Building a CRA-ready SBOM pipeline for safer smart homes

CRA-ready SBOM pipeline planning is becoming essential for smart device security. It helps manufacturers track software components, respond to vulnerabilities faster and build trustworthy products. Learn how a CRA-ready SBOM pipeline helps IoT brands build safer smart devices and earn consumer trust.
Key takeaways
- A CRA-ready SBOM pipeline helps manufacturers track software components and respond faster to vulnerabilities in connected devices.
- Under the Cyber Resilience Act (CRA), software transparency and vulnerability handling are increasingly important for products sold in the EU.
- For consumers, stronger SBOM practices can mean better-maintained smart home products and fewer hidden software risks.
- Tools like NETGEAR Armor add an extra layer of protection in IoT households by helping secure devices already connected to the home network.
Why SBOMs matter in the age of the Cyber Resilience Act
If you use smart cameras, video doorbells, plugs, speakers or connected appliances, you probably don’t spend a lot of time worrying about their software components. However, regulators increasingly do.
Under the European Union’s Cyber Resilience Act (CRA), manufacturers of products with digital elements are being pushed toward stronger security, better vulnerability management and clearer software transparency for connected products sold in the EU.
The CRA took effect on Dec. 10, 2024, reporting obligations begin on Sept. 11, 2026 and the main obligations apply from Dec. 11, 2027.
What goes into a CRA-ready SBOM pipeline
One of the most important components in that effort is the Software Bill of Materials (SBOM). The CRA defines an SBOM as a formal record containing details and supply-chain relationships of components included in the software elements of a product. In practical terms, it is an “ingredients label” for software. It helps manufacturers know exactly what third-party libraries, open-source packages and dependencies exist inside a device or app.
For smart home brands, that matters because many IoT products are built from layered software stacks. A single connected thermostat or camera may rely on Linux components, networking libraries, cloud connectors, mobile app code and update mechanisms from multiple sources.
If one weak link is discovered, vendors need to know exactly where it is used so they can assess exposure and ship fixes quickly. That is why the CRA’s vulnerability-handling requirements call for identifying and documenting vulnerabilities and components, including by drawing up an SBOM in a commonly used, machine-readable format that covers at least top-level dependencies.
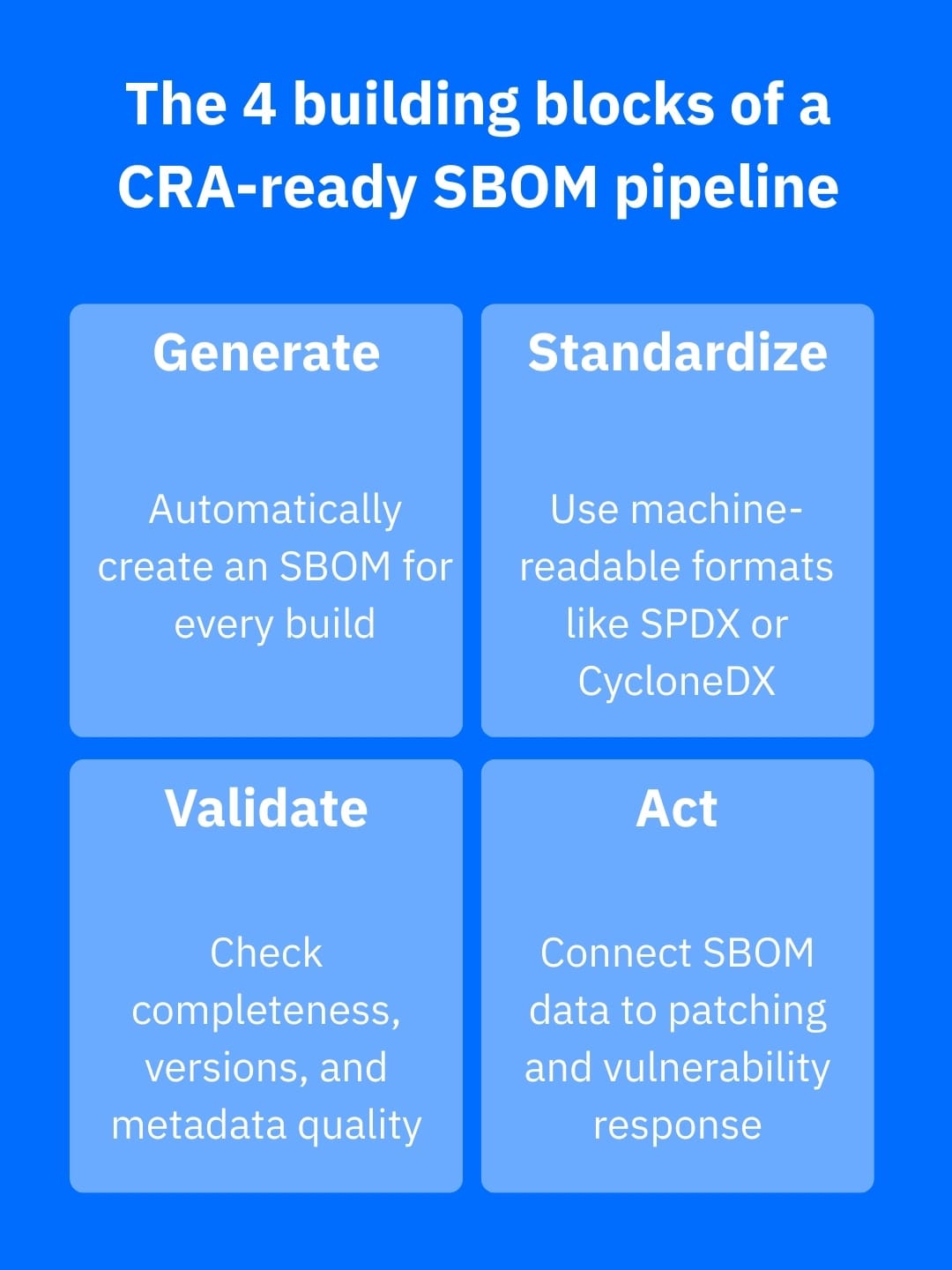
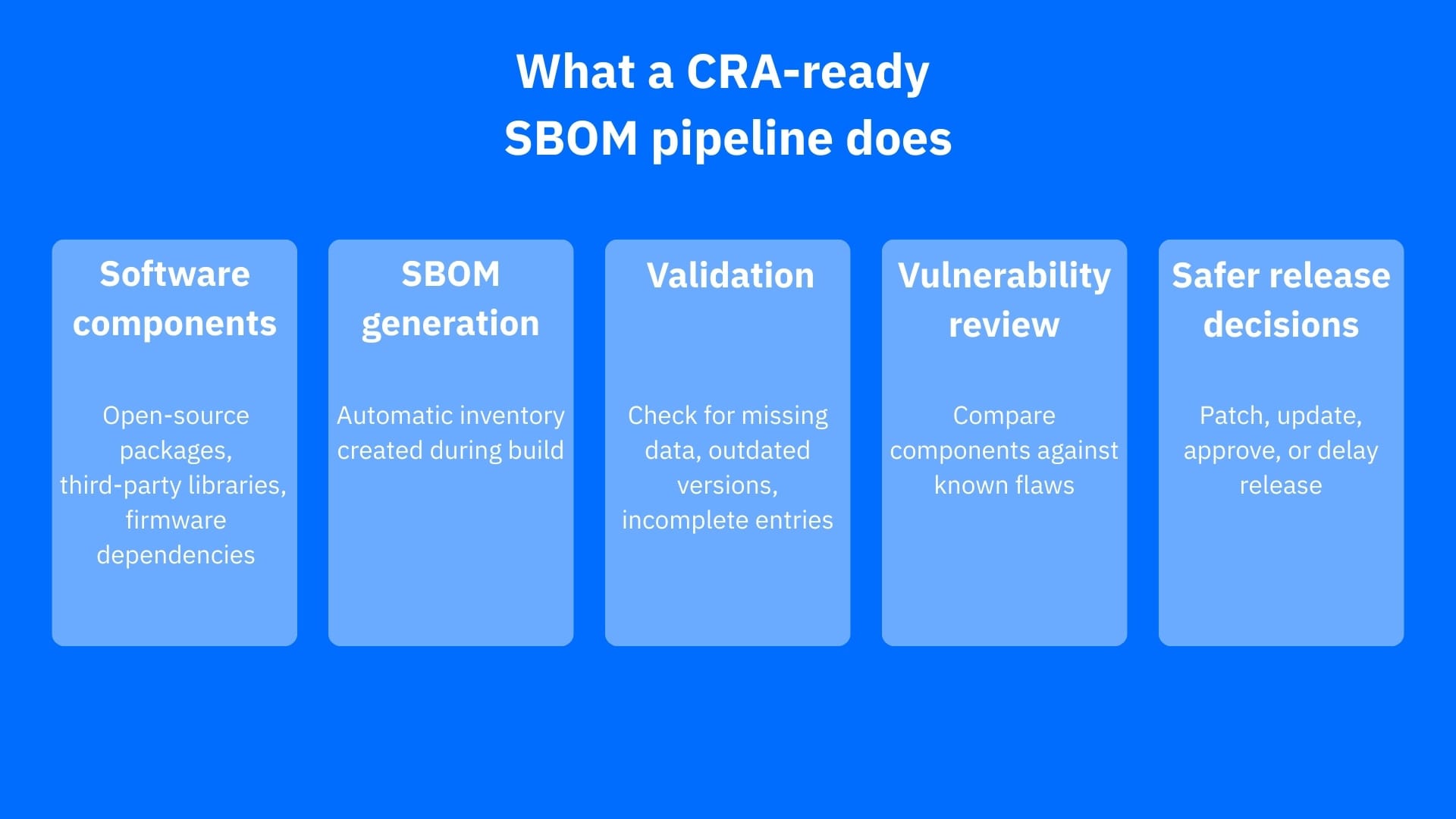
What a CRA-ready SBOM pipeline looks like
A CRA-ready SBOM pipeline is far more than a spreadsheet created moments before launch. It is an ongoing process built into development and update workflows. Each time software is built, the pipeline automatically generates an SBOM, checks it for completeness, stores it in a consistent format and links it to vulnerability management and release decisions.
That way, the SBOM becomes a living security record instead of a forgotten compliance file. Industry guidance from NTIA, CISA and ENISA all points in the same direction: SBOM are most useful when they are machine-readable, repeatable and integrated into broader supply-chain security operations.
For most teams, the pipeline should include these core steps:
- Generating an SBOM automatically during every build
- Standardizing the SBOM in a widely used format such as SPDX or CycloneDX
- Validating the file for missing components, bad metadata or version gaps
- Acting on the results by connecting the SBOM to patching and vulnerability review workflows
Why software transparency matters to smart home users
