Bitdefender Threat Debrief | February 2024

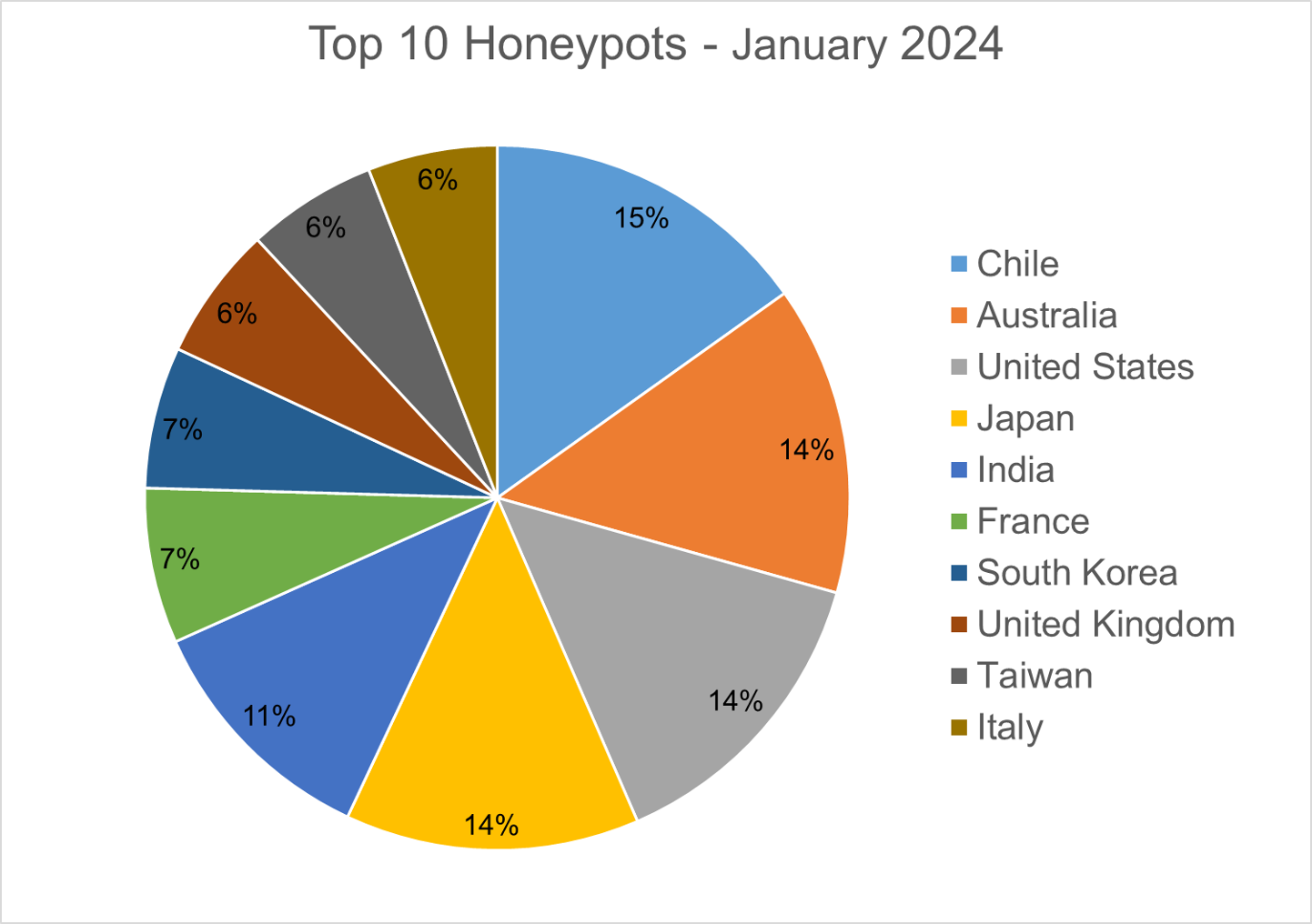
This month’s Bitdefender Threat Debrief introduces an exciting new wrinkle: the Honeypots Report. A honeypot is a system or network intentionally designed to attack and detect malicious activity. Think of them as decoy systems crafted to attack and analyze cyber threats. In our report, we focus solely on destination countries, not source countries. While we have access to this data, its relevance is limited, given that the majority of attacks are linked to virtual workloads running in the cloud, designed to conceal the identity of the actual attackers.
