Verizon Study Shows Mobile Devices among Top Entry Points for Hackers, Ransomware Remains Most Successful Attack

The Facebook data breach of 2018, probably the biggest of the year, illustrates better than any other example that no company, big or small, is immune to hackers. One would expect a company of Facebook’s size to sustain top-tier research and development for cybersecurity, but last year’s breaches prove it’s vulnerable anyway.
The worst breaches and data leaks of 2018 include large companies and organizations, in multiple sectors, that operated on exploitable vulnerabilities. Amazon, T-Mobile, Google+, British Airways, Air Canada, Ticketmaster, Marriott hotels, Rail Europe, Saks and Lord & Taylor, Dixons Carphone and Under Armour made the list of worst incidents.
Details of large breaches are rarely publicly disclosed. The new Verizon Mobile Security Index 2019 report found that too many organizations were poorly prepared to fend off attacks in 2018, resulting in data theft or downtime. Since smartphones, tablets, laptops and other connected devices are gaining popularity in the workplace even as they draw little scrutiny, the report takes a deep dive into mobile vulnerabilities. The percentage of organizations that confirmed that a mobile device introduced unnecessary risk or was involved in a data breach in 2018 rose to 33 percent in 2018, from 27 percent in 2017.
Companies’ failure to properly fend off attacks show them that their current defenses are not enough. Some 86 percent are concerned about the flourishing of mobile threats this past year, and 93 percent of financial services firms worry that they need to deploy stronger security.
Breaches are often caused by phishing and social engineering schemes that trick employees into clicking on infected links. Employees are the number one threat companies are concerned about, as stated by 38 percent of respondents, followed by activist groups or partners. The most-cited motives are personal gain (46%), unintentional (36%), grudge (32%), convenience (32%), ideology (27%), espionage (24%), fun/curiosity (24%) or duress/management pressure (21%).
Mobile devices come with many features that can easily be corrupted, which places them towards the top of the hacker entry point list. 39 percent of respondents said a device’s microphone is the top function that can be tampered with, among others that can easily facilitate access to customer lists, bank details, employee personal data or billing information. 51 percent of “sophisticated actors” targeted both mobile devices and desktops.
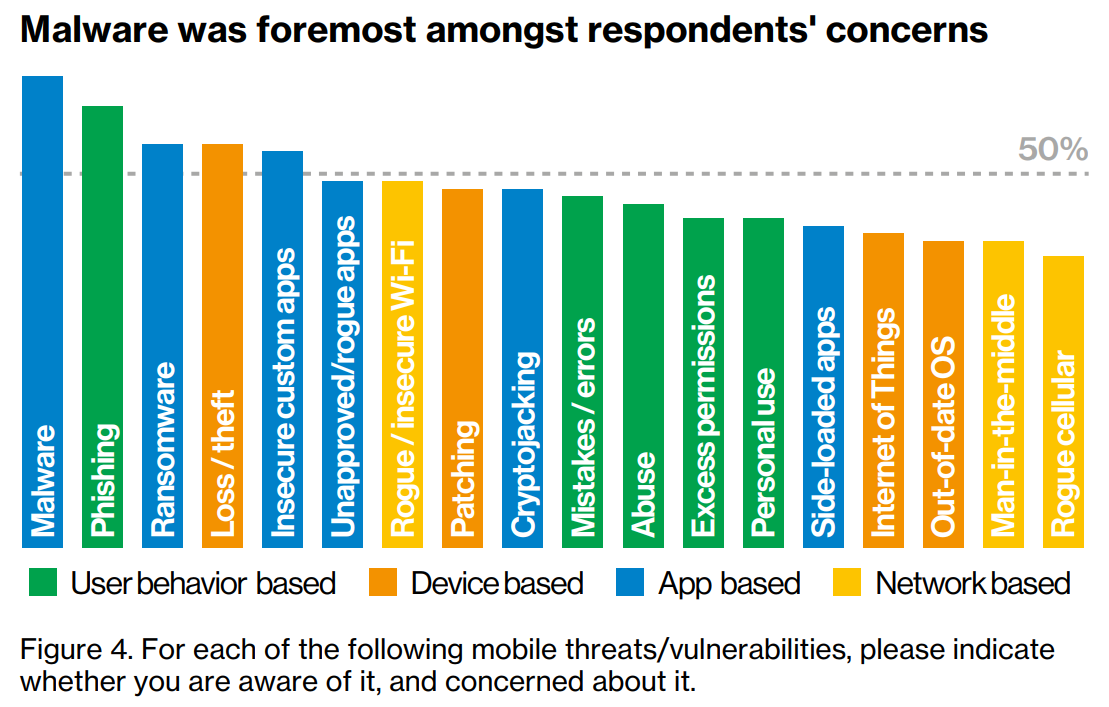
Ransomware has been trending as a top malware concern recently, so it’s no surprise that Verizon confirms ransomware as one of the most successful malware attacks of 2018.
Mobile compromises led to security breaches in companies of all sizes from all industries. Even though the companies understand the importance of security, 48 percent of them are willing to “sacrifice security to ‘get the job done’,” often resulting in a “mobile-related compromise.” Some organizations are overconfident in their current mobile security measures. 84 percent think they are “effective” and 79 percent trust them to instantly detect a vulnerable mobile device, but somehow this is not the case.
tags
Author

From a young age, Luana knew she wanted to become a writer. After having addressed topics such as NFC, startups, and tech innovation, she has now shifted focus to internet security, with a keen interest in smart homes and IoT threats. Luana is a supporter of women in tech and has a passion for entrepreneurship, technology, and startup culture.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks










