What is Online Privacy? And Why is it Important?

What does online privacy mean to you?
If you find it difficult to come up with a definitive answer when asking yourself the question, you are not alone. But there is an easier way to figure this out.
Find out what online privacy is and why it is worth your time and attention - directly from Bitdefender cybersecurity experts.
What Is Online Privacy? A Definition
The standard definition of privacy incorporates two important elements: “the state of being alone and not being watched or interrupted by other people.”
When you are by yourself, scrolling through your go-to social media app, you are physically alone. However, you are also “watched or interrupted by other people.” While they may not be in the same room, you are still a number on a screen for someone. On top of that, you are constantly interrupted by ads that interfere with your videos, articles, and browsing.
Although this situation may feel private, it is not.
That is why the definition of online privacy covers your natural (and justified) expectation to have your personal data protected and your behavior not tracked when you are connected to the Internet. At least not without your explicit consent.
But what exactly does “personal data” include? Let’s find out.
What Is Personal Data?
According to the General Data Protection Regulation (GDPR), “personal data is any information that relates to an identified or identifiable living individual. Different pieces of information, which collected together can lead to the identification of a particular person, also constitute personal data.”
Online privacy is deeply rooted in our fundamental need for safety. If you find it natural to protect your home and physical belongings, the same applies to your digital life. No matter what technology you use (or do not), privacy gives you control over your identity and all the things it is made of.
But because things are not as palpable or visible to everyone, online privacy is not on the priority list for most people. Moreover, the complex technological, legal, commercial, and social combo does not make online privacy easy to achieve. However, it does make it essential.
"It’s not just the way we interact with the Internet, it’s also the way the world interacts with us. For instance, we’re shopping somewhere, maybe in a mall or at the corner shop, and our face and voice get actively recorded by surveillance cameras. This information is also stored and processed in a way that we cannot oppose, which makes things even worse."
Bogdan Botezatu (Director of Threat Research and Reporting, Bitdefender)
Is Online Privacy a Myth?
So if simply connecting to the Internet involves some form of tracking or surveillance, is online privacy a myth?
Because privacy is not considered a standard in our connected world, it may appear so. But for those who believe in this right, online privacy is achievable. Not everywhere and not all the time but when and where it matters the most.
Every time you sign up for a new app or make a purchase, you agree with a set of terms and conditions. Your agreement means organizations can legally collect information about you such as what you buy, which websites you visit, and your preferences related to a wide range of topics. Although this type of personal data collection is legal, it does not mean you cannot take steps to limit these privacy invasion tactics.
Online privacy exists and it is up to each and every one of us to make it the norm instead of the exception.
Why Is Online Privacy Important?
To do something about your online privacy, you first have to believe it is worth it.
Online privacy is involved in everything from how technology evolves to how this evolution impacts your personal safety and security. The real, “offline” dangers that poor online privacy creates include doxing, harassment, extortion, and swatting, to name a few.
Let’s talk about how it affects you personally.
You probably do not want thieves to know you live alone or the exact time you are not home, giving them an opportunity to break into your apartment. You do not want to give scammers a chance to use your date and place of birth and other personal data to take out loans in your name. You also expect cyber-criminals to be stopped before they can trick you into opening malicious emails that install malware which records everything you type.
"We can look at our personal data as something hackers either directly exploit or use as soon as they get a hold of it. It’s also something they can trade with other cybercriminal organizations. So, personal data is commoditized. It has a price. Your medical data, your financial history, your credit card data, your online shopping preferences have a price."
Liviu Arsene (Senior E-Threat Analyst, Bitdefender)
Take a moment to list your most important online accounts. They may include your online banking account, your email address, and your favorite social media platform.
Now try to list the types of information they have about you. You don’t have to look far, just start with your social media profiles! You probably shared your phone number and contacts, email, your place and date of birth, where you work, where you went to school, and your relationship status.
