Bitdefender Threat Debrief | May 2023

MDR Insights
At Bitdefender MDR service, we highly value the power of big data in delivering valuable insights into intelligence matters. Recently, we conducted an extensive analysis of the information requests we receive from our diverse teams and stakeholders. Upon examining the data, we found that almost 60% of customer inquiries revolve around a fundamental question: "Are we adequately protected?"
The answer to that question is a resounding 'YES'! You may wonder how we achieve this level of protection. The answer lies in our multi-layered approach.
For starters, our Bitdefender Labs team is an incredible resource to the company, with security research teams armed with diverse skills and expertise. They diligently monitor global activities, including telemetry from millions of sensors worldwide, which provide real-time information about ongoing malware campaigns. Additionally, they stay up to date with security advisories and bulletins released by governments and research organizations worldwide. Based on various indicators, our researchers develop machine learning models and signatures that are powering GravityZone, our cutting-edge security engine.
While basic anti-virus and endpoint protection tools rely on traditional signature-based approaches, they are ineffective against unknown or zero-day attacks. In contrast, Bitdefender utilizes advanced algorithms and techniques that go beyond traditional methods. We also consider system and user behavior, which can indicate suspicious activities.
For Bitdefender MDR customers, an additional layer in the security chain is in place to protect them. In addition to the standard Bitdefender protection layers, our SOC analysts create custom detection rules that facilitate deeper investigation of suspicious activities. Analyzing these activities helps uncover potential malicious incidents within the environment. Human analysts triage and investigate these events, and if they reach critical levels, the customers are notified or an incident is escalated.
