This article is a step-by-step guide to help you manually eliminate fake antivirus infections quickly. We’ll also help you understand how fake antivirus works and how to identify it.
How to Recognize a Fake Antivirus Program
Rogue security software designers create legitimate looking pop-up windows that advertise security update software. Such windows might appear on your screen while you surf the web. They may appear as a “warning message” displayed on a web page, notifying the user that their system is “infected”.
Here are some examples of fake antiviruses:
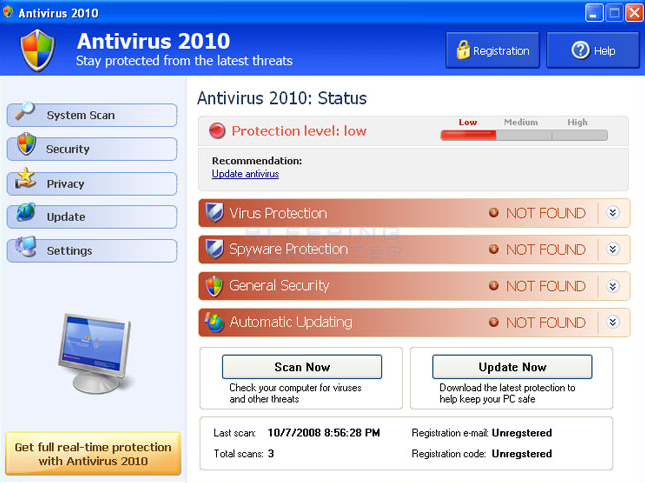
The “updates” or “alerts” in the pop-up windows call for you to take some sort of action, such as clicking to install the software, accept recommended updates, or remove unwanted viruses or spyware. When you click, the rogue security program downloads to your computer.
Most have a Trojan horse component, which users are misled into installing. The Trojan, which is a type of malware harming your computer from within, may be disguised as:
- A browser plug-in or extension (typically a toolbar)
- An image, screensaver or archive file attached to an e-mail message
- A multimedia codec required to play a certain video clip
- Software shared on peer-to-peer networks
- A free online malware scanning service
All of these files will appear with an .exe extension, meaning that they are executable files. Once executed, the infection is automatically deployed.
How to Remove a Fake Antivirus
We have created a clear set of instructions to help you remove malware if your computer has been infected with a fake antivirus.
 + the C key.
+ the C key.