Who Is Reading Your CEO's Email? And How to Stop it

We all know that Business Email Compromise (BEC) is one of the most dangerous IT threats facing organisations today.
Criminals dupe your staff into transferring money into a bank account under their control.
Sometimes they do it by posing as the boss and simply asking ordering a member of staff to wire the money into an account urgently.
In more sophisticated attacks, however, fraudsters may have compromised email accounts at the targeted company, spied upon communications between employees and suppliers, and send invoices related to genuine work that has been undertaken - but request the payment be made into the criminals' bank account.
Such BEC attacks were recently named by a top insurance firm as the top cause of loss for cyber claims, outstripping ransomware. Meanwhile, such attacks are thought to have attempted to steal a staggering $9 billion in the last three years alone.
With so much to lose, I wonder how many companies are taking steps to reduce the chances of suffering from a BEC attack, beyond simply trying to raise awareness amongst staff about the risk.
Simply emailing your userbase to inform them that some staff have had their email accounts targeted, for instance, may not be effective.
For example, hackers have been known to create rules in their victims' email accounts, automatically deleting any incoming email which contains words like "virus", "malware", "phishing", or "hack."
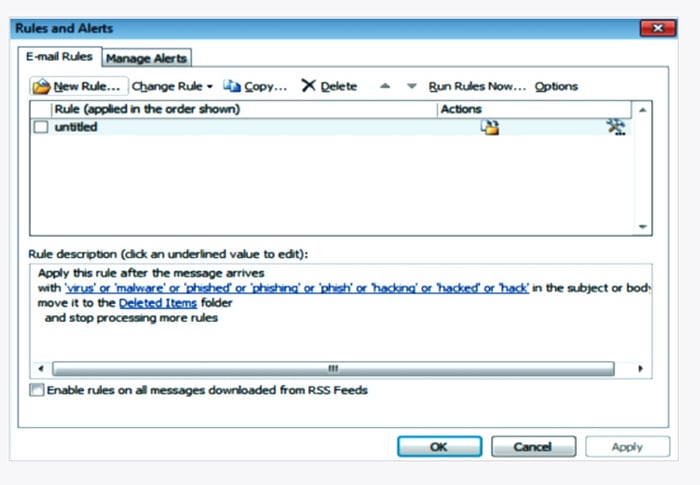
Such techniques can be deployed by a scammer to help maximise the amount of time they retain control of a hacked email account.
Ideally a hacker wants to retain control of an email account, even if its password is later changed, and they can achieve this by creating another rule which automatically forwards emails to an external account (such as a Gmail address) owned by the attacker.
There are plenty of examples online of IT staff discovering that executives have not only had their accounts hacked, but that an auto-forwarding rule has been put in place to continually leak sensitive and confidential information, with forwarded emails automatically erased from the Sent folder in an attempt to avoid detection.
Clearly things can also be done to harden staff email accounts from being compromised in the first place. Multi-factor authentication should be put in place, of course, and you may wish to control through IP addresses and GeoBlocking what locations users can access email systems from.
In addition, incoming emails can be clearly marked if they are from an external source, and password managers should be used to reduce the chance of a phishing site being able to steal login credentials.
But some email systems can go further in terms of the security features they offer.
For instance, some systems can raise an alarm if it believes a login may not be authentic (for instance, if a user signs in from San Francisco five minutes after connecting from London), or if the device being used to log into an account is running a different operating system or device from that normally used by the user.
However, to specifically tackle the threat posed by BEC scammers who regularly use the technique of forwarding email, I would also recommend that companies look into whether they can apply policies on their email system to prevent emails from being automatically forwarded to external domains.
If that isn't acceptable inside your company then the likes of Office 365 can offer IT teams reports on messages being auto-forwarded out of the business, who the new auto-forwarding users are in your organisation, and what domains they are auto-forwarding to.
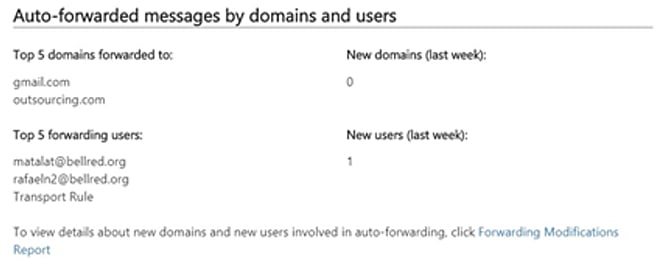
With Business Email Compromise such a significant and growing threat, it makes sense to keep a close eye on who is forwarding email out of your business, and where it is going to…
tags
Author

Graham Cluley is an award-winning security blogger, researcher and public speaker. He has been working in the computer security industry since the early 1990s, having been employed by companies such as Sophos, McAfee and Dr Solomon's. He has given talks about computer security for some of the world's largest companies, worked with law enforcement agencies on investigations into hacking groups, and regularly appears on TV and radio explaining computer security threats. Graham Cluley was inducted into the InfoSecurity Europe Hall of Fame in 2011, and was given an honorary mention in the "10 Greatest Britons in IT History" for his contribution as a leading authority in internet security.
View all postsRight now Top posts
FOLLOW US ON SOCIAL MEDIA
SUBSCRIBE TO OUR NEWSLETTER
Don’t miss out on exclusive content and exciting announcements!
You might also like
Bookmarks