Trezor's Twitter account hijacked by cryptocurrency scammers via bogus Calendly invite

This isn't the kind of thing you expect to see posted on the official Twitter account of Trezor, the well-known cryptocurrency wallet manufacturer.
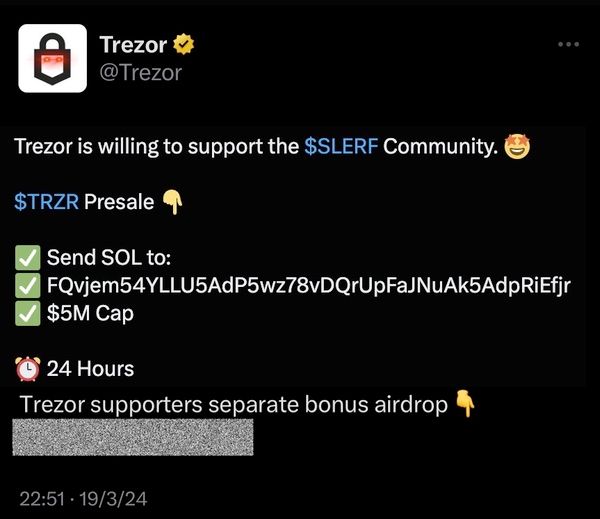
It's a fairly blatant attempt to dupe unwary cryptocurrency fans into transfering digital currency into the wallet of a scammer.
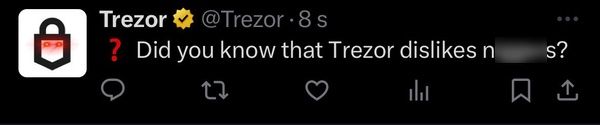
And whoever hacked Trezor's Twitter account didn't limit themselves to just posting a scam. They also tweeted a highly offensive message.
Trezor quickly deleted the unauthorised tweets, and posted a warning to its 205,000 followers.
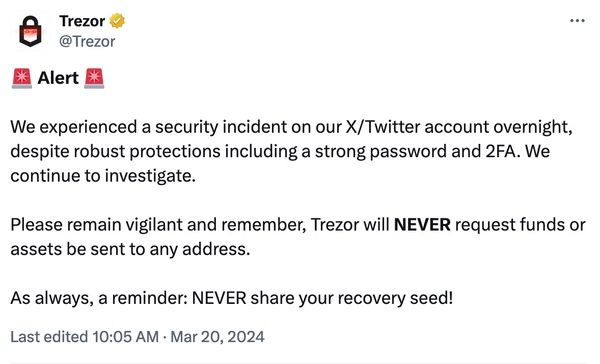
In a subsequent blog post, Trezor explained how its Twitter account had been compromised - despite the firm having sensible security precautions in place, such as strong passwords and multi-factor authentication.
According to Trezor, someone posing as "a credible entity from the crypto space", using a Twitter account with thousands of followers, approached its PR team on February 29, 2024. The imposter asked to interview Trezor CEO Matej Zak.
After several days of "credible back-and-forth communication", the attacker shared what appeared to be a Calendly invite link.
The scam link purported to be a way of scheduling a meeting via Calendly, but ultimately took Trezor's PR worker to Twitter instead, which asked them to enter their login credentials.
Sensing something was wrong, Trezor's team stopped without endangering their Twitter account.
Later, the attackers made another successful attempt to break into Trezor's Twitter account.
Feigning "technical issues", and a desire to reschedule the meeting, someone at Trezor was socially engineered into approving the authorisation request from the bogus Calendly app to connect with the official Trezor Twitter account.
Attackers could now use the fake Calendly app to post fraudulent tweets via Trezor's Twitter account.
Trezor emphasised to customers that it was only its Twitter account that was compromised by the security incident:
We want to stress here that the security of all our products remains unaffected. This incident has in no way impacted or compromised the security of Trezor hardware wallets or any of our other products. Your Trezor device and Trezor Suite remain safe to use.
Nonetheless, it's not a good look for the firm to have its Twitter account exploited by cryptocurrency scammers and posting racist slurs.
Be cautious when third-party apps request access to social media accounts. I've had my own personal experience of my Twitter account being exploited by hackers via a rogue third-party service.
Trezor says that it revoked all active sessions (kicking out anyone with access to the Twitter account) as well as deleting the unauthorised posts, and prevented further access by revoking third-party apps.
This isn't the first time that a phishing scam has made the rounds, duping firms into clicking on fake Calendly links.
For instance, in January The Verge reported that a scammer had posed as one of its journalists and pretended to be using Calendly to schedule interviews with targets - all in order to drain cryptocurrency wallets.
In the same month, a scammer posed as another journalist and successfully tricked blockchain security outfit CertiK into believing they were scheduling a meeting via Calendly. The scammer then succeeded in seizing control of the firm's Twitter account to post a malicious link.
Sadly, it isn't the first time that Trezor has fallen foul of cybercriminals.
In April 2022, Trezor users received a highly-convincing warning that the company had suffered a security breach, and that their cryptocurrency wallets might be compromised.
It later emerged that cybercriminals had hijacked control of Trezor's MailChimp-run newsletter to send out the warning. The warning attempted to trick users into downloading a malicious bogus version of Trezor Suite.
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsYou might also like
Bookmarks