This is an opportunity to evaluate whether the trade-off between your privacy and the benefits you get by using that service is still fair. Remember you can revoke their rights at any time, even if you have been comfortable using a product or a service until now.
Internet privacy is important because it gives you control over your identity and personal information. Without that control, anyone with the intention and means can manipulate your identity to serve their goals, whether it is selling you a more expensive vacation or stealing your savings.
What you post on social media, what you write about in the comments section of websites, and how well you protect your data also influence the people closest to you, whether it’s family, friends, or colleagues (your boss included!).
That is why everything you do for your own privacy also has a positive impact on others.
Examples of Threats to Your Online Privacy
The things that chip away at your privacy on the Internet are both big and small. They also add up. Let’s review the most frequent issues that consistently reduce your safety online.
Weak, Reused Passwords
At some point or another, we all used weak passwords. Maybe you still do. It is not uncommon. But it is, however, one the biggest threats to your privacy.
Reusing weak passwords is one of the leading causes for the massive data breaches you see in the news. That is because it allows cyber criminals to break into multiple accounts at once and engage in identity theft or financial fraud - often both.
Oversharing
Social media and other technology advancements have made it incredibly easy to share every aspect of our lives to expand our social ties. Oversharing is a consequence of that which often goes unnoticed because so many people do it.
Oversharing gives malicious onlookers more information about you than you would ever want to divulge. Posting videos of your home gives them a full map of your belongings and how to get to them. Pictures of your boarding passes reveal how long you will be gone and where you are traveling. With every post, you create a clearer picture of your life, habits, key relationships, and possessions.
IoT Devices
Another threat to your online privacy: all the Internet-connected devices that are constantly listening, recording, and gathering data about you.
Our shopping lists, our body temperature, the contents of our fridge – we have been producing this personal data for years, but no one has been interested in it before. Now we have connected toothbrushes, toasters, and TVs all over the place.
IoT devices are easy to use, and they keep getting better and better, increasing the risks to your online privacy on the way.
Unsecured Web Browsing
The browser is probably the app you use the most on your devices - consciously or not. Each time you open a link or run an online search, your default browser is one of the main ways you connect to the Internet. You may even have let it remember your passwords.
Cyber-criminals know that too! And they’re going after everything in it through malicious extensions, infected ads, links that lead to scam websites, and a lot more.
Security and privacy risks usually come as a combo. Besides cyber-crooks and scammers, companies can also build an accurate profile of you based on your browser history.
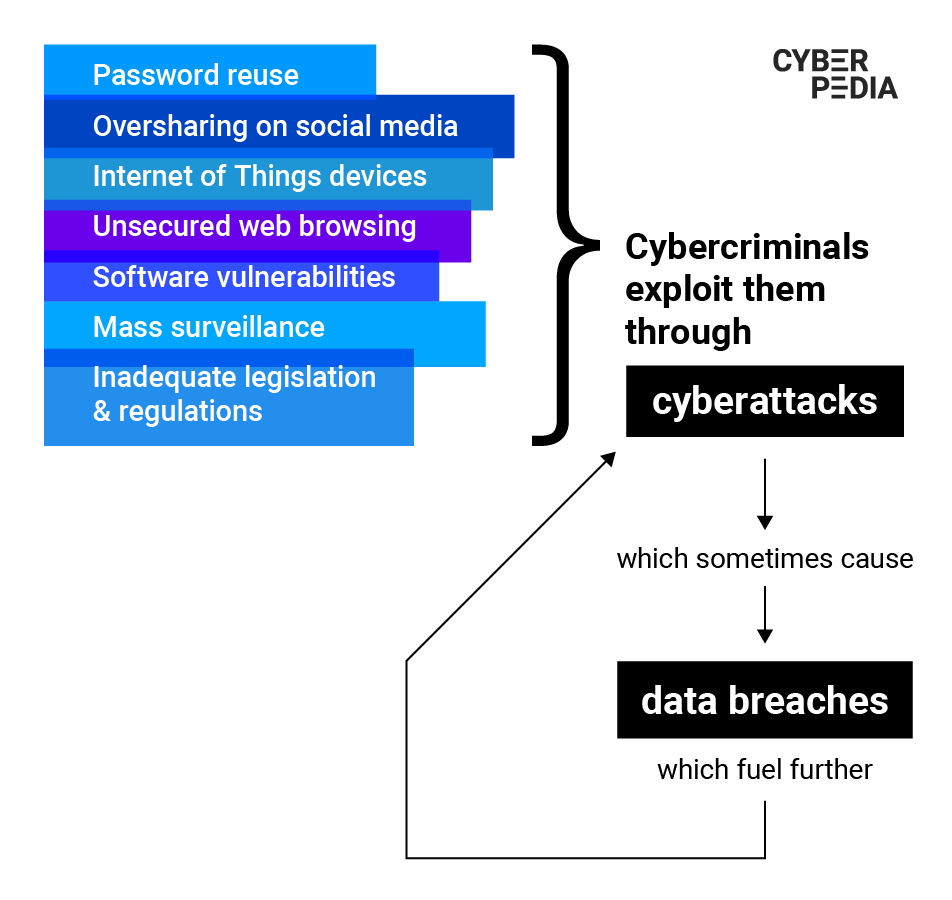
Security Vulnerabilities
