Cracked Apps and Modded or Full Games for Android Pose a Huge Security Problem

Cracked apps and modded Android games may promise free features, but they often come at a hidden cost. Behind the appeal of unlocked content lies a high risk of malware, data theft, and device compromise. Understanding these risks is essential before installing apps from unofficial sources.
Key Takeaways
- Cracked apps and modded games are high-risk malware carriers. Many modified APKs from third-party sites contain hidden malicious code rather than the promised features.
- Modded apps are significantly more likely to be malicious. Studies show they request more permissions and are far more likely to contain harmful components than official versions.
- Large-scale campaigns use modded apps to spread adware and steal data. Tens of thousands of modified apps have been found installing intrusive ads, phishing tools, and credential stealers on Android devices.
- Even trusted platforms aren’t immune—but third-party sources are far riskier. Malicious apps can bypass protections, making it critical to avoid unofficial downloads and use security tools.
Why Cracked Apps and Modded Android Games Are a Security Risk
The dangers of websites hosting modified APK files that promise full games, cracked apps and other benefits cannot be understated. They are so pervasive online, in fact, that it’s much more likely to get a malware file than the item the uploaders promise.
Content or app piracy can’t be ignored. It is a worldwide phenomenon, and many users are likely unaware that they’re actually doing something wrong. After all, they’ve simply downloaded an app that appears at a generic search on Google’s first results page.
Besides piracy, Android users are looking for trainers and mods for games hosted on the same websites. The attackers who distribute this malware know exactly what people want, and they build infected packages that can serve those requests.
Almost an industry
A recent Bitdefender investigation found tens of thousands of unique “apps” designed to plant malware in Android devices. They deploy annoying full-screen ads, so we categorize them as HiddenAds.
While they might seem innocuous, they’re anything but. Since the number of unique samples we see in the wild is so large, it likely means an automated process continues to churn out these “apps.”
The reason for the quotation marks around the word “app” is simple: these are not the apps, mods, or cracks they claim to be. They just use the names of popular, legitimate apps to trick people into downloading them. You’re not downloading YouTube Add Free Cracked. You’re only getting HiddenAd malware with that name.
The internet is rife with these fake apps
As a simple experiment, I performed a basic Google search for cracked Android apps and opened the first website on the list (results might vary depending on your search history). I downloaded the first APK, which promised to be a full game you would need to pay for otherwise.
The browsing experience on that website will differ depending on the platform used. When using Google Chrome on a desktop computer, you’re met with lots, but on the mobile version, the website aggressively tries to persuade you to enable notifications. Those notifications can always be used to push malware links for other, much more serious threats.
I installed the APK on a clean Android with no security solution present, and the result was straightforward. I received a message that the application is not available in my region and that it will be uninstalled. Of course, the message itself is fake and the application is already installed at that point. This is exactly the behavior we observed in the previous investigation.
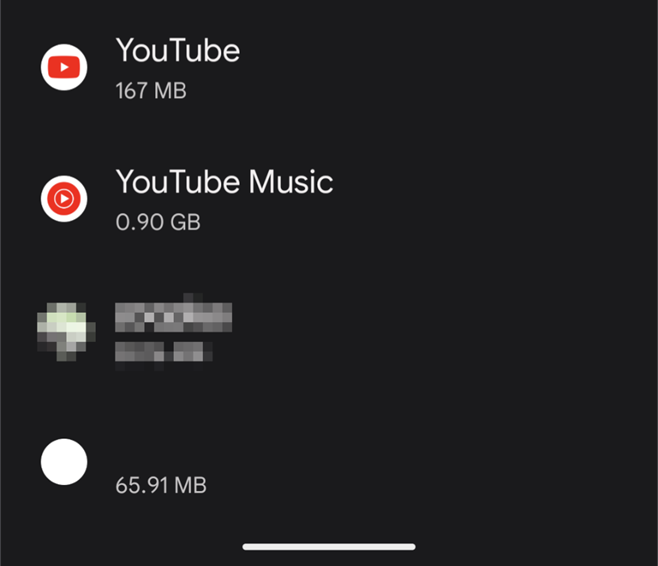
The new application is not visible in the apps list at the expected location based on its name. It has a transparent icon and a special character that places it at the end of a list. The only way to see that I was infected was to track the name of the APK via ADB commands from a terminal or check the list of installed apps and scroll all the way to the bottom.
Our investigation revealed that the full-screen ads can take a long time to appear, sometimes even two weeks, making it more difficult for the user to connect the two incidents.
App Anomaly Detection for the win
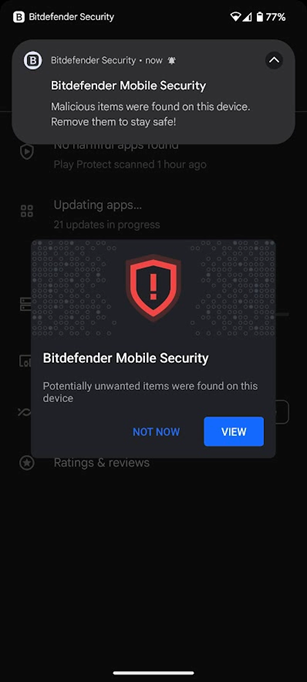
The best way to protect against these types of threats is to install Bitdefender Mobile Security for Android. With its new App Anomaly Detection technology, the security solution will inform users that an application is misbehaving and is likely malware. Of course, the problematic APKs will also be flagged as malicious.
This is what you would see if the security solution is present:
Always install apps from official stores, use a security solution, and avoid downloading apps from third-party sources, especially when they promise to deliver mods, trainers, cracks or full versions of apps that you’d normally have to pay for.
Frequently asked questions (FAQ)
Is using cracked apps illegal?
Yes, using cracked apps is generally illegal because it involves bypassing licensing protections and violating copyright laws. It also breaks the app’s terms of service. Beyond legal risks, cracked apps often contain malware that can steal data or compromise your device.
Are APKs illegal?
No, APK files themselves are not illegal. APK is simply the file format used to install Android apps. However, downloading APKs from unofficial or untrusted sources can be risky, especially if the app is pirated or modified, as it may contain malware or violate copyright laws.
Is Google killing instant apps on Android?
Google has been phasing out Android Instant Apps, with support expected to end as the company shifts focus to other technologies and app experiences. While not directly related to scams, this change reflects evolving Android ecosystem priorities.
Can I trust apps from F-Droid?
F-Droid is generally considered a safer alternative app repository because it focuses on open-source apps and transparency. However, it’s not risk-free—users should still review app permissions, developer reputation, and updates before installing any app.
tags
Author
Silviu is a seasoned writer who followed the technology world for almost two decades, covering topics ranging from software to hardware and everything in between.
View all postsYou might also like
Bookmarks


