Who installs Zoom apps outside the Play Store? Well, lots of people.

Video conferencing platform use has skyrocketed as people turn to remote work and e-learning, and Zoom has witnessed a tremendous surge in popularity. This popularity, though, has brought increased scrutiny that has revealed several issues with the platform and prompted big tech companies to ban the use of Zoom for business purposes.
We have written about fake Zoom applications floating outside the Google Play Store, and we were wondering if these binaries ever make it onto the devices of real victims. This led us to an important question: where do people download the Zoom client when they are about to start a meeting for the first time?
The answer should be straightforward: from the official site or Google Play. The official Zoom page even suggests a download of the Android version from Google Play.

The link takes you to the official Google Play page. However, our telemetry data shows something bizarre. People are not downloading Zoom from Google Play.
Starting January 1st this year, we have identified over 100,000 out of 750,000 cases where people have downloaded the Zoom application from places other than Google Play. That is, over 10% of users are risking their safety by downloading Zoom binaries from unofficial sources.
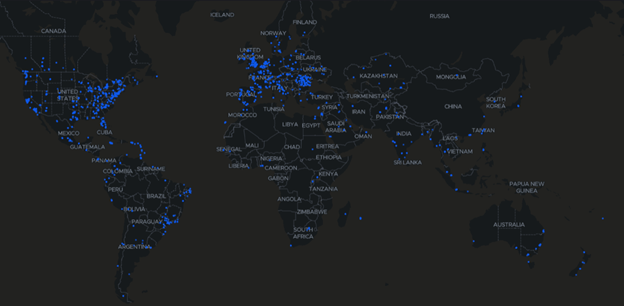
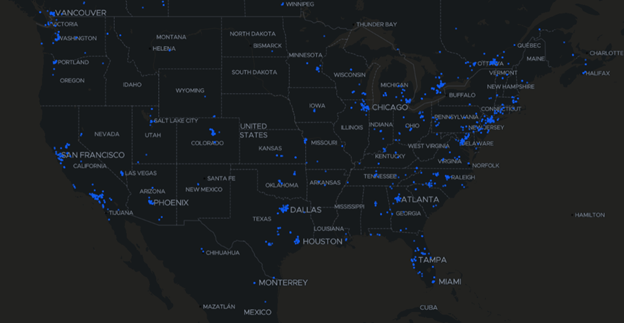
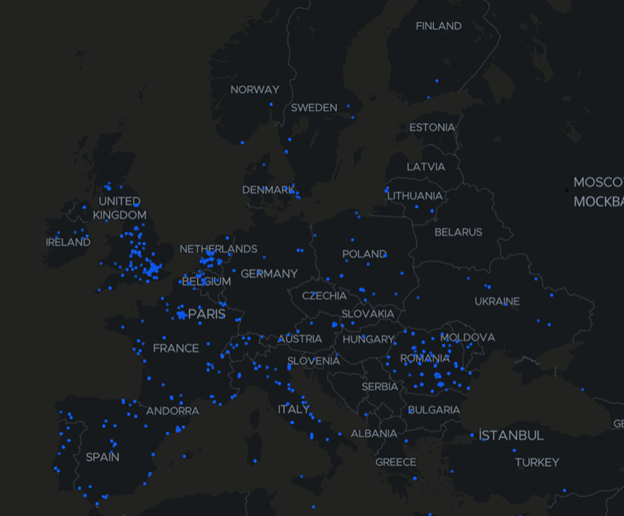
We bet China came to mind, didn’t it?
This is alarming. And it’s not restricted to a remote corner of the world – it’s a widespread phenomenon. As demonstrated in our previous blog post, malware authors do take advantage of this.
We can only extrapolate from this that people are confused as to where to download Zoom, so they resort to Google searches which might take them to third-party markets or other unofficial (read risky and questionable) distribution points.
So, how can we know whether an APK is installed from a third-party or from a sanctioned market? The answer is simple: we look at the file paths of specific scanned binaries that have the fingerprints of known Zoom APK versions. A simple query in our threat intelligence repository shows the following file paths and binary occurrences for official Zoom binaries.
| Zoom download path | Download count |
| /Download/zoom.apk | 91077 |
| /Android/data/com.android.chrome/files/Download/zoom.apk | 925 |
| /ZOOM.APK | 810 |
| /UCDownloads/zoom.apk | 369 |
| /Download/zoom-us-zoom.apk | 218 |
As expected, the vast majority of these binaries are generically saved to the Download folder. Other custom downloader software usually have their own dedicated download folders, as do Google Chrome (/Android/data/com.android.chrome/files/Download/zoom.apk ) and UC Browser (/UCDownloads/zoom.apk).
This situation brings another important observation. As shown in the maps above, this behavior is not isolated to China, where sideloading is normal. This is a global phenomenon, confirmed in North America, South America and Europe. Users who cannot access Google Play to download Zoom seem to resort to third-party markets such as aptoide.
I happen to have a spare Zoom installer just lying around here somewhere
Zoom installers don’t just get downloaded via search. They’re also passed along via WhatsApp, SHAREit or Verizon’s content transfer application. This behavior is seen even in business or enterprise environments, where Zoom installers are passed from employee to employee via WhatsApp Business.
| Application | File paths |
| X-Transfer – Share/Backup Files/Contacts/SMS/Calls | /Documents/X-Transfer/385395/1584429256/Apps/Zoom.apk |
| WhatsApp Messenger | /WhatsApp/Media/WhatsApp Documents/zoom.apk |
| /WhatsApp Business/Media/WhatsApp Business Documents/Private/zoom.apk | |
| /WhatsApp/Media/WhatsApp Documents/zoom-us-zoom.apk | |
| SHAREit – Transfer & Share | /SHAREit/apps/Zoom.apk |
| Verizon Content Transfer | /Download/vztransfer/apps/Zoom.apk |
If you’re paranoid about cyber-security, you probably realize how bad this “pass me the Zoom app” looks. One does not usually say “Pass me that Zoom installer, would you? I have a meeting in a few and I don’t know where to get it”.
Acquiring the Zoom installer this way leaves users even more vulnerable to being manipulated into installing tainted Zoom APK files that have Remote Access Trojan functionality.
Stay safe and install Android apps from official sources only. Always install a security solution on your Android device.
tags
Author
Right now Top posts
Infected Minecraft Mods Lead to Multi-Stage, Multi-Platform Infostealer Malware
June 08, 2023
Vulnerabilities identified in Amazon Fire TV Stick, Insignia FireOS TV Series
May 02, 2023
EyeSpy - Iranian Spyware Delivered in VPN Installers
January 11, 2023
Bitdefender Partnership with Law Enforcement Yields MegaCortex Decryptor
January 05, 2023
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks













