Cybercrime Dominates Business Fraud Losses

Business fraud has been on a dramatic uptick over the last decade and cybercrime stands near the top of the list of losses and events that organizations are experiencing. A new report out from consulting powerhouse PwC found that the ratio of organizations who admitted to falling prey to economic crime in the past year has increased by 63% since 2008, with just under half of organizations admitting to being victims.
Most relevant to cybersecurity professionals, the 2018 Global Economic Crime and Fraud Survey showed that globally cybercrime was the number two type of fraud behind asset misappropriation, ahead of business misconduct, bribery and corruption, and fraud committed by the consumer. In the US it was the top fraud category.
In some ways the incidence of cybercrime relative to other fraud may be understated, because certain types of general fraud are initiated through cyberattack. The report explains:
While all digital fraud is fraud, not all fraud is digital. It can therefore be helpful to distinguish two forms of cybercrime:
(1) As digital theft (the stolen goods, not the smashed door). This type of attack could include stealing cash, personal information, and intellectual property, and could involve extortion, ransomware, or a host of other crimes.
(2) As digital fraud. This type of attack is in many ways the more long-lasting and disruptive, because the fraudster penetrates an open door (typically, but not always, a customer- or employee-facing access point) and uses the company’s own business processes to attack it. To combat this type of fraud, the organisation must use digital methods – both as a vaccine and as a remedy. 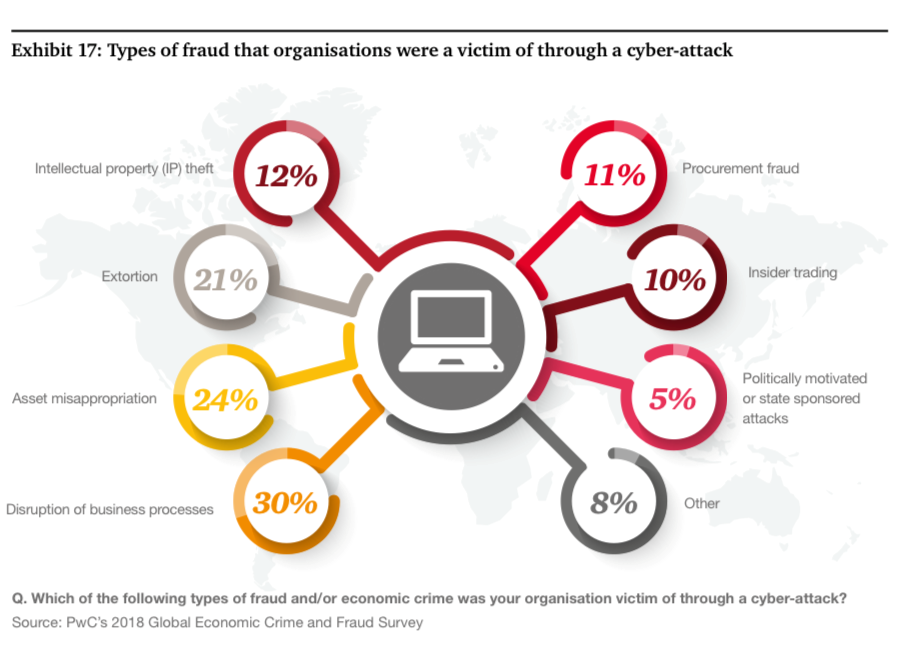
For example, 24% of organizations experienced asset misappropriation through a cyberattack. In the same vein, 21% experienced extortion through cyberattack, and 30% experienced disruption of business processes.
"In fact, cyber- attacks have become so pervasive that measuring their occurrences and impacts is becoming less strategically useful than focusing on the mechanism that the fraudsters used in each case," the report authors say.
Unsurprisingly, malware and phishing dominate the top cyberattack techniques used by organizations, which occurs with the following frequency reported by the enterprises surveyed:
- 36% malware
- 33% phishing
- 13% network scanning
- 10% not sure of technique
- 8% brute force attack
- 7% man-in-the-middle attack
- 3% other techniques
For many organizations, cybercrime was reported as the most disruptive and serious type of economic crime to impact them in the next two years. And many organizations expect it to be one of the most common disruptive factors to hit them in the near future-- it was more than twice as likely as any type of very disruptive fraud to expected in the next two years.
That high degree of disruption likely has to do with the extreme costs of clean-up and remediation relative to other kinds of fraud. Cleaning up after a case of bribery is likely to be a lot simpler than a complex cyberattack, which frequently involves not only legal and regulatory fines but also attendant costs in detailed technical forensics, cleaning up the network and other digital assets, and bringing in new cybersecurity technology to prevent similar attacks in the future. The PwC survey showed that 41% of executives queried spent at least twice as much on investigations and related interventions as they did on the actual cyber fraud losses or thefts themselves.
Unfortunately, too many organizations today aren't being proactive enough about the problem. Only 54% of organizations have conducted a general fraud or economic crime risk assessment in the past two years and less than half of them have conducted a cybercrime risk assessment, PwC says.
tags
Author

An award-winning writer, Ericka Chickowski specializes in coverage of information technology and business innovation. She has focused on information security for the better part of a decade and regularly writes about the security industry as a contributor to Dark Reading. Chickowski’s perspectives on business and technology have also appeared in dozens of trade and consumer magazines, including Consumers Digest, Entrepreneur, Network Computing and InformationWeek.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks










