Data minimization strategies for twin-heavy industries

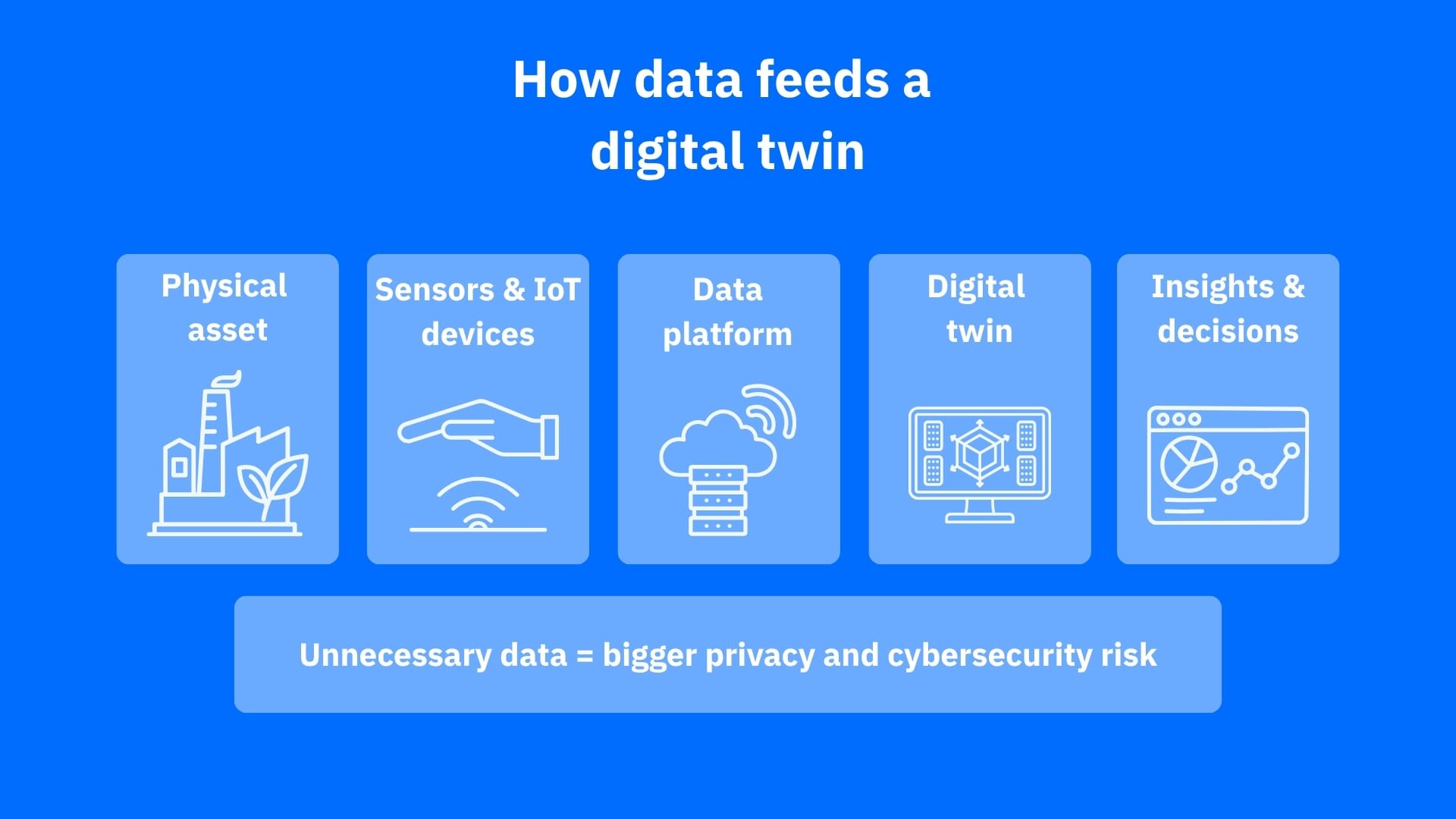
Digital twins are becoming the invisible control panels behind factories, utilities, smart buildings, logistics, devices and other connected industries. By mirroring real-world systems with data from sensors, devices and software, they can improve efficiency, predict failures and support faster decisions.
