Why EV charging networks need zero trust

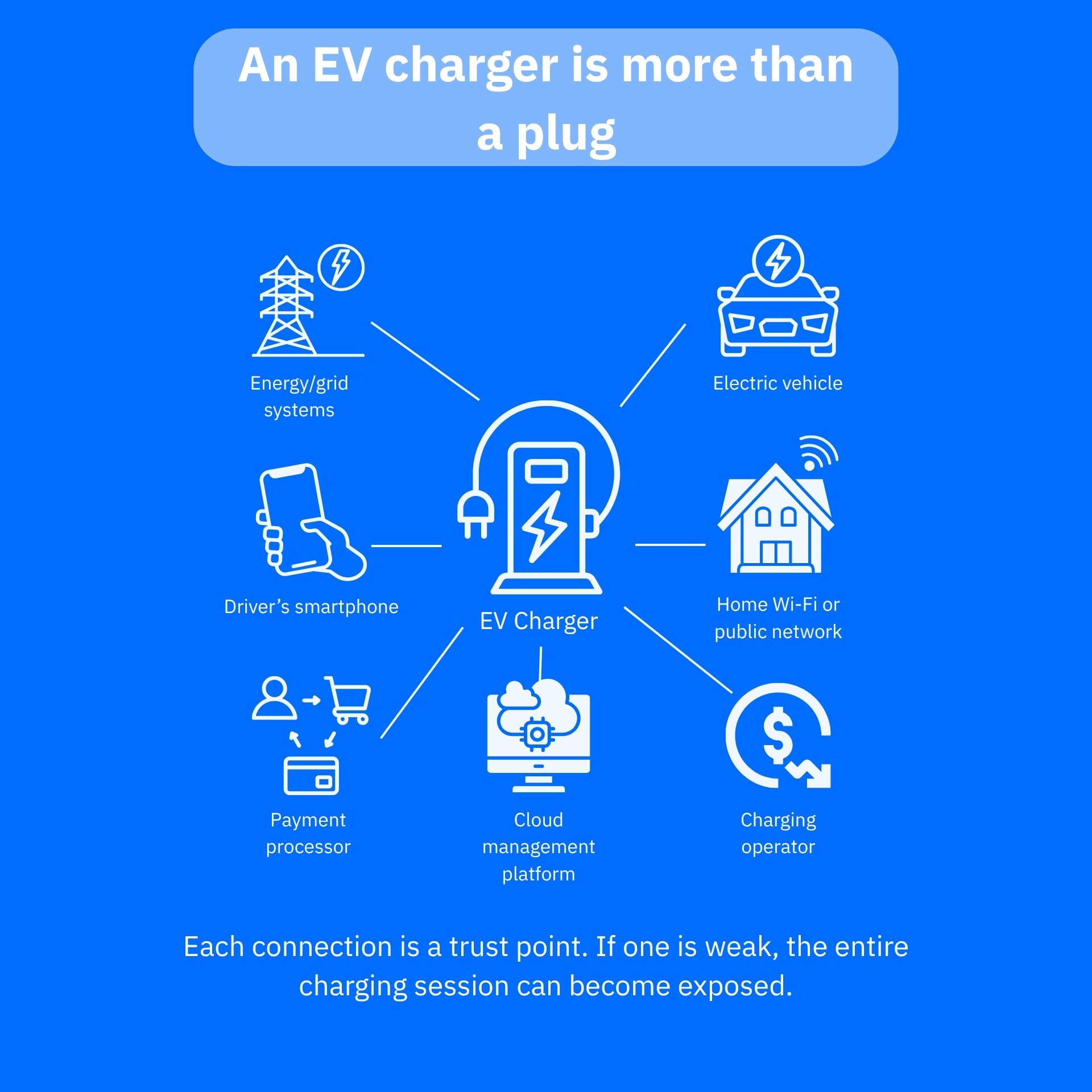
EV chargers may look like simple power outlets, but they are quickly becoming part of a much larger connected ecosystem, along with many other IoT devices. A public or home EV charger can involve mobile apps, payment cards, user accounts, cloud dashboards, location data, firmware updates, Wi-Fi, Bluetooth, RFID cards and links to the electric grid.
That makes EV charging networks less like parking-lot hardware and more like IoT infrastructure that must verify every device, user and request before trusting it.
