What is a Secure VPN? And the Reasons You Need One
Staying connected and sharing information online has never been easier. But with so many opportunities to share every aspect of your life, protecting your online identity can sometimes feel a bit overwhelming.
Find out how a secure VPN can protect your online privacy, keep your digital footprint under control - and why it's important to make sure you choose the right one.
What is a VPN? A Definition from Security Pros
As our lives grow more digital each day, one of the biggest challenges we are faced with is protecting personal information. By definition, a VPN does just that by securing data transfers and keeping your identity private.
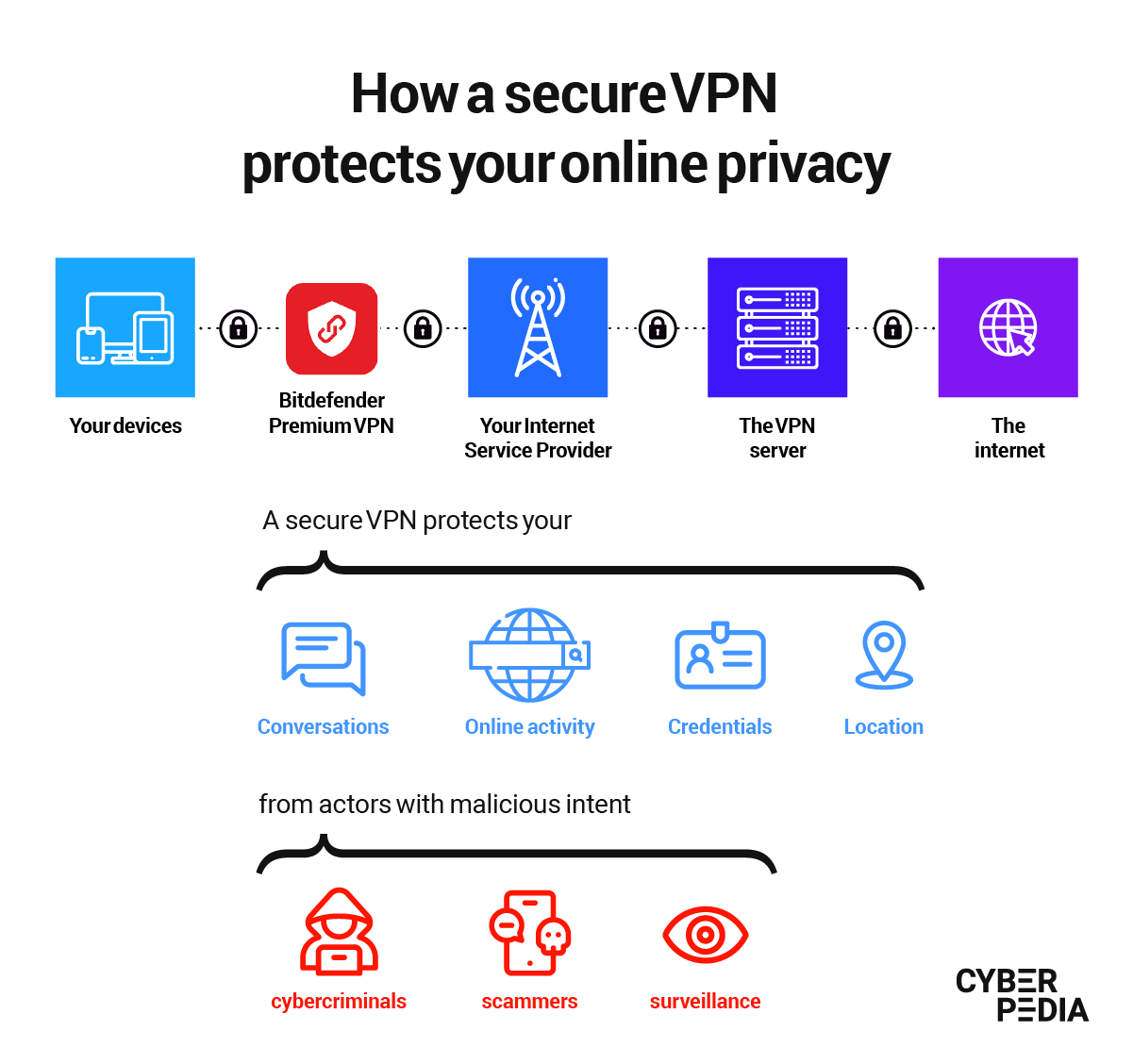
First and most important of all, a virtual private network (VPN) protects your Internet connection by encrypting all the data flowing between your device and the online resource you are trying to access, be it website, desktop app or mobile app.
For example, if you are logging in to check your e-mails, you can be sure that you are the only one reading them because the connection is safe and encrypted.
Secondly, a VPN shields all the personal data you send and receive from those who might try to harvest it, by rerouting your Internet traffic through a safe server. Some of that private information might include geographic location, your IP address, browsing habits, device information and many other sensible data like passwords or private documents.
What Does a Secure VPN Do?
A secure VPN has a lot of benefits to offer, especially to people who value their online privacy, and are trying to reduce their digital exposure. Let’s see what some of those benefits are according to our cybersecurity experts.
Personal Data Privacy
Almost every online resource you use knows your IP address. And they can utilize it to find out where you live, what type of device you are using and what time you are online. In fact, advertisers already use this information to target you with personally tailored ads.
The scary part is that your IP address is just a small fraction of the many things that expand your digital footprint without you even realizing it. Linked with other personal data scraped from all over the Internet, and from data breaches (like your, name, e-mail address, or phone number), it makes it much easier for scammers and other cyber-criminals to target you with customized messages that trick you into giving them what they want (information, money, or both).
“Just by knowing someone’s IP Address you can launch a Distributed Denial-of-Service Attack (DDoS) against them, virtually cutting their Internet connection. But that’s not all. In terms of privacy, you can track their online activity and find out a lot of other things about them and the devices they’re using. For example, you might find out they’re using a device that wasn’t updated and that can easily be hacked. Moreover, personal information is like a puzzle, cyber-criminals rarely find only one piece, and the more pieces they collect the more dangerous it gets for that person.”
Alex "Jay" Balan (Director of Security Research, Bitdefender)
So, when it comes to protecting your digital identity, a secure VPN is one of the most helpful tools in your online safety setup. A safe, reliable VPN hides your identity and protects your online activity, which in turn throws off any interested parties in tracking you, harvesting your data or building a profile to scam you.
Here is how:
- It hides your IP address and masks your location, fending off efforts to pinpoint your whereabouts.
- It prevents DDoS attacks that could potentially prevent you from connecting to the Internet
- It prevents interested parties from tracking your online habits, including advertisers, ISPs, or cyber criminals
- It prevents hackers from harvesting information about your devices
- It does not store any traffic logs, which means it does not keep records of your online activity while you have the VPN enabled.
Personal Data Security
When talking about a VPN, often times people tend to focus only on the privacy benefits and overlook the security-oriented perks. However, this should not be the case, as security is also a vital component with compounding effect in the long run, by protecting communication and shielding devices.
A secure VPN is designed to offer robust security features and is all about making sure your data goes straight to where you intended, with no detours or interference.
In practice, a VPN creates a secure tunnel for your data from sender to receiver. The virtual private network reroutes your data through this encrypted tunnel which ensures stronger protection against tracking and certain cyber-attacks.
Basically you make it substantially more difficult for hackers to:
- Capture your usernames and passwords and use them to hijack your accounts
- Get your online banking details and empty your account
- Intercept your private communication (including private pictures or video) and use them for blackmail
- Collect your personal information and use it for digital identity theft
- Impersonate you on social media with the details they gathered through your online activity.
