Cybersecurity Tips in Armed Conflict Zones. Here’s How Bitdefender Is Helping
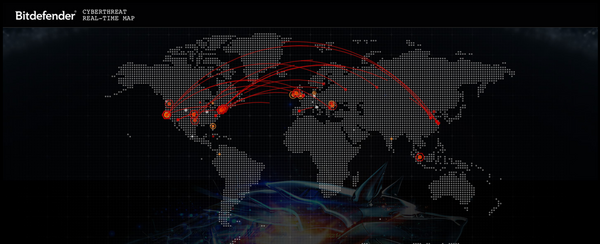
We’re living in unprecedented times. Cyberattacks during a military crisis have become the norm, as they are a highly effective way to divert attention and create panic. For more than a decade, security companies have been making significant efforts to fend off state-sponsored attacks and hacktivists, as well as to anticipate the enemy’s next move in this fifth dimension of warfare.
This article aims to help people in conflict areas to improve their security posture, educate citizens on the threats of an increasingly inter-connected world, and arm businesses and institutions with a set of actions to fight against emerging attacks.
In our offices in Bucharest, on the Eastern NATO flank, we are deeply concerned with the events unfolding in Ukraine. We want to do our part and lend a helping hand. In this regard, Bitdefender & the Romanian National Cyber Security Directorate (DNSC) are offering free cybersecurity protection during this time, for any Ukrainian citizen, company, and institution, for as long as necessary.
Truth is always a casualty of war. As misinformation spreads, it gets increasingly difficult to determine what's true and what isn’t. It’s not the first time fear and lack of information are weaponized to spread malware. The COVID-19 outbreak in early 2020 served as the perfect example: cybercriminals used seemingly valid information from ‘official’ sources to spread malware and deploy phishing attacks.
Like then, people are now anxious to know the latest developments. This opens the door to attacks. Here’s what you can do:
- Don't open emails or attachments coming from untrusted senders, especially those that try to induce a sense of urgency, even if they look or sound ‘official’
- If you don't know the sender, don't click links arriving via instant messaging apps or SMS
- Don't participate in spreading fake information via social media or instant messaging. A clear red flag is a message that urges you to share that information further.
- Install a security solution as soon as possible. Modern security solutions prevent you from accessing malicious links, block malware before installation, and notify users when they receive malicious content. This is particularly important now, as some ransomware operators have pledged to help Russia execute cyber-attacks against rival nations. Security solutions can also help keep devices operational so people can stay connected, even during disruptions.
- If you're in a conflict zone, turn off location services.
- Watch out for phishing attempts, particularly if you (or someone you know) are in the military Stolen credentials can and will be used to access sensitive or classified information.
- Avoid checking in on social platforms if not absolutely necessary. The lower the online footprint, the safer you are.
- Use a VPN solution whenever possible. Remember that sharing pictures may also reveal your location or other personal information through the embedded metadata.
- Sanitize images prior to sending them to others (watermarks, EXIF data, etc).
- Talk to your children. As avid social media users, they must understand that sharing certain information online can disclose sensitive information to unintended parties. Use parental control solutions to manage who they can get in touch with or how much personal information they can share.
For companies, it’s challenging to issue a common set of rules that apply identically to every infrastructure. But there are some common measures that IT administrators can immediately apply:
- Check internal systems and company-issued devices, ensuring that the latest security patches have been installed. Critical vulnerabilities are always weaponized as soon as they are discovered.
- Ensure that all employees are up to speed with security rules - i.e. avoid using work devices for anything other than work.
- Perform a quick audit of the network infrastructure to ensure that no unnecessary ports are left open.
- Look for misconfigurations or outdated software.
- Restrict the use of remote desktop connections unless they are absolutely necessary.
- Make sure that all endpoint protection clients are up and running with the latest updates.
We are also providing free-of-charge cyber technologies and expertise to any NATO member, as well as to any company or public entity in the EU seeking to enhance their security posture by replacing existing solutions that present trust concerns from a technical or geopolitical perspective.
tags
Author
The meaning of Bitdefender’s mascot, the Dacian Draco, a symbol that depicts a mythical animal with a wolf’s head and a dragon’s body, is “to watch” and to “guard with a sharp eye.”
View all postsYou might also like
Bookmarks