Key takeaways
- EV charging networks are connected IoT systems, not just electrical equipment, exposing them to account abuse, app flaws, payment fraud, firmware tampering and remote disruption
- Zero trust security helps EV charging operators reduce risk by continuously verifying users, chargers, apps, APIs and backend systems instead of assuming anything “inside” the network is safe
- For consumers, zero trust is important because EV chargers can touch personal data, payment details, location patterns and home Wi-Fi networks
- Home EV owners should secure their routers, isolate smart devices where possible, use strong authentication and consider router-level protection such as NETGEAR Armor for connected home environments
EV chargers expand the IoT attack surface
Electric vehicle charging is no longer a simple exchange of electricity. A typical charging session may involve a driver’s phone, a charging app, a user account, a payment processor, a charging station, an operator’s cloud platform—and sometimes the vehicle itself. The US Department of Energy has warned that the EV charging infrastructure introduces cybersecurity considerations across vehicles, charging equipment, networks and the very grid they’re bound to.
That connectivity lets drivers find chargers, check availability, pay digitally and monitor charging sessions. However, it also creates more vulnerable points, including weak passwords, insecure APIs, outdated charger firmware or compromised companion apps. These weaknesses increase the attack surface and can expose drivers to privacy risks, payment abuse or failed charging stations.
What ‘zero trust’ means for EV charging
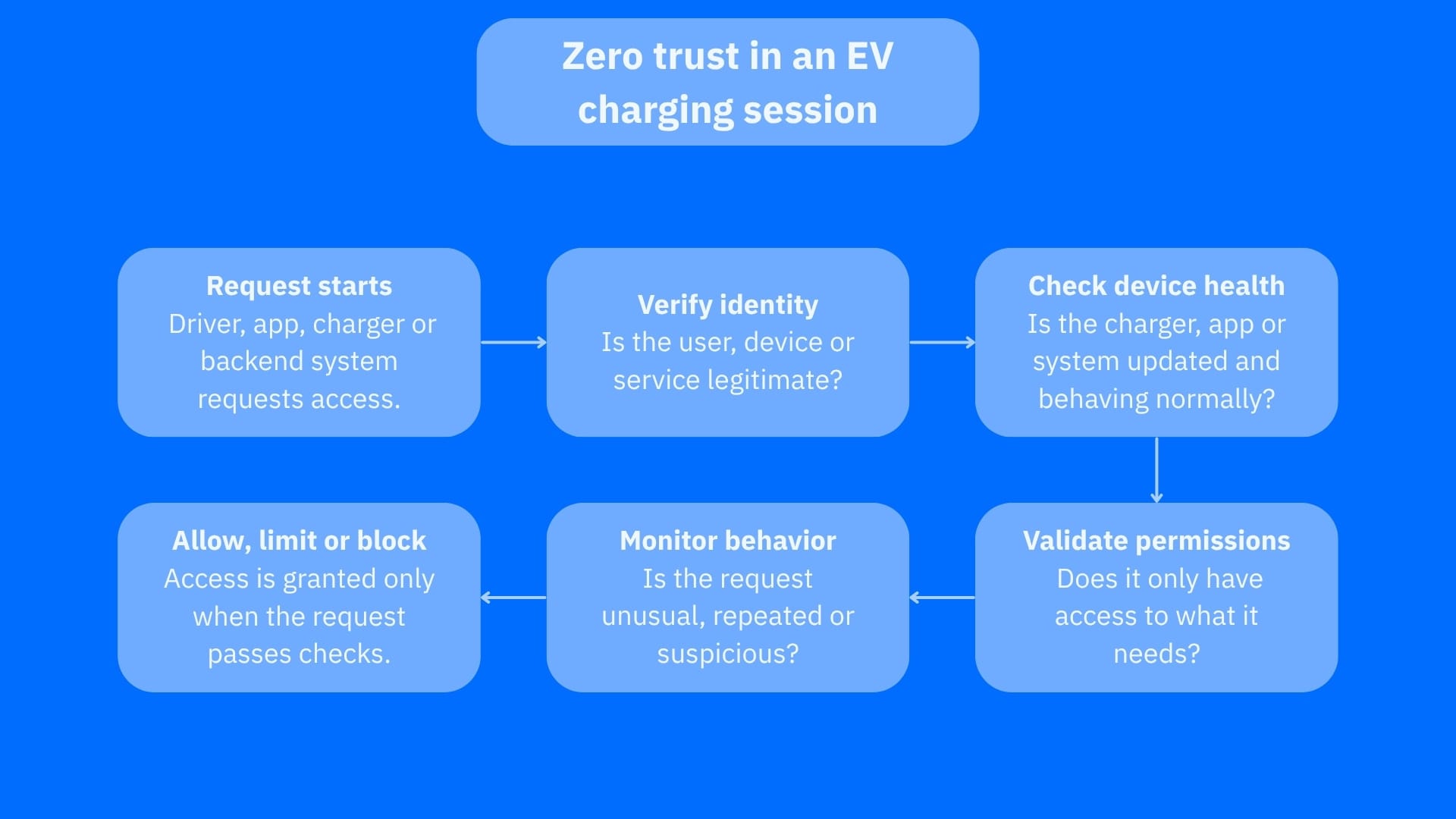
Zero trust is a cybersecurity model built around the idea that no device, user, app or network connection should be automatically trusted.
In an EV charging network, that means the system should continuously ask:
- Is this charger really the charger it claims to be?
- Is this driver account legitimate?
- Is this app request normal, or is it suspicious?
- Should this backend system have access to payment, location or charging data?
- Has this device been updated and configured securely?
Instead of assuming that a charger, app or operator dashboard is safe because it belongs to the network, zero trust require constant, repeated verification at each step.
Why EV charging networks are attractive targets
EV charging networks sit at the intersection of consumer technology, transportation and critical infrastructure. They handle data that threat actors can monetize, and they control physical equipment people rely on to move.
Attackers may be interested in:
- Driver accounts and stored payment methods
- Charging history and location patterns
- Charger availability and uptime
- Backend management portals
- APIs connecting mobile apps, chargers and operators
- Links between charging infrastructure and energy systems
EV charging could open new cybersecurity risk pathways for energy and transportation infrastructure, especially because the ecosystem involves many users, vendors, software platforms and operators.
This doesn’t mean EV drivers should panic. Instead, charging networks need security models designed for connected infrastructure, not outdated assumptions that connected devices will always behave properly.
How zero trust reduces EV charging risks
A zero-trust approach can strengthen the resilience of EV charging networks by limiting what any single compromised account, app or device can do.
For example, a charging operator can use strong identity controls so that employees, technicians and automated systems can only access what they need. Chargers can be authenticated before communicating with backend platforms. APIs can be monitored for abnormal behavior. Payment systems can be separated from charger management systems, and firmware updates can be signed and verified before installation.
For consumers, these changes are less obvious, but their benefits are crucial. A well-designed zero-trust charging network is less likely to let one weak point become a system-wide problem. If one charger is compromised, segmentation and least-privilege access can help prevent the issue from propagating across the network.
Home EV chargers need attention as well
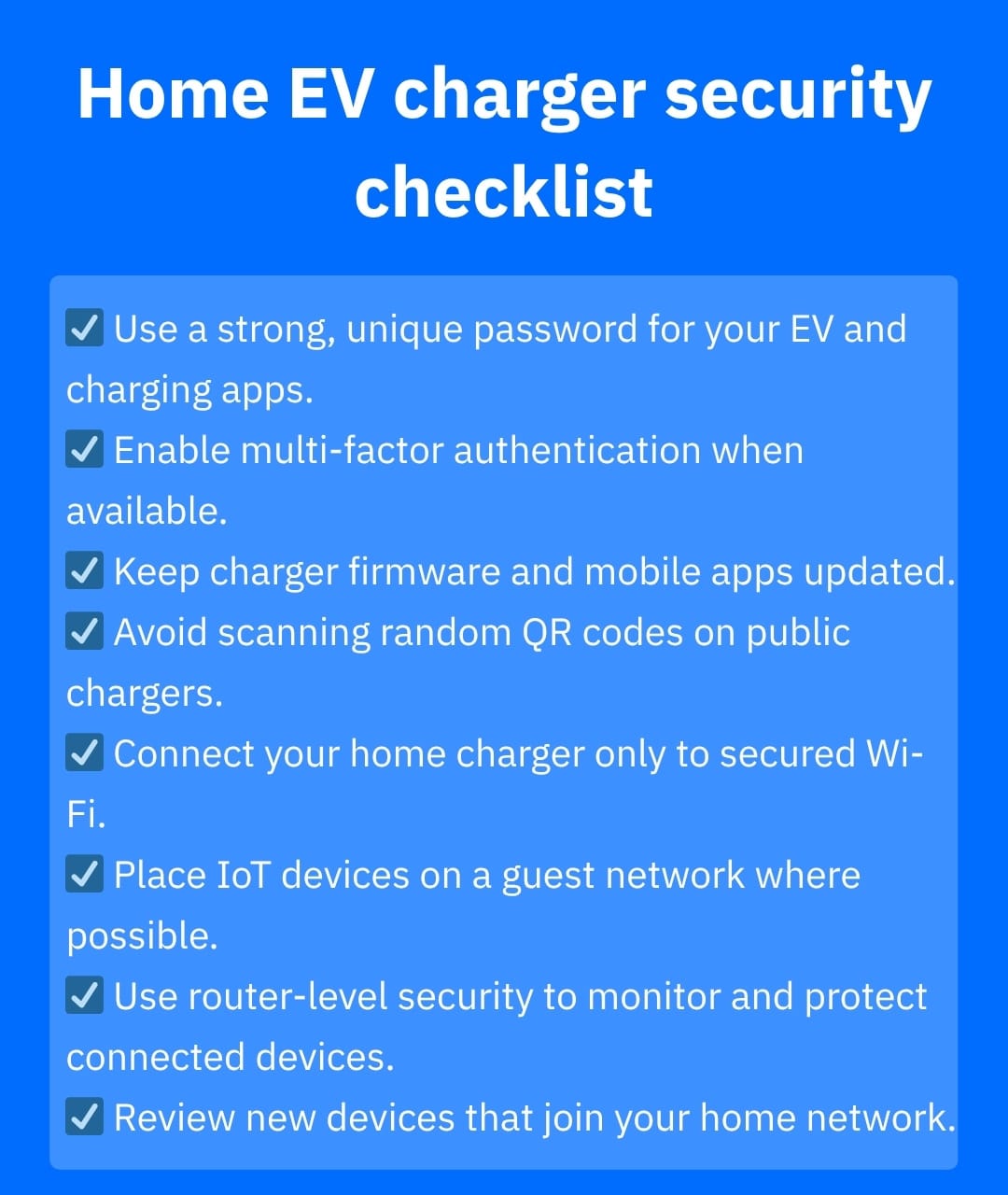
Public networks are not the only concern. Home EV chargers are often connected to Wi-Fi, controlled through apps and installed alongside other smart home devices. If your home network is poorly secured, your charger becomes one more connected device that depends on your router, password, update habits and overall cybersecurity hygiene.
In this scenario, consumer security tools can help. NETGEAR Armor, powered by Bitdefender, protects connected devices at the router level, including IoT devices that traditional endpoint security may not cover. It helps shield smart home devices before attacks can reach them and alert users when new devices join the network.
Although it does not replace secure charger design or responsible charging-network operation, router-level protection can support the same basic zero trust mindset of knowing what is on your network, blocking what does not belong and reducing blind trust.
What EV owners can do now
Although you may not be able to rebuild public charging infrastructure, you can reduce personal risk by:
- Using strong unique passwords for EV and charging apps (use password managers like Bitdefender SecurePass to avoid password fatigue)
- Enabling multi-factor authentication (MFA) when available
- Keeping your charger app and home charger firmware updated
- Avoiding scanning random QR codes placed on public chargers (threat actors can use fake stickers to redirect drivers to phishing pages)
- Connecting the charger only to a secure Wi-Fi network when charging at home
- Segmenting your home network or place IoT devices on a guest network
- Treating EV charging accounts like financial accounts, as they may include billing details, travel habits and access to a device you depend on
Conclusion
EV charging networks need zero trust because they are no longer isolated pieces of electrical equipment. They are connected IoT systems that handle identity, payments, location data, software updates and operational commands. As EV adoption grows, the security model must evolve with it.
For charging operators, zero trust means verifying every device, user and request before granting access. For consumers, it means understanding that EV chargers are part of a broader smart home and connected mobility ecosystem. The safer path is not to avoid EV technology altogether, but to stop assuming that every charger, app and connected deserves automatic trust.
Frequently asked questions (FAQ)
What are the disadvantages of zero trust architecture?
Zero trust can be complex to implement. It may require stronger identity management, device monitoring, network segmentation, better logging and ongoing policy tuning. If deployed poorly, it can also frustrate users with too many authentication prompts or block legitimate activity. The goal is not to make access difficult, but to make trust conditional, limited and continuously verified.
What are the 5 pillars of zero trust model?
CISA’s Zero Trust Maturity Model uses five pillars:
- Identity
- Devices
- Networks
- Applications and Workloads
- Data
It also includes cross-cutting capabilities such as visibility and analytics, automation and orchestration and governance.
Is zero trust outdated?
No. Zero trust is not outdated, but it’s often misunderstood or poorly implemented. The model remains relevant because modern networks include cloud apps, remote access, IoT devices, mobile apps and connected infrastructure such as EV chargers.
tags
Author
Vlad's love for technology and writing created rich soil for his interest in cybersecurity to sprout into a full-on passion. Before becoming a Security Analyst, he covered tech and security topics.
View all postsYou might also like
Bookmarks