But when these virtual models collect more information than they need, they can also expose sensitive patterns and operational details, and create privacy risks that attackers are eager to exploit.
Key takeaways
- Digital twins rely on constant data flows from sensors, connected devices and software platforms, which can increase privacy and cybersecurity risks
- Data minimization helps reduce exposure by collecting only the information needed for a specific purpose
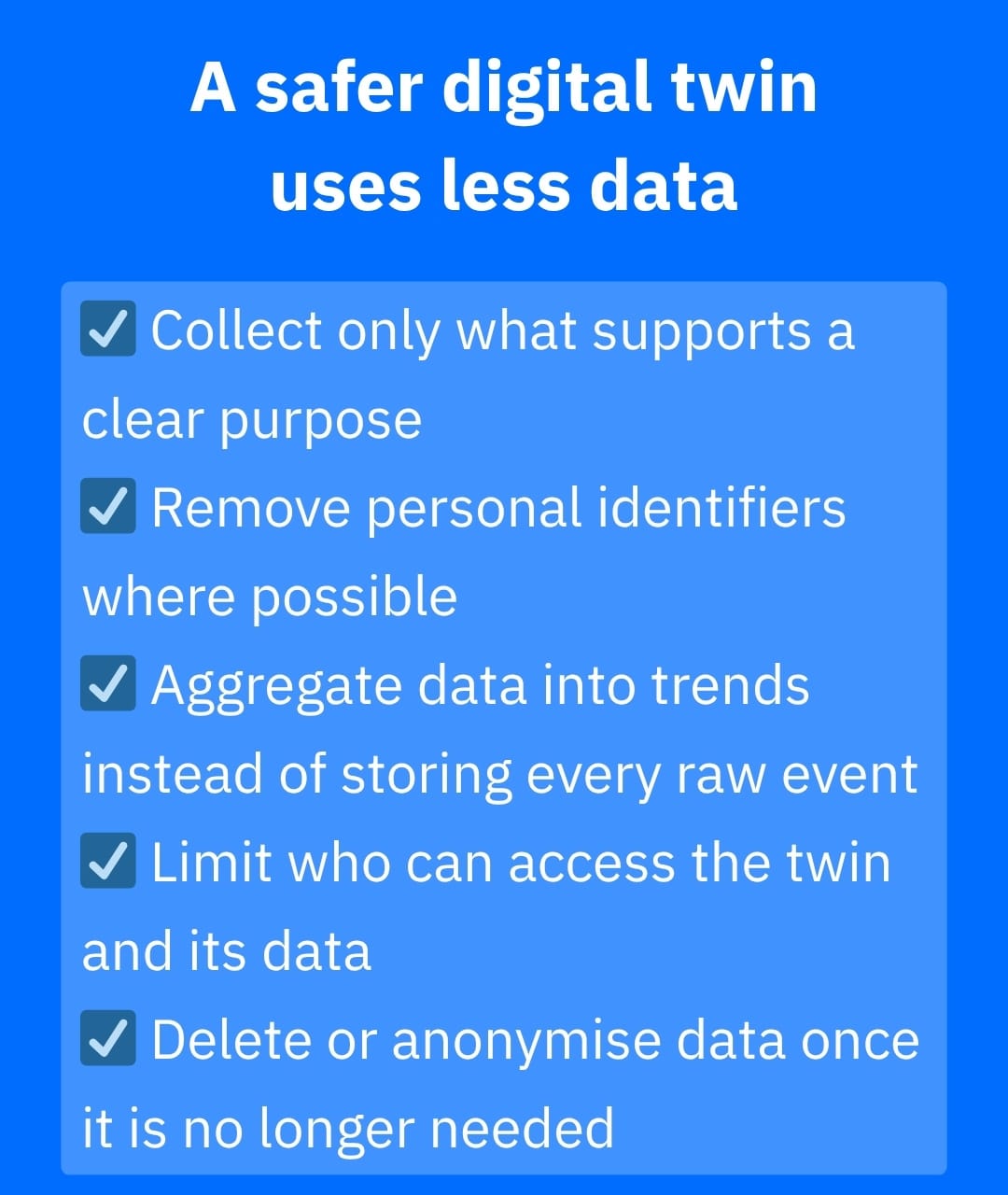
- Aggregation, anonymization, access controls and clear retention rules can make digital twins safer without reducing usefulness
- For home consumers, fewer unnecessary data flows and better IoT monitoring can reduce smart-device risk
Digital twins slowly morph into the backbone of modern life. Factories can use twins to simulate production lines, hospitals to model patient flows or equipment performance, utility companies to monitor energy grids, and smart cities to map traffic, air quality and infrastructure. Simply put, a digital twin is a virtual version of a real object, system or process, updated with data from sensors, software and connected devices.