Bitdefender MDR analysts often conduct some level of threat hunting and investigation of customer environments that proactively identify other kinds of suspicious or unknown activity beyond detections. While these investigations may not always result in a security incident, at the very least they can often turn into a security advisory to a customer based on a configuration issue, for example, or to confirm certain services or applications running in the environment. This activity contributes to understanding the customer’s environment baseline, which often helps tune signatures by reducing the noisy alerts from false positives.
Finally, the Bitdefender MDR team occasionally comes across newly emerging threat campaigns that were previously unknown. In these instances, our team proactively develops intelligence hunt packages to address the defensive gaps until appropriate detections can be implemented. To track and monitor these campaigns, we utilize a range of intelligence tools, including internal Bitdefender resources, third-party threat feeds, and open-source investigations.
Ransomware Report
Spear phishing attacks are often used as an initial attack vector and ransomware infection is often the final stage of the kill chain. For this report, we analyzed malware detections collected in April 2023 from our static anti-malware engines. Note: we only count total cases, not how monetarily significant the impact of infection is. Opportunistic adversaries and some Ransomware-as-a-Service (RaaS) groups represent a higher percentage compared to groups that are more selective about their targets, since they prefer volume over higher value.
When looking at this data, remember these are ransomware detections, not infections.
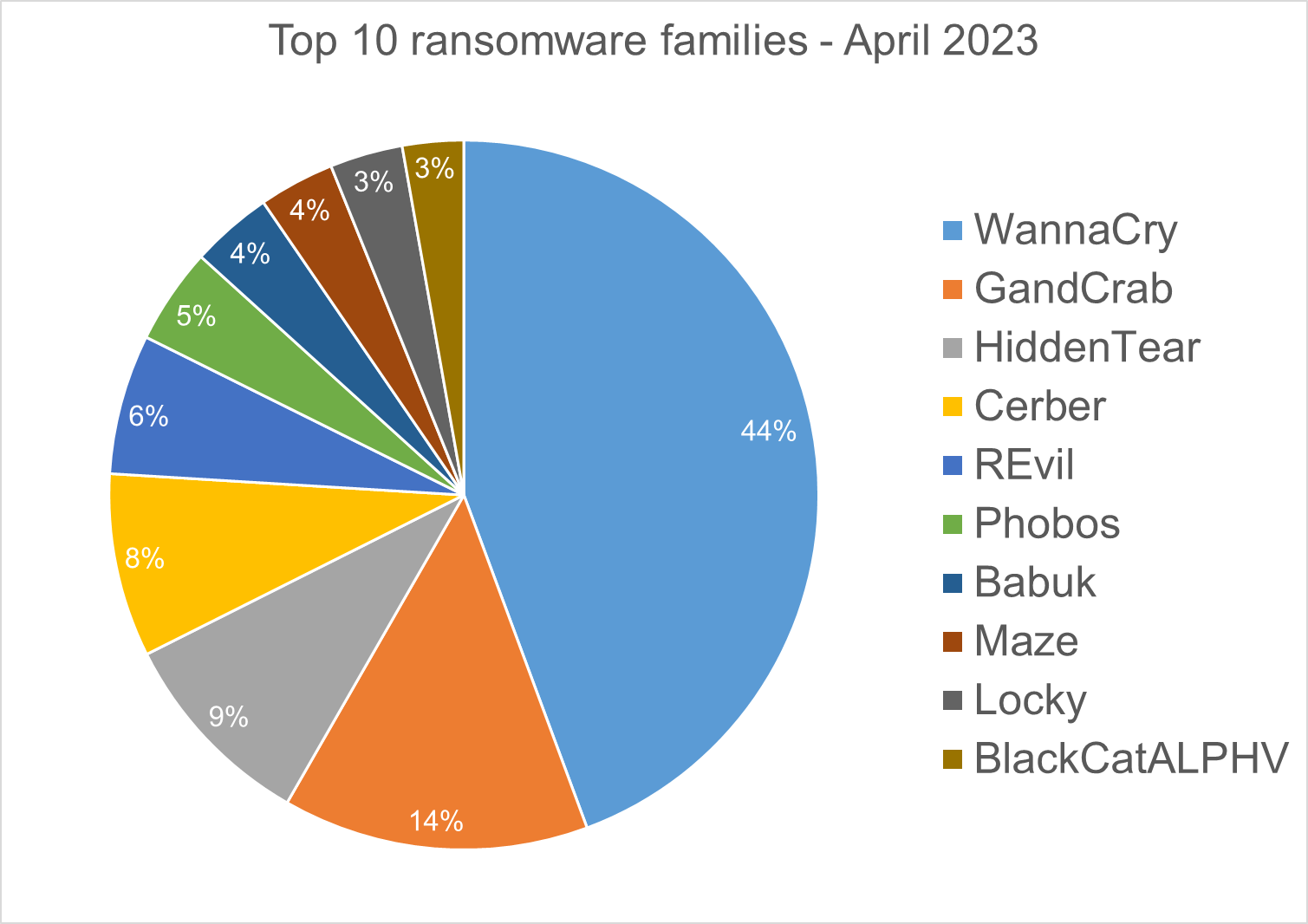
Top 10 Ransomware Families
We analyzed malware detections from April 1 to April 30. In total, we identified 231 ransomware families. The number of detected ransomware families can vary each month, depending on the current ransomware campaigns in different countries.
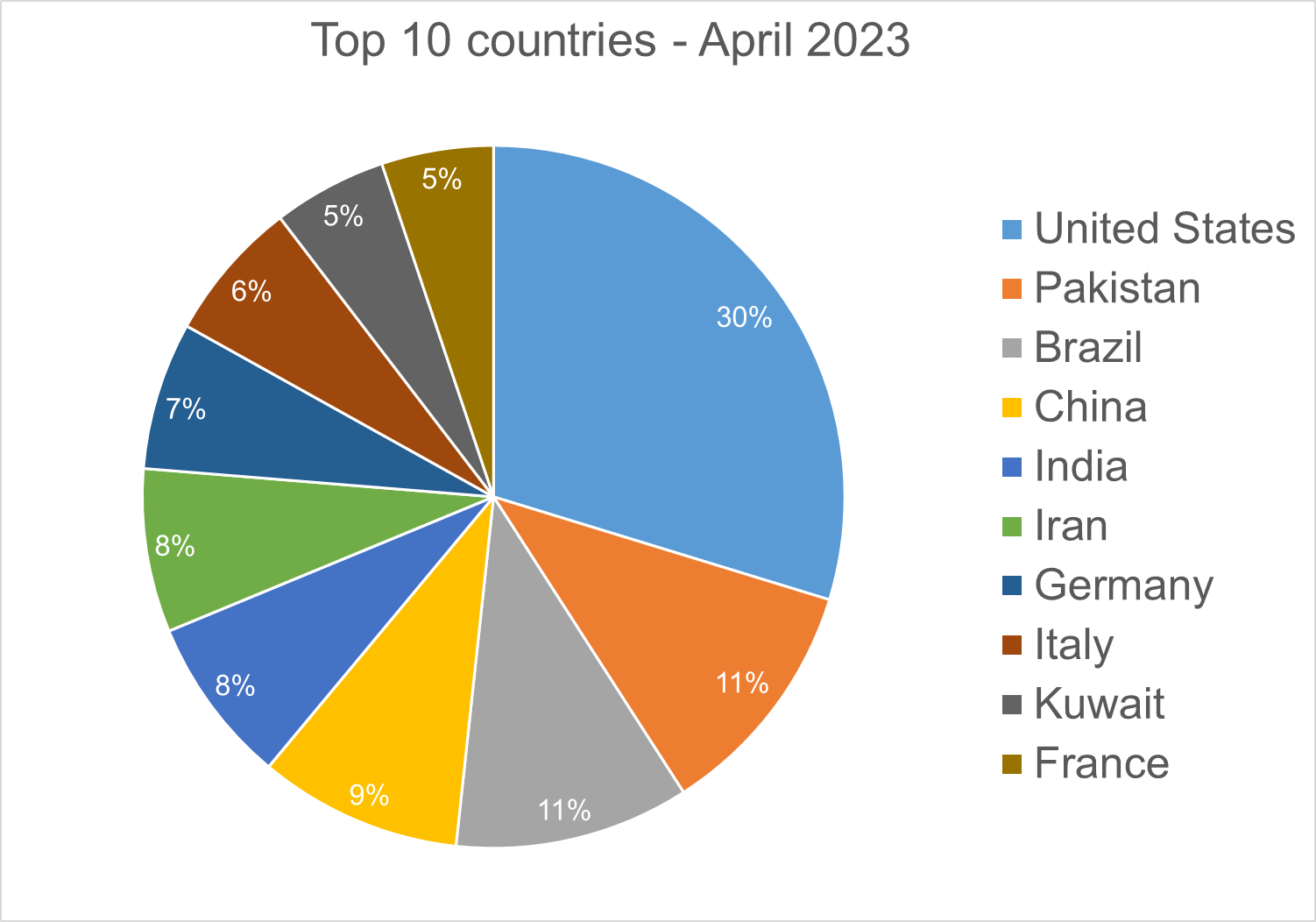
Top 10 Countries
In total, we detected ransomware from 127 countries in our dataset this month. Ransomware continues to be a threat that touches almost the entire world. Below is a list of the top 10 countries most impacted by ransomware. Many ransomware attacks continue to be opportunistic, and the size of population is correlated to the number of detections.
Android trojans
Below are the top 10 trojans targeting Android we have seen in our telemetry during April 2023.
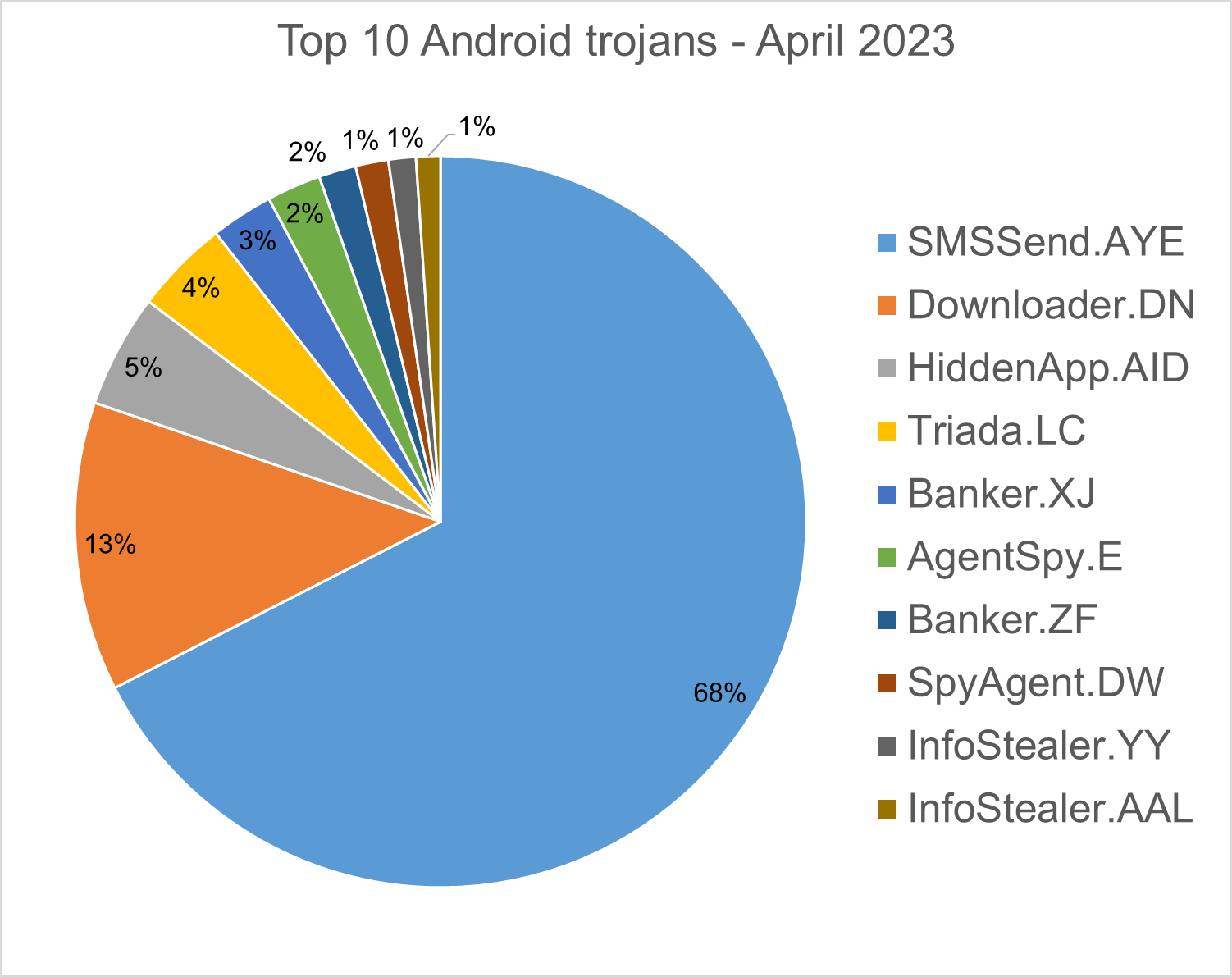
SMSSend.AYE - Malware that tries to register as the default SMS application on the first run by requesting the consent of the user. If successful, it collects the user's incoming and outgoing messages and forwards them to a Command & Control (C&C) server.
Downloader.DN – Repacked applications taken from Google App Store and bundled with aggressive adware. Some adware downloads other malware variants.
HiddenApp.AID - Aggressive adware that impersonates AdBlock applications. When running for the first time, it asks permission to display on top of other apps. With this permission, the application can hide from the launcher.
Triada.LC – Malware that gathers sensitive information about a device (Device IDs, Subscriber IDs, MAC addresses) and sends them to a malicious C&C server. The C&C server responds by sending back a link to a payload that the malware downloads and executes.
