Take Your QNAP NAS Offline! DeadBolt Ransomware Locks Devices via Alleged Zero-Day Flaw
A new ransomware strain is targeting the seemingly ill-fated QNAP customer base, locking users out of their NAS devices and the data stored on them. The attacks seem to be leveraging a zero-day flaw in the products.
QNAP Network Attached Storage (NAS) devices have been a lucrative target for ransomware strains like QLocker and Ch0raix (aka QNAPCrypt). Now a third – and apparently new – ransomware strain is targeting the already battered QNAP NAS community. It’s called DeadBolt and it hijacks the NAS’s actual operating system to display its ransom note at login.
An onslaught of DeadBolt victims took to the QNAP forums and Reddit to share their stories. A common (mis)configuration, as one might expect, was Internet access and improper remote-access restrictions.
QNAP recently published a comprehensive checklist of configurations to keep ransomware actors at bay. However, that checklist now seems useless – at least when it comes to this new threat.
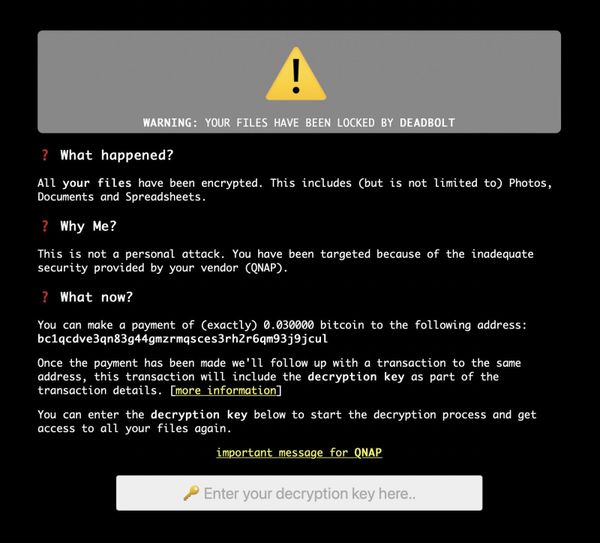
BleepingComputer shares a screenshot depicting the actual DeadBolt ransom note, which reveals that whomever is behind the attacks is likely exploiting a zero-day flaw in QNAP NAS units.
“All your files have been encrypted,” reads the note. “This is not a personal attack. You have been targeted because of the inadequate security provided by your vendor (QNAP).”
The note then directs affected parties to make a 0.03 Bitcoin payment to the attacker’s digital wallet. The note promises that once the payment has been made, the attackers will follow up with the decryption key.
According to at least one victim, paying more than 0.03 in ransom produced an invalid decryption key.
A redditor going by the handle clauderbaugh shares an interesting story of how he dodged the bullet by unintentionally feeding DeadBolt a bunch of useless data and unplugging the NAS before the malware could could get to the important files.
Considering the rapid succession in ransomware attacks on the QNAP user base, NAS owners are strongly advised to keep their gear behind a firewall and completely secluded from the web – at least until QNAP sorts out the vulnerability leveraged by the DeadBolt actors.
tags
Author
Filip has 17 years of experience in technology journalism. In recent years, he has focused on cybersecurity in his role as a Security Analyst at Bitdefender.
View all postsYou might also like
Bookmarks
