Introducing Unified Incidents: Streamlining EDR and XDR in GravityZone

Bitdefender's new Unified Incidents feature simplifies the process of identifying connections between historical events and current alerts, enhancing incident detection and response.
Analyzing security incidents can be overwhelming for security analysts. Having to sift through extensive data from various sources without clear connections significantly reduces response time and the likelihood of stopping the spread of an attack. With the new Unified Incidents feature under GravityZone, administrators gain access to a consolidated platform that streamlines the analysis process by providing a unified view.
Unified Incidents
Unified Incidents consolidates all incidents and detections into a single panel. Whenever possible, this functionality correlates endpoint detection and response (EDR) incidents at the host level with larger-scale attacks identified by extended detection and response (XDR) that originate from sensors. Once incidents are correlated, only the root entry remains, simplifying the triage process, and allowing security professionals to concentrate on these more intricate incidents.
The primary incident entry covers all response actions necessary to stop the attack. Depending on the sensor type, administrators may use actions such as, but not limited to, isolating hosts, initiating a forced credential reset, disabling users, or deleting emails.
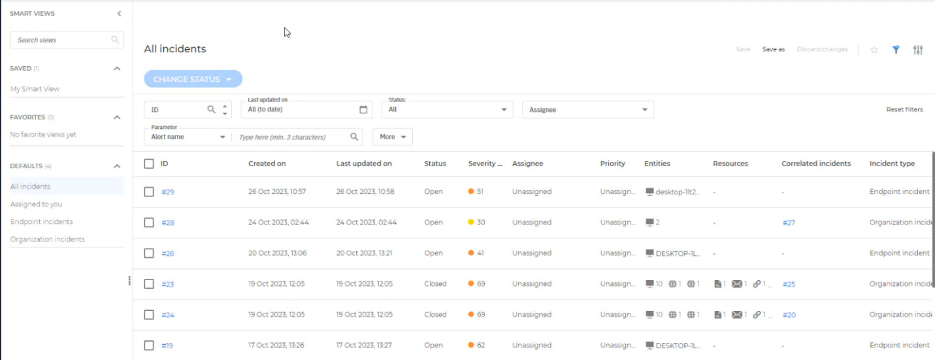
GravityZone Incident offers a comprehensive view of all incidents.
In the main incidents section administrators can customize smart views according to their needs or use default ones. Enhanced filtering capabilities including but not limited to parameters such as correlated incidents, Att&ck technique, IP, SHA256, username, filename, email address, URL, and process path, enabling administrators to efficiently refine and manage security incidents more effectively.
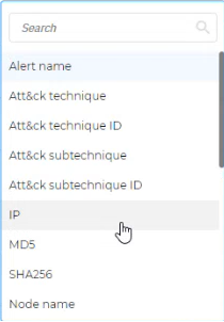
In GravityZone Incident, security teams can quickly review incidents using parameter filters.
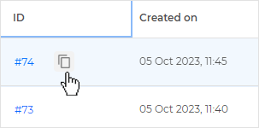
The administrator can copy the link to incidents, facilitating the seamless sharing of incidents among SOC teams.
By selecting the correlated incident's ID from the incident section, the administrator will be redirected to the graph displaying the correlated incident. This section can include multiple related incidents that together comprise the attack, with the number varying based on the attack's complexity.
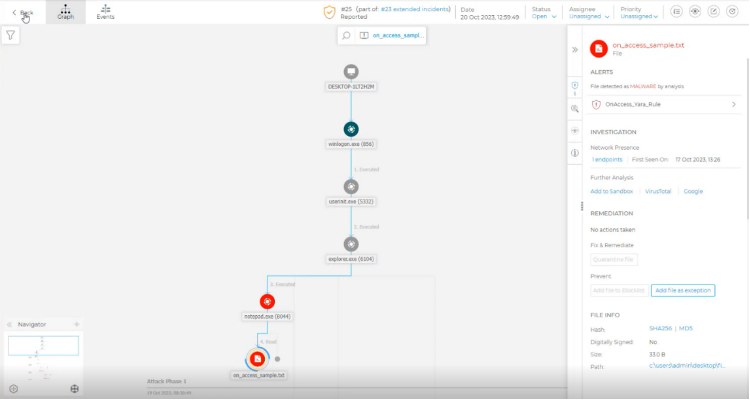
GravityZone Incident Graph provides information about all details, including alerts, investigation, and remediation actions.
When security professionals analyze incidents, they can review events and alerts by utilizing the View Events and Alerts menu. This enables a Historical Search with an automatically predefined query based on selected active incidents, facilitating future investigations.
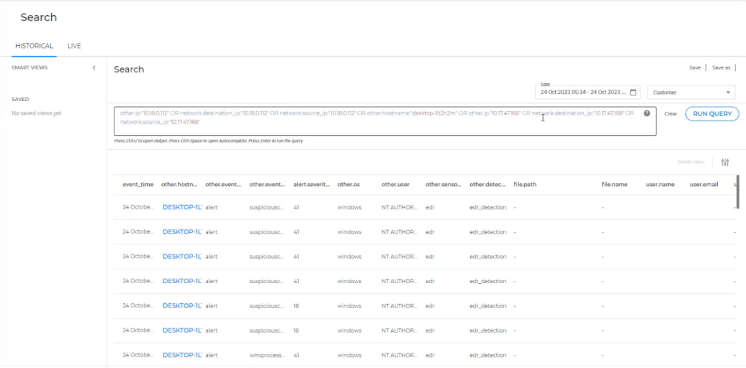
GravityZone Historical Search with a predefined query.
Summary
In summary, Unified Incidents in GravityZone redefines incident management. It empowers security analysts with an integrated and streamlined approach, enabling them to identify patterns and connections swiftly, respond promptly, and enhance their overall ability to proactively thwart the spread of potential attacks. This marks a key step forward in the realm of cybersecurity, aligning technology with the dynamic needs of modern security landscapes.
tags
Author
Grzegorz Nocon is a graduate of the Faculty of Physics at the University of Silesia. With over 16 years of experience in the IT industry, he currently works as a Technical Marketing Engineer at Bitdefender. A strong supporter of a holistic approach to security and passionate about solving security problems in a comprehensive and integrated way. Outside of work, an avid CrossFit enthusiast and a lover of fantasy literature.
View all postsYou might also like
Bookmarks