This month’s edition also features a change in the Homograph Report. Previously, it included all detections from our telemetry, with one site consistently dominating the report for months. To enhance accuracy, we've now refined the report by filtering only active and online domains. This tweak helps to enhance the accuracy of the report by filtering out detections that, while valid, don't contribute significantly to its overall usefulness.
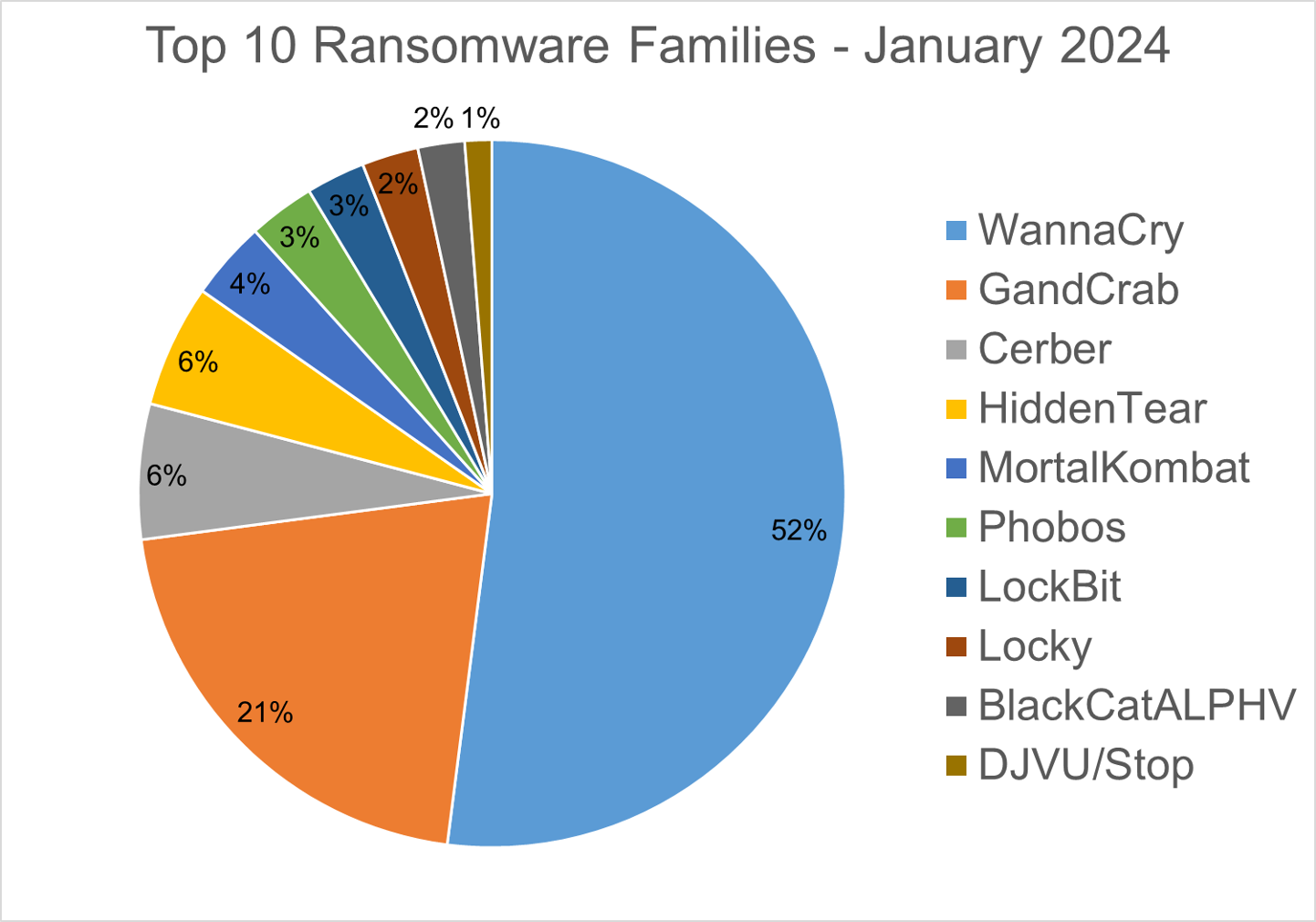
Ransomware Report
For this report, we analyzed ransomware detections collected in January 2024 from our static anti-malware engines. Note: we only count total cases, not how monetarily significant the impact of infection is. Opportunistic adversaries and some Ransomware-as-a-Service (RaaS) groups represent a higher percentage compared to groups that are more selective about their targets since they prefer volume over higher value.