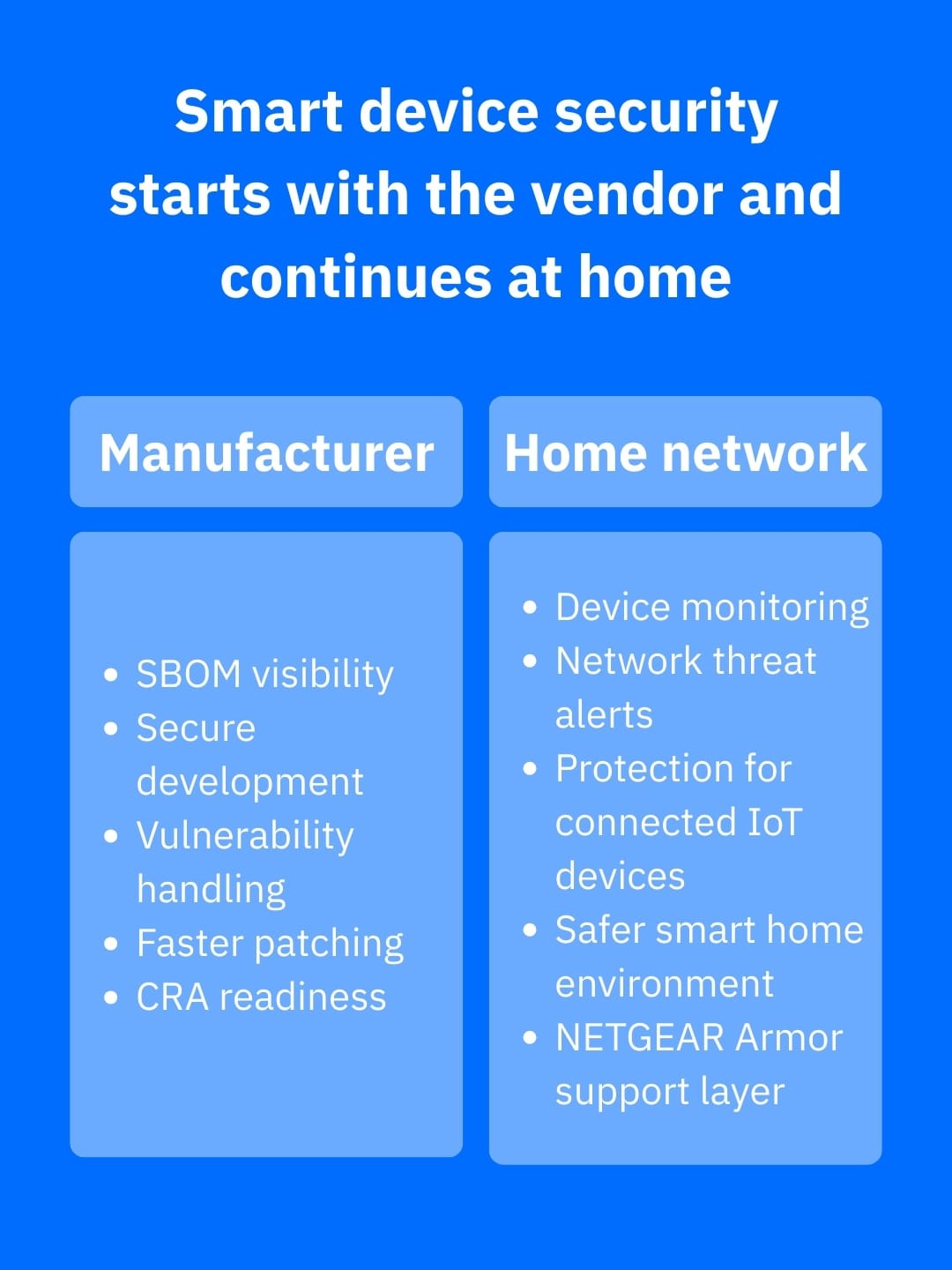
While this may sound like back-office engineering work, it has real consequences for households full of connected devices. When vendors understand their software components, they are in a better position to respond to newly disclosed flaws, see devices through their entire support period and communicate security updates more effectively.
The CRA itself is designed to simplify this for consumers and businesses alike, so they can easily identify products with appropriate cybersecurity features, while also improving accountability across the product lifecycle.
In other words, a strong SBOM pipeline supports something consumers already want – fewer silent security surprises in the products they bring home.
Caveats to avoid
A common mistake is treating generating SBOMs as a one-time box-ticking exercise. A static SBOM created once – then ignored – will not help much when a new vulnerability appears months later in a reused component. A CRA-ready approach means updating SBOMs as firmware, apps, dependencies and cloud-connected functionality evolve.
It also means making sure the information is usable, not just technically present. ENISA’s recent implementation work stresses that successful SBOM adaptation depends on process integration and organizational maturity as well as tooling.
SBOM visibility alone is not enough for IoT households
Even the best manufacturer pipeline cannot eliminate all smart home risk. Consumers still need protective layers in the home because connected devices can remain exposed through weak passwords, unsafe configurations or delayed updates. That is where network-level protection comes in.
For households with many IoT devices, NETGEAR Armor is a practical second line of defense. Powered by Bitdefender, it can help protect smart devices, phones and laptops connected to supported Orbi and Nighthawk systems. It also extends protection beyond the home network by increasing device visibility, alerting users when new devices join the network and providing broad defense against threats targeting home networks.