That sounds useful, and it is. However, “twin-heavy” industries also create a serious cybersecurity and privacy problem: the more a digital twin knows, the more valuable it becomes to attackers. A digital twin may reveal production schedules, building layouts, energy patterns, device behavior, maintenance windows or sensitive user activity. By limiting the collection, processing and storing of data to what’s truly necessary, data minimization can solve some of these issues.
Why digital twins collect so much data
Digital twins work best when they are fed accurate, timely information. In industrial IoT (IIoT) environments, that can include sensor readings, location data, equipment logs, user access records, video feeds, maintenance data and environmental conditions.
The risk is that companies often collect first and ask questions later. That creates “data exhaust”: information that may not improve the twin but still increases exposure. If attackers compromise a twin, they may understand how a system behaves well enough to disrupt it.
Digital twins introduce operational risks because they connect modelling, monitoring and decision-making into one environment. As ISC2 points out, these systems may use real-time data, machine learning and reasoning to support decisions, which makes their accuracy and security especially important.
Limit data to only what’s truly needed
The first rule of data minimization is simple: refrain from collecting data just because the technology allows it. A smart building twin may need occupancy trends to optimize heating and cooling. It probably does not need personally identifiable movement patterns tied to individuals. A manufacturing twin may need vibration data from a machine and may not need full employee activity logs to predict maintenance needs.
Before collecting data, twin-heavy industries should ask the following questions:
- What decision will this data support?
- Can the same result be achieved with less detailed data?
- Does the twin need real-time data or would periodic updates work?
- How long does the data remain useful?
- Who genuinely needs access to collected data?
According to privacy-by-design principles, embedding data protection safeguards into products, services and processes from the start would be far more effective. Until that becomes a reality, however, end-users and companies need to adjust their data collection largely on their own.
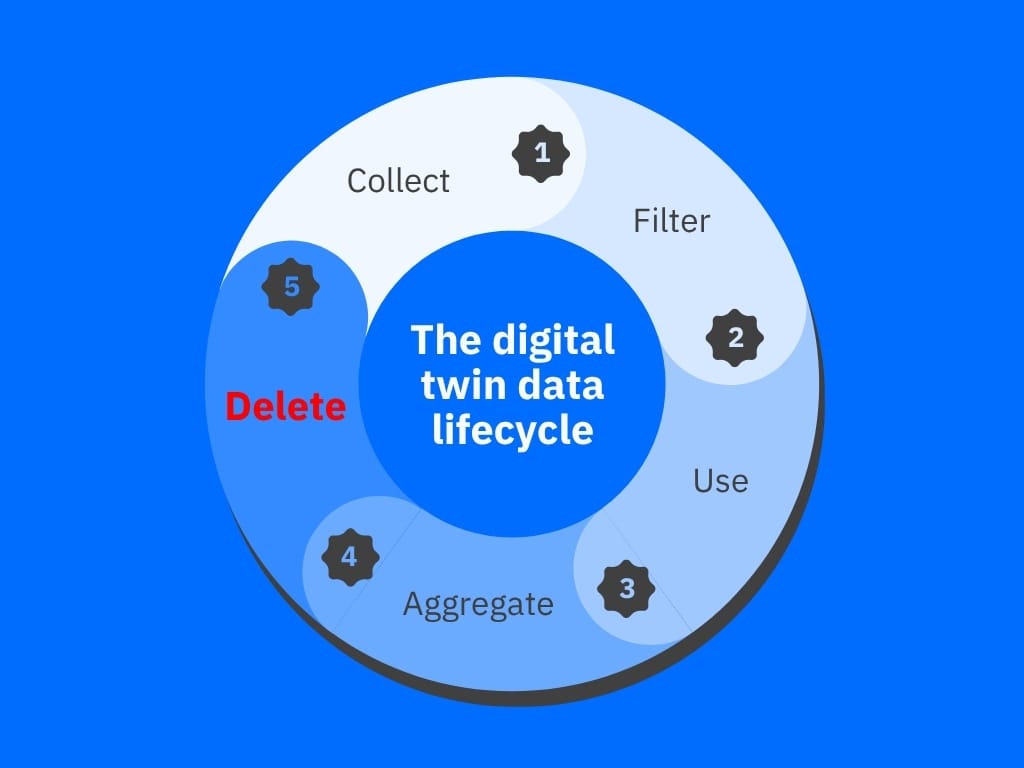
Use aggregation and anonymization
Not every digital twin needs raw, device-level or user-level data. In many cases, aggregated data is safer and just as useful.
