Netflix Phishing Scams: They’re More Dangerous Than You Think

Cybercriminals are actively targeting Netflix users, trying to trick them into accessing phishing websites and handing over their login credentials. This apparently simple type of attack can have wide-reaching implications, even if it might not be immediately evident.
Key takeaways
- Netflix phishing emails aim to steal login credentials and payment details—not just your streaming account.
- Attackers reuse stolen passwords to break into email, banking, and social media accounts.
- Cybercriminals sell compromised Netflix accounts or bundle them in larger fraud operations.
- These scams rely on a sense of urgency, fear, and the promise of rewards to trick victims into acting quickly.
- One successful case of phishing can lead to identity theft, financial loss, and long-term account compromise.
What is a Netflix phishing scam?
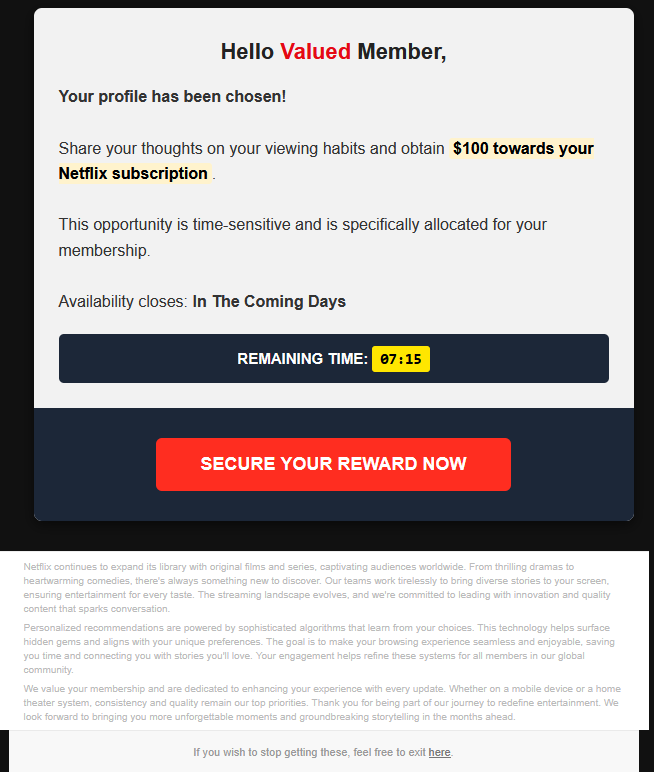
Netflix phishing scams, usually sent via email or SMS, are fraudulent messages built to impersonate the streaming company and trick users into entering their usernames and passwords. These messages often claim you’ve received a reward or warn you of suspicious activity on your account.
It’s either a carrot or a stick, but this type of approach is always a red flag.
They usually arrive disguised as official Netflix messages, complete with branding, logos, and urgent calls to “do something.” But instead of ending up on the Netflix website, the links direct you to fake websites that gather your login credentials and, in some cases, your payment details.
How these attacks trick users
Attackers carefully create these messages to manipulate emotions and force quick decisions.
Some rely on excitement. A message that your profile has been “selected” for a reward, encouraging you to act fast before the offer expires. Others seek to trigger fear, warning that your account will be restricted within 72 hours unless you verify your identity.
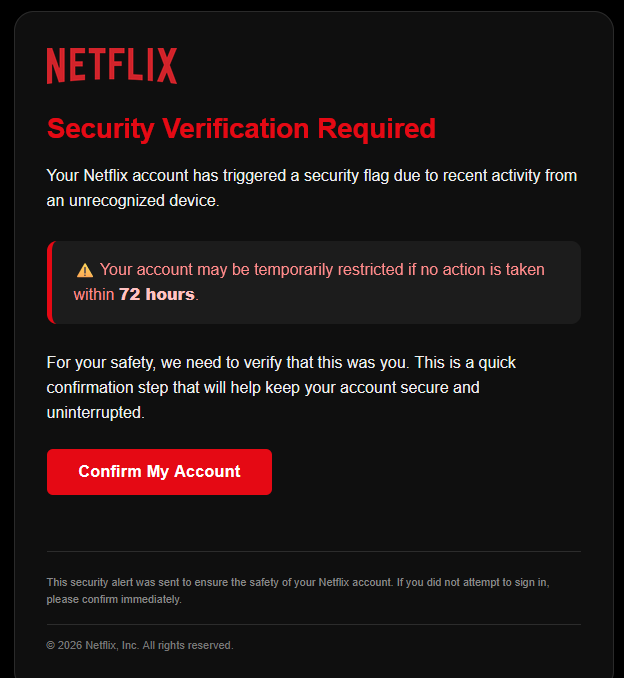
Both approaches rely on the triggers:
- Urgency, through countdown timers or deadlines
- Authority, by impersonating a trusted brand
- Emotion, by exploiting fear or curiosity
Instead of giving you time to think, the messages aim to push you to click immediately.
What happens after you enter your credentials
The problems start the moment you type your credentials into a fake login page.
Attackers instantly capture your email address, your password, and, depending on the type of scam, payment information.
Your Netflix account is just the starting point. It’s not the final target.
Most people reuse passwords across multiple platforms. Hackers take advantage of this by launching automated attacks known as credential stuffing, where they test your stolen login details on other services such as email accounts, banking apps, and online stores.
If the same password works elsewhere, attackers gain access to far more valuable accounts.
Account takeover & resale
After attackers gain access to a Netflix account, they don’t leave it untouched. They typically change the associated email and password within minutes, locking out the legitimate owner. In some situations, they will create a new user to blend with the existing ones.
It’s not uncommon for some users to treat the Netflix account like any other subscription, paying month after month but not really using it. These types of users are the ideal victims.
From there, the account becomes a commodity.
Cybercriminals trade stolen Netflix accounts on underground marketplaces, where they are sold cheaply to buyers seeking discounted access. These accounts are often bundled with other compromised credentials and sold as part of larger “account packages.”

This resale ecosystem turns individual victims into sources of recurring profit. Even if the value of a single account seems low, the scale of these operations lets attackers generate consistent revenue.
Credential stuffing attacks
Credential theft is only the first step. The real escalation happens when attackers automate the reuse of stolen credentials across hundreds of platforms.
This technique, known as credential stuffing, is based on the assumption that people reuse their passwords. Statistically, around 20% of users reuse the same password across multiple online accounts.
Using automated tools, attackers test the same email-password combination on services such as payment platforms, e-commerce sites, corporate VPNs and more.
There’s also the real danger of losing your Netflix password and letting attackers into your company's infrastructure because you used the same password.
Even if just a small percentage of these attempts succeed, attackers gain access to significantly more valuable accounts. In some cases, a single phishing incident can cascade into a full digital identity compromise.
Financial fraud
If attackers obtain payment details directly from the scam campaign or gain access to accounts linked to financial information, the impact becomes all too real very quickly.
The attackers can initiate unauthorized transactions, purchase goods or services or exploit stored payment methods for recurring charges. In more sophisticated schemes, the stolen financial info is sold on underground markets or used in laundering operations.
Malware & secondary payloads
Not all phishing campaigns stop at credential theft. Some introduce another layer of risk by delivering malware. Depending on the scam and the messages used, criminals can persuade some victims to download dangerous software, like fake security tools, for example.
These tactics shift the attack from account compromise to device-level attack. With malware on the device, attackers gain persistent access, monitor user activity, or capture additional sensitive data.
How to Protect Yourself from Netflix Phishing
The most effective defense starts with skepticism.
- If an email pressures you to act quickly or promises an unexpected reward, pause before clicking anything. Instead of using the link provided, open Netflix directly in your browser or app and check your account from there.
- Use a unique password for Netflix and every other service. This single step can stop credential stuffing attacks from spreading beyond one account.
- Enable two-factor authentication wherever possible, especially for your email account. Since your email acts as the central hub for password resets, protecting it significantly reduces your risk.
- Finally, keep your devices secured with a reliable security solution, such as Bitdefender Total Security, that can block phishing websites and detect malicious activity before it causes harm.
FAQ
How can I tell if a Netflix email is a phishing scam?
Answer: Check the sender address, links, spelling, and tone. Netflix phishing emails often use urgent language, unexpected rewards, fake security warnings, or buttons that lead to suspicious domains instead of the official Netflix website.
What happens if I click a Netflix phishing link?
Answer: Clicking the link may take you to a fake Netflix login page designed to steal your email, password, and sometimes payment details. In more dangerous cases, the link may also lead to malware or fake verification tools.
What should I do if I entered my Netflix password on a fake website?
Answer: Change your Netflix password immediately, then change the password on any other account where you reused it. Check your payment details, review recent account activity, and secure your email account first because attackers can use it to reset other passwords.
Can hackers use stolen Netflix credentials on other accounts?
Answer: Yes. Attackers often use credential stuffing tools to test stolen Netflix usernames and passwords on email, banking, shopping, cloud, and workplace accounts. Password reuse can turn one phishing incident into a much larger compromise.
Why do cybercriminals target Netflix users?
Answer: Netflix has a large global user base and strong brand recognition, which makes phishing messages more convincing. Attackers use Netflix as bait to steal credentials, access higher-value accounts, resell accounts, or collect data for future fraud.
What do attackers do with stolen Netflix accounts?
Answer: They may change the login details, lock out the real owner, sell the account on underground markets, or bundle it with other stolen credentials. In many cases, the Netflix account is only the first step toward broader fraud.
How can I protect myself from Netflix phishing scams?
Answer: Avoid clicking links in unexpected Netflix emails. Go directly to the Netflix app or website to check your account. Use unique passwords, enable two-factor authentication where available, protect your email account, and use security software that can detect phishing pages.
tags
Author
Silviu is a seasoned writer who followed the technology world for almost two decades, covering topics ranging from software to hardware and everything in between.
View all postsYou might also like
Bookmarks


