Outsmarting Connected Devices – A brief history of Bitdefender IoT research
Bitdefender is deeply committed to its mission of protecting the digital world and delivering expert-grade solutions to consumers and companies. That is why, in 2015, we were one of the first information security companies to acknowledge the growing need for safer smart-home equipment.
Making IoT devices safer - a never-ending journey
Motivated by innovation and responsibility to our clients, we assembled a dedicated team of experts, capable of tackling the complex vulnerabilities and challenges of connected devices, and it immediately started getting results.
“One of the scariest (and, unfortunately, extremely plausible) scenarios is a hacker with a backdoor and full access to a smart device that's in your home (or even corporate) network. Could be in your printer, smart light, surveillance camera, and virtually any piece of equipment that has an operating system and is connected. That's why we set off to explore just how plausible this scenario is back in 2015. The results speak for themselves: we found critical vulnerabilities that would enable an attacker to get full control over devices, even without direct connection to the internet in more than 35% of all the Things we analyzed, and medium to high vulnerabilities in about 80%. It's scary. I know. But that's the reality of the IoT Landscape.” - Alex “Jay” Balan – Chief Security Researcher Bitdefender
Fast forward to today, our team is closely monitoring the consumer IoT device market. Since 2015, they have been hard at work testing over two dozen popular IoT devices, publishing numerous whitepapers aimed at helping the community, and teaming up with media partners to address vulnerabilities that could potentially affect millions.
However, our effort does not stop here. From day one we made it our duty to improve device security on a deeper level. This can only be achieved by working closely with IoT device manufacturers and vendors, that is why our research work is never meant to shame or preach. Instead, it is intended to be a constructive conversation starter for the IoT and infosec communities, a cornerstone for safer consumer devices.
Our greatest reward comes when vendors reach out to thank us for our contribution and the way we helped them deliver safer products.
Do smart and safe mix well together?
The IoT universe is expanding at a staggering pace. There were 10 billion connected devices in 2021, and that number is estimated to hit 25 billion units by 2030. On average, a normal household had at least 10 connected devices in 2020 with smart appliances, home automation devices, and IP cameras being the most popular categories among users, according to our study, “The State of IoT Security In 2020”.
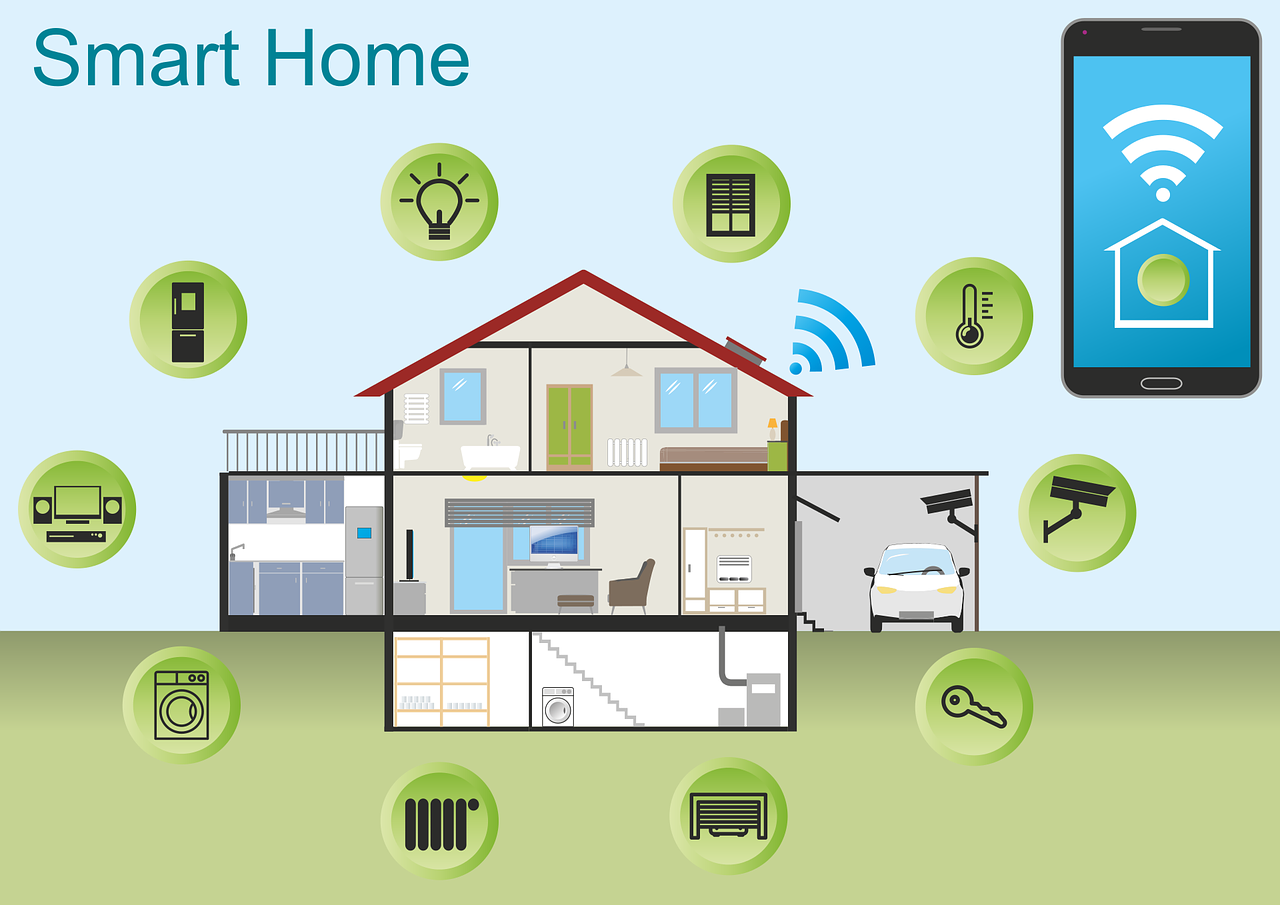
But with such a quick adoption rate, and virtually no technical security requirements, questions started popping up about how safe smart home devices really are.
Is it really that smart to bring all these gadgets into our homes and have them connected to the Internet 24/7? Are all devices equally safe? Can someone else access my devices without me knowing it? Can anyone spy on me through my baby monitor?
Who’s watching?
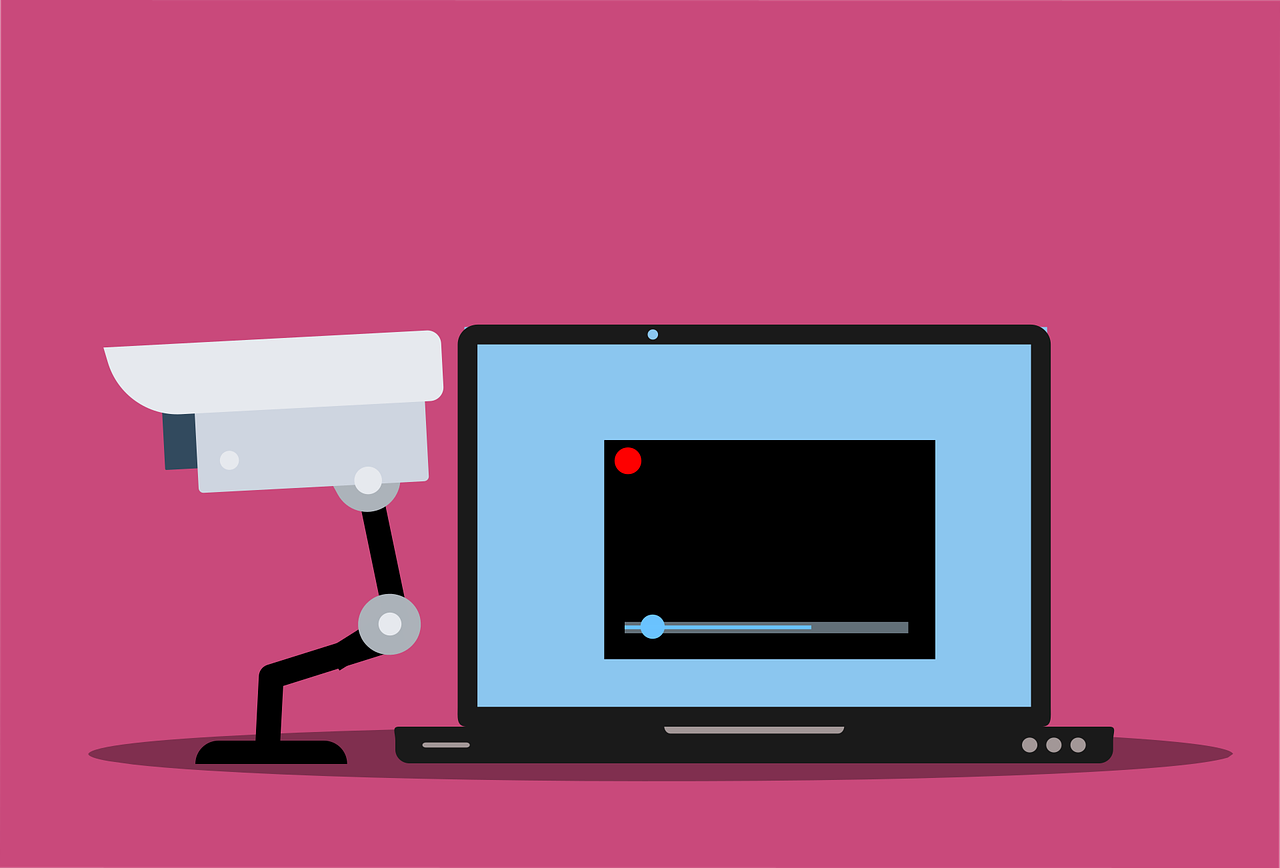
Our team set out to answer these questions and quickly discovered that some types of devices warrant more attention than others as they have a much bigger impact on our privacy and security. That is why over half of the devices our team focused on have audio-video recording and streaming capabilities.
Security cameras, home surveillance cameras, video doorbells, and baby monitors are among the most popular and accessible products on the market, but they also pose the biggest security issues. Let’s face it, having your own security camera turn against you, and the idea of a stranger watching your every move is everyone’s biggest nightmare.

However, this doesn’t mean we downplayed other types of devices. On the contrary, our team found out during tests that sometimes even non-camera devices can pose serious threats. Imagine, for example, a smart bulb that reveals your home WI-FI password, or another device that leaks your geographic location.
Without further ado, here is a list of common issues our team encountered during its first seven years of device security assessment:
Common IoT problems:
1. Faulty authentication
Regardless of the type of device you’re installing, the initial setup and its inclusion in the home network remain critical steps. However, as our researchers found, it’s also one of the most vulnerable stages of the process as an attacker can easily exploit it to take control or gain further access.
During the onboard process, many devices create a temporary hotspot that the user must connect to, usually via mobile phone. However, often enough that hotspot lacks the proper authentication mechanisms and is available to virtually anyone in range. Furthermore, the open hotspot can be used by malicious parties to intercept and steal the owner’s WI-FI network credentials, which in turn grants an attacker access not only to the new device but to all the devices connected to that network.
Another worrying practice, that we’ve encountered often enough, consists of using easy to guess default credentials like “admin,” “admin” or including hidden administrative panels with hardcoded credentials that are the same for all units. Both situations can easily lead to device takeover if an attacker is close by and has enough info about the connected devices.
2. Unprotected data transfer
Smart devices constantly talk to servers and among themselves using different protocols. The transferred information can include almost anything from authentication information (“user logged in,” “password reset”) to commands (“turn on” or “turn off”), to state changes (“movement detected,” “temperature up one degree”) and even video/audio recordings and live streams.

Our researchers have found that due to faulty authentication, misconfiguration, or lack of encryption, a fair share of devices, especially video capturing devices, are vulnerable to man-in-the-middle attacks. This means malicious parties can intercept data transfer, tap into RTSP video feeds, and interfere with firmware updates.
In turn, this can lead to device takeovers and, more disturbingly, cyberstalking, with attackers being able to access the live video/audio stream, or older recordings.
“Unencrypted communication with the cloud is the most common vulnerability we found during device testing. Even when the connection uses HTTPS, usually the certificates aren’t validated which means man-in-the-middle attacks can still happen.” Radu Basaraba - Security Researcher, Bitdefender Labs
3. Cloud misconfiguration
Most smart devices connect to a cloud service for remote access and data storage. However, our researchers determined that in some cases this can lead to serious vulnerabilities as the service is misconfigured, lacks proper security, or the cloud API (Application Program Interfaces) can be brute-forced to reveal vulnerable data.

In more than one instance we found out that using the ID of a single device, the API can be tricked into revealing information related to all the devices associated with a certain user, and even devices related to other users.
In other cases, we learned that by abusing API privileges, an attacker could steal personal information and credentials related to a user, remotely control devices and gain access to video feeds and recordings.
However, the worst scenario we encountered is that of a cloud bucket that completely lacked access control. From our experience, this is a general problem that doesn’t affect only smart devices manufacturers, it also plagues many other companies and is one of the leading causes of data breaches.
4. Remote Code Execution and Command Injection
Remote Code Execution (RCE) and Command Injection are two types of cyberattacks commonly used to take over devices. Although at first glance they may seem similar, they actually work very differently. An RCE consists of actual programming code being executed to exploit a vulnerability, whereas a command injection relies on using existing operating system commands to take advantage. Briefly, although the result may be the same, the angle of approach differs.

Our team determined that almost half of the devices we examined are susceptible to these kinds of attacks with most RCEs (Remote Code Execution) exploiting stack buffer overflow - an anomaly that occurs when a program writes to a memory address on the program's call stack outside of the intended data structure, which is usually a fixed-length buffer.
In our opinion, this should definitely raise a red flag among developers as stack buffering is one of the oldest and most basic cyber threats in the book, and at the same time one of the first attack vectors, a hacker, will try.
5. Privacy issues
The worst privacy scenario when it comes to IoTs is having your devices watching, listening, and recording you without your knowledge. This can be used for stalking, intimidation, blackmail, and several other frauds. It can also be used for planning a robbery when no motion is detected, and no car is in sight. However, as we found during our tests, there is other personal information an attacker can also grab using device vulnerabilities.

Most people tend to reuse passwords for multiple accounts and devices, that’s why if someone were to extract your e-mail address and password from a poorly protected device account, they could potentially try to use them to hijack other accounts and devices. If you have financial information tied to that account, like a monthly subscription, then those can be easily stolen too.
Similarly, if someone were to steal your Wi-Fi credentials, they could use them to exploit other vulnerabilities and to gain access to other devices in your home network like a computer, or a Network Attached Storage.
An unusual vulnerability we discovered during testing was a device that gave away its users’ geographical location. This may not seem like much but combined with other information ultimately it could potentially lead to a scenario in which a malicious actor tries to intimidate or extort you.
How can smart devices become more secure?
As previously stated, our main conclusion is that making smart devices safer should’t be a one-sided struggle. It should be an ongoing partnership between vendors, the IoT device industry, and the infosec community. As Dan Berte, IoT Director puts it:
“As a category with exceptional growth, furthered by the pandemic that forced work from home to bring even more devices into our homes, the Smart Home is no longer an experimental environment. It’s an established day-to-day reality that billions of people rely on without second guessing the perils in a fully unregulated market. At the current scale, the issues escape the home or corporate environment and directly transcend into national security concerns”

Here are a few key points that support our hypothesis:
1. The threats against IoTs are multiplying
The number of connected devices isn’t the only one growing fast, cyberattacks are also increasing at an alarming rate. According to Bitdefender telemetry, in 2021, over the course of just 6 months, there were 68 million security events related to 11 million IoT devices monitored. New botnets, such as Mozi, generated 90% of the total IoT traffic in 2019. With millions of users at risk, identifying vulnerabilities and fixing them as quickly as possible has become vital, however, there’s a lot to improve in the way vendors and infosec experts communicate.
2. Vendor transparency needs to improve
Up-to-date frameworks and internal procedures make sure vendors deliver products that are both safe and functional. Nevertheless, due to the complexity of modern software and hardware systems, vulnerabilities are bound to appear. In fact, it’s safe to assume all IoT products come with some form of vulnerability. It’s the security expert’s mission to identify those issues and report them to the vendor so they can be fixed. However, this process can be perfected.
Most vendors don’t have a responsible resource on their website or an internal procedure to handle bug submissions. From our experience, the most popular method to contact a vendor is by email, followed by support channels and some through both phone and email. But even after initial contact, interaction is fairly slow. According to our team, about 33% of vendors were said to reply in under one month, 50% from one to three months, and 17% were said to reply in three months to a year. When it comes to patching the vulnerability, 80% of vendors took three months to a year to fix and 20% one to two months. More alarmingly an uncomfortable majority of vendors never reply to disclosure contact, reply with significant delays, never fix reported vulnerabilities, or take too long to issue patches. This leads to another important topic: the lack of industry regulations.
3. Is the industry doing enough?
So far, the process of disclosing and fixing IoT vulnerabilities has greatly been governed by informal arrangements and best practices. For example, the industry standard for disclosure policy, which sets a protected period given to a vendor to release the patch for the vulnerability, is 90 days from contact and, in most cases, there is no extension if the patch isn’t issued within the allowed timeline.
However, there’s no guarantee a vendor will take responsibility and fix the known issues. From our experience, almost a quarter of vendors would have never patched the vulnerability, or it would have been close to the end-of-life cycle for their product. Sure, losing credibility and a damaged reputation can be a direct consequence, but is it enough when millions of users can be affected?
In our opinion, a possible solution to the problem would be to adopt an industry-wide compelling standard to govern responsible disclosure.
“It’s a creative industry and nobody like constraints but right now there aren’t any repercussions for failing to follow best practices. It’s common sense that vendors should be mandated to have a security contact responsible to handle inbound vulnerability disclosure requests. Disclosed vulnerabilities must be fixed within the lifetime of the IoT product and there should pe legal and financial consequences in case of a breach. At the end of the day, the safety of millions is at stake and you must be responsible.” – Dan Berte, IoT Security Director
tags
Author
The meaning of Bitdefender’s mascot, the Dacian Draco, a symbol that depicts a mythical animal with a wolf’s head and a dragon’s body, is “to watch” and to “guard with a sharp eye.”
View all postsYou might also like
Bookmarks


