The Internet of Things is going to require a maniacal focus on availability and security
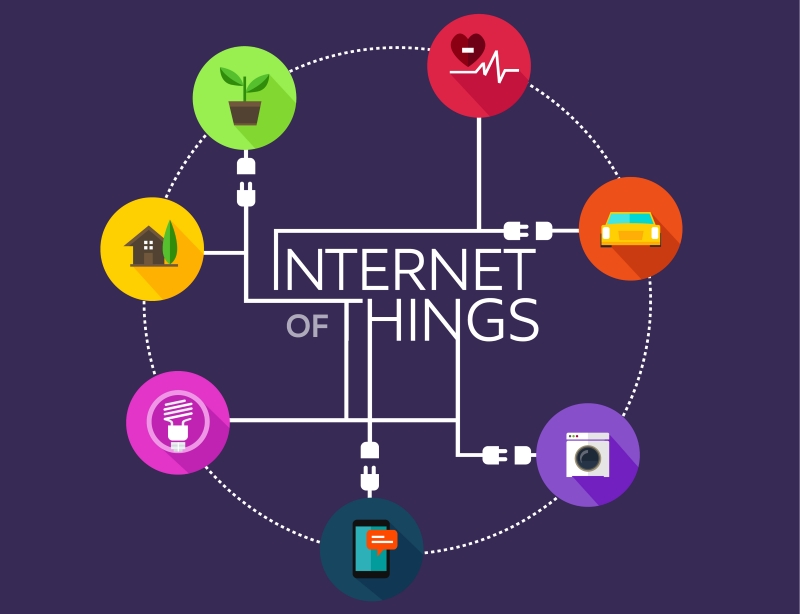
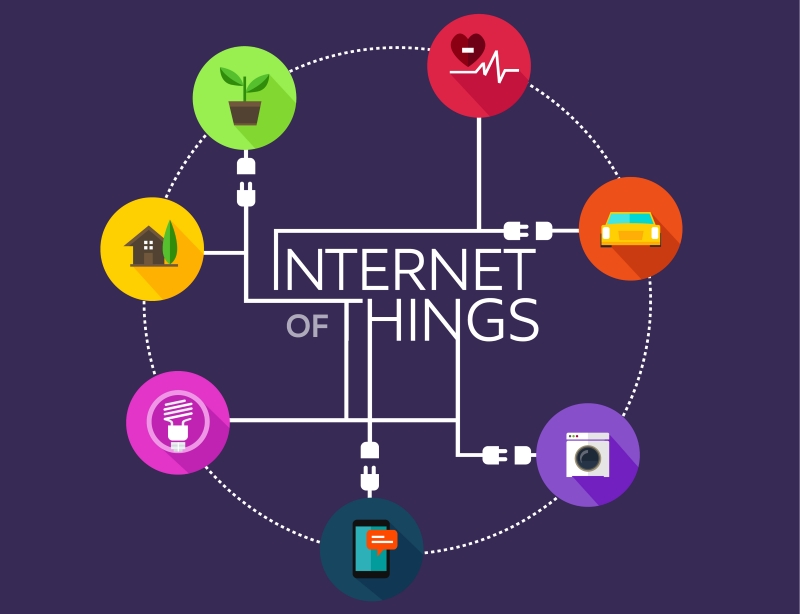
The Internet of Things is quickly moving from hyped concept to reality – and it’s proving to be a mix of consumer devices, such as home thermostats, electric locks, and security systems to the industrial Internet of Things, which ranges from devices that help improve field machinery maintenance to fully automated office campuses. We really are moving from the phases of connected to devices, and each other, to connecting everything.
We recently blogged about the IoT in the post, Don’t let the Internet of Things Catch You by Surprise.
Enterprises that deploy and manage IoT devices will find their attack surface increasing, which is the space that is attackable by adversaries. They’re also going to find that their business risks increase, too. What this means is that business leaders have to understand how disruptions, hacks, and data breaches that stem from the IoT can have a profound impact on how people trust, or don’t trust, a business’s brand.
This will be true in both the industrial and consumer Internet of Things: customers just won’t tolerate disrupted access to their physical world through cyber attacks. It’s one thing to be denied access to your credit card’s web site because of a worm or a denial of service attack, which causes a delay in finishing an expense report; it’s something else to be denied access to one’s car, home, or heating and cooling system.
How many times would you tolerate being locked out of your home through electronic locks being hacked, or your car being stalled (or worse) through some malicious attack? How many business managers would tolerate corrupted telemetry information coming in from their field sensors? Not many.
When it comes to these kinds of attacks, we are seeing warning signs. In December, it became clear that attackers managed to commandeer control of the mill system in a German steel works. According to this BBC story, Hack attack causes 'massive damage' at steel works, the attackers sent attack phishing emails that enabled them to steal the credentials they needed to access the machinery in the mill.
The story quoted the annual report of the German Federal Office for Information Security (BSI) and said, “In its report, BSI said the attackers were very skilled and used both targeted emails and social engineering techniques to infiltrate the plant. In particular, said BSI, the attackers used a "spear phishing" campaign aimed at particular individuals in the company to trick people into opening messages that sought and grabbed login names and passwords,” the BBC reported.
Last summer, David Jacoby wrote in Dark Reading How I Hacked My Home, IoT Style that he analyzed all of the things attached to his home network: a smart TV, satellite receiver, DVD/Blu-ray player, network storage devices, gaming consoles, and such. “As I started my research, it didn’t take long to figure out just how easy it was to find vulnerabilities in all of the systems. I managed to find 14 vulnerabilities in the network attached storage, one vulnerability in the smart TV, and several potentially hidden remote control functions in the router,” he wrote.
This state of affairs is very reminiscent of the Web era in the late 1990s, when enterprises started to open up their databases – databases that were once tucked behind their firewalls were indirectly exposed to the open Internet in the rush to engage in ecommerce – and only a few (if any) actually bothered to vet the applications for security flaws. From that, we had an age of operating system and web worms that wreaked havoc. While we have a long way to go, operating systems – and to a large degree web applications – are much better today than they were 15 years ago.
Do we really want to repeat this with the IoT? I know I don’t.
It’s important, as the market moves toward the IoT, that we learn from the lessons of eCommerce and the early days of the Web and design and deploy IoT devices and communications with security in mind – instead of bolting security onto those devices and systems after the fact.
The good news is that these are things that we already know well how to do. We know how to threat model the devices and then improve their design. It’s also going to require that the makers of IoT devices take a page from the DevOps playbook and adopt continuous improvement in their designs. That’s going to need tight collaboration among designers, security teams, and developers, and continuous feedback from customers and field technicians.
The alternative is to have these embedded devices get sold and then never updated even though they’re connected or are updatable.
If we want a secure and resilient IoT, that just won’t do.
tags
Author

George V. Hulme is an internationally recognized information security and business technology writer. For more than 20 years Hulme has written about business, technology, and IT security topics. From March 2000 through March 2005, as senior editor at InformationWeek magazine, he covered the IT security and homeland security beats. His work has appeared in CSOOnline, ComputerWorld, Network Computing, Government Computer News, Network World, San Francisco Examiner, TechWeb, VARBusiness, and dozens of other technology publications.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks










