Midwives clinic takes nine months to deliver news of data breach

CBC News in Canada is reporting that clients of a pregnancy care clinic in Ontario have had their personal information exposed to hackers.
Midwives of Windsor has reportedly contacted clients, informing them that one of its email accounts was compromised in April 2023, allowing hackers to gain unauthorised access to the following information:
- Client's name
- Date of birth
- Mailing address
- Email address
- Telephone number
- Information regarding pregnancy
- Treatment/Diagnosis information
- Prescription information
- Patient ID
- Health insurance information
Clearly there is a good amount of sensitive information there, which could be exploited by fraudsters.
The most elementary attack could simply see a cybercriminal contact victims via email or SMS text message with a malicious link.
However, it's also possible that a determined fraudster could use the breached information to scam yet more information out of victims, and piece together more of an individuals' personal details with the eventual aim of committing a more costly identity theft attack.
And what's also a concern is that the security breach occurred in April 2023, but affected members of the public are only finding out about it now - some nine months later. I'm sure I don't need to tell anyone who has made use of the services of a midwife, that a lot can happen in nine months...
CBC News says that it contacted Ontario's Information and Privacy Commissioner for more information, and it said in a statement that the breach was reported to it on November 3 2023 - again, several months after the incident occurred.
It's true to say that in many instances organisations may not realise that hackers have gained access to sensitive data for months on end. But if I were one of Midwives of Windsor's clients I would be asking some hard questions as to just why it has taken so long to issue a warning, months after privacy regulators were informed.
One concerned victim is Nancy Lefebvre, who used the midwifery services in 2020, and probably hadn't thought much of Midwifes of Ontario since - until she received an email from them out of the blue which warned of the data breach:
"You go to a midwife for that higher degree of intimacy and not wanting to be part of like a big corporation ... where you don't think that's something that would happen," said Lefebvre. "It is also concerning because in that span of time a lot can be done with that information and it would have been nice to know sooner."
Midwives of Ontario says that it "acted immediately to secure the email account and retain third-party experts to assist us in our investigation" upon learning of the incident.
Midwives of Ontario has not shared any information about how many people may have been impacted by the breach, but says that it is not aware of any misuse of the exposed data.
Of course, it's impossible for a breached organisation like Midwives of Ontario to categorically prove that there has not been any misuse of the data over the past nine months or so, or won't be in the future.
The practice advises patients to remain alert to "suspicious communications that could be linked to this incident."
Midwives of Ontario says on its website that is is committed to safeguarding the privacy and confidentiality of individuals.
Links on the Midwifes of Ontario website and official Facebook page direct clients to an outlook.com email address.
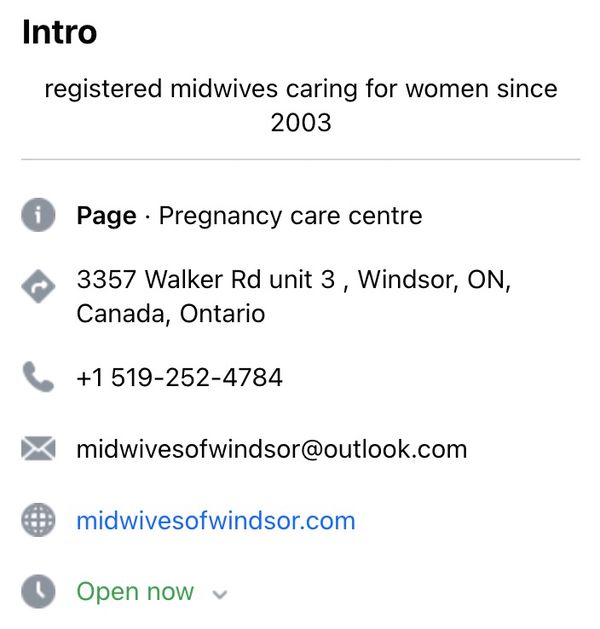
My hunch is that this may well be the email address which was compromised by the hackers. I wonder if it was secured with a strong, unique password and protected with two-step verification?
tags
Author
Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s.
View all postsRight now Top posts
Few People Consider Themselves a Target for Cybercriminals, Bitdefender Study Shows
July 10, 2024
Uncovering IoT Vulnerabilities: Highlights from the Bitdefender - Netgear 2024 Threat Report
June 26, 2024
FOLLOW US ON SOCIAL MEDIA
You might also like
Bookmarks