A VPN does more than just securing your data under strong encryption. It also unlocks remote access to resources you would not be able to use otherwise. For example, with Bitdefender Premium VPN, you can stream content from anywhere in the world or use messaging platforms and other apps that may be unavailable in your country. And this works for all your devices, no matter if they run Windows, macOS, Android or iOS.
What Is a Secure VPN Connection?
A secure VPN connection does not compromise on the key factors that keep invasive use of technology at bay, whether they are being used by mainstream organizations or cyber-criminal operations.
To be truly secure, a VPN connection must use the highest encryption standard available (right now, AES 256-bit).
Secondly, it must include various security protocols that protect the confidentiality of your data. These protocols make sure unauthorized entities cannot access the connection and the integrity of the data you send and receive remains intact. A secure VPN should feature protocols such as Internet Protocol Security (IPsec), Transport Layer Security (SSL/TLS), Datagram Transport Layer Security (DTLS) and more.
The third most important aspect of a secure VPN connection is the no-logs policy. This is the VPN provider’s commitment to never store details of your online activity while the app is enabled. This policy guarantees that an attacker cannot gain access to protected information if they compromise the VPN developer. The same applies to other entities that may pressure the VPN maker into giving away data about their users, under legal pretenses or otherwise.
If you are looking into a variety of VPNs, make sure the one you choose protects you against IP address leaks. It is also a great sign if it has an Internet kill-switch that automatically closes certain programs in case your connection gets spotty. You can use this automated feature to avoid data leaks that might reveal sensitive information. And if the VPN app of your choosing also features two-factor authentication, then you have a potential winner on your hands.
How Secure Is a VPN? How to Make the Right Choice
The answer to this question relies entirely on the reputation and history of the organization that created the VPN application.
Take it from a cybersecurity expert to which being extra cautious is second nature:
“The thing that makes the fundamental difference in terms of how likely it is for your data to get leaked is the reputation of the company managing it.
This is the one very important thing to keep in mind when you’re sharing extremely sensitive information with a company. And that’s not necessarily your email and password – because your password can and should be different on all the websites you use.
When you share a very sensitive document, then you have to be very careful about selecting a technology ‘partner’ you’re going to share the document with. The company that will manage your data needs to be trustworthy and you need to review how they handle security, how they deal with vulnerabilities and how they’ve handled security incidents in the past.”
Alex "Jay" Balan (Director of Security Research, Bitdefender)
It is important to remember that VPN services are not secure by default. The level of protection they ensure depends on a variety of factors – like the team who developed the product, the track record of the company that created the VPN and even the physical location of the organization (as legal provisions may interfere with having a no-logs policy, for example).
Another aspect you should be careful about is using free VPNs. Tempting as it may be, cybersecurity and privacy researchers have proven time and time again that free VPNs collect user data and then share it with advertisers or other entities. This essentially defeats the purpose of a virtual private network.
How to Get a Secure VPN
First and foremost: make sure the VPN developer has a level of technical expertise and maturity that gives you peace of mind and the certainty that they hold up their end of the terms of service.
If you are ready to take the next step, check out the Bitdefender Premium VPN and see if its ultra-fast speed, servers and safe access capabilities are what you need.
How to Set Up a Secure VPN
Using a virtual private network was at some point the privilege of tech-savvy individuals who knew their way around protocols and other security concepts. But that is no longer the case.
Online privacy and security protocols have come a long way, just in time to meet the ever growing need to stay safe online.
With Bitdefender Premium VPN, protecting your connection is as simple as downloading the app from your Bitdefender Central account, installing it and then hitting the “Connect” button.
As always, our cybersecurity experts encourage you to build your online protection in layers, with a secure VPN protecting your anonymity online and other solutions fending off other types of cyber-attacks.
Pro tip: when you get all your security layers from a single provider, you will get better integration and more effective protection with no overlap or software conflicts. Just something to keep in mind for your next online security decision!
tags
Author
Choose what the experts use. Award-winning cybersecurity you can trust and rely on.
View all posts

