What Is Your Digital Footprint?
When is the last time you searched for your name online?
This is the first step to take if you want to find out more about your digital footprint.
The next one is to use the methodical approach below to see your online presence through the eyes of Bitdefender cybersecurity experts. Here's how to stay up to date with security best practices and how to manage your online identity for extra privacy.
As you think about your digital footprint, keep these 3 things in mind:
- It is most likely bigger than you realize.
- You cannot use the Internet or any connected device without leaving a trace.
- There is always something you can do to manage, limit, and protect your exposure.
What Is a Digital Footprint?
An accurate digital footprint definition includes the volume of information you create by using the Internet for any kind of activities that can be traced to your unique identity. You can find the same concept under the name of “digital shadow”, “digital fingerprint” or “digital dossier.”
Your digital footprint includes all the actions you perform on Internet-connected devices, through your online accounts and independent of them. More broadly, the perception that your actions create on the Internet also contributes to your digital footprint.
That is why your instinct may be to worry about your reputation when wondering what people can find about you online. Even if it is not an accurate representation, your digital footprint is tied to your way of life. It is natural to be concerned about the impression you make, because reputation influences our social ties, our place in society and our growth prospects. The same applies to organizations, no matter if they are private or public.
“Every click you made, every site you visited, every social media post you published, every email you sent, anything you shared online or information about you that others posted on the Internet - that is your digital footprint.”
Liviu Arsene (Senior E-threat Analyst, Bitdefender)
Having a digital footprint combines both risks and benefits. Here’s how you can increase its positive impact.
What Does Your Digital Footprint Look Like?
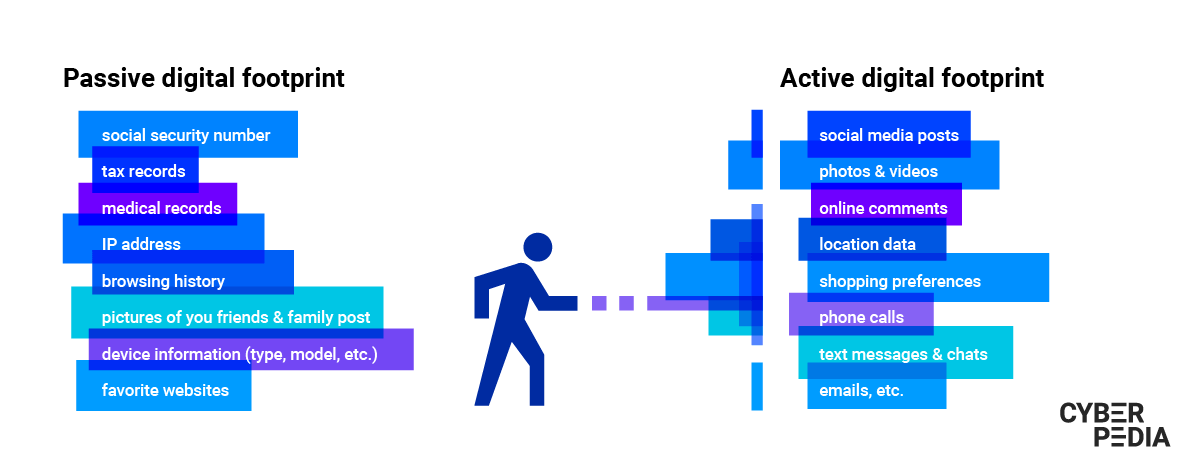
There are 2 major types of digital footprint you create: a passive one and an active one. And you have more control over just one of them.
What Is a Passive Digital Footprint?
Everything you “touch” on the Internet forms your passive digital footprint. This is the data you unintentionally leave online (also called metadata) and it includes:
- Your IP address (which also reveals your location)
- The details of the device you are using (model, version etc.)
- The websites you visit (your browsing history)
- Your actions on these websites (how many times you have visited, pages you spent the most time on, buttons and links you clicked)
- The kind of browser you are using and its version (also called a browser fingerprint)
- Your search queries
- Your online purchases - and more.
The passive aspect comes from the fact that you are not intentionally leaving this data behind. It is a combination of data about the systems you use and your online behavior.
You have limited control over your passive digital footprint, even if it was created with your consent (generally, each website or app has terms and conditions you have to agree to in order to use it).
For example, once a website has details about your activity, they can use them based on the terms of service you agreed to. They may use your IP address to automatically display the website content in your native language. Or they can use your browser cookies to target you with ads for the products you looked at the longest.
“Even if you don’t have an online social media account, even if you haven’t personally uploaded any personal information online, that doesn’t mean it’s not there.”
Liviu Arsene (Senior E-threat Analyst, Bitdefender)
Now let’s look at the part you have a lot more control over.
What Is an Active Digital Footprint?
On top of the data you produce passively, there is also your digital activity, the information you choose to share over the Internet. Combined with your digital identity, this creates your active digital footprint.
Every email you send, online form you fill, video you upload and person you connect to on social media adds to the personal data you intentionally expose on the Internet.
These active data traces build up over time and paint an increasingly accurate picture of your identity, belongings, preferences, history, and lifestyle - including your relationships. Whether they have an active digital footprint or not, the people in your life also add to your digital shadow.
“The more information we disclose outside of our trust circle, the more likely it is to land in the wrong hands.”
Bogdan Botezatu (Director of Threat Research and Reporting, Bitdefender)
Realizing the level of detail that forms your active digital footprint can be overwhelming.
A wave of revelations flooded the media when the EU General Data Protection Regulation gave individuals the right to access the data companies have on them. Many could not believe their entire online activity was stored as messages, calls, searches, preferences, pictures, videos and other details that documented their entire life. This reality defied their perception of being the sole owners of their data.
Recently, an analysis of Bitdefender’s Digital Identity Protection community revealed the worrying volume of personal data that exposed most users:
“Only 19.48% of users have between one and five data entry points exposed online, including a home address, names, usernames, emails and job titles. 20.20% of users have between six and 12 data entry points made public. For the remaining 57.49%, more than 12 data entry points are exposed, with 16.13% of users having more than 50 instances of personally identifiable information on display in the virtual world.”
Your passive and active digital footprints can be – and frequently are – linked together. Consequently, the effect of your online persona overflows into your offline life. This also works the other way around.
At this point, you are probably wondering what kind of effort would be reasonable to invest in protecting your digital footprint. We will help you do a cost-benefit analysis so you can decide what is worth protecting and how far you want to go for it.
Some Examples of Digital Footprints
|
Online shopping digital
footprint |
Social media digital
footprint |
Citizen digital footprint |
Smartphone digital
footprint |
Your network’s digital
footprint |
|
Email address Address Phone number Credit card details Your product search history Most frequently bought items Average shopping basket value Most browsed products Products you’re likely to buy & more |
All your posts Photos & videos (including deleted ones) Messages you sent/received Files you shared/received Phone contacts Email address Address Phone number Type of content you consume Favorite topics Most clicked ads & more |
Social security number Address Phone number Medical records Tax records Bank accounts Household composition & family
relationships Real estate ownership records Criminal record Fingerprints Age Ethnicity |
Photos & videos Contacts Fingerprints and/or facial features Location data, including history Apps you run List of contacts List of phone calls Text messages Downloaded files Passwords Shopping list Notes |
Posts, pictures and videos you’re tagged in Relationships (significant others, close
family and other relatives, friends, etc.) Messages Groups or group chats Video calls Emails Shared accounts Their online searches on shared devices |
By combining these data points - and many others - organizations build your profile with high accuracy.
The same applies to both the public and private sectors. Most importantly, the same profiles are targets to a range of actions designed to influence you for a multitude of agendas - intuitive or well disguised.
Why Should You Care About Your Digital Footprint?
For two main reasons that are bound to get even stronger as technology evolves.
First, once you put a piece of information online, it can be difficult – or even impossible – to remove. Second, your digital footprint offers a roadmap for those who seek to influence you, defraud you or harm you in any way.
We see this every day: cyber-criminals constantly collect and corroborate information from data breaches, publicly available data and active attacks that enhance digital footprints. The more accurate their understanding of victims and their context, the better they can maximize their chances for success.
Malicious actors are not worried about legal implications. Instead, they are highly motivated to capture and monetize as much of the data they have on as many people as possible.
Your digital footprint is often a more detailed and accurate reflection of your thoughts, emotions and behaviors than you realize. To understand this is to learn how to manage it, protect it and keep yourself safe from harm.
What Are the Risks of Having a Digital Footprint?
How Your Digital Footprint Impacts Your Work
While background checks may not be standard everywhere, online searches and reviewing social media profiles are.
Potential employers look at your digital footprint and try to identify off-putting signs that you may not be fit for the job. They can include details such as:
- Compromising pictures and videos
- Sensitive content shared on public profiles
- Attitude towards former employers (including complaints and insults)
- Use of profanity in online posts and public comments
- Public references to alcohol or illegal drug consumption
- Signs of prejudice or aggressive behavior - and more.
Depending on your role and industry, even bad spelling and grammar can raise a flag.
Your digital footprint does not just influence your job prospects. Your current employer is most likely keeping an eye on things as well. There are plenty of examples of people who got fired because their past online actions were deemed inappropriate.
The more important your role in the company is, the stronger the impact of your digital footprint. The same goes for the company itself, as your employer’s digital reputation can also influence yours.
How Your Digital Footprint Impacts You at Home
As someone with tech know-how and a privacy-oriented mindset, you can make a big difference in the lives of your loved ones.
The examples, explanations and support you provide can significantly improve their safety – online and offline. Vulnerable categories such as children and the elderly are especially susceptible to scams and cyber-attacks.
Before buying a new device or service, consider how they contribute to your digital footprint and theirs. See what you can do to minimize that from the beginning.
For example, IoT devices exponentially increase the volume of data associated with your online persona. Details such as your body temperature, heartbeat, sleep patterns, teeth brushing habits, the map of your home and its surroundings - all flow from IoT devices and into companies’ servers. Often 24/7.
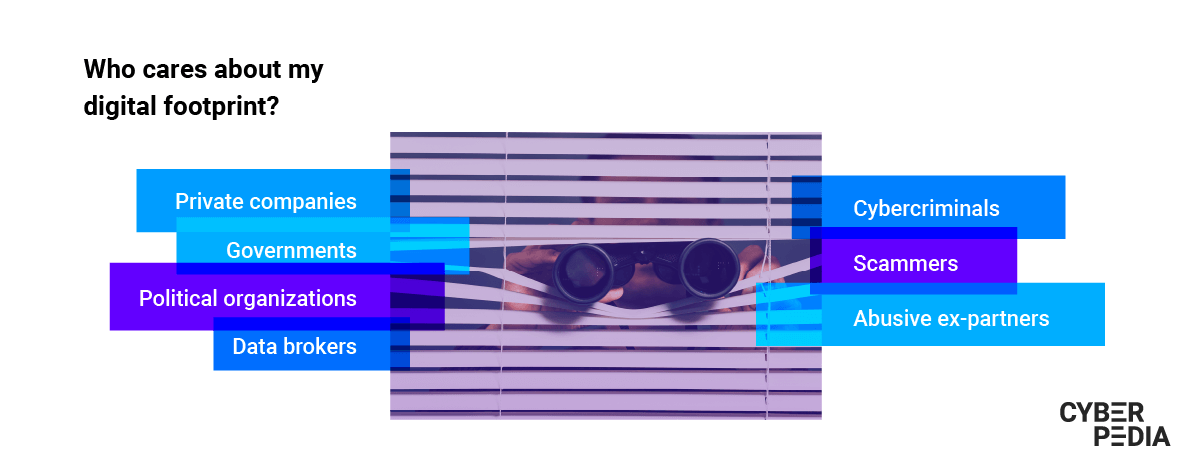
Who Stands to Gain from Your Digital Footprint?
It is very difficult to see the connection between your digital trail and how others use it for their interests. Organizations, including cyber-criminal ones, use it to influence your behavior to their advantage.
There are some aspects you can notice directly, such as article suggestions or personalized advertising based on your previous searches. Frustratingly, the bulk of how your digital footprint is captured, analyzed and used happens in the background. And it never stops.
There are various categories of actors who stand to gain from investing (billions) in this:
- Private companies that want to nudge buyers to spend more
- Governments that seek to monitor and control citizens, sometimes in abusive ways
- Political organizations that aim to influence voting preferences and the larger political decisions they generate
- Data brokers that focus on getting as much data as possible so they can sell a more accurate profile for a higher price
- Cybercriminals that harvest digital footprints to target victims with persuasive scams and cyberattacks with the end goal of cashing in big
- Abusive ex-partners who use stalkerware to track victims’ activities and whereabouts so they can continue to harass them.
How Much Should You Worry About Your Digital Footprint?
Ask yourself: “How comfortable am I with what my digital footprint says about me?”
If your mind jumps to a particular set of items you want to delete, clean up or remove from the public domain, then trust your instinct.
It is also useful to remember this: as you go through life, your needs and interests may change.
Sometimes, aspects related to our private lives (such as a personal blog or a community) can evolve into a business. It is normal to want to have fun with social media when you are young, but some things you post can cause future trouble. So you have to decide what is worth a potentially hefty negative consequence and what is not.
The most important aspect is to acknowledge your digital footprint. Once you are motivated to care about it, it gets easier to find the information you need and spend some time managing it.
Through small, consistent actions, you can set up layers of protection, including in your behavior. The result? Minimizing the risk of a major crisis caused by the trail of data you leave online.
How to Find Your Digital Footprint
You are probably wondering if there is a way to check your digital footprint. All of it. At the same time.
Fortunately, there is!
Bitdefender Digital Identity Protection monitors your digital footprint starting with an email address and phone number. It automatically finds your private information in online legal and illegal collections of data and even checks if your personal details have been exposed on the Dark Web. Plus, you get instant alerts for new breaches and privacy threats so you can act quickly to limit their impact.
With this solution as part of your toolkit, you can also start to map as much of your digital footprint as you can see and understand. Next off, clean up your essential accounts and improve your privacy and security settings.
You can even go as far as to ask for your data to be removed. Ethical operators will most likely de-link, hide, or delete that information, but unethical ones can go as far as extorting you to take the information down. Situations range from authors of negative reviews asking for money to take down the critique to much more harmful forms of blackmail.
Eager to act on what you just learned? Check out our practical guide on managing your digital footprint and follow the steps and recommendations.
tags
Author
Choose what the experts use. Award-winning cybersecurity you can trust and rely on.
View all posts