Banker.XJ - Applications that drop and install encrypted modules. This trojan grants device admin privileges, and gains access to manage phone calls and text messages. After deploying, it maintains a connection with the C&C server to receive command and upload sensitive information.
AgentSpy.E - Applications that were taken from Google Play Store and re-packed with malware. The malware packages are obfuscated, with the primary objective of stealing personal data.
Banker.ZF - Applications that disguise themselves as banking apps and can imitate conversation with customer support. When the malware runs for the first time, it asks for permissions to access contacts, microphone, geolocation, and camera. Once the permissions are granted, the malware can receive commands from the C&C server to exfiltrate sensitive data from the phone.
SpyAgent.DW - Applications that exfiltrate sensitive data like SMS messages, call logs, contacts, or GPS location.
InfoStealer.YY - Remote Administration Tool for mobile devices that allows an attacker to take control of a victim's device without needing root access. Once the malware is installed on the phone, the attacker can carry out various attacks that compromise the confidentiality and privacy of the victim's data. The tool has the ability to capture the screen content, stream live video from the phone's cameras, upload and download files from the device, track the user's location and even capture authentication credentials from Facebook and Google platforms.
InfoStealer.AAL - This application is like InfoStealer.YY, but doesn’t have the ability to capture authentication credentials. It is a different family of Remote Administration Tools.
