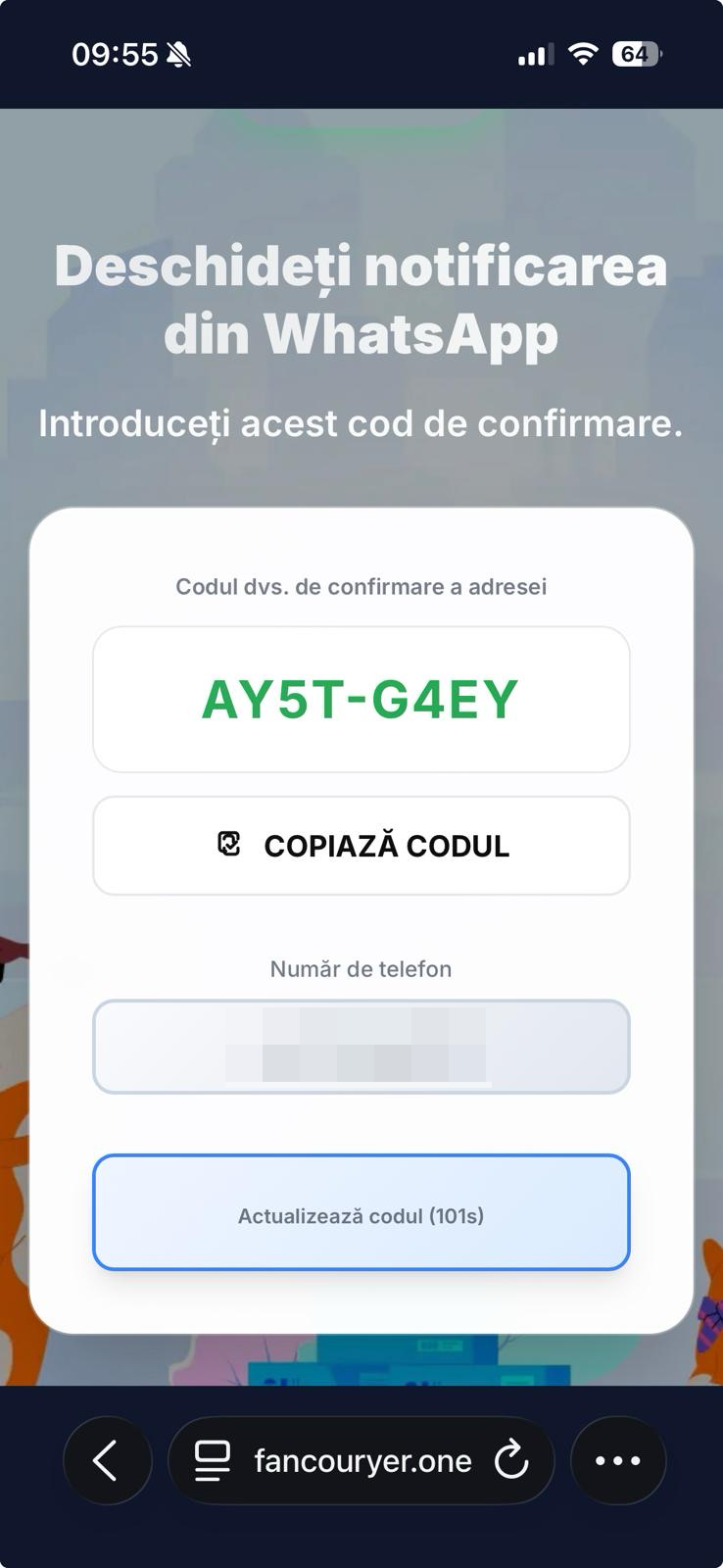
Second, attackers simultaneously initiate a WhatsApp registration attempt using the victim’s phone number. WhatsApp then sends a real verification code to the victim’s device.
The phishing page instructs the victim to enter that code under the pretext of confirming delivery details. When the victim enters the code, the attackers complete the login process on their own device.
At that moment, the attackers have control of the WhatsApp account. There is no malware on the phone, and the victim unknowingly authorizes the takeover.
What happens after attackers hijack the account?
Once attackers gain access to the account, they move quickly. They use the contact list to send urgent financial requests. Messages often mention temporary emergencies and promise repayment the next day.
Because the requests come from a trusted contact, recipients are more likely to comply without verifying the situation. This second phase generates the financial gain and is the actual goal of the attack.
How can you recognize the fake courier messages?
- Suspicious domains that do not match the official Fan Courier website
- Unusual domain extensions
- Messages sent from random mobile numbers
- Requests to enter a WhatsApp confirmation code
- Requests for money, with the promise of returning them the same day
Legitimate courier services will never ask for WhatsApp login credentials or verification codes. If a website requests your WhatsApp code, it's an account takeover attempt.
How can you protect yourself?
Follow these defensive steps:
- Do not click courier links received via unexpected SMS messages.
- Type the official courier website manually into your browser.
- Never enter WhatsApp verification codes outside the WhatsApp app.
- Enable WhatsApp two-step verification (Settings → Account → Two-step verification).
- Verify urgent money requests with a direct phone call.
- Use Bitdefender security solutions to prevent interaction with these domains and block incoming calls from fraudulent numbers.
What should you do if your WhatsApp account was compromised?
Re-register your phone number in WhatsApp to attempt account recovery or reinstall the application. Notify your contacts through alternative communication channels. Inform them to ignore any financial requests.
If attackers set a two-step verification PIN before you regain access, recovery may require waiting for WhatsApp’s security reset process.
Frequently Asked Questions
Is Fan Courier involved in this scam?
No. Attackers impersonate the brand. The company itself is a victim of brand abuse.
Can attackers read my WhatsApp messages?
If they fully hijack your account, they can access ongoing conversations and impersonate you.
Is this malware?
No. This attack relies on social engineering and credential theft, not malicious software installation.
Can two-step verification stop this?
Yes. It adds an additional PIN requirement, preventing attackers from completing the registration process.
Final Security Reminder
- If a delivery SMS feels unexpected, pause.
- If a website asks for your WhatsApp confirmation code, stop immediately.
- If a friend asks for urgent money, verify the request by phone.A few seconds of caution can prevent account hijacking and financial loss.
tags
Author
Silviu is a seasoned writer who followed the technology world for almost two decades, covering topics ranging from software to hardware and everything in between.
View all postsYou might also like
Bookmarks