When looking at this data, remember these are ransomware detections, not infections.
Top 10 Ransomware Families
We analyzed malware detections from January 1 to January 31. In total, we identified 194 ransomware families. The number of detected ransomware families can vary each month, depending on the current ransomware campaigns in different countries.
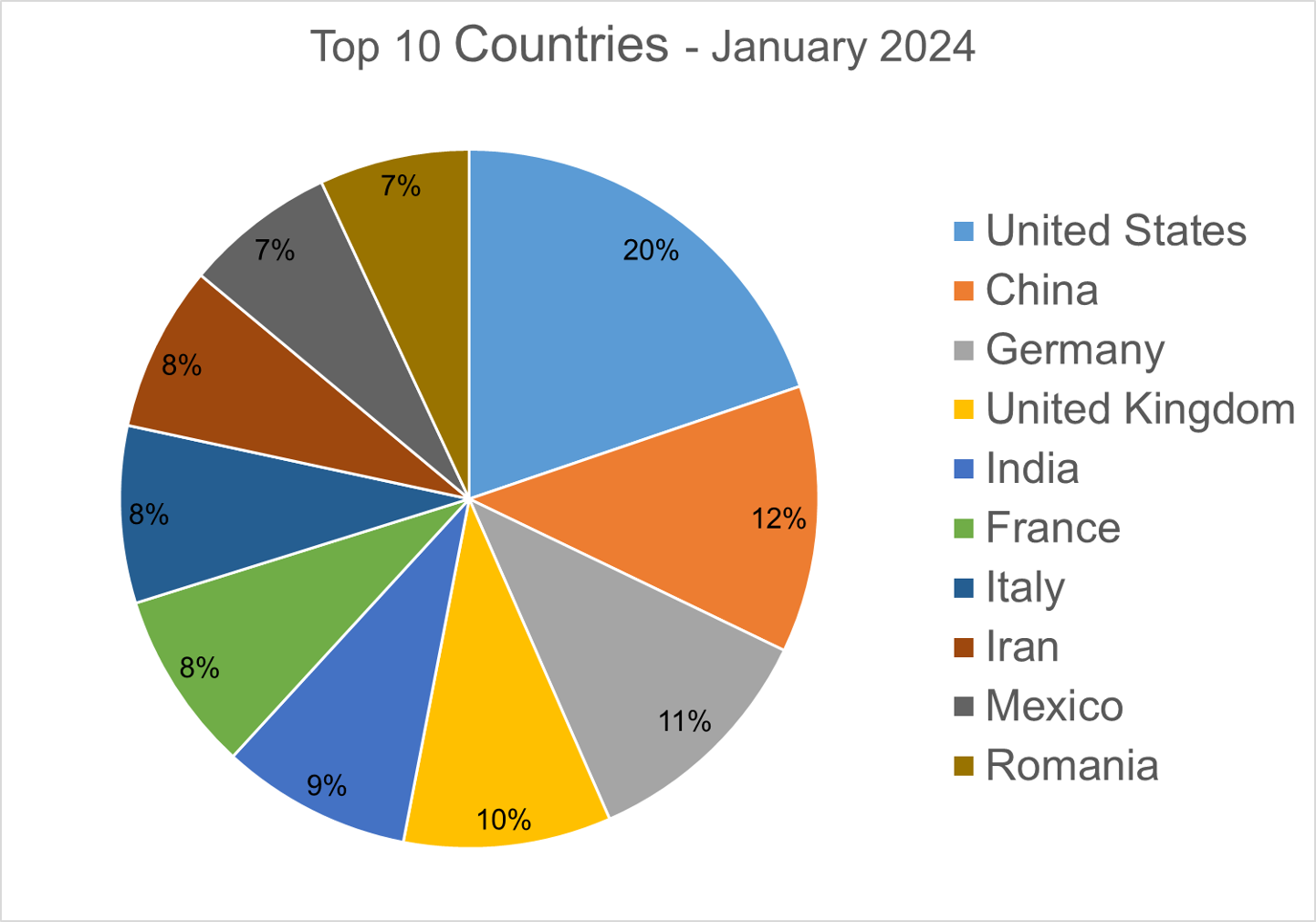
Top 10 Countries
In total, we detected ransomware from 138 countries in our dataset this month. Ransomware continues to be a threat that touches almost the entire world. Below is a list of the top 10 countries most impacted by ransomware. Many ransomware attacks continue to be opportunistic, and the size of a population is correlated to the number of detections.