Conclusion
The smartest way to think about a CRA-ready SBOM pipeline is that it is not merely about regulation, nor does it only affect developers. It revolves around giving connected products a clearer security paper trail, from building stage to living room.
For IoT brands, that translates into a better chance that the smart devices they rely on are supported by security practices built for the real world.
Frequently asked questions (FAQ)
What is an SBOM in cybersecurity?
An SBOM, or Software Bill of Materials, is a structured inventory of the software components, libraries and dependencies inside an application, device or firmware. In cybersecurity, it helps vendors identify what is running inside a product, track vulnerable components and respond faster to newly discovered flaws.
What is CRA in terms of security?
In cybersecurity, CRA usually refers to the Cybersecurity Resilience Act, an EU regulation designed to improve the security of products with digital elements, including connected devices and software. It focuses on secure-by-design practices, vulnerability handling, software transparency and stronger accountability across the product lifecycle.
Is SBOM legally required?
An SBOM is not required by law in every country or for every product, but it is increasingly important in regulation, procurement and compliance. Under framework like the EU Cyber Resilience Act, manufacturers may need software component transparency and documentation that make SBOM practices highly relevant, especially for connected products sold in regulated markets.
tags
Author
Vlad's love for technology and writing created rich soil for his interest in cybersecurity to sprout into a full-on passion. Before becoming a Security Analyst, he covered tech and security topics.
View all postsYou might also like
Bookmarks


