Securing your home wallbox against PLC exploits

As home EV chargers get smarter, they also inherit new attack surfaces. Understanding how power line communication works and where it can go wrong can help homeowners make better security decisions before convenience turns into security incidents.
Key takeaways
- Home wallboxes are smart connected devices, which means they can inherit cyber risks alongside charging functionality.
- PLC exploits target the communication layer between an EV and the charger, not just the home Wi-Fi network around it.
- Consumers can reduce risk by updating charger firmware, securing companion apps and accounts, and isolating the charger on a separate IoT network.
- NETGEAR Armor can help protect a smart home environment by monitoring connected devices and blocking network-side threats.
Why you should secure your home wallbox
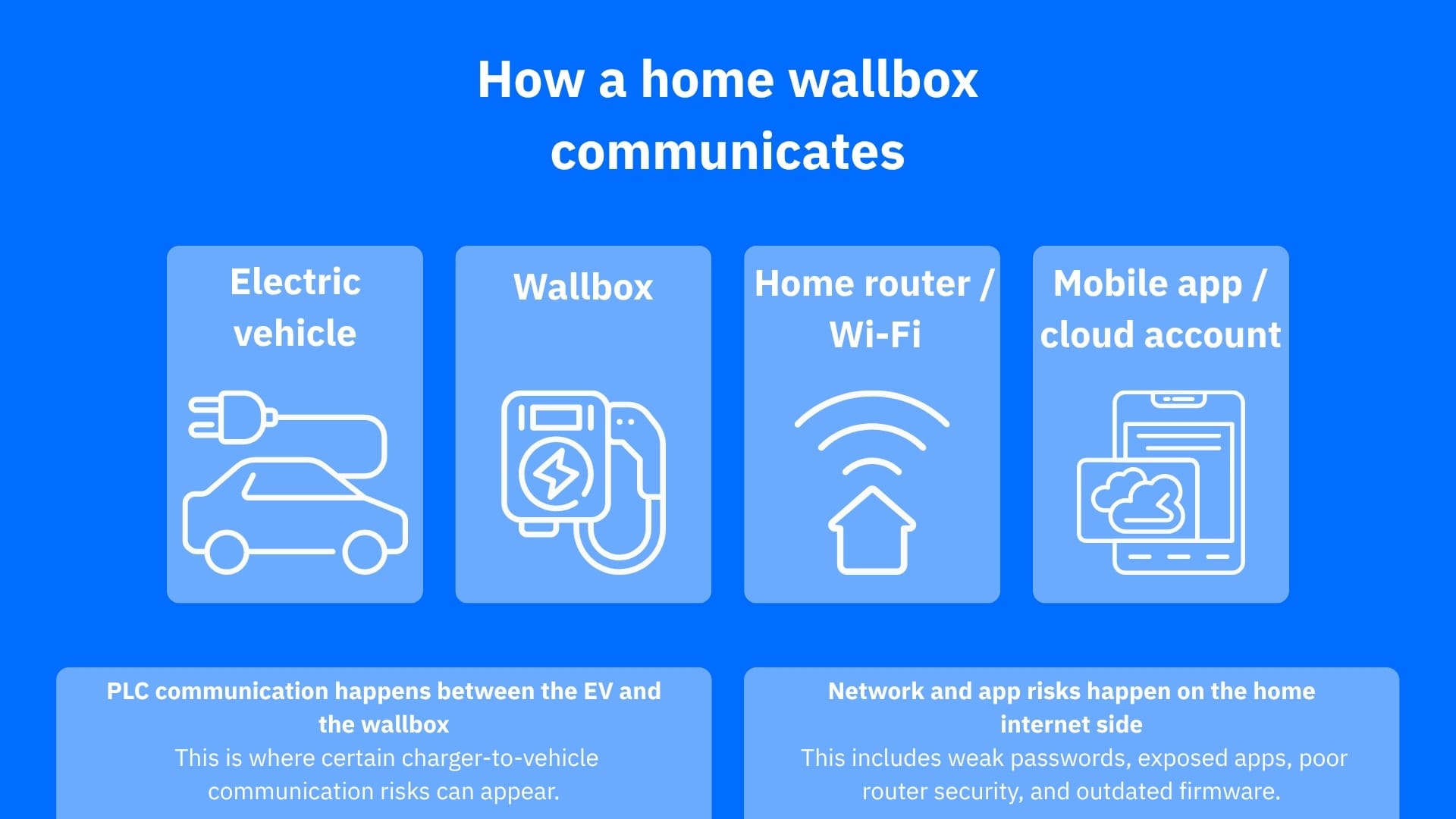
For many homeowners, a wallbox feels like a simple appliance you can just mount, connect, charge the car with, and move on. But modern EV charging extends beyond mere electricity, as many chargers now combine cloud connectivity, firmware updates, mobile companion apps, remote management and, in some cases, even standardized communication between the vehicle and charger over power line communication (PLC).