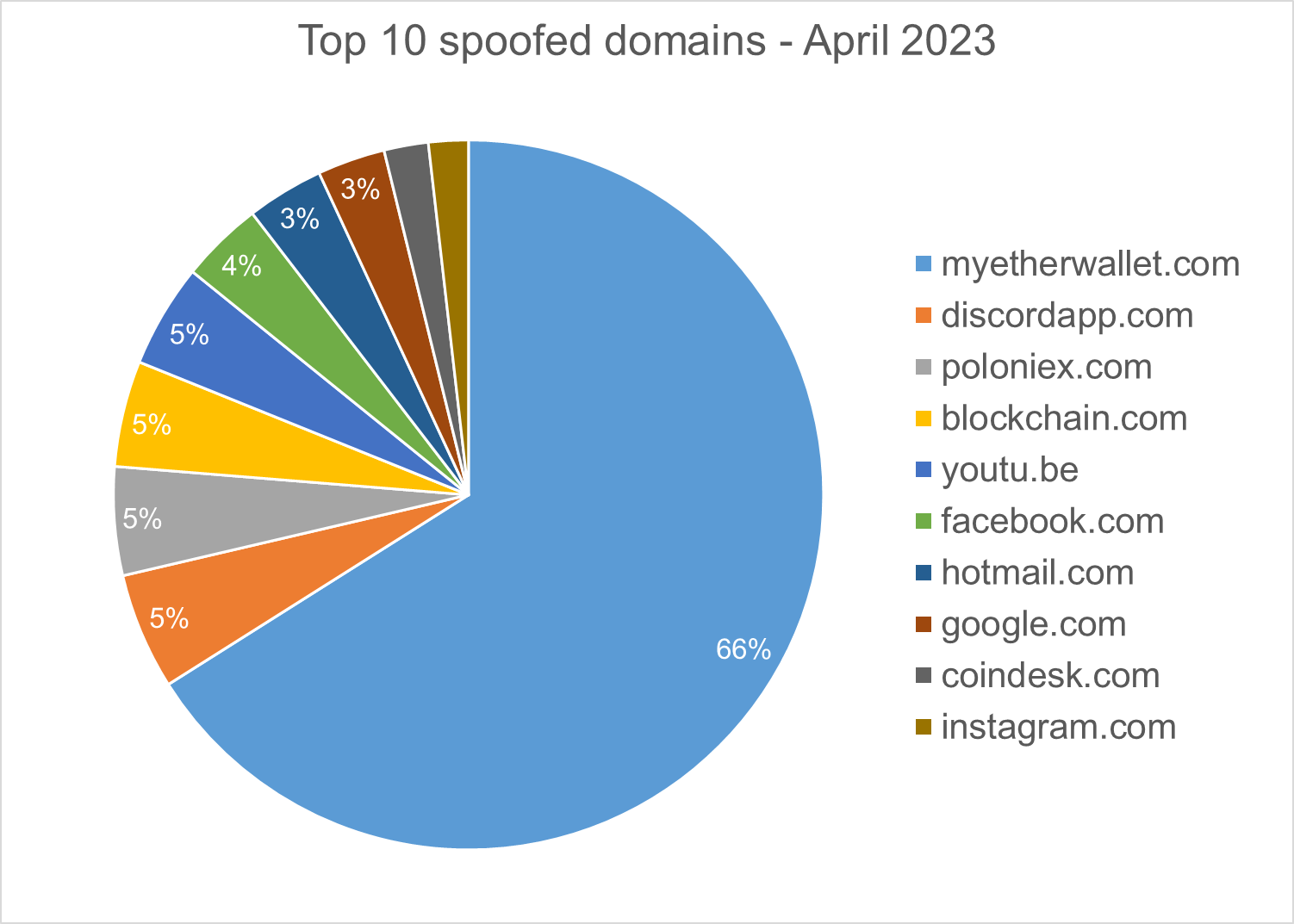
Homograph Phishing Report
Homograph attacks work to abuse international domain names (IDN). Threat actors create international domain names that spoof a target domain name. When we talk about “target” of IDN homograph phishing attacks, we refer to the domain that threat actors are trying to impersonate. You can read more about this type of attack in one of our previous reports.
Below is the list of the top 10 most common targets for phishing sites.
About Bitdefender Threat Debrief
The Bitdefender Threat Debrief (BDTD) is a monthly series analyzing threat news, trends, and research from the previous month. Don’t miss the next BDTD release, subscribe to the Business Insights blog, and follow us on Twitter. You can find all previous debriefs here.
Bitdefender provides cybersecurity solutions and advanced threat protection to hundreds of millions of endpoints worldwide. More than 150 technology brands have licensed and added Bitdefender technology to their product or service offerings. This vast OEM ecosystem complements telemetry data already collected from our business and consumer solutions. To give you some idea of the scale, Bitdefender Labs discover 400+ new threats each minute and validate 30 billion threat queries daily. This gives us one of the industry’s most extensive real-time views of the evolving threat landscape.
We would like to thank bitdefenders Tyler Baker, Alin Damian, Mihai Leonte, Andrei Mogage, Sean Nikkel, Nikki Salas, Rares Radu, Ioan Stan, Marius Tivadar, and Horia Zegheru (sorted alphabetically) for their help with putting this report together.
tags
Author
Martin is technical solutions director at Bitdefender. He is a passionate blogger and speaker, focusing on enterprise IT for over two decades. He loves travel, lived in Europe, Middle East and now residing in Florida.
View all postsYou might also like
Bookmarks