It is not just your habits and the mechanisms of the platforms and devices you use that weaken your privacy on the Internet. Security vulnerabilities also create massive issues. They range from data breaches, where a set of your personal data ends up in publicly accessible places online, to security issues that make devices… misbehave.
Security vulnerabilities leak data that hurts not only your personal privacy online but also that of millions of users which weakens the overall security level for all of us.
“There are two ways people usually find out their information was exposed online. They either read the news and discover that a service provider or a company they use has been breached and some of their personal information may have been leaked online. Or, if it doesn’t make the news, they sometimes get an email from the breached company notifying them that <Hey, there’s been a breach. Your personal information may have been affected.>”
Liviu Arsene (Senior E-Threat Analyst, Bitdefender)
Cyber-Attacks
Your online privacy has everything to do with your security on and off the Internet.
Relying on default settings for everything and using the simplest passwords you can set makes you an easy target for cyber criminals.
Malicious hackers combine their tech skills with psychological manipulation to exploit your habits and preferences so that you will click, tap, download, and open their traps.
They bait you into opening deceiving emails (phishing), taping links in misleading messages on your phone (smishing), or even provide personal data in fake phone calls (vishing). Their attacks almost always include malicious software designed to capture everything you type on your device (keyloggers) and collect your usernames and passwords. They will later use them against you to steal your money, access confidential information, or simply make your life hell.
“The information we have might be trivial for us. We all know where we live, what our date of birth is, what shopping history we have and so on. But aggregated, this information depicts a very, very complex and accurate overview of what our lives look like. And most of the time, we cannot revoke the access we have already granted to organizations.”
Bogdan Botezatu (Director of Threat Research and Reporting, Bitdefender)
Anyone can become a target. Most ongoing cyber-attacks are automated and simply search for people with unprotected accounts, apps, and devices, which are easy to hack into and maliciously exploit.
What Can You Do Next?
Now that you have a solid grasp of what online privacy is and what threatens it, you can take meaningful steps to reclaim it and protect it.
One of the first things you can do is set up an early-warning system that patrols the Internet for you. Bitdefender Digital Identity Protection helps you take control of your online privacy and personal data so you can take decisive action when something pops up on its radar. The service monitors your digital footprint starting with just your email address and phone number and alerts you if your personal data is leaked in new breaches and through privacy threats, including social media impersonators.
With this automatic and constant scanning keeping watch for you, you can now work to build your own privacy-protecting ecosystem.
tags
Author
Choose what the experts use. Award-winning cybersecurity you can trust and rely on.
View all posts