For instance, a logistics company may need to know that average warehouse temperature exceeded a safe threshold and may not need every individual sensor reading stored indefinitely. Good minimization strategies include:
- Aggregating readings into trends or ranges
- Removing identifiers before data reaches the twin
- Masking sensitive fields such as names, exact locations or account IDs
- Using synthetic or simulated data for testing
- Separating operational data from personal data
The goal is to give the twin enough information to function without turning it into a surveillance vault or weakening its effectiveness.
Limit data retention
Data has a shelf life. For instance, vibration readings collected months ago may help long-term reliability analysis, but door-access events from the same period may no longer be needed. The longer data sits in storage, the more attractive it becomes to attackers.
Twin-heavy industries should define retention rules by data type. Safety logs, compliance records, anonymized performance trends and raw personal data should not follow the same timeline. Raw data should often be deleted or transformed into less sensitive summaries once it has served its purpose.
Restrict access to the twin and its data streams
A digital twin can become a high-value map of a business or infrastructure environment. Access should be based on role, need and context, as engineers, vendors, executives and support teams do not all need the same visibility.
Strong controls should include multi-factor authentication (MFA), least privilege access, logging, regular access reviews and segmentation between the twin, production systems and general corporate networks.
The same principle applies to consumers and smart-home enthusiasts. Your router, smart cameras, thermostat, speakers and appliances may not form an industrial digital twin, but they still paint a behavioral picture of your household. In this scenario, a consumer security layer such as NETGEAR Armor can come in handy by helping you monitor connected devices, detect suspicious activity and block network-side threats across the home environment. While it may not secure an industrial digital twin, it can help reduce exposure in smaller IoT ecosystems that people actually live with.
Conclusion
The future of digital twins should not be “collect everything forever.” It should be smarter modelling with cleaner, leaner data. Data minimization makes digital twins safer because it reduces what attackers can steal, manipulate or infer. It also improves governance by forcing organizations to understand why each data stream exists.
A useful digital twin does not need to know everything. It just needs to know enough: the right things for the right purpose and for the shortest reasonable time.
Frequently asked questions (FAQ)
What are digital twins in industry?
Digital twins are virtual models of real-world machines, buildings, production lines or infrastructure systems. They use sensors and software data to monitor performance, simulate changes, predict failures and improve decisions.
Is a digital twin an AI?
No. A digital twin is not AI by itself; it is a virtual model of a real system. However, digital twins often use AI, machine learning and analytics to detect patterns, run simulations and make predictions.
Why is data minimization important for digital twins?
Data minimization reduces the amount of sensitive or unnecessary information collected by digital twins, lowering the risk of data leaks, surveillance, profiling and cyberattacks.
How can companies make digital twins more secure?
Companies can secure digital twins by limiting data collection, anonymizing or aggregating information, enforcing access controls, segmenting systems, updating connected devices and deleting data that is no longer needed.
tags
Author
Vlad's love for technology and writing created rich soil for his interest in cybersecurity to sprout into a full-on passion. Before becoming a Security Analyst, he covered tech and security topics.
View all postsYou might also like
Bookmarks