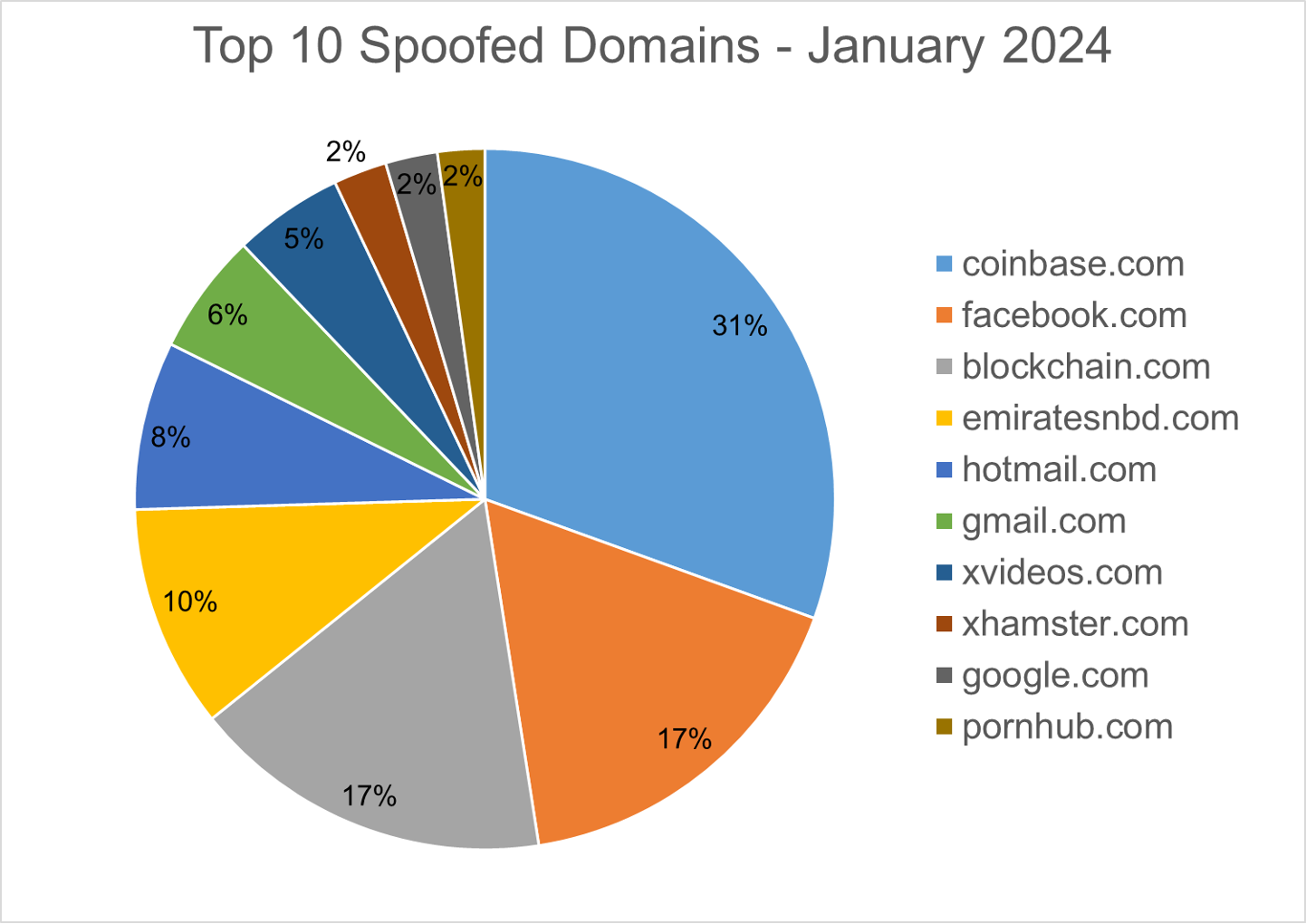
Homograph Phishing Report
Homograph attacks work to abuse international domain names (IDN). Threat actors create international domain names that spoof a target domain name. When we talk about the “target” of IDN homograph phishing attacks, we refer to the domain that threat actors are trying to impersonate. You can read more about this type of attack in one of our previous reports.
Below is the list of the top 10 most common targets for phishing sites.
Honeypots Report
Honeypots are a system or network intentionally designed to attract and detect malicious activity. Essentially, a honeypot is a decoy that is set up to lure attackers and study their methods, tactics, and techniques.
In our report, we focus solely on destination countries, not source countries. While we have access to this data, its relevance is limited, given that the majority of attacks are linked to virtual workloads running in the cloud, designed to conceal the identity of the actual attackers.
Here is a list of the top 10 countries where our honeypots were triggered:
Android Trojans Report
Below are the top 10 trojans targeting Android we have seen in our telemetry during January 2024. Android trojans refer to malicious software programs specifically designed to target Android operating systems. These trojans disguise themselves as legitimate applications but contain harmful code that can compromise the security and privacy of the device they infect.
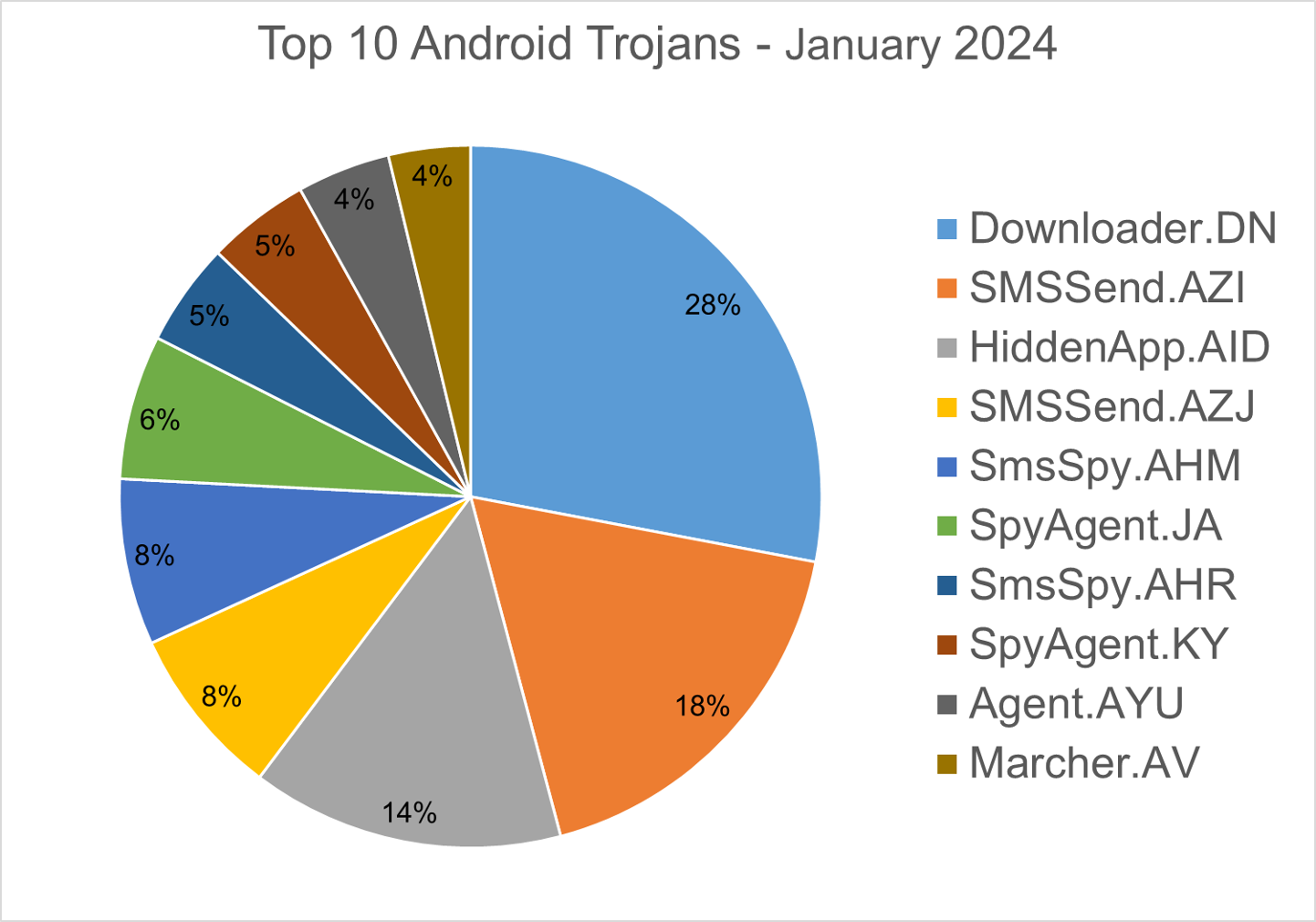
Downloader.DN – Repacked applications taken from the Google App Store and bundled with aggressive adware. Some adware downloads other malware variants.
SMSSend.AZI - Detect backdoor applications that execute malicious commands, enabling the theft of data from infected systems. These backdoors also can send SMS messages, potentially enabling SMiShing, or texting premium numbers to generate revenue via SMS fees.
HiddenApp.AID – Aggressive adware that impersonates adblock applications. When running for the first time, it asks permission to display on top of other apps. With this permission, the application can hide from the launcher.
SMSSend.AZJ – Detects applications that collect personal information and transmit it to Telegram via a chatbot. Afterward, a displayed message prompts the user to transfer funds to a designated bank card number.
SmsSpy.AHM– Detects applications that collect information about incoming and outgoing SMS messages, as well as the user's location, and then sends this data to a remote server.
SpyAgent.JA – Malware that collects personal data like user messages and contacts, allowing access to the compromised device's camera and microphone. This enables malicious individuals to secretly monitor infected users.
