Bart Ransomware Decryption Tool Released; Works for All Known Samples

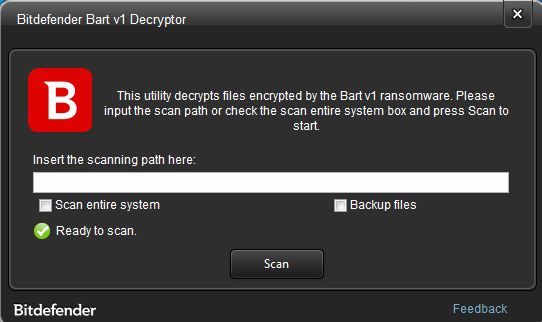
The Bart ransomware that encrypts machines without an internet connection has been analyzed by Bitdefender researchers, and victims can now download the Free Bart Ransomware Decryption Tool to recover their lost data.
While the ransomware was first spotted in the wild in July 2016, Bitdefender is the only security vendor to offer a decryption tool for all Bart ransomware samples. The Bart Ransomware Decryption Tool can decrypt files with the “.bart.zip”, “.bart” and “.perl” extension, and will also be available for download from the “No More Ransomware” website starting April 4 2017.
The tool is a direct result of successful collaboration between Bitdefender, Europol and Romanian police, supporting the “No More Ransom” initiative kick started by Europol’s European Cybercrime Centre.
Bart in a Nutshell
Unlike other ransomware families, Bart can encrypt a victim’s files without any internet connection. However, the decryption process does require an internet connection to access the attacker-controlled C&C (Command and Control) server, to transfer bitcoins and receive the decryption key.
While the first iterations of Bart included rudimentary encryption capabilities, such as creating password-protected .zip archives, other interactions have dropped this method.
Here’s how Bart works:
- Deletes system restore points
- Generates a seed to create an encryption key using information from the victim’s machine
- Enumerates files and encrypts them with the generated key
- Uses a master key to encrypt the key used to encrypt the files (this becomes the victim’s unique id – UID)
- Displays ransom note and redirects to a .onion website (the URL contains the victim’s UID)
Ransomware in Context
Losses from ransomware globally have surged to an estimated $1 billion, affecting average users and companies. With almost half of victims paying fees ranging from $300 to $500, according to a Bitdefender survey, ransomware-on-demand or ransomware-as-a-service have boosted its proliferation considerably. Conservative statistics from the US government estimate that ransomware attacks increased by 300 percent in 2016 from 2015, indicating even more ransomware in 2017.
Neither security companies nor the FBI encourage victims to give in to ransomware demands and pay the fees, as there’s no guarantee they’ll actually receive the decryption keys and they’ll only fuel other cybercriminal activities and offer funding for new ransomware developments.
tags
Author
Liviu Arsene is the proud owner of the secret to the fountain of never-ending energy. That's what's been helping him work his everything off as a passionate tech news editor for the past few years.
View all postsYou might also like
Bookmarks