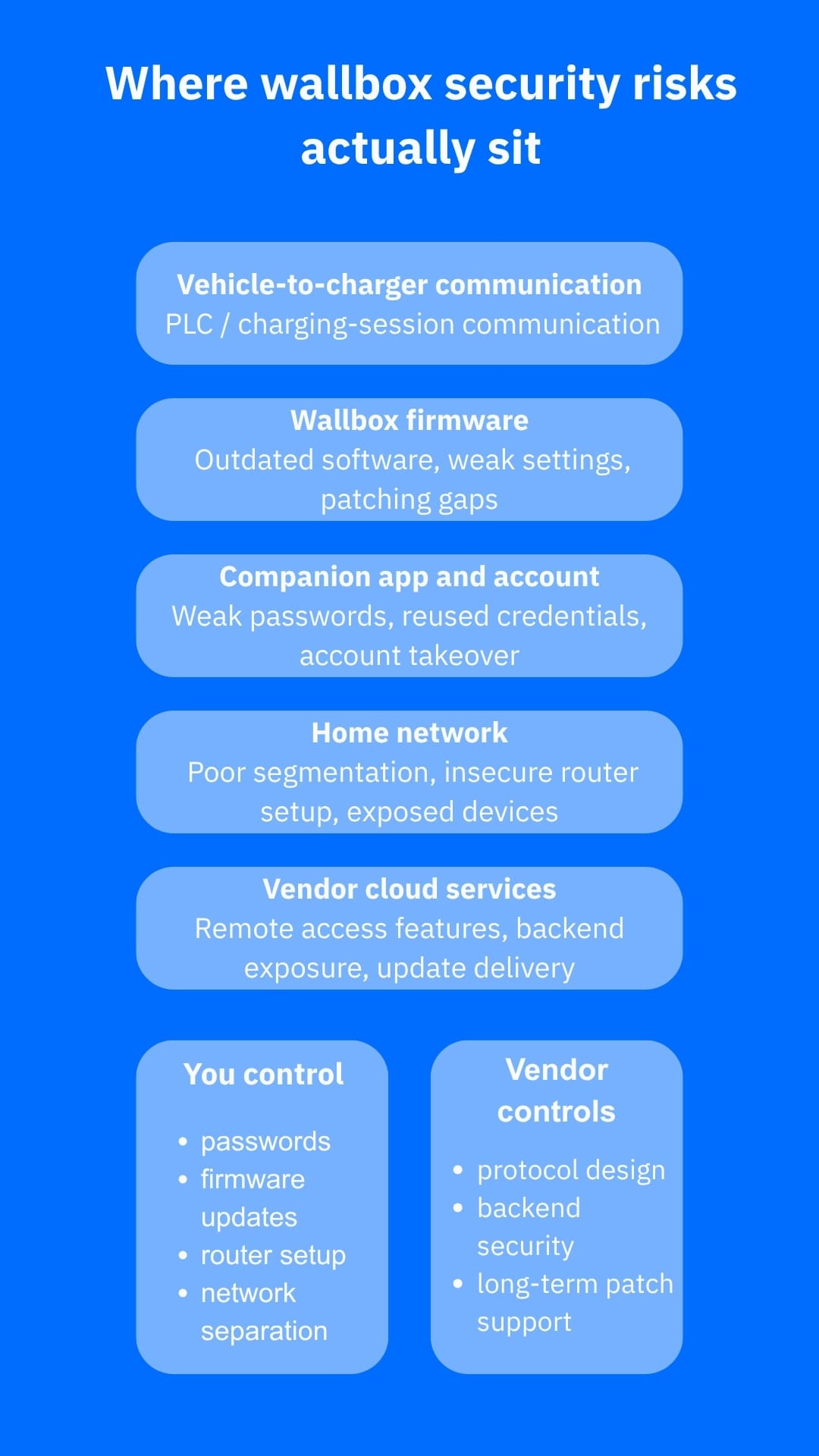
Although the added intelligence brings much more convenience, it also expands the attack surface. Standards used in EV charging, especially ISO 15118, rely on HomePlug Green PHY to carry data between the vehicle and charging equipment over the charging connection itself. As researchers have pointed out, several weaknesses affect EV charging communications, including eavesdropping and man-in-the-middle (MiTM) attacks, under certain conditions.
While this doesn’t mean every home charger can be hacked from the street, it does mean homeowners should stop seeing their wallboxes as mere “power devices.” In reality, these devices are better categorized as IoT endpoints with physical charging roles.
What PLC exploits mean for homeowners
In plain language, PLC in EV charging allows the car and charger to negotiate charging parameters and, in some cases, support advanced features such as Plug and Charge. The issue is that researchers have found design and implementation flaws around this communication process.
A notable CISA advisory from late 2025 warned that manipulating the SLAC (Signal Level Attenuation Characterization) pairing process in ISO 15118-2 could facilitate an MiTM attack, potentially even wirelessly at close range via electromagnetic induction. This vulnerability is tracked as CVE-2025-12357 and is marked as medium on the severity scale.
Earlier academic work also showed that CCS charging communications could be observed wirelessly because of physical-layer leakage, and later measurement research found many deployed chargers still lacked TLS or relied on very old HomePlug modem firmware. That combination of weak protocol protection and stale embedded software is exactly the sort of mix attackers look for.
For consumers, the realistic risks revolve more around privacy than cinematic sabotage and include session manipulation, billing abuse in advanced charging environments, unreliable charger behavior and even compromised chargers becoming a weak point in the home network. Even when the PLC link itself is vendor-dependent and not entirely under your control, its surrounding ecosystem definitely is. Routers, charger apps, account security, firmware hygiene and network design all contribute to your setup’s exposure.
How to harden a home wallbox without overcomplicating it
Keep everything up to date
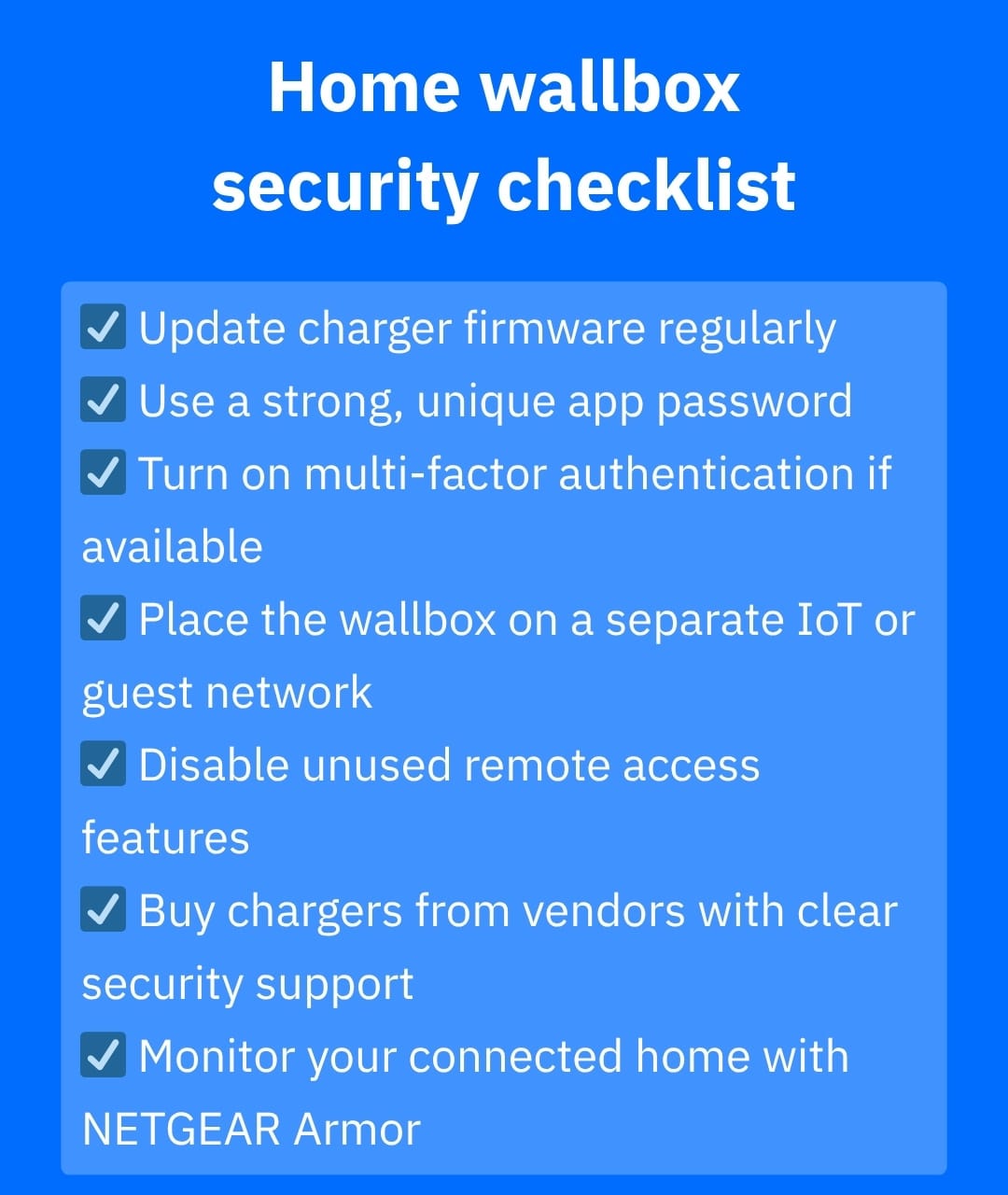
The first step might seem boring but it’s essential: keep the charger updated. This is not an option, much more so in a device category that already has a record of published vulnerabilities and vendor-issued fixes.
CISA advisories involving residential or wall-mounted chargers have repeatedly pointed users toward firmware updates and secure configuration changes. If your charger gets updates through an app or cloud portal, make sure it remains enrolled and reachable for legitimate updates.
Lockdown accounts
The second step is to secure the account attached to the charger. If your wallbox has an app, installer account, cloud dashboard or homeowner portal, make sure you use a strong, unique password and enable multi-factor authentication (MFA) if supported.
Many smart device compromises begin with weak credentials, reused passwords or exposed management features rather than exotic protocol attacks.
Isolate the charger
The third step is to treat the charger like more than just a power port. Your wallbox should receive the same treatment as any other smart home device. Isolate it on the same network as your other IoT devices if possible. Putting EV chargers, cameras, smart TVs and similar endpoints on a separate IoT or guest network reduces the blast radius if one of them is compromised.
Minimizing network exposure and isolating connected devices behind firewalls, rather than leaving them broadly accessible, is crucial for your IoT home security.
Use dedicated software
Specialized software like NETGEAR Armor is designed to add router-level protection for connected home devices, helping block malicious sites, detect vulnerable devices and monitor threats across the network.
For an IoT-heavy household that includes a smart wallbox, that extra layer can help contain the network-side risks around the charger ecosystem, even though it does not directly “fix” the PLC protocol between the vehicle and the charger.
Be mindful
Last but not least, you should be selective when buying or configuring a charger. Favor vendors with a visible patch history, clear update instructions and ongoing security support.
A smart charger with remote features is only as trustworthy as the vendor maintaining it. If the product documentation is vague about updates, account controls or network behavior, treat it as a red flag.
Conclusion
Home wallboxes are becoming part of the broader IoT household, and PLC-related research shows that EV charging security is no longer a niche concern. Homeowners do not need to master ISO 15118 or HomePlug Green PHY to be prepared. They just need to think like smart-device owners and patch quickly, reduce exposure, secure accounts, segment the network and add router-level protection that can spot trouble early.
The safest mindset is that while your charger may live in the garage, its risk profile still belongs to your home network. In a connected home full of smart endpoints, protecting that network with a tool like NETGEAR Armor can help turn one vulnerable edge device into a much smaller problem.
Frequently asked questions (FAQ)
What are the cyberattacks on EV charging stations?
Cyberattacks on EV charging stations can include unauthorized access, firmware tempering, app or account compromise, denial-of-service (DoS) attempts and attacks on charger-to-vehicle communication. In some cases, attackers may try to disrupt charging stations, steal data or exploit the charger as a weak point inside a connected home or broader network.
What does a wallbox do?
A wallbox is a dedicated EV charging unit installed at home or on a private property to charge an electric vehicle more safely and efficiently than a standard outlet. It manages power delivery, can shorten charging times and often includes smart features such as scheduling, remote control and energy monitoring.
What is a PLC exploit?
A PLC exploit is an attack that targets power line communication, the technology used to transmit data over the charging connection between an EV and a charger in certain charging standards. In practice, this means an attacker tries to interfere with, observe or manipulate the communication that helps coordinate the charging session.
tags
Author
Vlad's love for technology and writing created rich soil for his interest in cybersecurity to sprout into a full-on passion. Before becoming a Security Analyst, he covered tech and security topics.
View all postsYou might also like
Bookmarks