SmsSpy.AHR– Detects applications that intercept incoming SMS messages and send them to a remote server.
SpyAgent.KY– Detects obfuscated applications that monitor SMS messages and calls, utilize the camera API to record and send videos from the device's camera to a command & control server.
Agent.AYU - Detects popular instant messaging apps that are repackaged with a spyware module. After establishing a connection with a C&C server, it can receive instructions to record audio, upload device data (such as contacts), or upload requested files.
Marcher.AV– Applications that disguise themselves as Play Store applications. The malware tries to ask for accessibility permissions to capture keystrokes, and also uses the VNC screen recording function to log user’s activity on the phone.
About Bitdefender Threat Debrief
The Bitdefender Threat Debrief (BDTD) is a monthly series analyzing threat news, trends, and research from the previous month. Don’t miss the next BDTD release, subscribe to the Business Insights blog, and follow us on Twitter. You can find all previous debriefs here.
Bitdefender provides cybersecurity solutions and advanced threat protection to hundreds of millions of endpoints worldwide. More than 150 technology brands have licensed and added Bitdefender technology to their product or service offerings. This vast OEM ecosystem complements telemetry data already collected from our business and consumer solutions. To give you some idea of the scale, Bitdefender Labs discover 400+ new threats each minute and validate 30 billion threat queries daily. This gives us one of the industry’s most extensive real-time views of the evolving threat landscape.
We would like to thank bitdefenders Alin Damian, Mihai Leonte, Andrei Mogage, Silviu Sofronie, Rares Radu, Ioan Stan, Marius Tivadar, and Horia Zegheru (sorted alphabetically) for their help with putting this report together.
tags
Author

Martin is technical solutions director at Bitdefender. He is a passionate blogger and speaker, focusing on enterprise IT for over two decades. He loves travel, lived in Europe, Middle East and now residing in Florida.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks







