‘Downfall’ CPU Vulnerability Could Expose Billions of Devices to Data Theft
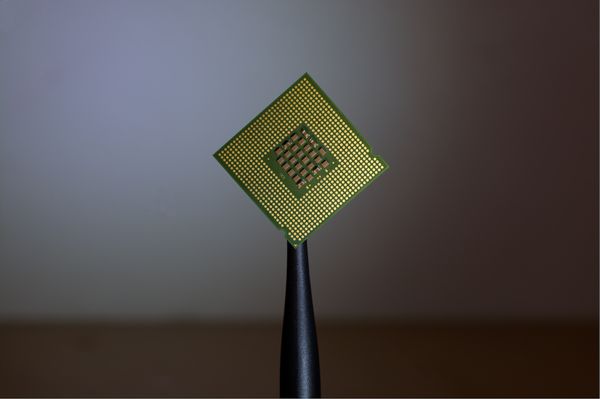
A novel and disturbing vulnerability has been discovered in billions of modern processors, potentially affecting both personal and cloud systems worldwide.
Cybercriminals could use the flaw, identified as CVE-2022-40982 and named "Downfall," to steal passwords, encryption keys, banking details and other critical data.
The vulnerability affects Intel Core processors from the 6th Skylake to the 11th Tiger Lake generation, a span that dates back to at least 2014.
Daniel Moghimi, a senior Google researcher who uncovered the flaw, explained, "I discovered that the Gather instruction, meant to speed up accessing scattered data in memory, leaks the content of the internal vector register file during speculative execution. To exploit this vulnerability, I introduced Gather Data Sampling (GDS) and Gather Value Injection (GVI) techniques."
How Does It Work?
The vulnerability is rooted in the memory optimization features of modern processors. These features inadvertently leak internal hardware registers to software, allowing untrusted applications to access data normally inaccessible.
In a demonstration, Moghimi used the GDS technique to steal AES 128-bit and 256-bit encryption keys on a separate virtual machine (VM) from the controlled one. This exploit took less than 10 seconds and managed to steal AES round keys, effectively breaking the encryption.
A malicious app downloaded from an app store could use the Downfall attack to harvest sensitive information. In cloud environments, a malicious customer could weaponize the vulnerability to steal data and credentials from others sharing the same cloud computer.
The Impact
The Downfall vulnerability is particularly alarming due to its broad potential, affecting computing devices that have been put in use over nearly the past decade.
Moghimi warned that detecting the attack is not simple, as "Downfall execution looks mostly like benign applications."
However, a detection system based on hardware performance counters to identify abnormal behaviors like excessive cache misses could be theoretically possible, he posited.
Mitigation and Response
Intel is actively working to mitigate the attack by releasing a microcode update that blocks transient results of gather instructions, effectively preventing attacker code from "observing speculative data from Gather."
The researcher has published a website encompassing detailed information about the attack as well as demonstrations. Additionally, Intel has provided a consolidated list of affected processors.
The discovery of Downfall underscores the importance of ongoing vigilance in the cybersecurity landscape.
Users of affected processors are advised to monitor updates from Intel and apply necessary patches as they become available to protect against the exploitation of this alarming flaw.
tags
Author
Vlad's love for technology and writing created rich soil for his interest in cybersecurity to sprout into a full-on passion. Before becoming a Security Analyst, he covered tech and security topics.
View all postsYou might also like
Bookmarks


