Hackers Grab Yahoo Credentials through Mail Activity Reports Campaign
Yahoo users are being targeted by a new phishing campaign that helps hackers grab their credentials and hijack accounts. Bitdefender was already blocking the malicious URLs spreading in inboxes worldwide.
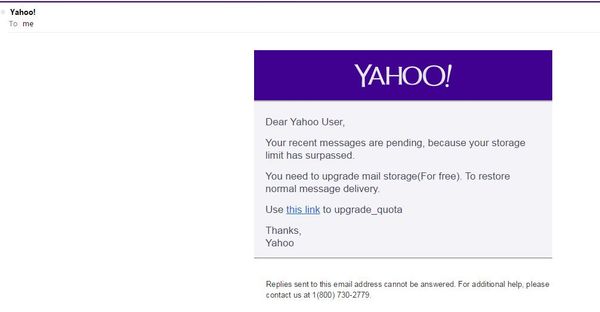
The phishing campaign starts with messages that bypass the e-mail provider’s antispam filters, reaching the Inbox folder. The e-mails pose as “mail activity reports” and copy Yahoo’s email format to look legitimate.


“Dear Yahoo User, your recent messages are pending, because your storage limit has surpassed,” phishing messages read. “You need to upgrade mail storage (For free). To restore normal message delivery. Use this link to upgrade_quota.”
The malicious URLs quickly redirect to a copycat sign-in page, tricking unwary users into giving their usernames and passwords. Though phishing has been around for many years, it remains a persistent e-threat. The latest available data show 2013 was another record year in the number of phishing attacks launched globally, inflicting record losses of over $5.9 billion, according to EMC.
With little cost for cyber-crooks and a high degree of efficiency in reaching new victims, phishing will continue to hit the global economy in coming years, Bitdefender warns. The Online Threats Lab revealed that PayPal, eBay, Yahoo, Facebook and LinkedIn are among the most abused brands when it comes to launching phishing attacks.
All product and company names mentioned herein are for identification purposes only and are the property of, and may be trademarks of, their respective owners.
tags
Author
Bianca Stanescu, the fiercest warrior princess in the Bitdefender news palace, is a down-to-earth journalist, who's always on to a cybertrendy story.
View all postsRight now Top posts
Fake Download of Mission: Impossible – The Final Reckoning Movie Deploys Lumma Stealer
May 23, 2025
Scammers Sell Access to Steam Accounts with All the Latest Games – It's a Trap!
May 16, 2025
How to Protect Your WhatsApp from Hackers and Scammers – 8 Key Settings and Best Practices
April 03, 2025
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








