Security Researchers Develop New Automated Cold Boot Attack, Extract Encrypted Data from RAM Chips
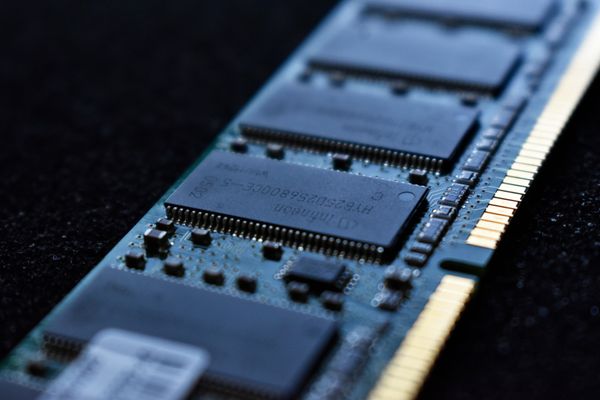
Researchers from Red Balloon Security have developed a groundbreaking technology to forcibly extract encrypted data from DDR3 memory modules, which they will showcase at an upcoming conference.
Led by CEO and founder Ang Cui, along with colleagues Grant Skipper and Yuanzhe Wu, the team has invented a Cryo-Mechanical robot capable of pulling encrypted data out of memory chips.
This marks a significant advancement from previous cold boot attack methods, which have been around since 2008.
The new attack methodology involves freezing a Random Access Memory (RAM) chip, physically extracting the memory from the device, and inserting it into a Field Programmable Gate Array (FPGA) fixture for reading.
This process bypasses manufacturer mitigations such as disabling Joint Test Action Group (JTAG) debugging interfaces and Universal Asynchronous Receiver/Transmitter (UART) circuitry, the use of encrypted firmware, and the use of ball grid array (BGA) packaging.
The RAM extraction robot can automate this process, transforming the manual cold boot attack method into an advanced machine that costs about $2,000.
The first part of the experiment consists of building a machine to freeze the RAM modules using commercial-off-the-shelf (COTS) components, expected to cost "less than a thousand dollars." To efficiently extract the data would require a robot with an FPGA module that automates the process; according to Cui, building this gadget should cost roughly $1,000, "using low-cost hardware that is widely available."
This means threat actors could use the method more widely, raising the stakes for memory security.
The breakthrough will be presented at the upcoming REcon reverse engineering conference in Canada in a presentation titled "Ice Ice Baby: Coppin' RAM With DIY Cryo-Mechanical Robot." Cui will discuss in detail how the extraction process works, its implications, and potential future applications.
This pioneering research underscores the constant evolution of cybersecurity threats and the corresponding need for continuous innovation in data protection measures.
Memory manufacturers and technology developers may need to rethink current security measures to protect our data, considering this new cold boot attack variant.
The importance of such developments serves as a sobering reminder of the lengths to which cyber threats are evolving and the corresponding urgency of developing robust, foolproof security mechanisms.
It also emphasizes the value of events like REcon, which provide a platform for exchanging knowledge and ideas in cybersecurity.
tags
Author
Vlad's love for technology and writing created rich soil for his interest in cybersecurity to sprout into a full-on passion. Before becoming a Security Analyst, he covered tech and security topics.
View all postsYou might also like
Bookmarks


